Wazuh is an open source unified XDR and SIEM platform that offers compatibility and integration methods with other security platforms. Integrating Wazuh with other platforms enables you to flexibly manage Wazuh data and enhance your security monitoring approach.
Wazuh integrates with other SIEM and XDR platforms such as Splunk and Elastic Stack. Previously, these integrations depended on vendor-specific plugins built and maintained by Wazuh, which posed challenges in keeping up-to-date with third-party platform releases. We have developed new integration methods for these security platforms to address this issue.
Previous integration methods
In Wazuh 4.5 and lower, Wazuh develops plugins for Splunk and Elastic Stack that allow you to transfer and visualize analyzed Wazuh data to these third-party SIEM and XDR platforms.
- Wazuh app for Splunk: The Wazuh app for Splunk is a free and open source plugin that allows you to visualize and analyze Wazuh data directly on Splunk. The installation package for this plugin is shipped in two ways. First, as an all-in-one installation with the Splunk indexer, Splunk forwarder, the Wazuh app for Splunk, and the Wazuh manager on a single server. Then, as a distributed installation with the Splunk forwarder and the Wazuh manager on one server and the rest of the Splunk components installed on different servers.
- Wazuh Kibana plugin: The Wazuh Kibana plugin provides a comprehensive user interface that allows you to visualize and analyze data collected by Wazuh agents in Elastic Stack. This integration uses the Elastic Stack basic license option. This version contains everything in the open source version under the Apache 2.0 license, along with features such as Elastic Stack Security, Kibana alerting, and others.
New integration methods
Starting from Wazuh 4.6 releases, we no longer provide support for the Wazuh app for Splunk and the Wazuh Kibana plugin. Nonetheless, note that all technical steps for performing these integrations are still available in our documentation up to version 4.5.
The new integrations are now possible from the Wazuh server and Wazuh indexer components.
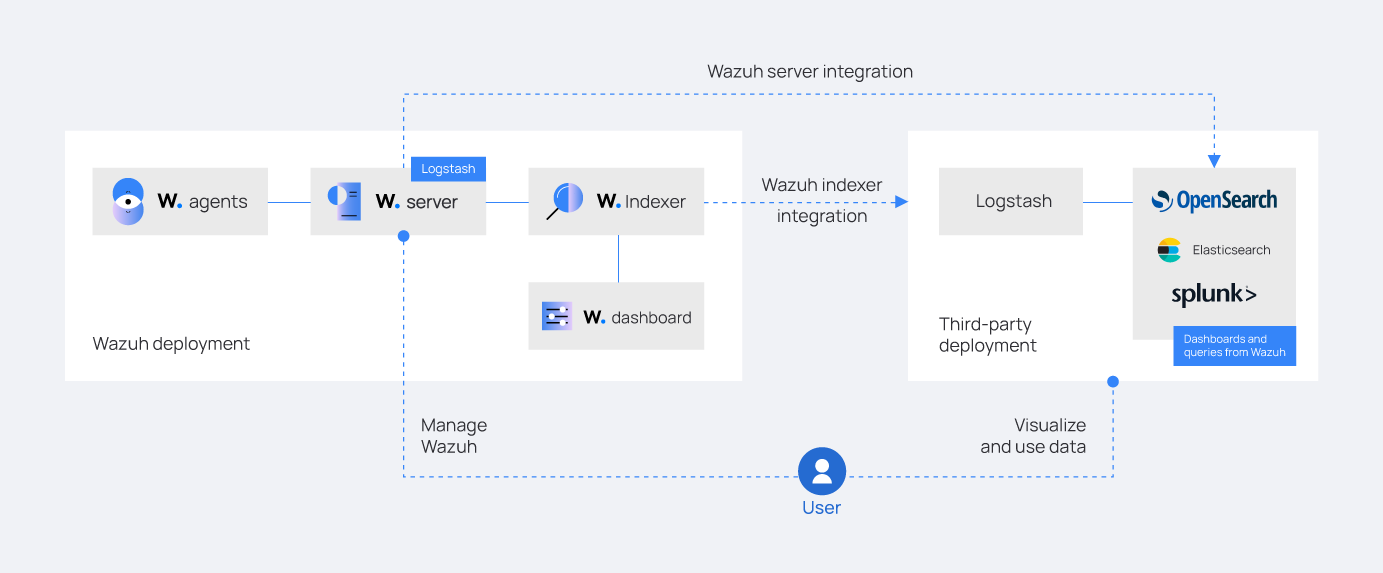
Wazuh indexer integration
We recommend this integration method if you want to continue indexing security data in Wazuh and archive it in a data lake for storage or out-of-band analysis. However, the Wazuh indexer and the third-party platform indexer generate indices for the same alerts, leading to index redundancy and high resource utilization.
The Wazuh indexer integration relies on Logstash as a data forwarder to ingest events from indices on the Wazuh indexer and send them to:
It requires you to install Logstash on a dedicated server or on the server hosting the third-party indexer.
Wazuh server integration
We recommend this integration method if resource constraints prevent hosting the third-party security platform indexer and the Wazuh indexer. This is useful for environments with large-scale Wazuh operations that generate a large volume of alerts.
The Wazuh server integration operates by reading the JSON alerts file and forwarding the alerts to the third-party platforms using appropriate data forwarders like:
- Logstash for Elastic Stack, OpenSearch, and Splunk.
- Splunk forwarder for Splunk.
For either approach, the data forwarder needs to be installed on the same server as the Wazuh server. When performing this integration in a distributed environment, it is necessary to have a data forwarder for each Wazuh server.
Data forwarders
Wazuh adopts Splunk forwarder and Logstash as data forwarders because of their flexibility and support for various data sources. They are used to transfer data from the JSON alert files on the Wazuh server and indices on the Wazuh indexer to third-party platforms.
Logstash integrates with various solutions and allows you to configure and manage the entire data ingestion pipeline. This solves the issues of compatibility between Wazuh and third-party platform versions.
Splunk forwarders offer dependable and secure data gathering from remote sources by forwarding this data into the Splunk indexer for consolidation and indexing. It provides robust mechanisms to parse, filter, and enrich the collected data. This enables users to extract relevant information, apply custom formatting, and enhance the data’s overall quality and usefulness.
Conclusion
From Wazuh version 4.6, the Wazuh app for Splunk and the Wazuh Kibana plugin will no longer be supported. In the new integration methods, Wazuh uses Logstash and Splunk forwarders as data forwarders. They help transfer data from the Wazuh server or Wazuh indexer to the third-party security platforms, allowing for direct ingestion of events and optimizing compatibility with various platforms.
The Wazuh server and indexer integrations provide solutions that fit diverse operational needs and advanced security analysis. In the near future, we will release blog posts that showcase use cases for these integrations.
References