The DOGE Big Balls is a sophisticated ransomware variant linked to the Fog ransomware group, first observed in early 2025. It has affected organizations across various sectors, such as technology, education, and finance, by combining technical exploits with psychological manipulation. Delivered primarily through phishing campaigns containing malicious ZIP archives, the ransomware uses PowerShell scripts to download and execute payloads while exploiting vulnerable drivers for privilege escalation. Its attacks can cause severe operational disruptions, financial losses, and reputational damage.
In recent months, there has been a surge in DOGE Big Balls ransomware incidents, particularly targeting Windows-based environments. In addition to encrypting files and demanding ransom payments, the ransomware spreads fear and confusion through provocative ransom notes and data leak threats. In this blog post, we demonstrate how to detect DOGE Big Balls ransomware using Wazuh.
DOGE Big Balls ransomware behaviour
The ransomware is delivered through phishing emails containing malicious ZIP archives that execute PowerShell scripts when opened. After execution, DOGE Big Balls ransomware exhibits the following behavior:
- Privilege escalation: It exploits vulnerable drivers, such as
iqvw64e.sys, to gain kernel-level access without triggering security alerts. Notably, this driver is associated with CVE-2015-2291, a known vulnerability that allows attackers to bypass security controls and execute arbitrary code at the kernel level. - Reconnaissance: The ransomware collects detailed system information by executing a series of reconnaissance commands such as
systeminfo,net config Workstation,ipconfig /all, andwhoami. The output of these commands is written to a log file namedDbgLog.sys, which is stored locally in theC:\Users\<USER_NAME>\Downloadsdirectory, where the DOGE Big Balls ransomware was executed before potential exfiltration. This behavior allows the attackers to profile the victim’s environment and assess the value of the compromised system. - File encryption: It encrypts user files across the system while excluding critical Windows directories such as
C:\WindowsandC:\PerfLogs. - Ransom note creation: It leaves a ransom note named
RANSOMNOTE.txtin affected directories, often containing provocative or misleading content.
Analyzed sample
| Type | Value |
| SHA256 | 44b7eebf7a26d466f9c7ad4ddb058503f7066aded180ab6d5162197c47780293 4ad9216a0a6ac84a7b0b5593b0fc97e27de9cdfeb84ab7e5339ae5a4102100c0 30a6688899c22a3ce4c1b977fae762e3f7342d776e1aa2c90835e785d42f60c1 |
Infrastructure
We use the following infrastructure to demonstrate the detection of DOGE Big Balls ransomware with Wazuh:
- A pre-built, ready-to-use Wazuh OVA 4.12.0, which includes the Wazuh central components (Wazuh server, Wazuh indexer, and Wazuh dashboard). Follow this guide to download and set up the Wazuh virtual machine.
- A Windows 11 victim endpoint with the Wazuh agent 4.12.0 installed and enrolled to the Wazuh server.
Detection with Wazuh
Detection rules
We monitor system events on the Windows endpoint using Sysmon and create custom rules on the Wazuh server to detect the malicious behavior of DOGE Big Balls ransomware.
Windows endpoint
Follow the steps below to configure Sysmon on the monitored endpoint and forward logs in the Sysmon event channel to the Wazuh server for analysis.
- Download the latest version of Sysmon from the Microsoft Sysinternals page.
- Extract the compressed Sysmon file to your preferred location.
- Download the Sysmon configuration file using PowerShell as an administrator. Replace
<SYSMON_EXECUTABLE_PATH>with the path to your Sysmon executable.
> wget -Uri https://wazuh.com/resources/blog/emulation-of-attack-techniques-and-detection-with-wazuh/sysmonconfig.xml -OutFile <SYSMON_EXECUTABLE_PATH>\sysmonconfig.xml
- Switch to the folder containing the Sysmon executable and run the command below to install and start Sysmon:
> .\Sysmon64.exe -accepteula -i sysmonconfig.xml
- Add the following configuration within the
<ossec_config>block of the C:\Program Files (x86)\ossec-agent\ossec.conffile to forward Sysmon events to the Wazuh server:
<localfile>
<location>Microsoft-Windows-Sysmon/Operational</location>
<log_format>eventchannel</log_format>
</localfile>
6. Restart the Wazuh agent to apply the changes:
> Restart-Service -Name wazuh
Wazuh server
In this section, we create rules to detect the activities of the DOGE Big Balls ransomware on the monitored Windows endpoint.
- Create a CDB list
dog-big-balls-ransomwareof known DOGE Big Balls reconnaissance commands and save it to the/var/ossec/etc/listsdirectory on the Wazuh server.
# touch /var/ossec/etc/lists/doge-big-balls-ransomware
- Add the known DOGE Big Balls reconnaissance commands to the file:
net config Workstation: systeminfo: hostname: net users: ipconfig /all: route print: arp -A: netstat -ano: netsh firewall show state: netsh firewall show config: schtasks /query /fo LIST /v: tasklist /SVC: net start: DRIVERQUERY:
- Add a reference to the CDB list in the Wazuh server configuration file
/var/ossec/etc/ossec.conf. You can do this by specifying the path to the list within the<ruleset>block:
...
<ruleset>
<list>etc/lists/doge-big-balls-ransomware</list>
<ruleset>
...
- Create a file
doge_big_balls_ransomware_rules.xmlin the/var/ossec/etc/rules/directory:
# touch /var/ossec/etc/rules/doge_big_balls_ransomware_rules.xml
- Add the following detection rules to the
/var/ossec/etc/rules/doge_big_balls_ransomware_rules.xmlfile:
<group name="doge_big_ball,ransomware,">
<rule id="100020" level="10">
<if_sid>61613</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)[C-Z]:.*\\\\.*.exe</field>
<field name="win.eventdata.targetFilename" type="pcre2">(?i)[C-Z]:.*.\\\\DbgLog.sys</field>
<description>A log file $(win.eventdata.targetFilename) was created to log the output of the reconnaissance activities of the DOGE Big Balls ransomware. Suspicious activity detected.</description>
<mitre>
<id>T1486</id>
</mitre>
</rule>
<rule id="100021" level="8" timeframe="300" frequency="2">
<if_sid>61603</if_sid>
<list field="win.eventdata.commandLine" lookup="match_key">etc/lists/doge-big-balls-ransomware</list>
<description>The command $(win.eventdata.commandLine) is executed for reconnaissance activities. Suspicious activity detected.</description>
<options>no_full_log</options>
</rule>
<!-- Ransom note file creation -->
<rule id="100022" level="15" timeframe="300" frequency="2">
<if_sid>61613</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)[C-Z]:.*\\\\.*.exe</field>
<field name="win.eventdata.targetFilename" type="pcre2">(?i)[C-Z]:.*.\\\\readme.txt</field>
<description>DOGE Big Balls ransom note $(win.eventdata.targetFilename) has been created in multiple directories. Possible DOGE Big Balls ransomware detected.</description>
<mitre>
<id>T1486</id>
</mitre>
</rule>
<rule id="100023" level="15" timeframe="300" frequency="2" ignore="100">
<if_matched_sid>100020</if_matched_sid>
<if_sid>100021</if_sid>
<description>Possible DOGE Big Balls ransomware detected.</description>
<mitre>
<id>T1486</id>
</mitre>
</rule>
</group>
Where:
- Rule ID
100020is triggered when the ransomware starts gathering the victim’s system information by executing a series of reconnaissance commands. The output of these commands is written to theC:\Users\<USER_NAME>\Downloads\DbgLog.sys file. - Rule ID
100021is triggered when the ransomware executes several reconnaissance commands to gather the victim’s system information. - Rule ID
100022is triggered when multiplereadme.txtransom notes are created in multiple directories. - Rule ID
100023is triggered when rule IDs100020and100021are triggered within300seconds.
- Restart the Wazuh manager to apply changes.
# systemctl restart wazuh-manager
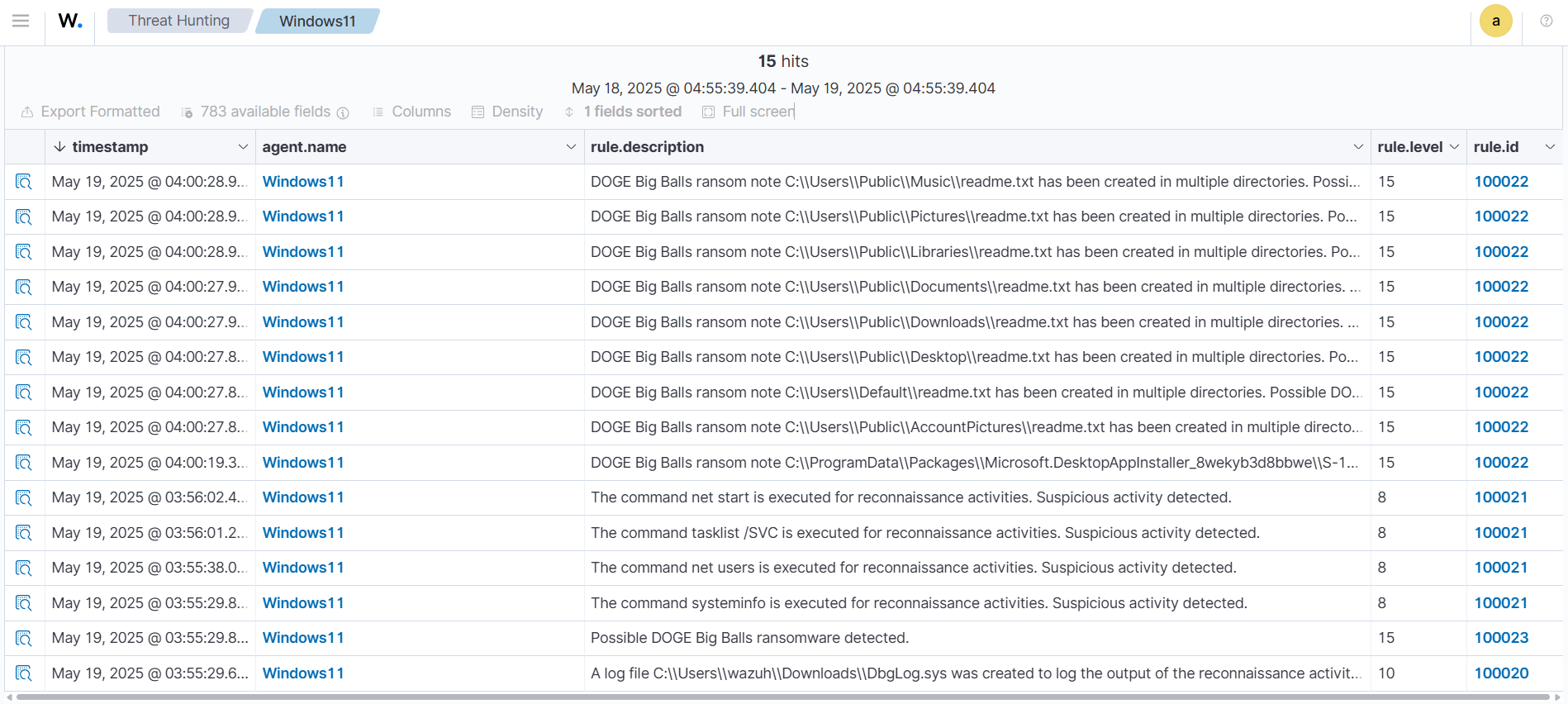
Wazuh dashboard detection alerts
Follow the steps below to view the alerts generated on the Wazuh dashboard when the DOGE Big Balls ransomware is executed on the Windows endpoint.
1. Navigate to Threat intelligence > Threat Hunting.
2. Click + Add filter. Then filter by rule.id.
3. In the Operator field, select is one of.
4. Search and select 100020, 100021, 100022, and 100023 in the Values field.
5. Click Save.
Removing malicious files with YARA integration
Ransomware renders infected endpoints unusable, making recovery difficult and time-consuming. A proactive defense involves detecting and removing malicious files before they are executed. We recommend enabling pre-execution protection using the Wazuh File Integrity Module (FIM) with VirusTotal or YARA integration. This approach matches the hash of downloaded files against threat intelligence databases and triggers a Wazuh Active Response script to remove malicious files before execution.
In this section, we illustrate how to detect and remove malicious files by leveraging Wazuh integration with YARA. We configure the Wazuh FIM module to track file modification or addition in a specific directory. When a change is detected in the monitored directory, the Wazuh Active Response module initiates a YARA scan, which detects potentially malicious files based on predefined rules.
Windows endpoint
Perform the steps below to set up the monitored endpoint for this integration.
- Install the following prerequisites:
- Python 3.12.2 or later (with
pippre-installed). Make sure to check the box Add python.exe to PATH, which places the Python interpreter in the execution path. - Microsoft Visual C++ 2015 Redistributable.
- Launch PowerShell with administrator privileges and download YARA:
> Invoke-WebRequest -Uri https://github.com/VirusTotal/yara/releases/download/v4.5.2/yara-v4.5.2-2326-win64.zip -OutFile v4.5.2-2326-win64.zip
- Extract the downloaded YARA file:
> Expand-Archive v4.5.2-2326-win64.zip
- Create a
yarafolder in theC:\Program Files (x86)\ossec-agent\active-response\bin\folder and copy the YARA binary into it:
> mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\' > cp .\v4.5.2-2326-win64\yara64.exe 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\'
- To download the YARA rules, use the
piputility to installvalhallaAPI. This API retrieves the public signature-based YARA ruleset:
> pip install valhallaAPI
- Run the below command to create a
file download_yara_rules.py, with the below script:
@'
from valhallaAPI.valhalla import ValhallaAPI
v = ValhallaAPI(api_key="1111111111111111111111111111111111111111111111111111111111111111")
response = v.get_rules_text()
with open('yara_rules.yar', 'w') as fh:
fh.write(response)
'@ | Set-Content -Path ".\download_yara_rules.py"
- Run the
download_yara_rules.pyscript file to download YARA rules:
> python download_yara_rules.py
- Create a folder rules in the
C:\Program Files (x86)\ossec-agent\active-response\bin\yarafolder and copy the rules into it:
> mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\' > cp yara_rules.yar 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\'
- Edit the downloaded YARA rule file
C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yarand add the following DOGE Big Balls ransomware rule:
rule _DOGE_Big_Balls_Ransomware {
meta:
description = "DOGE Big Balls ransomware executable detection"
author = "Anthony Faruna"
reference = "https://github.com/Neo23x0/yarGen"
date = "2025-05-19"
strings:
$s1 = "Failed to open file. ShellExecute error: %d" fullword ascii
$s2 = "AppPolicyGetProcessTerminationMethod" fullword ascii
$s3 = "\\RANSOMNOTE.txt" fullword ascii
$s4 = "Failed to get Desktop path." fullword ascii
$s5 = "%s\\Desktop\\RANSOMNOTE.txt" fullword ascii
$s6 = "Open RANSOMNOTE.txt?" fullword ascii
$s7 = " Type Descriptor'" fullword ascii
$s8 = "operator co_await" fullword ascii
$s9 = "User clicked OK." fullword ascii
$s10 = "api-ms-win-appmodel-runtime-l1-1-2" fullword wide
$s11 = "User clicked Cancel or closed the MessageBox." fullword ascii
$s12 = " Class Hierarchy Descriptor'" fullword ascii
$s13 = " Base Class Descriptor at (" fullword ascii
$s14 = "COM256" fullword ascii
$s15 = "F9]%c%" fullword ascii
$s16 = " Complete Object Locator'" fullword ascii
$s17 = "\"^4]%* " fullword ascii
$s18 = "(- d|X" fullword ascii
$s19 = "USERPROFILE" fullword ascii /* Goodware String - occured 154 times */
$s20 = "network down" fullword ascii /* Goodware String - occured 567 times */
condition:
( uint16(0) == 0x5a4d and filesize < 1000KB and ( 8 of them )
) or ( all of them )
}
- Monitor the
Downloadsfolder of all users in real-time by adding the below configuration within the<syscheck>block of theC:\Program Files (x86)\ossec-agent\ossec.conffile:
<directories realtime="yes">C:\Users\*\Downloads</directories>
Note
In this blog post, we only monitored the Downloads folder of all users. However, you can configure other folders you wish to monitor.
- Create a batch file
yara.batin theC:\Program Files (x86)\ossec-agent\active-response\bin\folder and copy the below script into it. The Wazuh Active Response module runs this script to perform YARA scans for malware detection and removal:
:: This script deletes the DOGE Big Balls ransomware executable as well as other malicious files matched by the YARA Rules
@echo off
setlocal enableDelayedExpansion
reg Query "HKLM\Hardware\Description\System\CentralProcessor\0" | find /i "x86" > NUL && SET OS=32BIT || SET OS=64BIT
if %OS%==32BIT (
SET log_file_path="%programfiles%\ossec-agent\active-response\active-responses.log"
)
if %OS%==64BIT (
SET log_file_path="%programfiles(x86)%\ossec-agent\active-response\active-responses.log"
)
set input=
for /f "delims=" %%a in ('PowerShell -command "$logInput = Read-Host; Write-Output $logInput"') do (
set input=%%a
)
set json_file_path="C:\Program Files (x86)\ossec-agent\active-response\stdin.txt"
set syscheck_file_path=
echo %input% > %json_file_path%
FOR /F "tokens=* USEBACKQ" %%F IN (`Powershell -Nop -C "(Get-Content 'C:\Program Files (x86)\ossec-agent\active-response\stdin.txt'|ConvertFrom-Json).parameters.alert.syscheck.path"`) DO (
SET syscheck_file_path=%%F
)
set yara_exe_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\yara64.exe"
set yara_rules_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yar"
echo %syscheck_file_path% >> %log_file_path%
for /f "delims=" %%a in ('powershell -command "& \"%yara_exe_path%\" \"%yara_rules_path%\" \"%syscheck_file_path%\""') do (
echo wazuh-yara: INFO - Scan result: %%a >> %log_file_path%
:: Deleting the scanned file.
del /f "%syscheck_file_path%" >nul 2>&1
if exist "%syscheck_file_path%" (
echo wazuh-yara: INFO - Error removing threat: %%a >> %log_file_path%
) else (
echo wazuh-yara: INFO - Successfully deleted: %%a >> %log_file_path%
)
)
exit /b
- Restart the Wazuh agent to apply the changes:
> Restart-Service -Name wazuh
Wazuh server
We configure rules, custom decoders, and the Wazuh Active Response module to capture alerts related to the addition and removal of the ransomware sample.
- Add the custom rules below to the
/var/ossec/etc/rules/local_rules.xmlfile. These rules trigger alerts when files are added or modified in theDownloadsfolder on the monitored endpoint.
<group name="syscheck,">
<rule id="100024" level="7">
<if_sid>550</if_sid>
<field name="file" type="pcre2">(?i)C:\\Users.+Downloads</field>
<description>File modified in the Downloads folder.</description>
</rule>
<rule id="100025" level="7">
<if_sid>554</if_sid>
<field name="file" type="pcre2">(?i)C:\\Users.+Downloads</field>
<description>File added to the Downloads folder.</description>
</rule>
</group>
Where:
100024is triggered when a file is modified in theDownloadsfolder.100025is triggered when a file is added to theDownloadsfolder.
- Add the following configuration within the
<ossec_config>block of the/var/ossec/etc/ossec.conffile:
<command>
<name>yara</name>
<executable>yara.bat</executable>
<timeout_allowed>no</timeout_allowed>
</command>
<active-response>
<command>yara</command>
<location>local</location>
<rules_id>100024,100025</rules_id>
</active-response>
The Wazuh Active Response module runs the yara.bat script when a file is added or modified in the Downloads folder.
Where:
<name>specifies thatyarais the name of the command being called in the<active-response>block.<executable>specifies thatyara.batis the executable file to run.<command>specifies the command that the Active Response module will use.- The
<active response>block calls the<command>block when the rule ID100024or100025is triggered. <location>specifies where the Active Response script is executed.
- Add the following decoders to the
/var/ossec/etc/decoders/local_decoder.xmlfile to decode the logs generated by the Active Response script:
<decoder name="yara_decoder">
<prematch>wazuh-yara:</prematch>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Scan result: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Successfully deleted: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Error removing threat: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
- Create custom rules in the
/var/ossec/etc/rules/local_rules.xmlto generate alerts when response actions are taken:
<!-- Rule for the decoder (yara_decoder) -->
<group name="yara,">
<rule id="100026" level="0">
<decoded_as>yara_decoder</decoded_as>
<description>Yara grouping rule</description>
</rule>
<!-- YARA scan detects a positive match -->
<rule id="100027" level="12">
<if_sid>100026</if_sid>
<match type="pcre2">wazuh-yara: INFO - Scan result: </match>
<description>File "$(yara_scanned_file)" is a ransomware. Yara rule: $(yara_rule)</description>
</rule>
<!-- Wazuh successfully deletes malware with a positive match -->
<rule id="100028" level="12">
<if_sid>100026</if_sid>
<match type="pcre2">wazuh-yara: INFO - Successfully deleted: </match>
<description>Successfully removed "$(yara_scanned_file)" by active response due to YARA rule $(yara_rule) positive match</description>
</rule>
<!-- Wazuh encounters an error when deleting malware with a positive match -->
<rule id="100029" level="12">
<if_sid>100026</if_sid>
<match type="pcre2">wazuh-yara: INFO - Error removing threat: </match>
<description>Error removing "$(yara_scanned_file)". YARA rule: $(yara_rule)</description>
</rule>
</group>
Where:
100026is the base rule for detecting YARA related events.100027is triggered when YARA scans and detects the DOGE Big Balls ransomware executable.100028is triggered when the executable has been successfully removed by the Wazuh Active Response module.100029is triggered when the executable is not removed successfully by the Wazuh Active Response module.
- Restart the Wazuh manager for the changes to take effect:
# systemctl restart wazuh-manager
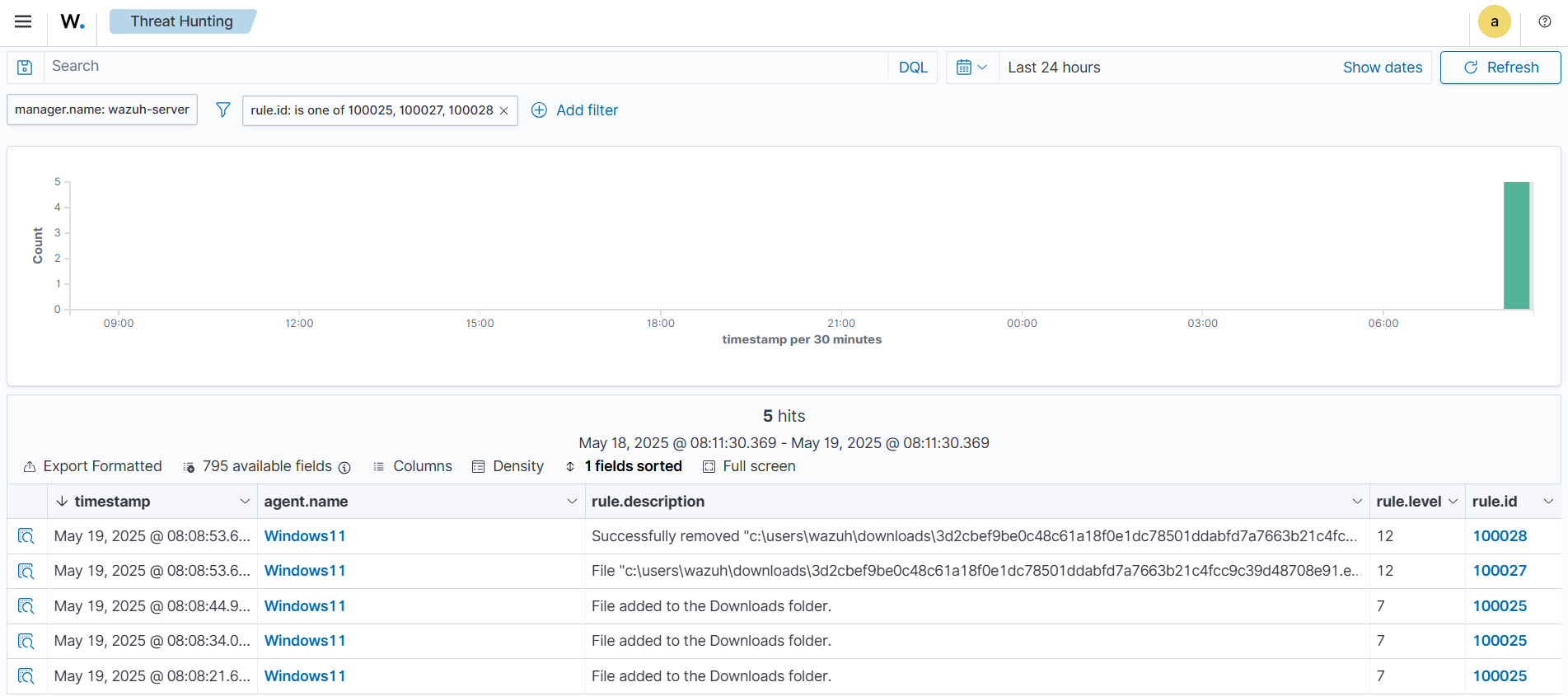
Visualizing the detection alerts
When the DOGE Big Balls ransomware executable is added to the Downloads folder of the victim endpoint and removed by the Active Response module, alerts are generated on the Wazuh dashboard.
To view these alerts:
- Navigate to Threat intelligence > Threat Hunting.
- Click + Add filter. Then filter by
rule.id. - In the Operator field, select
is one of. - Search and select rule IDs
100025,100027, and100028in the Values field. - Click Save.
Conclusion
This blog post shows how to detect DOGE Big Balls ransomware on a Windows endpoint using Wazuh. We leverage the Wazuh data analysis engine to create rules that identify the malicious activities associated with the ransomware. Also, we demonstrate how to use the Wazuh FIM and Active Response capabilities with YARA integration to respond to threats.
Wazuh is a free and open source security solution that provides a wide range of capabilities to monitor and protect your infrastructure against various threats. If you have questions about this blog post or need assistance with Wazuh, we encourage you to join our Slack community, where our team is ready to support you.
