Encryption is the conversion of data from a readable format into an encoded format that can only be read or processed after it’s been decrypted. The Advanced Encryption Standard (AES), also known by its original name Rijndael is a specification for the encryption of electronic data established by the U.S. National Institute of Standards and Technology (NIST) in 2001.
The primary goal of AES is to create an encryption method that is irreversible without the key, and it uses keys that are unbreakable through guessing or brute-force attacks. AES represents a safe and secure way to hide data from unwanted third-parties.
AES encryption in the communication between agents and manager
Encryption of data flowing between agents and manager is very important to prevent sensitive data leaks if our network environment is compromised.
Sniffers, Man-in-the-middle attacks and other network exploits can use unencrypted communications to their advantage. AES encryption also provides a means of proving that information is authentic and comes from the point of origin it claims to come from. It is also able to confirm that information hasn’t been altered during transmission.
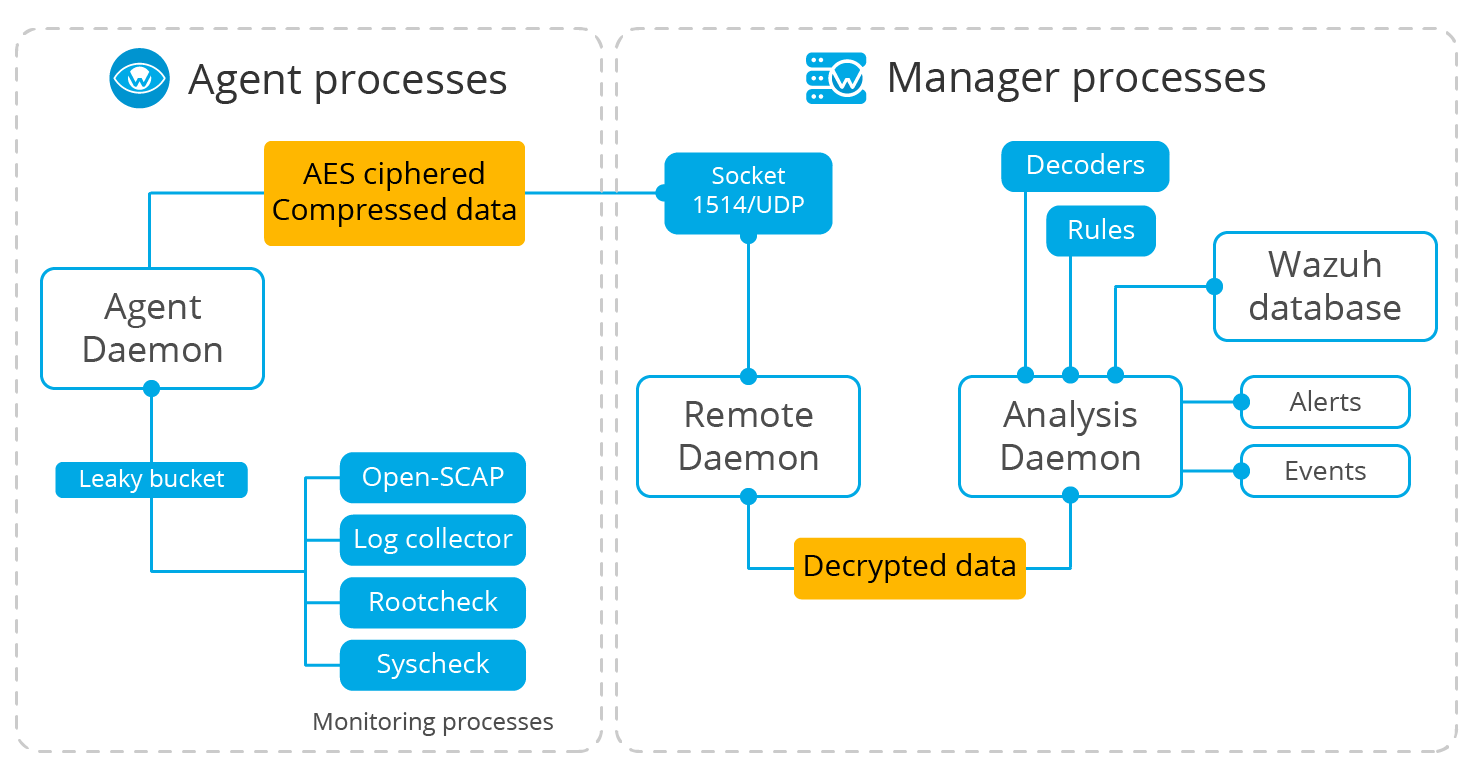
After the events are generated, they are encrypted on the agent side and sent to the manager. The Remote daemon on the manager receives and decrypts the ciphered messages sent by the agents and sends them to the Analysis daemon for further processing.
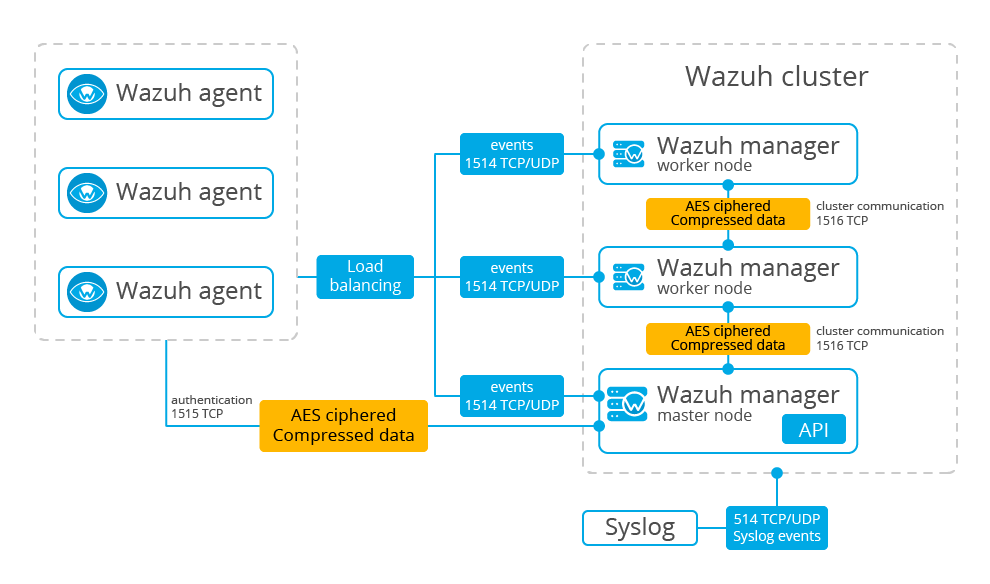
Communication between managers on cluster configuration
When using a cluster configuration, there is even more sensitive data flowing, so communications among nodes in the cluster are also encrypted using AES algorithms.
Blowfish or AES?
Before Wazuh v3.5.0, all messages in the agent-manager channel or between cluster nodes were encrypted using Blowfish. Since Wazuh v3.5.0, AES is the default encryption, so every output from the agents is sent by a safer channel to the manager. It offers improved security on the communication side.
Wazuh uses CBC (Cipher Block Chaining) AES encryption mode. In CBC mode, each block of plaintext is XORed with the previous ciphertext block before being encrypted. This way, each ciphertext block depends on all plaintext blocks processed up to that point. To make each message unique, an initialization vector must be used in the first block.
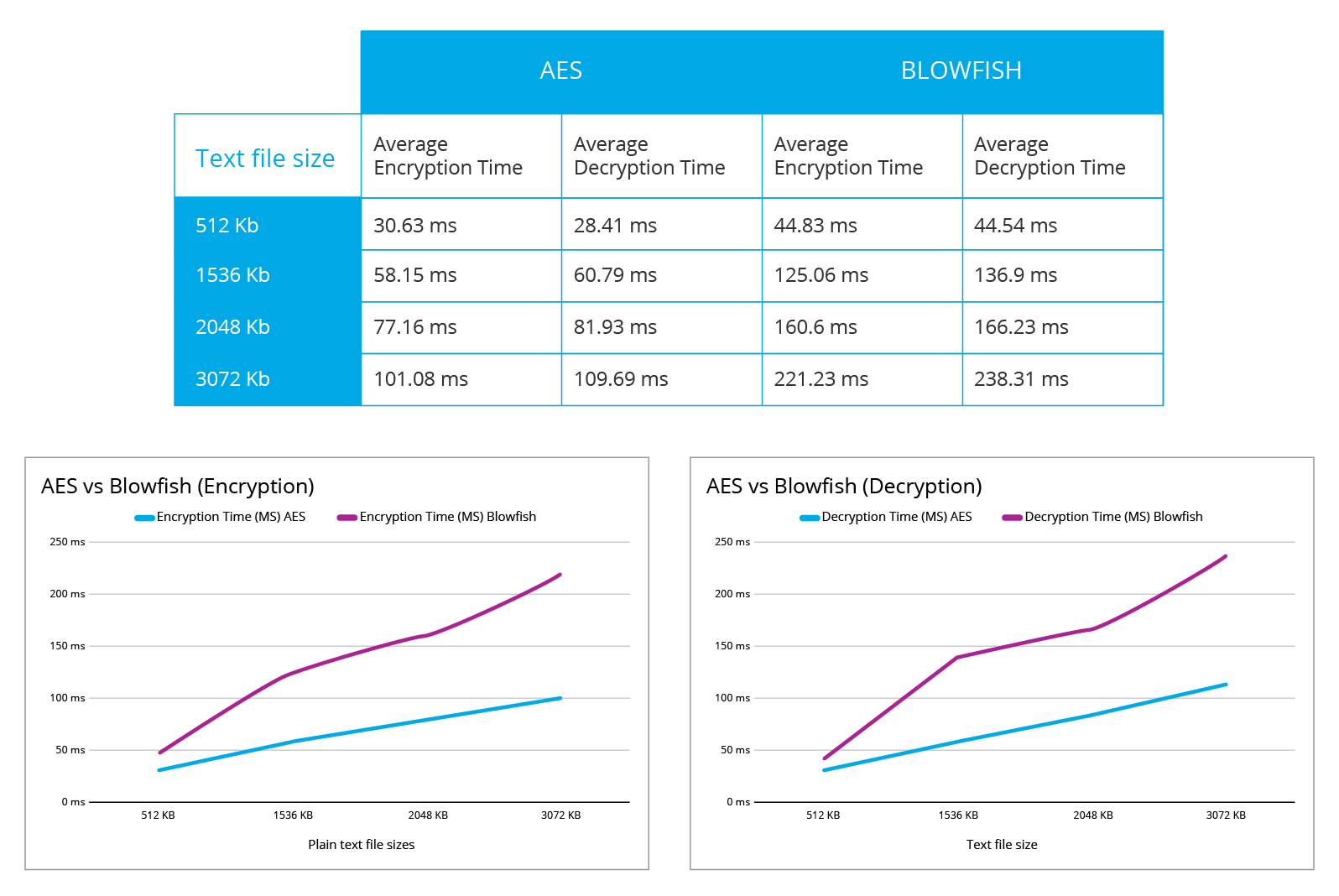
This reporting data table and graph compare AES and Blowfish performance:
Hardware acceleration
Hardware instructions reduce CPU cycles for each round of encryption. The Advanced Encryption Standard instruction set is now integrated into many processors. The purpose of the instruction set is to improve the average speed of applications performing encryption and decryption operations and to add resistance to side-channel attacks. They are often instructions implementing a single round of AES along with a special version for the last round which has a slightly different method.
To check if your machine is capable of using instructions from the AES-NI set:
On Linux systems:
# if (grep flags /proc/cpuinfo | grep -q aes) ; then echo "True"; fi True
On macOS systems:
# if (sysctl -n machdep.cpu | grep -qi aes) ; then echo "True"; fi True
On Windows systems, install application coreinfo to check if your processor supports AES-NI:
# CoreInfo.exe -f | findstr "AES" Coreinfo v3.31 - Dump information on system CPU and memory topology Copyright (C) 2008-2014 Mark Russinovich Systernals - www.systernals.com AES * Supports AES extensions
The transition from Blowfish to AES was due to the better balance between security and performance that Advanced Encryption Standard offers:
- A bigger key size, and this means stronger encryption. The key size directly relates to the resistance to brute force attacks.
- A bigger block size that increases its suitability for encrypting large amounts of data.
- Is compatible with hardware and software implementations.
- Provides confidentiality, integrity and authenticity.
If you have any questions about this, don’t hesitate to check out our documentation to learn more about Wazuh or join our community where our team and contributors will help you.