Chaos is a fast-spreading malware written in Go. It infects Windows and Linux systems across multiple architectures, including ARM, Intel i386, MIPS, and PowerPC. The malware can enumerate the infected endpoint, run remote shell commands, load additional modules, and launch DDoS attacks against entities across the gaming, financial services, media, and entertainment industries. Chaos malware spreads itself by exploiting unpatched vulnerabilities on endpoints.
This blog post analyzes the Indicators of Compromise (IOCs) of Chaos malware and mitigates the infection using Wazuh.
Chaos malware behavior
Below are some actions performed by Chaos malware when it is executed on the victim endpoint:
- File creation: Immediately Chaos malware is executed, the Windows variant of the malware creates a copy of itself in the
C:\ProgramData\Microsoft\directory to mimic a legitimate Windows process,csrss.exe. The Linux variant creates a copy of itself in the Linux system configuration folder/etc/id.services.conf. The Linux variant also creates a reverse shell module,/etc/profile.d/bash_config.shthat allows the malware actor to run arbitrary commands on an infected endpoint. - Persistence: The Windows variant of the malware maintains persistence by creating a registry key
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run. This key has the valueC:\ProgramData\Microsoft\csrss.exe, ensuring the malware is executed after reboot. To maintain persistence, the Linux variant of the malware creates a bash script at/etc/32678. The script references the dropped copy of the malware/etc/id.services.conf. Below is the content of the script:
#!/bin/sh while [ 1 ]; do sleep 60 /etc/id.services.conf done
- DNS query to rogue hosts: The malware attempts to establish a connection with a C2 by querying the host
yusheng.j0a.cn. Every successful ping to the C2 returns aQueryStatusof 0.
Detection with Wazuh
In this blog post, we use VirusTotal, Sysmon, and Auditd with Wazuh to detect Chaos malware behavior on the victim endpoint.
Infrastructure
- A pre-built ready-to-use Wazuh OVA 4.3.10. Follow this guide to download the virtual machine.
- A Windows 10 victim endpoint with Wazuh agent installed.
- An Ubuntu 22.04 victim endpoint with Wazuh agent installed.
Using VirusTotal integration
VirusTotal is an online IT security platform that analyzes suspicious files, URLs, domains, and IP addresses to detect threats. Wazuh provides an out-of-the-box VirusTotal integration which, when combined with the Wazuh File integrity monitoring (FIM) module, detects malicious file hashes on an endpoint.
We configure the VirusTotal integration on the Wazuh server and FIM on the Windows and Linux endpoints to monitor the Downloads directory using this guide. Alerts are generated on the Wazuh dashboard whenever the malicious Chaos malware file is added to the Downloads directory.
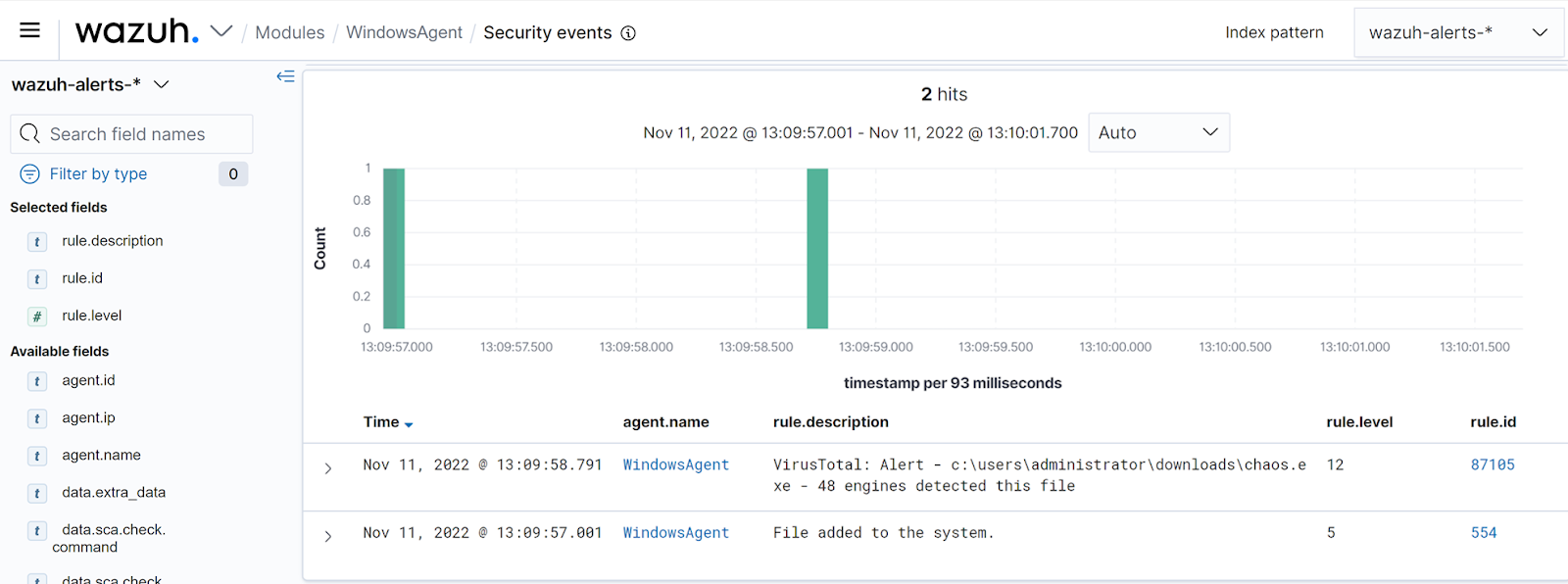
The image below shows FIM and VirusTotal alerts on the Wazuh dashboard:
Using detection rules
We detect Chaos malware by comparing extracted Auditd and Sysmon logs from the Linux and Windows endpoints with a custom ruleset to look for matches.
Windows endpoint
We can detect Chaos malware activities by enriching the Windows Wazuh agent logs with Sysmon.
Configure the Wazuh agent as described below to collect Sysmon logs and transfer them to the Wazuh server for analysis:
- Download Sysmon from the Microsoft Sysinternals page.
- Download the Sysmon configuration file.
- Launch Powershell as an administrator and install Sysmon using the command below:
.\Sysmon64.exe -accepteula -i sysmonconfig.xml
- Edit the Wazuh agent
C:\Program Files (x86)\ossec-agent\ossec.confand include the following settings within the<ossec_config>block.
<localfile> <location>Microsoft-Windows-Sysmon/Operational</location> <log_format>eventchannel</log_format> </localfile>
- Restart the Wazuh agent to apply the changes:
Restart-Service -Name WazuhSvc
Linux endpoint
In this section, we use Auditd rules to detect when Chaos malware creates malicious files on the Linux victim endpoint. Auditd is a Linux utility for monitoring system calls, file access, and creation.
To configure the Wazuh agent to capture Auditd logs on the Linux endpoint, we install Auditd and configure custom rules.
- Install Auditd on the endpoint:
# apt -y install auditd
- Add the following custom rules to the Auditd rules
/etc/audit/rules.d/audit.rulesfile:
-w /boot/System.img.config -p wa -k possible_chaos_malware_infection -w /etc/32678 -p wa -k possible_chaos_malware_infection -w /etc/init.d/linux_kill -p wa -k possible_chaos_malware_infection -w /etc/id.services.conf -p wa -k possible_chaos_malware_infection -w /etc/profile.d/bash_config.sh -p wa -k possible_chaos_malware_infection
- Reload the Auditd rules to apply the changes and verify the applied configuration:
# auditctl -R /etc/audit/rules.d/audit.rules # auditctl -l
- Next, edit the Wazuh agent configuration file
/var/ossec/etc/ossec.confand add the following settings within the<ossec_config>block.
<localfile> <log_format>syslog</log_format> <location>/var/log/audit/audit.log</location> </localfile>
- Restart the Wazuh agent to apply changes:
# systemctl restart wazuh-agent
Wazuh server
In this section, we create rules to detect Chaos malware using the techniques, tactics, and procedures (TTPs) identified. We add the rules below to the /var/ossec/etc/rules/local_rules.xml file on the Wazuh server:
<group name="chaos_malware_windows,">
<!-- Rogue file creation -->
<rule id="100112" level="15">
<if_sid>61613</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)(\\\\Users\\\\.+\\\\)</field>
<field name="win.eventdata.targetFilename" type="pcre2">(?i)\\\\ProgramData\\\\Microsoft\\\\csrss\.exe</field>
<description>Malicious activity detected. csrss.exe created at $(win.eventdata.targetFilename)</description>
<mitre>
<id>T1574.005</id>
</mitre>
</rule>
<!-- Registry key creation for persistence -->
<rule id="100113" level="15">
<if_sid>92300</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)[c-z]:(\\\\Users\\\\.+\\\\)</field>
<field name="win.eventdata.details" type="pcre2">(?i)[c-z]:(\\\\ProgramData\\\\Microsoft\\\\csrss\.exe)</field>
<description>Possible Chaos malware activity: $(win.eventdata.details) added itself to the Registry as a startup program to establish persistence</description>
<mitre>
<id>T1547.001</id>
</mitre>
</rule>
<!-- DNS query to rogue hosts -->
<rule id="100114" level="5" ignore="600">
<if_sid>61600</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)(\\\\Users\\\\.+\\\\)</field>
<field name="win.eventdata.queryName" type="pcre2">(?i)yusheng.j0a.cn</field>
<description>Possible Chaos malware activity: DNS query to rogue host</description>
<mitre>
<id>T1071.004</id>
</mitre>
</rule>
</group>
<!-- Rule to detect Chaos malware on Linux -->
<group name="chaos_malware_linux">
<rule id="100120" level="15">
<if_sid>80700</if_sid>
<field name="audit.key">possible_chaos_malware_infection</field>
<description>Possible Chaos malware infection - Auditd</description>
<mitre>
<id>T1204.002</id>
</mitre>
</rule>
</group>
Where:
- Rule id
100112detects when Chaos malware creates a copy of itselfcsrss.exein theProgramDatadirectory. - Rule id
100113detects when the malware sets the malicious copycsrss.exeas a run key in the Registry. - Rule id
100114detects when the malware makes a DNS request.
Note
Due to the large volume of DNS requests from the malware, rule 100114 can cause agent event queue flooding. Therefore, the detection rule is optional.
- Rule id
100120is the rule created to detect when Auditd rules are triggered.
Once the rules have been added, restart the Wazuh manager to apply the changes using the command below:
# systemctl restart wazuh-manager
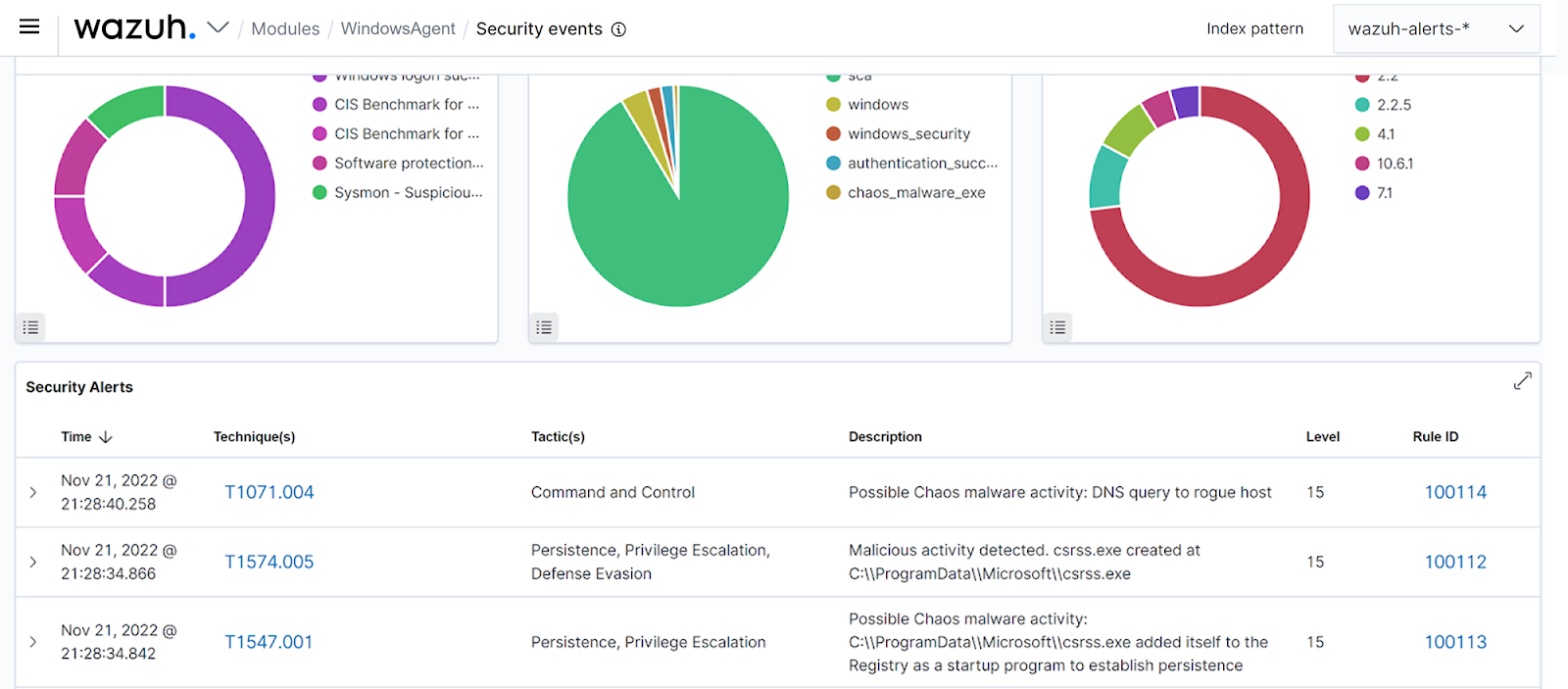
Below is the screenshot of the alerts generated on the Wazuh dashboard when the Chaos malware is executed on the Windows victim endpoint:
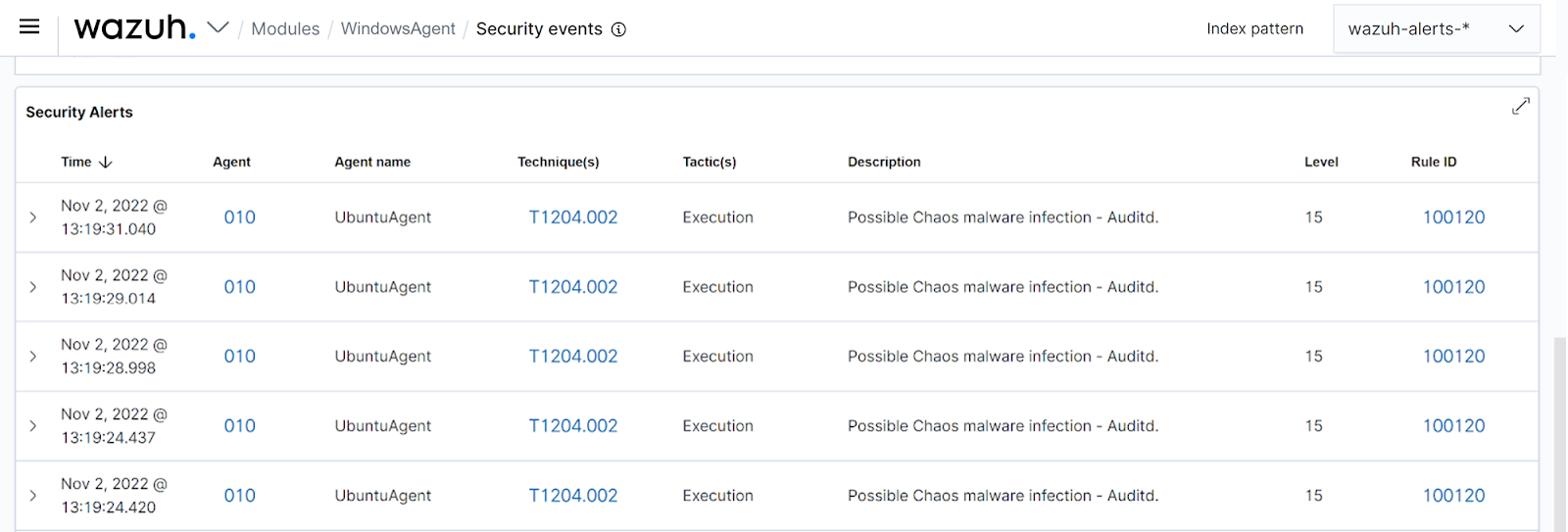
Also, the screenshot below shows the alerts generated on the Wazuh dashboard when Chaos malware is executed on the Ubuntu victim endpoint:
Conclusion
In this blog post, we demonstrated how to detect Chaos malware using Wazuh. We showed how to utilize Wazuh integration with VirusTotal, Sysmon, and Auditd, to detect Chaos malware and its malicious activities.
