In this article we will be learning how to configuring OSSEC, using the report_changes option, in order to get the exact content changes from a file that has been previously modified. This configuration option is only available for unix/linux systems, and works only for text files.
The syscheck component works as follows: each agent scans the system, predefined by the user, and sends all checksums to the manager. Then, the manager stores those checksums, compare them with the previous data and looks for those that don’t match. An alert will be triggered for every single mismatch found.
In this example of how configuring OSSEC, we will set up our system using the report_changes option to track the changes performed in a text file. Also, we will see how the alert generated by this event looks like.
Our starting point is a manager using Wazuh HIDS and several linux agents reporting to it. All of them are running on Ubuntu 14.0.4.
Syscheck component configuration
To start configuring OSSEC, modify the main configuration file in the manager /var/ossec/etc/ossec.conf. My suggestion is adding this line to the syscheck section:
<auto_ignore>no</auto_ignore>
This option specifies whether syscheck will ignore files that change too often (more than 3 changes). By default is set to yes, but let’s say no and, this way, we make sure that an alert will be shown after every change. However, this is up to the user and not essential for the purpose of this exercise.
Now, we need to configure syscheck properly to monitor the desired files. Also, here is where the activation of the option that will show the changes in the content is done. Open /var/ossec/etc/shared/agent.conf file and add this lines:
<agent_config os="Linux">
<syscheck>
<directories check_all="yes" realtime="yes" report_changes="yes">/test</directories>
</syscheck>
</agent_config>
By doing the above, all the files that belong to the /test directory will be monitored as follows:
- check_all : OSSEC can do different checks, such as check_size, check_sum, check_owner… In this case, let’s say we want to monitor all those parameters and, therefore, I am using this option.
- realtime: By default OSSEC runs with the frequency set at
ossec.conf. Using this option we are telling OSSEC to ignore that frequency and show what is going on in real time. Be careful with realtime if you have a lot of files since this can cause disk space issues. - report_changes: Here is the key part of the exercise. This option gives us the exact content that has been changed in a text file. Be careful with the folders you set up to
report_changes, because what OSSEC does is to copy every single file you want to monitor into a private location.
Save the file, and restart the manager to push the configuration to all the linux agents we have.
$ sudo /var/ossec/bin/ossec-control restart
Working on the Agent
First we are going to activate the debug option to facilitate the debug in our agent. Go to your agent and edit this file /var/ossec/etc/internal_options.conf, Set the highlighted line as follow:
# Debug options. # Debug 0 no debug # Debug 1 first level of debug # Debug 2 full debugging # Windows debug (used by the windows agent) windows.debug=0 # Syscheck (local, server and unix agent) syscheck.debug=2
Now we create the test directory. If you wish to monitor a different folder you can skip this step.
$ mkdir /test
Inside the folder, we create the text file that we are going to modify, for instance we can call it hello:
Hello World
Now, we edit this file:
Hello from Wazuh
Let’s see how report_changes works. The copy of the files are stored at /var/ossec/queue/diff/local/your-dir-name/your-file-name, which in our case would be /var/ossec/queue/diff/local/test/hello.
You should have files similar to these:
last-entry: This file show the last state of the file.state.1460947958: This file has the previous state of the file.diff.1460948255: Which contains the differences between the above mentioned files.
The diff file is used to report the changes on the alert.
Two things you can find at this point:
There is no state.XXX or diff.XXX files : You probably need to wait a little bit. Indexing all the files by syscheck can take a while.
There is no diff.XXX file but there is state.XXX file: Take a look to the /var/ossec/logs/ossec.log. We activated the debug option so if we have errors we will find them here. Check if you have an error similar to this one:
ERROR: Unable to link from '/var/ossec/queue/diff/local/test/hello/last-entry' to '/var/ossec/tmp/syscheck-changes-cebbec1cd82d5dd7042d748ff3b9d1c0-1460944367' due to [(2)-(No such file or directory)].
If you found it, it is because you don’t have a tmp dir on your /var/ossec/ dir. Just create it:
$ mkdir /var/ossec/tmp
And change the permissions:
$ chmod 550 /var/ossec/tmp
This should solve the issue. Modify the file again.
Check Generated Alert
Come back to your manager, and make a tail of the alerts.log:
$ tail -f /var/ossec/logs/alerts/alerts.log
You should have an alert similar at your terminal:
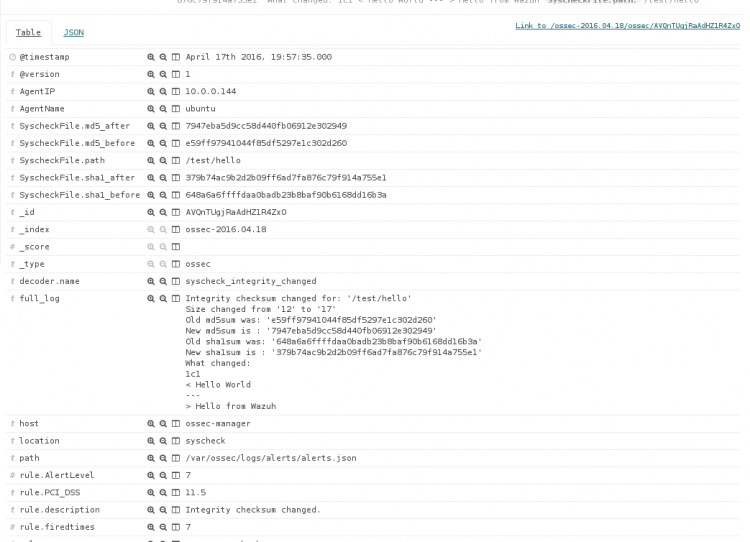
** Alert 1460948255.25442: mail – ossec,syscheck,pci_dss_11.5, 2016 Apr 17 19:57:35 (ubuntu) 10.0.0.144->syscheck Rule: 550 (level 7) -> ‘Integrity checksum changed.’ Integrity checksum changed for: ‘/test/hello’ Size changed from ’12’ to ’17’ Old md5sum was: ‘e59ff97941044f85df5297e1c302d260’ New md5sum is : ‘7947eba5d9cc58d440fb06912e302949’ Old sha1sum was: ‘648a6a6ffffdaa0badb23b8baf90b6168dd16b3a’ New sha1sum is : ‘379b74ac9b2d2b09ff6ad7fa876c79f914a755e1’ What changed: 1c1 < Hello World! — > Hello from Wazuh
Or using Kibana:
If you have any questions about configuring OSSEC to report file changes, join our Slack #community channel! Our team and other contributors will help you.