In this blog post, we explain how to analyze ModSecurity events with Wazuh. Wazuh is a unified XDR and SIEM solution. It can be used to collect, analyze and correlate security event data for threat detection and incident response. Wazuh has an out-of-the-box integration with ModSecurity which eliminates the need for creating custom integration.
ModSecurity is an open source, cross platform web application firewall (WAF) engine for Apache, IIS, and Nginx. The integration between these two platforms, added to ModSecurity WAF capabilities, can help users detect and block web attacks. Some of the reasons why Wazuh should be integrated with ModSecurity are highlighted below:
- Collect security related events: There is the need to collect all security related events to a centralized platform for easy and more efficient monitoring, correlation, and incident response.
- Alerting and visualization: ModSecurity can take advantage of Wazuh’s alerting and visualization capabilities.
The prerequisites to having a functional setup are:
- A Wazuh server. The Installation guide can be found here.
- A Wazuh agent on the WAF endpoint. A Wazuh agent can be installed by following the guide in the documentation here.
The setup in the following sections shows how to install an Apache web server and the WAF module. The Wazuh agent on the web server endpoint is configured to forward the WAF logs to the Wazuh manager.

Install Apache2
We install the web server, enable it to run on system reboot, and then start the web service with the commands below:
sudo apt install apache2 sudo systemctl enable apache2 sudo systemctl start apache2
Install ModSecurity
We install ModSecurity, enable the ModSecurity extension module for Apache, and then restart the web service with the commands below:
sudo apt install libapache2-mod-security2 sudo a2enmod security2 sudo systemctl restart apache2
Configure ModSecurity
ModSecurity by default only detects suspicious activity. In our case, we need to configure it to block this activity.
The default ModSecurity configuration file modsecurity.conf-recommended is copied to a new file as provided in the command below:
sudo cp /etc/modsecurity/modsecurity.conf-recommended /etc/modsecurity/modsecurity.conf
We opened the configuration file /etc/modsecurity/modsecurity.conf and located the line SecRuleEngine DetectionOnly. We changed this line to SecRuleEngine On in order to block malicious requests. After changing the line, the file looks like this:
# -- Rule engine initialization ---------------------------------------------- # Enable ModSecurity, attaching it to every transaction. Use detection # only to start with, because that minimizes the chances of post-installation # disruption. SecRuleEngine On
The Apache server is restarted to apply the changes.
sudo systemctl restart apache2
Configure the Wazuh agent to forward ModSecurity logs to the Wazuh manager
Apache ModSecurity logs are saved in the Apache error log by default. The error log file is located at /var/log/apache2/error.log. We configured the Wazuh agent on the web server to forward the error log to the Wazuh manager. This is done by modifying the /var/ossec/etc/ossec.conf file on the agent and adding the following lines to the <ossec_config> section:
<localfile> <log_format>apache</log_format> <location>/var/log/apache2/error.log</location> </localfile>
Restart the Wazuh agent.
sudo systemctl restart wazuh-agent
Test the setup
In order to test the setup and generate alerts on the dashboard, we use a command line tool Nikto to run a vulnerability scan against the web application.
Nikto can be installed on Debian systems from the APT repository with the command:
sudo apt-get install nikto -y
After installation Nikto, run it to scan the web server with the following command:
nikto -h <webserver_IP>
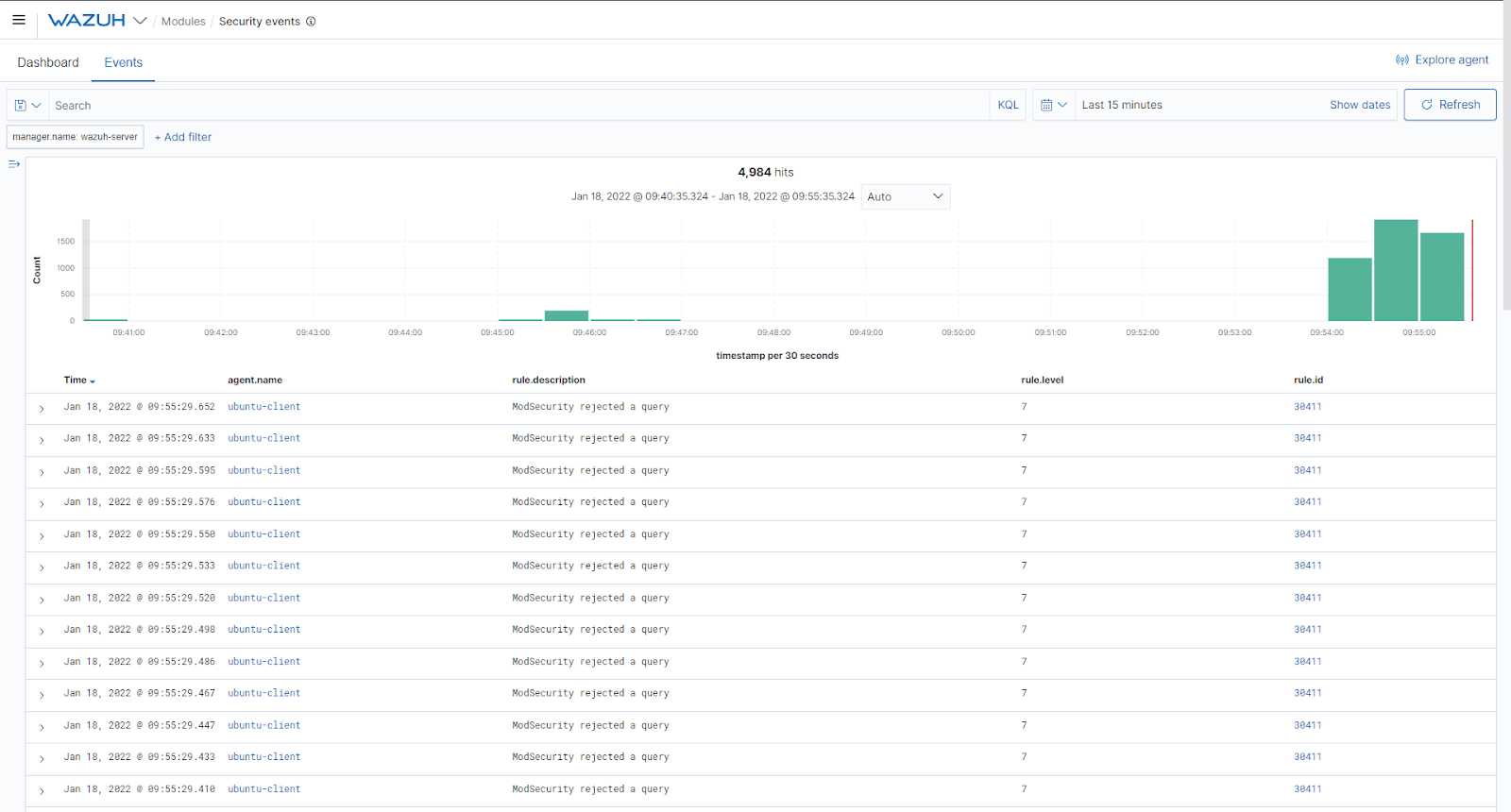
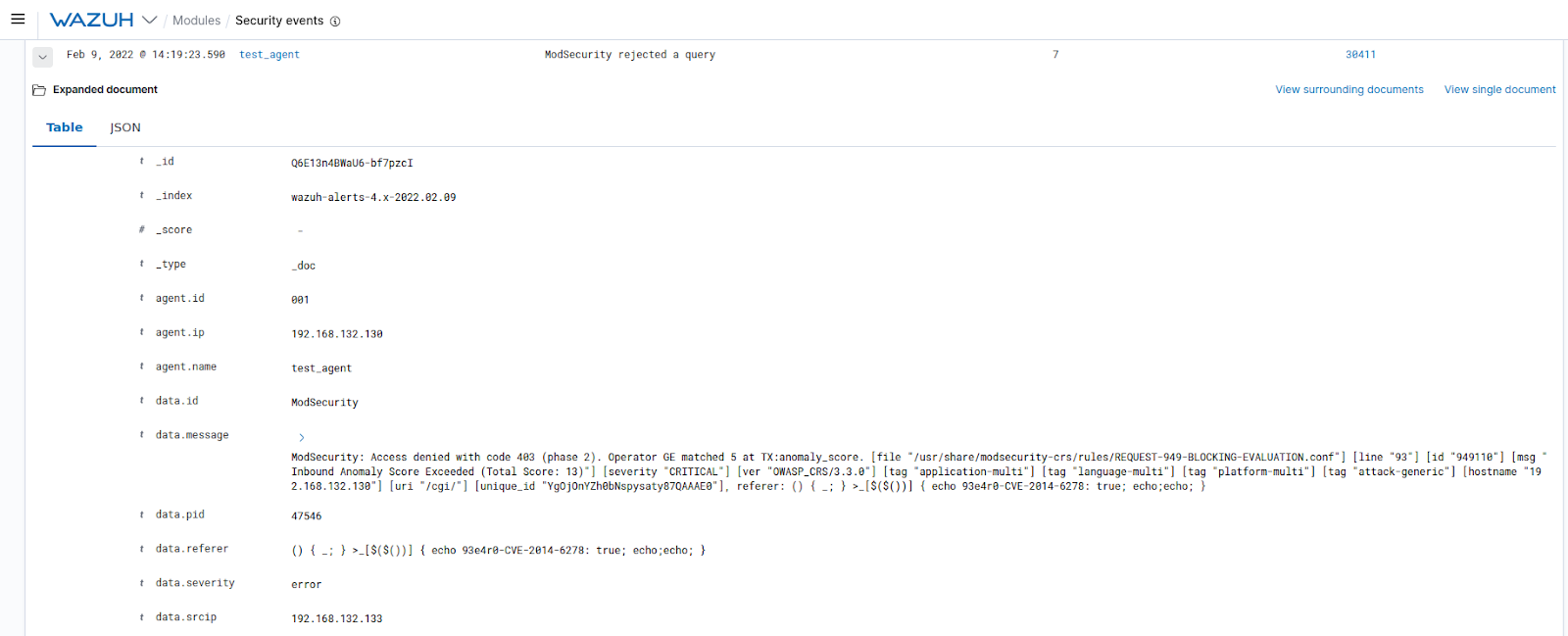
The scanning activity of Nikto triggered several alerts on ModSecurity and these alerts can be seen on Wazuh’s event dashboard:
Summary
In conclusion, the test shows that ModSecurity integrates efficiently with Wazuh. By forwarding the WAF’s logs to the Wazuh manager via the agent, users can collect and analyze firewall-related events, getting the most out of these two security platforms.
The logs are automatically processed and analyzed by the manager without the user doing any further work. This integration is fairly simple because Wazuh provides out-of-the-box support for ModSecurity and several other security tools.