Wazuh is an open source security platform that helps you to secure your environment infrastructure by monitoring hosts at an operating system and application level.
With the emergence of Web 2.0 came the exchange of information through social networks and business growth using the Web as a tool to create business and offer services. It also means that hacking activity has increased dramatically by attackers who pursue an economic or strategic objective.
Today, a significant percentage of economic activity depends on digital technologies which are exposed to cyber attacks and security breaches that can cause disruptions and large monetary losses for companies as well as damage to their reputations. A study conducted by the Ponemon Institute, the 2018 cost of a Data Breach Study[1], found that the average cost of a data breach study is $3.86 million.
One of the most effective strategies for to secure your environment mitigating and minimizing the effects of a cyber attack is prevention and detection.
How can Wazuh help prevent attacks on your systems and detect anomalies?
Wazuh can secure your infrastructure with the following capabilities:
File Integrity Monitoring
Wazuh monitors the file system, identifying changes in content, permissions, ownership, and the attributes of files. In addition, it can identify the user, the program name, or the process that made the changes. With the ability to perform this monitoring in real time, Wazuh can generate an alert in real time that will inform the user that these changes have been made.
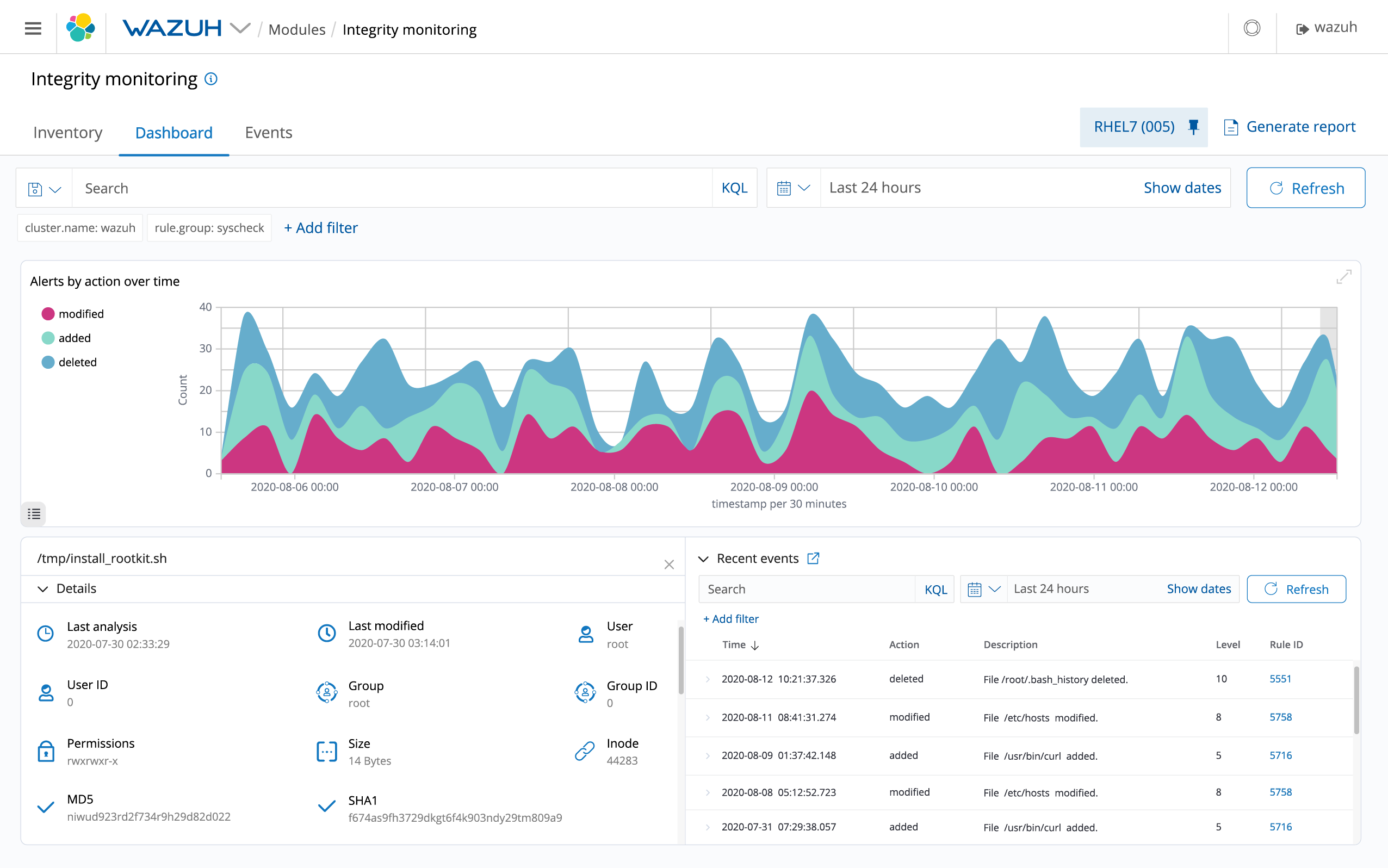
The component of Wazuh responsible for this task is called Syscheck. More info: (Wazuh Documentation).
Automated log analysis
Wazuh can read operating system and application logs and securely send them to a central manager for rule-based analysis and storage. Wazuh rules help you to report application or system errors, misconfigurations, attempted and/or successful malicious activity, policy violations, and a variety of other operational and security issues.
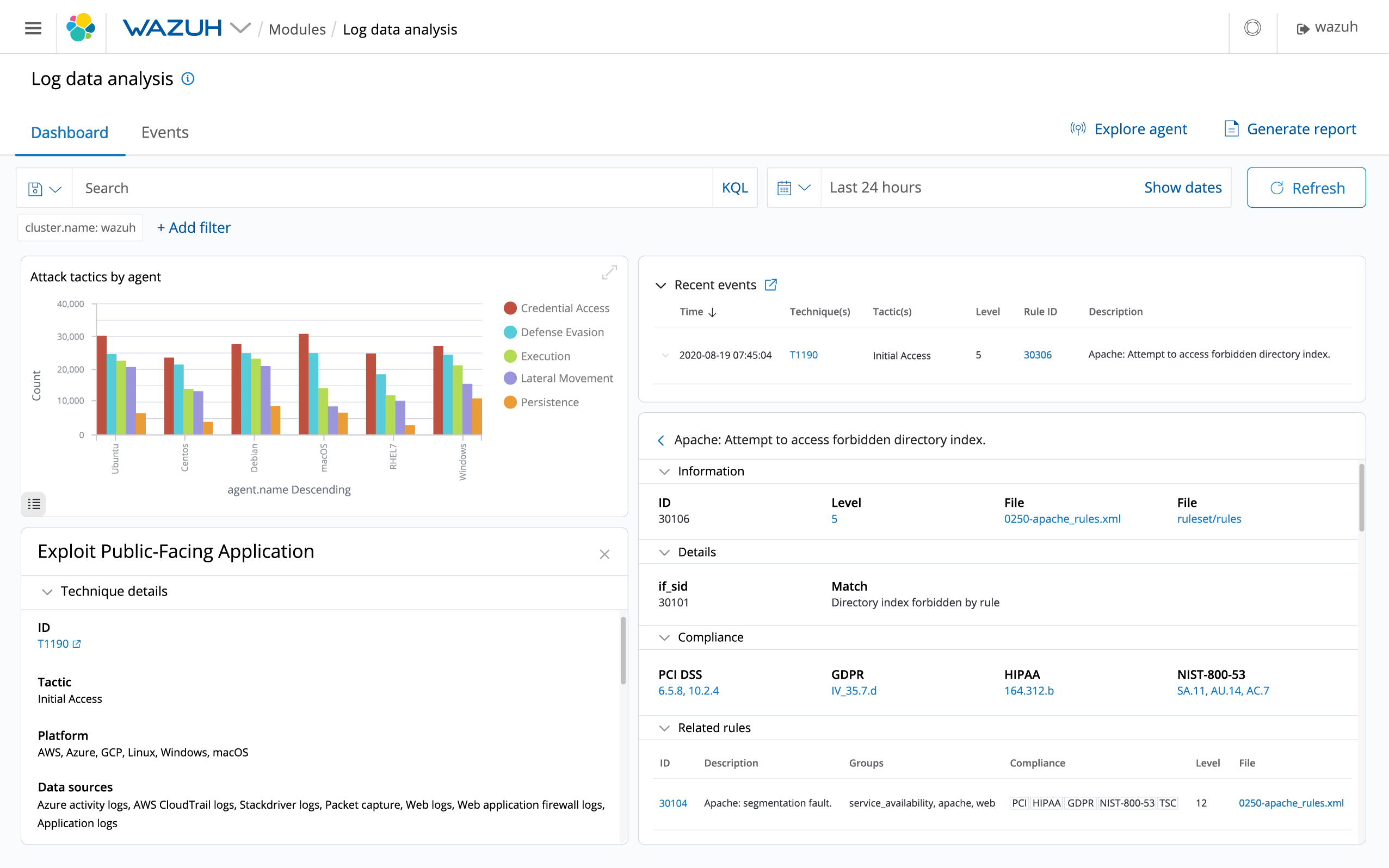
More info: (Wazuh Documentation).
Policy and compliance monitoring
Policy monitoring is the process of verifying that all system conform to a set of predefined rules regarding configuration settings and approved application usage.
The component of Wazuh responsible for this task is called Rootcheck. Wazuh also uses 2 integrations for policy and compliance monitoring: OpenSCAP and CIS-CAT.
- Rootcheck allows defining policies to check if the agents meet the requirements specified.
- OpenSCAP is an integration that allows you to verify compliance with your security policies, performs vulnerability assessments (identifying and classifying vulnerabilities) as well as custom system checks.
- CIS-CAT is a tool based on CIS. An entity dedicated to safeguarding private and public organizations against cyber threats. This entity provides CIS benchmarks, which are a recognized global standard and best practices for securing IT systems and data against cyber attack. A CIS-CAT scan targets systems and generates a report comparing the system settings to the CIS benchmarks.
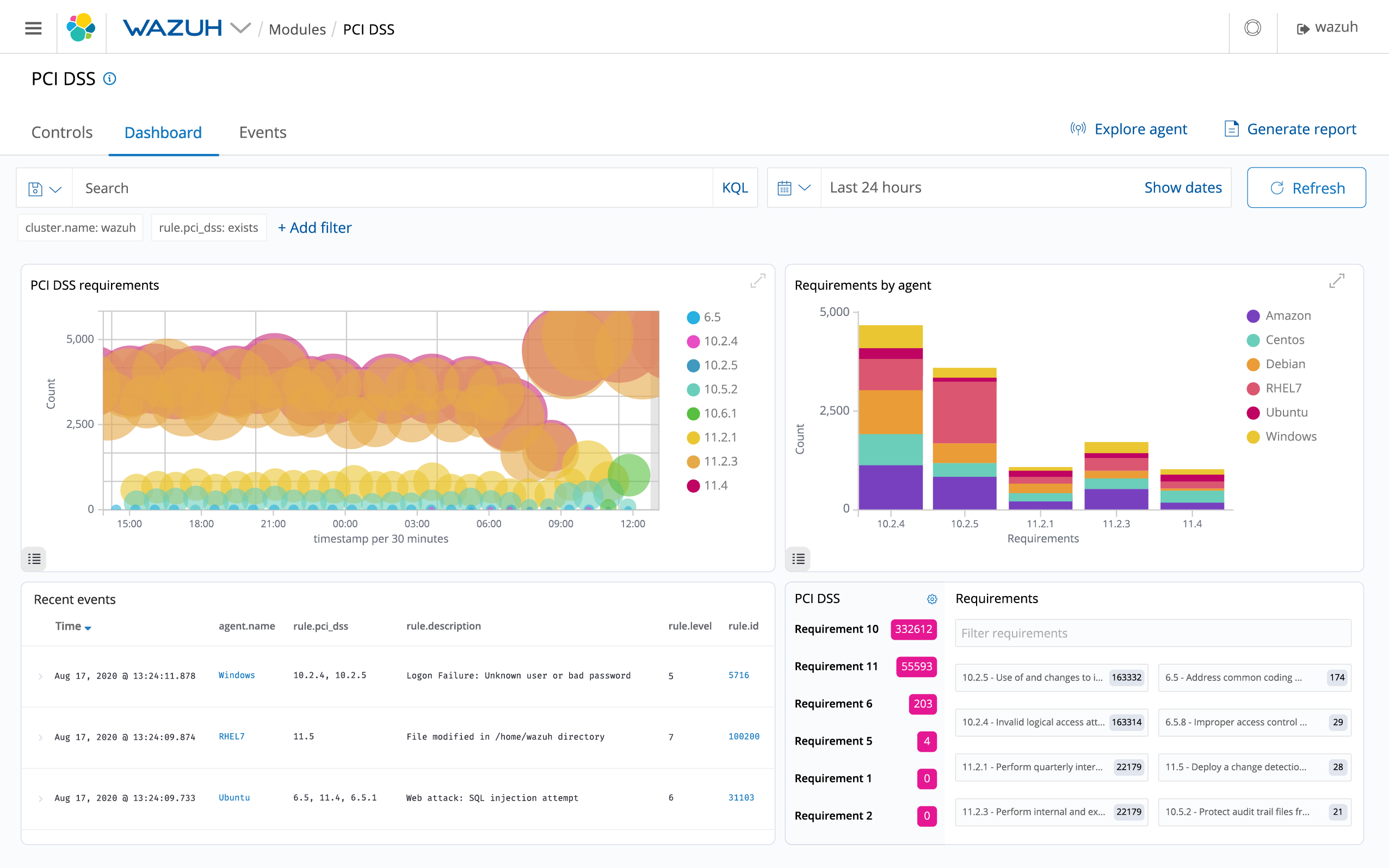
More info: (Wazuh Documentation).
Intrusion and anomaly detection
Anomaly detection refers to the action of finding patterns in the system that do not match the expected behavior. The platform uses a broad spectrum approach to finding anomalous patterns that indicate possible intruders.
The components responsible for this task are Rootcheck and Syscheck.
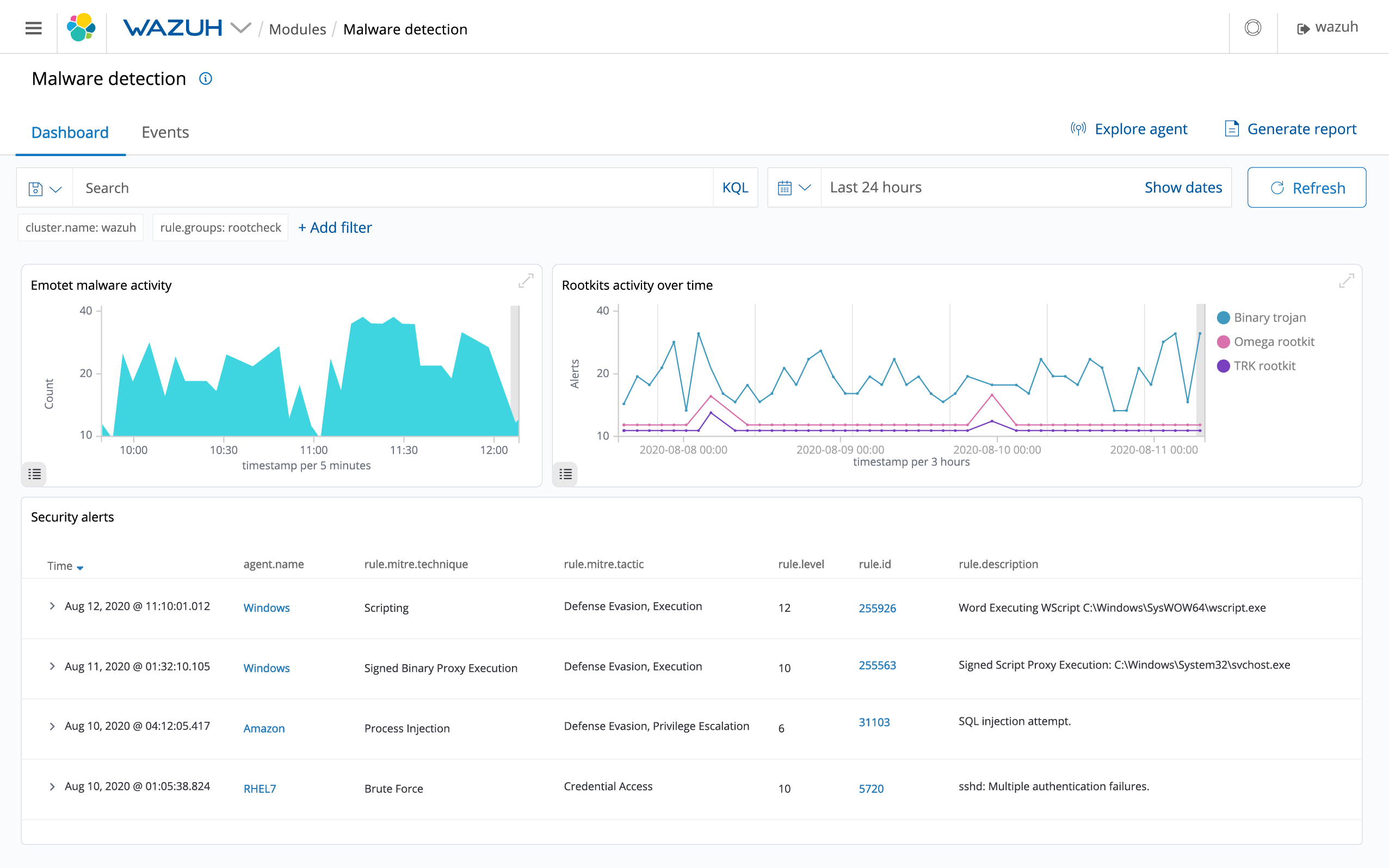
More info: (Wazuh Documentation).
Wazuh has many possibilities to offer. We invite you to try them!
If you need some help to secure your environment remember we have a Slack channel you can join, a public mailing list and GitHub repositories.