The Windows Group Policy Objects (GPO) is a feature in the Microsoft Windows operating systems that represents a collection of policy settings. It allows administrators to fine-tune the operating system configurations of user and computer accounts within an organization’s active directory network. GPOs are created in the Domain Controller and applied to clients based on their position in the domain tree. GPOs can perform various tasks, including deploying software programs to client workstations and enforcing security configuration policies for users and computers.
This blog post demonstrates how to deploy the Wazuh agent on a Windows Active Directory (AD) infrastructure using Group Policy Objects. The Wazuh agent is published as a Microsoft Software Installer (MSI) package. The package is executed by the Windows installer (msiexec.exe), which is responsible for registering and configuring the software on the endpoint.
Infrastructure
- A pre-built, ready-to-use Wazuh OVA 4.7.3. Follow this guide to download the virtual machine. This VM hosts the Wazuh central components (Wazuh server, Wazuh indexer, and Wazuh dashboard).
- A Windows Server 2019 or newer domain controller that hosts the Active Directory infrastructure. It also hosts the Group Policy Management Console that contains the Group Policy Objects. In this blog post, we use the domain name wazuhtests.com.
- A Windows 11 endpoint that is registered to the Active Directory. This is the endpoint for installing the Wazuh agent.
- A user account on the Active Directory with local administrative privilege on the Windows 11 endpoint. We use this user account to install Orca and force group policy updates.
Configuration
We configure the Wazuh server to enroll agents using a defined password. Then, we download and configure Orca on the Windows 11 endpoint to generate the MST file. The GPO created on the Windows server hosting the Active Directory uses the MST file to deploy the Wazuh agent to the Windows endpoint. Also, we created a GPO to activate the Wazuh service from the Windows server.
Wazuh server
Perform the following steps to configure the Wazuh server to enroll Wazuh agents using password authentication.
1. Enable the password authentication option by changing the value of the use_password option from no to yes in the <auth> section of the /var/ossec/etc/ossec.conf configuration file:
<auth> <use_password>yes</use_password> </auth>
2. Create the file authd.pass in the path /var/ossec/etc/. This file stores the password used in the Wazuh agent enrollment. We set the password BlueWolf in the file. You can set the password to any value you desire for the Wazuh agent enrollment.
# echo BlueWolf > /var/ossec/etc/authd.pass
3. Change the /var/ossec/etc/authd.pass file permissions and ownership using the following command:
# chmod 640 /var/ossec/etc/authd.pass # chown root:wazuh /var/ossec/etc/authd.pass
4. Restart the Wazuh manager to apply the changes:
# systemctl restart wazuh-manager
Windows endpoint
We perform the following configuration on the Windows endpoint using a domain account with local administrative privilege to enable the deployment of the Wazuh agent via GPO. We use the Windows endpoint to download both Orca and the Wazuh agent, as internet access is usually restricted on most domain controllers as per best security practices. We will create a network shared folder on the Windows server and copy the Wazuh agent downloaded to it for the installation process using the GPO. We:
1. Download and install Orca. (it comes bundled in the Windows SDK Components for Windows Installer Developers). Orca is a graphical database table editor for creating and editing Windows installer packages. It is used to create the custom Microsoft Transform (MST) file. It is located with the installer name Orca-x86_en-us.msi in the bin subdirectory of the Windows Kits folder in the path C:\Program Files (x86)\Windows Kits\10\bin\10.0.22621.0\x86.
2. Download the latest version of the Windows Wazuh agent in a local folder on your Windows endpoint.
Configuring the Wazuh agent installer with Orca
We perform the following steps to configure the Wazuh agent installer file and custom Microsoft Transform (MST) file. The Wazuh agent MSI package format contains a parameter database and the actual program and installer utilities. To automate the agent installation, we need to create an MST file to modify the parameter database at installation time.
Steps:
1. Navigate to C:\Program Files (x86)\Windows Kits\10\bin\10.0.22621.0\x86 and launch Orca-x86_en-us.msi to install the application.
2. Navigate to C:\Program Files (x86)\Orca and launch the Orca.exe application.
- Click on File, and open the Wazuh agent MSI package with Orca. The interface shows the MSI internal database with options to personalize the package installation.
- Click on the Property table (this is where the MSI options are located).
3. Click on Transform > New Transform. In the Property table field, right-click on the table field and select Add Row. A new dialog opens, which accepts the Wazuh deployment variables below needed to perform the installation:
- ADDRESS:
<WAZUH_SERVER_IP_ADDRESS>Replace the <WAZUH_SERVER_IP_ADDRESS> variable with the IP address of your Wazuh server. - AUTHD_SERVER:
<WAZUH_SERVER_IP_ADDRESS>Repace the <WAZUH_SERVER_IP_ADDRESS> variable with the IP address of your Wazuh server. - PROTOCOL:
TCPSets the communication protocol between the manager and the agent. The default value is TCP. - PASSWORD:
<PASSWORD>Replace the<PASSWORD>with the password of your choice. You can set the password asBlueWolfif you used it as the enrollment password earlier.
4. Save the MST file by clicking Transform > Generate Transform and save it as custom.mst. The highlighted fields show the added Wazuh agent deployment variables.
Windows server
To deploy the Wazuh agent MSI, create a network shared folder and a group policy objects. We perform the following steps.
Create a network shared folder
We create a network shared folder to share the MSI installer to the Windows endpoint for the Wazuh agent deployment. The GPO applied on the Windows endpoint that is on the domain will use the installer to install the agent. The folder also facilitates the initial copy of the Wazuh agent installer and the custom.mst files to the Windows server.
Steps:
1. Create a folder named DC in any directory on the Windows server. We created a folder in the C:\Users\<USERNAME>\Desktop directory.
2. Right-click on the folder, then select properties. Navigate to the Sharing tab, click Share, and assign the necessary permissions. You can add a single user account or a group containing the users needing access to the shared folder and assign Read/Write permissions. Then click on Advanced Sharing, select Share this folder, click Apply, and OK. Here, we added the authenticated users group that contains all users whose identities were authenticated when they logged on to an endpoint on the Wazuhtests.com domain.
3. Copy the Wazuh agent MSI installer and the custom.mst file to the shared folder DC.
4. Confirm that the created network shared folder is accessible from the Windows workstation by pressing Win + R on the keyboard and entering the path to the shared folder. The Network path to the shared folder we created in the step above is \\Win-0aeqj5brr86\dc. Take note of your network path, as it would be required when creating the Wazuh agent deployment GPO.
Create the Group Policy Objects
We perform the following steps to create the GPO in the AD and apply the policy to the organizational unit (OU) or the domain. We created a Wazuh OU, added the Windows endpoint, and then applied the GPO to the OU.
Steps:
1. Click on the Windows icon on the menu bar, then Windows Administrative Tools > Active Directory Users and Computers.
- Right-click on Wazuhtests.com and select New > Active Directory Users and Computers > Organizational Unit.
- Enter the name as
Wazuh, then click OK.
2. Click on the Find objects in Active Directory Domain Services icon, then select Wazuhtests.com from In.
- Click on Find > Computers > Find Now.
- Right-click on the WINDOWS 11 endpoint and select Move, then select Wazuh and click OK.
3. Press the Win+R on the keyboard and type gpmc.msc then click OK to launch the Group Policy Management Editor console on the domain controller.
4. Expand Forest:Wazuhtest.com, then Domains, then Wazuhtests.com in the Group Policy Management pane, and right-click on Group Policy Objects. Select New, name the policy Wazuh agent deployment, and use none as Source Starter GPO.
5. Right-click the Wazuh agent deployment policy and select Edit. A Group Policy Management Editor Wizard will open. Select Computer Configuration > Policies > Software Settings > Software installation and right-click New > Package.
6. Enter the network path for the shared folder we created earlier and select the Wazuh agent MSI installer. You will be presented with a prompt to select a deployment mode. Select Advanced and click OK.
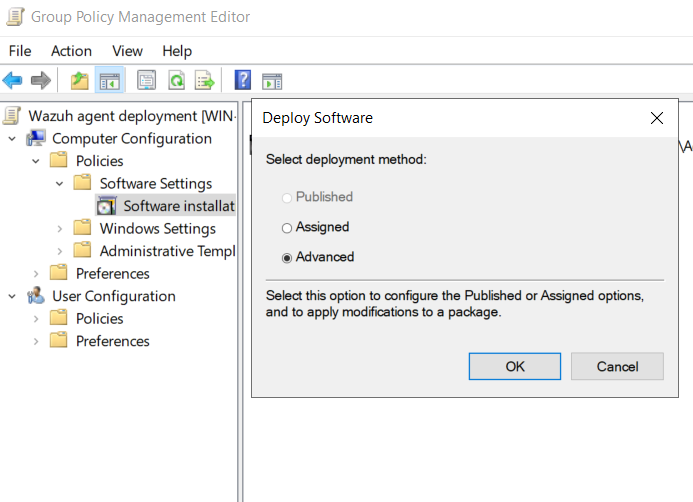
7. Add the custom.mst file in the Modification tab and click OK. Close the Group Policy Management Editor.
8. Apply the Wazuh agent deployment GPO to the OU where the Windows 11 endpoint resides. To perform this action, right-click on the OU name and select Link an Existing GPO, then select Wazuh agent deployment and click OK. Here, we link the GPO to Wazuh OU containing the Windows 11 endpoint.
9. Run the command below on the Windows 11 endpoint with administrative privilege to enforce the Wazuh agent deployment policy:
> gpupdate /force
For a non-interactive option, you can use the following command. This command suppresses the interactive prompt during the Group Policy update process. It is useful when initiating the update without user intervention or when scripting the process. However, remember that the installation or upgrade process may only take effect after a subsequent system reboot or when a user logs on:
> echo N | gpupdate /force
| Microsoft Windows [Version 10.0.22631.3155](c) Microsoft Corporation. All rights reserved. C:\Windows\System32>gpupdate /forceUpdating policy… Computer Policy update has completed successfully. The following warnings were encountered during computer policy processing: The Group Policy Client Side Extension Software Installation was unable to apply one or more settings because the changes must be processed before system startup or user logon. The system will wait for Group Policy processing to finish completely before the next startup or logon for this user, and this may result in slow startup and boot performance.User Policy update has completed successfully. For more detailed information, review the event log or run GPRESULT /H GPReport.html from the command line to access information about Group Policy results. Certain Computer policies are enabled that can only run during startup. OK to restart? (Y/N) |
Activate the Wazuh agent
We perform the following steps to create the group policy in the AD to activate the Wazuh agent. This is most helpful when there are many Wazuh agents, and it would be cumbersome to activate them individually.
1. Expand the domain Wazuhtests.com in the Group Policy Management pane and right-click on Group Policy Objects. Select New, name the policy Wazuh agent activate, and use None as Source Starter GPO.
2. Right-click the Wazuh agent activate policy and select Edit. The Group Policy Management Editor wizard will then open. Select Computer Configuration > Preferences > Control Panel Settings > Services.
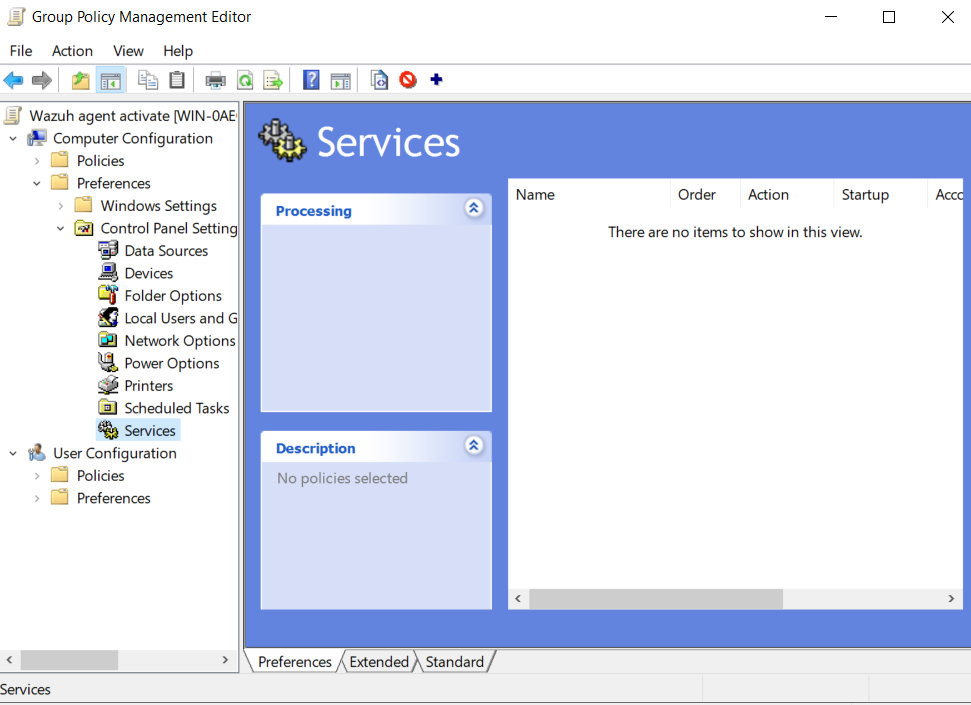
3. Right-click on Services and choose New > Service. Set the Service name as WazuhSvc and the Service action to Start service under the General tab.
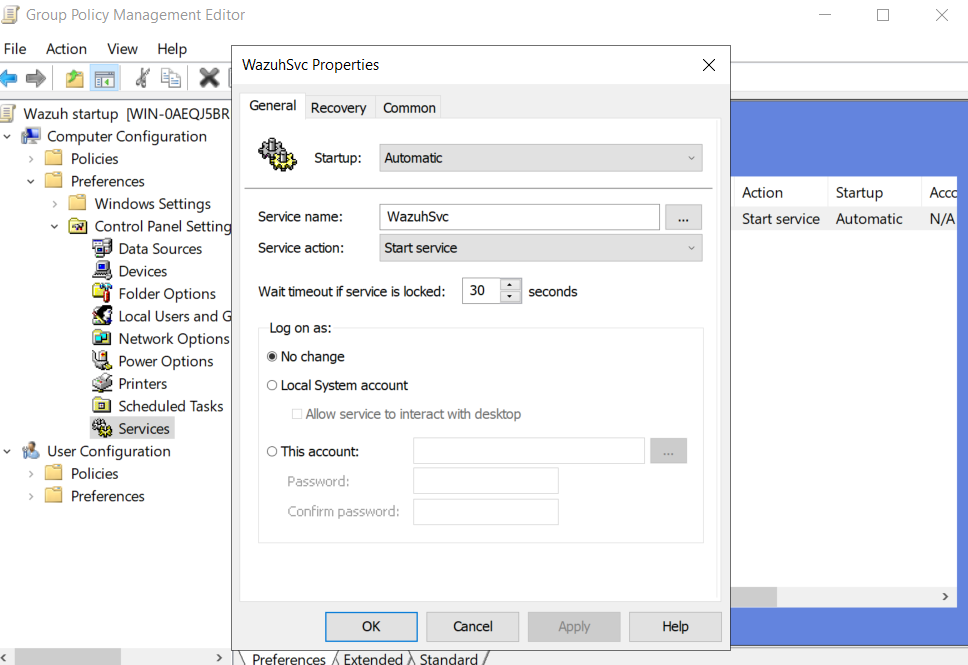
4. Select the Recovery tab and set all three recovery options to Restart the Service. Click OK and close the Group Policy Management Editor.
5. Apply the Wazuh agent activate GPO to the OU where the Windows 11 endpoint resides. To perform this action, right-click on the OU name and select link an Existing GPO, then select Wazuh agent activate and click OK. Here, we link the GPO to Wazuh OU containing the Windows 11 endpoint.
6. Run the command below with the local admin account on the Windows 11 endpoint to enforce the Wazuh agent activate policy:
> gpupdate /force
For a non-interactive option, you can use the following command. This command suppresses the interactive prompt during the Group Policy update process. It is useful when initiating the update without user intervention or when scripting the process. However, remember that the installation or upgrade process may only take effect after a subsequent system reboot or when a user logs on:
> echo N | gpupdate /force
C:\Users\wazuh> gpupdate /forceComputer Policy update has completed successfully. |
Alternatively, run the command below with admin privileges on the Windows 11 endpoint to start the Wazuh agent service:
> NET START WazuhSvc
Result:
Run the /var/ossec/bin/agent_control—l command on the Wazuh server terminal to show that the agent is registered on the Wazuh server.
[root@wazuh-server wazuh-user]# /var/ossec/bin/agent_control -l
Wazuh agent_control. List of available agents: ID: 000, Name: wazuh-server (server), IP: 127.0.0.1, Active/Local ID: 001, Name: Windows11, IP: any, Active List of agentless devices: [root@wazuh-server wazuh-user]#
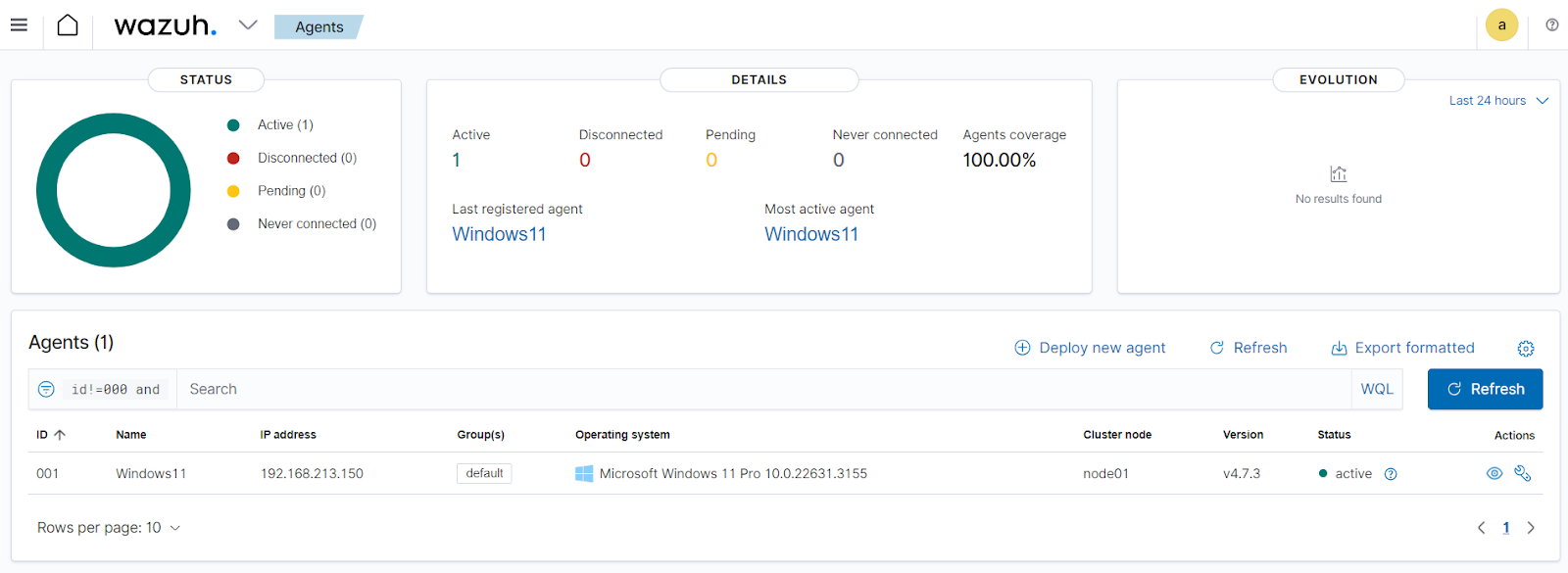
After starting the Wazuh agent service, we can visualize the agent on the Wazuh dashboard.
Conclusion
We demonstrate how to deploy the Wazuh agent in a Windows Active Directory infrastructure using the configured Transformation file generated with Orca and then applying it through a Group Policy (GPO).
Wazuh is an open source security monitoring platform that provides a unified security management approach across various IT assets. It provides capabilities such as security analytics, intrusion detection, file integrity monitoring, vulnerability detection, incident response, and more. To learn more about Wazuh, please check out our other blog posts and official guides.
References
- Using password authentication – Additional security options (wazuh.com)
- Microsoft Support: How to use Group Policy to remotely install software in Windows Server 2008
- Create an organizational unit (OU) in Microsoft Entra Domain Services – Microsoft Entra ID | Microsoft Learn
- Windows Dev Center: About Transforms