Since version 4.3.0, Wazuh introduced a new technique for collecting logs from macOS endpoints using the unified logging system (ULS). ULS is available in macOS 10.12 and later. Wazuh uses the CLI log tool to gather these logs in syslog format. This tool provides an interface for log collection in a filtered way using the unified logging system. For a better understanding of how this process works, visit our documentation on how to collect macOS ULS logs.
From version 4.4.2, Wazuh added new decoders and rules to the Wazuh server to enhance the analysis of the logs collected by the agent on macOS endpoints. The Wazuh macOS agents contain a default configuration to collect the appropriate logs. This blog post explains the agent configuration, decoders, and rules and shows some use cases.
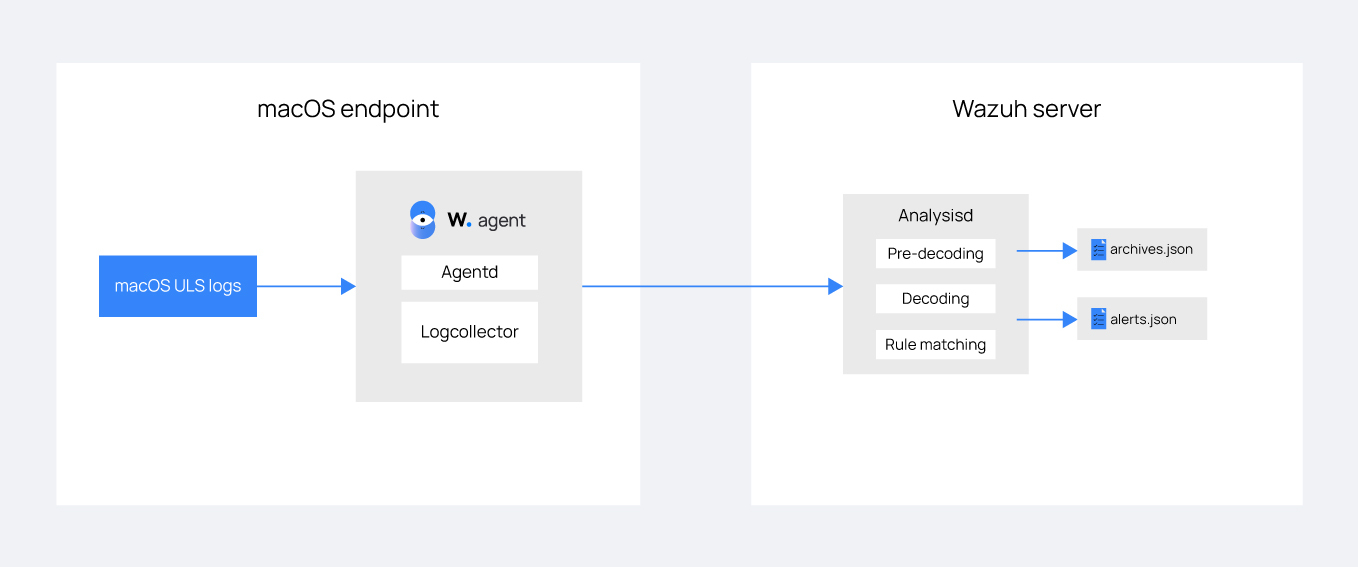
Figure 1: Wazuh log collection and analysis process for macOS endpoints.
Agent configuration
The Wazuh agent uses the log tool to collect logs. You can use the log tool in the Terminal, followed by options filters to control what logs you want to see. For example, running the command below will display all the logs the operating system generates:
% log stream
The log tool generates a lot of events, so it is necessary to filter for only important events. For example, to see only sudo events, you can run the command below:
% log stream --process="sudo"
The command uses filters to ensure that the log tool shows only the events of interest. Using the same technique, the Wazuh agent uses the following configuration included in macOS agents to collect only relevant logs:
<localfile> <location>macos</location> <log_format>macos</log_format> <query type="trace,log,activity" level="info">(process == "sudo") or (process == "sessionlogoutd" and message contains "logout is complete.") or (process == "sshd") or (process == "tccd" and message contains "Update Access Record") or (message contains "SessionAgentNotificationCenter") or (process == "screensharingd" and message contains "Authentication") or (process == "securityd" and eventMessage contains "Session" and subsystem == "com.apple.securityd")</query> </localfile>
This configuration is included by default and allows the Wazuh agent to collect logs that support different event types. The agent runs the log tool and passes the included filters to specify the monitored processes. You can find the configuration in the /Library/Ossec/etc/ossec.conf file on macOS endpoints. The log collection configuration supports only sudo, SSH, security sessions, and authentication events.
Note: Upgrading the Wazuh agent from a version that does not include this enhancement to a supported version will not update the configuration. If you want to apply the default configuration, you can include the configuration above in your agent configuration file (for Wazuh 4.3.0 and above ) or uninstall and install the agent.
Decoders
You can find the decoders for the events collected by Wazuh macOS agents in the /var/ossec/ruleset/decoders/0580-macos_decoders.xml file on the Wazuh server. The decoders in this file correspond to the log types that the default agent configuration supports. However, the Wazuh server uses the syslog decoders for sudo and SSH events because these events are common across UNIX variants including macOS.
Rules
Wazuh now has out-of-the-box rules that trigger alerts for ULS logs collected by the Wazuh agent on macOS endpoints. The rules provide coverage for common security events on macOS endpoints. You can find the rules in the /var/ossec/ruleset/rules/0960-macos_rules.xml file on the Wazuh server. The Wazuh server uses the syslog rules for sudo and SSH events from macOS endpoints.
Use cases
We focus on specific use cases, which include monitoring sudo events, tracking permission changes with TCCD (Transparency, Consent, and Control Daemon), and monitoring screen sharing activity on macOS endpoints.
Prerequisites
- A pre-built, ready-to-use Wazuh OVA 4.4.4: Follow this guide to download the virtual machine (VM). This VM hosts the Wazuh central components (Wazuh server, Wazuh indexer, and Wazuh dashboard).
Wazuh agent 4.4.2 (or later) installed on a macOS endpoint and enrolled to the Wazuh server. The macOS version should be 10.12 or later.
Note: You need two macOS endpoints to perform the screen sharing authentication attempts in the third use case.
Monitoring sudo events
The rules and decoders for macOS sudo events are the same as for other syslog events that the Wazuh agent collects from other UNIX-based operating systems. However, the agent configuration on macOS endpoints now supports collecting events that will trigger the appropriate rules. Follow the steps below to see the alerts displayed on the Wazuh dashboard.
macOS endpoint
- Open the Terminal and run the command below to switch from a normal user account to the root user:
% sudo -i
Wazuh dashboard
Click on the macOS agent from the Agents tab and click on Security events on the Wazuh dashboard. Click on the Events tab to view the alerts which will trigger rules IDs within the range 5401 – 5406.
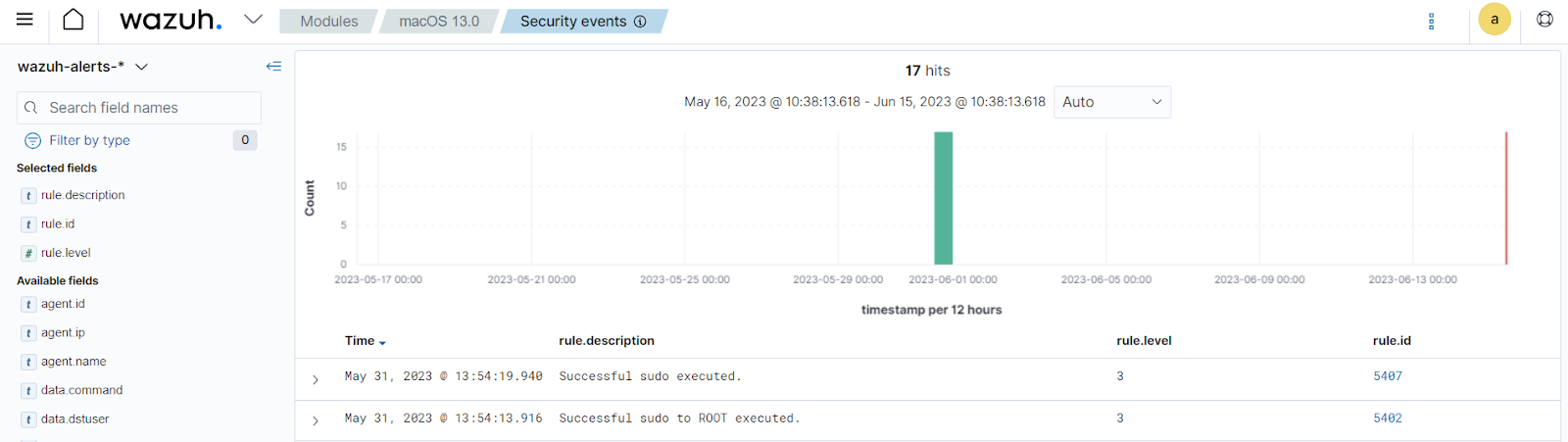
Figure 2: Wazuh dashboard displaying macOS sudo events.
Tracking permission changes with TCCD (Transparency, Consent, and Control Daemon)
TCC is a macOS feature that limits or regulates an application’s access to particular components of the operating system. The components include full disc access, location services, contacts, camera, accessibility, microphone, and other privacy-related permissions. TCCD is the process that enforces TCC permissions on macOS endpoints.
Wazuh agents on macOS endpoints collect logs that indicate any change to application permissions. The Wazuh server analyzes these logs and triggers alerts which the Wazuh dashboard displays.
To simulate this use case, you can update the permissions of an application in the Settings app on a macOS endpoint. In this simulation, we update the Full Disk Access permission for the Terminal application in the Security and Privacy menu. Follow the steps below to see the events on the Wazuh dashboard.
macOS endpoint
- Open the System Preferences application and open the Security and Privacy settings.
- Click the lock icon to make changes, and enter your password if prompted.
- Select the Privacy tab, scroll down to Full Disk Access and click on it.
Toggle the Terminal checkbox off and on. This will disable and enable the full disk permissions for the Terminal application.
Figure 3: Changing permissions on the macOS endpoint to trigger TCCD events.
Wazuh dashboard
Click on the macOS agent from the Agents tab and click on Security events on the Wazuh dashboard. Click on the Events tab to view the alerts.
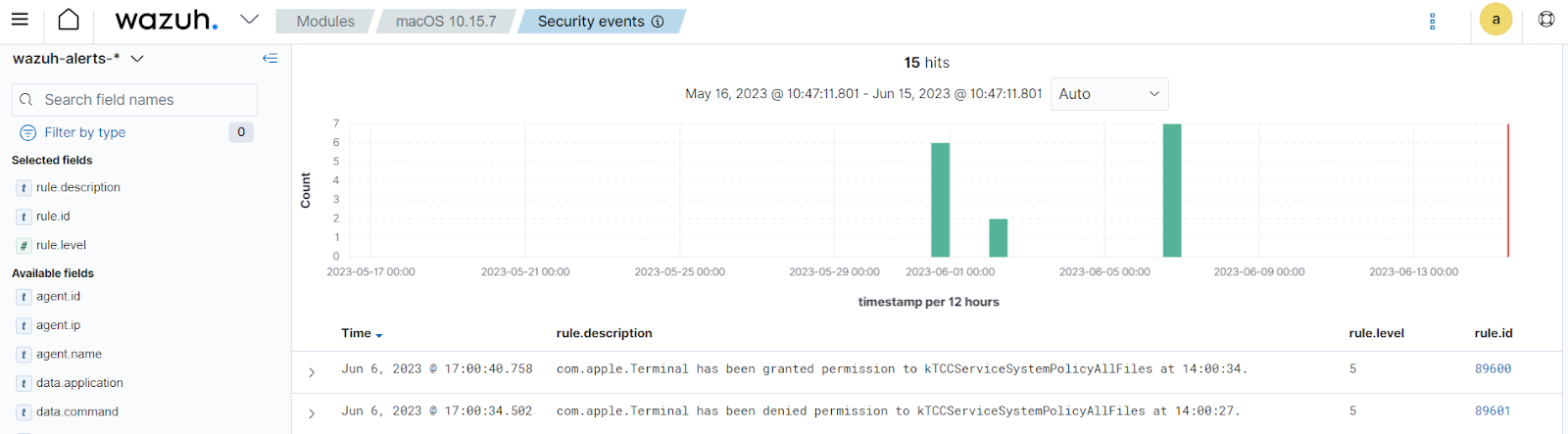
Figure 4: Wazuh dashboard displaying macOS TCCD events.
The Wazuh server triggers the alert 89601 when a user denies an application permission to use a resource. The alert 89600 indicates that the user granted the application permission to use the identified component. In addition to this, users can use these rules as a foundation for other rules that monitor specific system components.
Monitoring screen sharing authentication activities
Screen sharing is a macOS feature that allows users to share their screen and audio over a network with other devices. This feature can allow users to view and control devices remotely.
The Wazuh server triggers alerts for successful and unsuccessful attempts when anyone attempts to screen share to a monitored macOS endpoint. Follow the steps below to simulate screen sharing alerts on macOS Ventura. For other macOS versions, please visit the macOS user guide and select the appropriate version.
macOS endpoint 1 (with Wazuh agent installed)
- Choose Apple menu > System Settings, click General in the sidebar, then click Sharing on the right. You may need to scroll down to see this option.
- Turn on Screen Sharing, then click the Info button on the right.
- Note the name and address of the macOS endpoint (it’s listed at the top), then click Done. The name looks like iMac (7) or Joe’s MacBook Pro. The address looks like
vnc://[IPAddress]orvnc://[Name.Domain].
macOS endpoint 2
Use either the first or second step below before performing the third step.
- Connect using the name: Click the Finder icon in the Dock to open a Finder window. In the Locations section of the sidebar, click Network, double-click the macOS endpoint you want to share, then click Share Screen. If no items appear in the Locations section of the sidebar, hold the pointer over the word Locations, then click the arrow.
- Connect using the address: In the Finder application, choose Go > Connect to Server, enter the address of the macOS endpoint you want to share, then click Connect.
- After using any of the methods above, you may be prompted to enter your username and password, do so, and click Sign In. The screen sharing session starts if both computers are logged in using the same Apple ID. If they’re not, you’re prompted to enter the username and password of a user who is allowed screen sharing access on that computer. Alternatively, you can request permission to share the screen if the computer allows it.
Wazuh dashboard
Click on the macOS agent from the Agents tab and click on Security events on the Wazuh dashboard. Click on the Events tab to view the alerts. The screenshot below shows the alert for rule IDs 89606 and 89607. These alerts indicate failed and successful attempts, respectively.
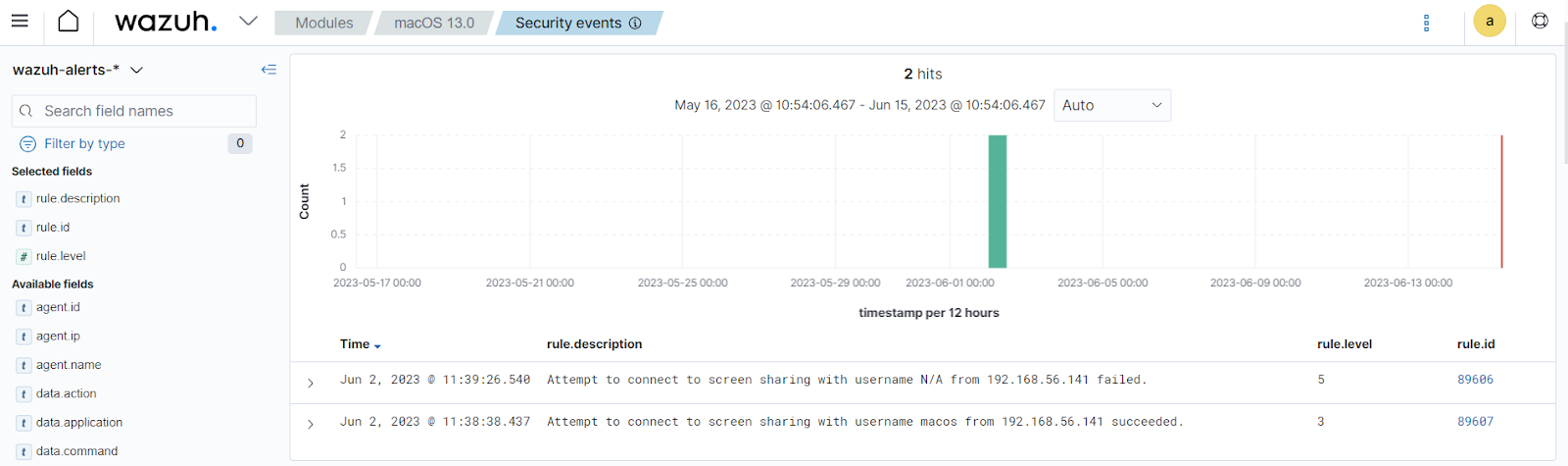
Figure 5: Wazuh dashboard displaying macOS screen sharing events.
Conclusion
This blog has highlighted how Wazuh provides visibility for macOS endpoints using the Unified Logging System (ULS). The enhanced log collection, decoders and rules helps security teams to track user and application activity on macOS endpoints. The enhancements provide visibility into user login and logout events, screensharing authentication events, security sessions and changes in application permissions.Connect with us through any of our community channels if you have any questions or comments.
