Rsyslog is a high-performance, versatile log processing system commonly used in UNIX and Linux environments. It is responsible for handling log messages generated by various system components and applications. It can then forward these messages to different destinations, such as files, databases, and remote servers.
Wazuh, an open source security monitoring platform, collects and analyzes log data from various sources and can be configured to receive events from Rsyslog. This implementation is particularly useful when monitoring devices on which the Wazuh agent can’t be installed. This blog post guides you through the process of forwarding Rsyslog events to Wazuh for enhanced security monitoring.
Infrastructure
We use the following infrastructure to demonstrate how to forward Rsyslog events to Wazuh.
- A pre-built, ready-to-use Wazuh OVA 4.8.1. Follow this guide to download the virtual machine (VM). This VM hosts the Wazuh central components (Wazuh server, Wazuh indexer, and Wazuh dashboard).
- A Linux endpoint running Ubuntu 22.04.
Configuration
Configure the Wazuh server
Here we configure the Wazuh server to receive and analyze logs from remote endpoints.
1. Append the following remote block to the /var/ossec/etc/ossec.conf configuration file:
<ossec_config>
<remote>
<connection>syslog</connection>
<port><PORT></port>
<protocol><PROTOCOL></protocol>
<allowed-ips><CIDR_NOTATION></allowed-ips>
<local_ip><WAZUH_MANAGER_IP></local_ip>
</remote>
</ossec_config>
Where:
connectionspecifies the type of incoming connection to accept. Here we usesyslog, which is a standard for forwarding log messages in an IP network.portdefines the network port number for the remote connection. Replace<PORT>with the port number you wish to use. Note that the same port number should be configured on the monitored endpoint.protocolspecifies the communication protocol. Replace<PROTOCOL>with your preferred communication protocol either TCP or UDP. Note that the same protocol should be configured on the monitored endpoint.allowed-ipsspecifies which endpoints are allowed to send logs to this server. Replace<CIDR_NOTATION>with the CIDR address of the network on which your endpoints are. If you monitor just one endpoint, you can put its IP address.local-ipspecifies the local IP address of the Wazuh server to be used for this connection. Replace<WAZUH_MANAGER_IP>with the IP address of the Wazuh server.
Learn more about remote configuration options on the Wazuh reference guide.
2. Restart the Wazuh manager to apply the changes:
# systemctl restart wazuh-manager
Configuring the Ubuntu endpoint
In this section, we install and configure Rsyslog to forward events to the Wazuh manager. Some Linux distributions come with Rsyslog pre-installed, but if yours does not, you can install it by following the steps below:
Note: You need root user privileges to execute the commands below.
1. Run the following commands to install Rsyslog:
# apt-get update # apt-get install -y rsyslog
2. Edit the /etc/rsyslog.conf file to enable remote logging by specifying the endpoint to which Rsyslog should forward messages.
- For TCP:
*.* action(type="omfwd" target="<WAZUH_SERVER_IP>" port="<PORT>" protocol="tcp")
- For UDP:
*.* action(type="omfwd" target="<WAZUH_SERVER_IP>" port="<PORT>")
- Where:
The *.* flag instructs that all logs on the monitored endpoint should be forwarded. To forward only certain logs, you can replace this instruction with the specific parameters to match the service name. For example, to forward only cron logs, you can use the following syntax:
if $programname == 'cron' or $programname == 'crond' or $programname == 'crontab' then {
action(type="omfwd" target="<WAZUH_SERVER_IP>" port="<PORT>" protocol="tcp")
}
& ~
Replace:
<WAZUH_SERVER_IP>with the IP address of your Wazuh server.<PORT>with the appropriate TCP or UDP port number, typically514, or change the port number as you see fit.
type="omfwd"instructs to use theomfwdplug-in which provides message forwarding functionality over UDP or TCP. The default protocol is UDP.
3. Start and enable Rsyslog:
# systemctl start rsyslog # systemctl enable rsyslog
Testing the configuration
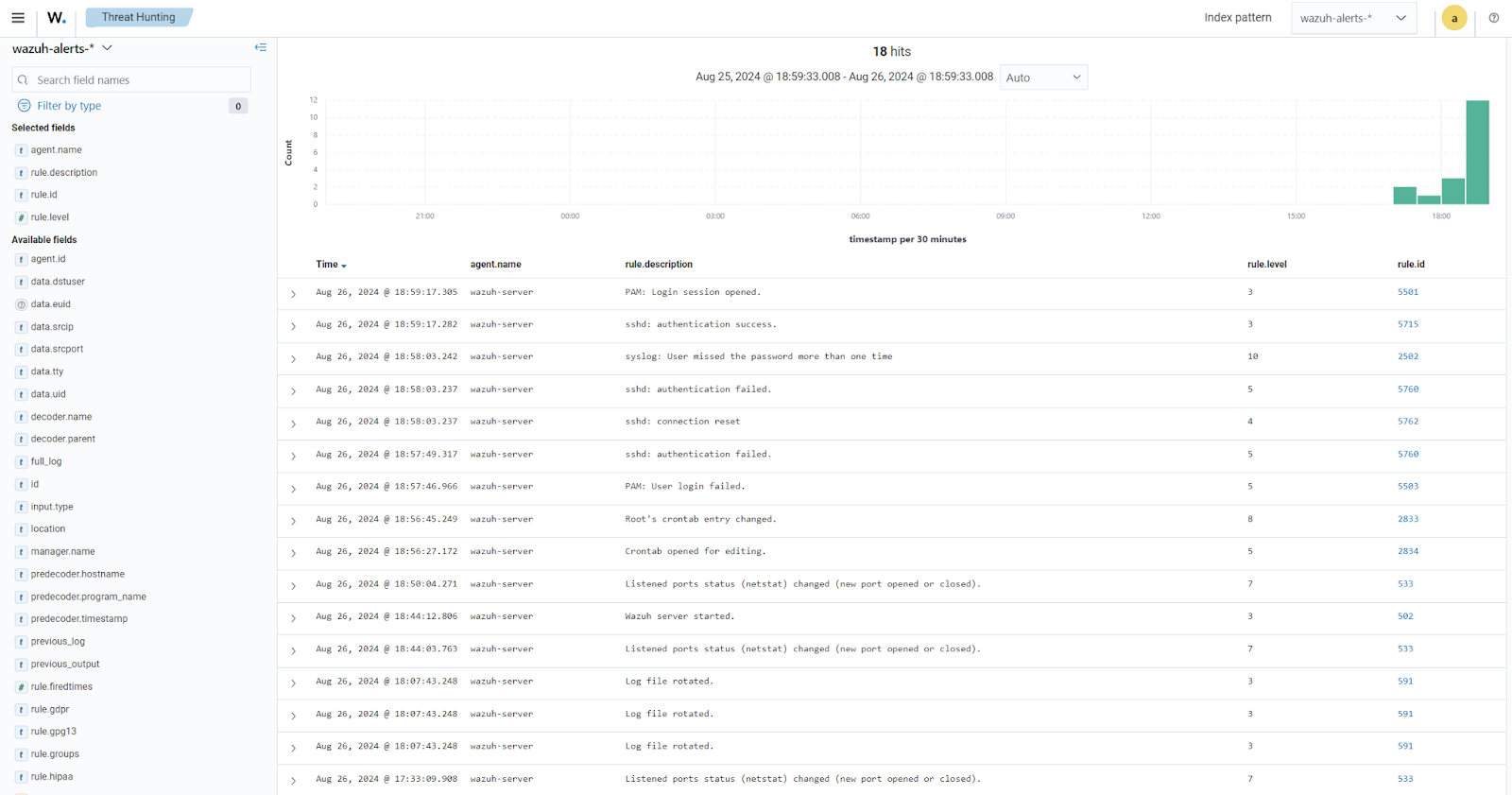
To visualize the events on the Wazuh dashboard, navigate to Threat hunting > Events.
Use case: Forwarding Apache2 logs to Wazuh using Rsyslog
In this section, we configure Rsyslog to forward Apache2 logs to the Wazuh server. By default, Apache HTTP Server does not write logs to syslog. It writes its logs to files such as access.log and error.log, which are typically located in the /var/log/apache2/ or /var/log/httpd/ directory, depending on your operating system.
However, Apache can be configured to write logs to syslog by using a program like logger.
Configure the Wazuh server
1. Append the following configuration to the /var/ossec/etc/ossec.conf file:
<ossec_config>
<remote>
<connection>syslog</connection>
<port>514</port>
<protocol>tcp</protocol>
<allowed-ips><CIDR_NOTATION></allowed-ips>
<local_ip><WAZUH_SERVER_IP></local_ip>
</remote>
</ossec_config>
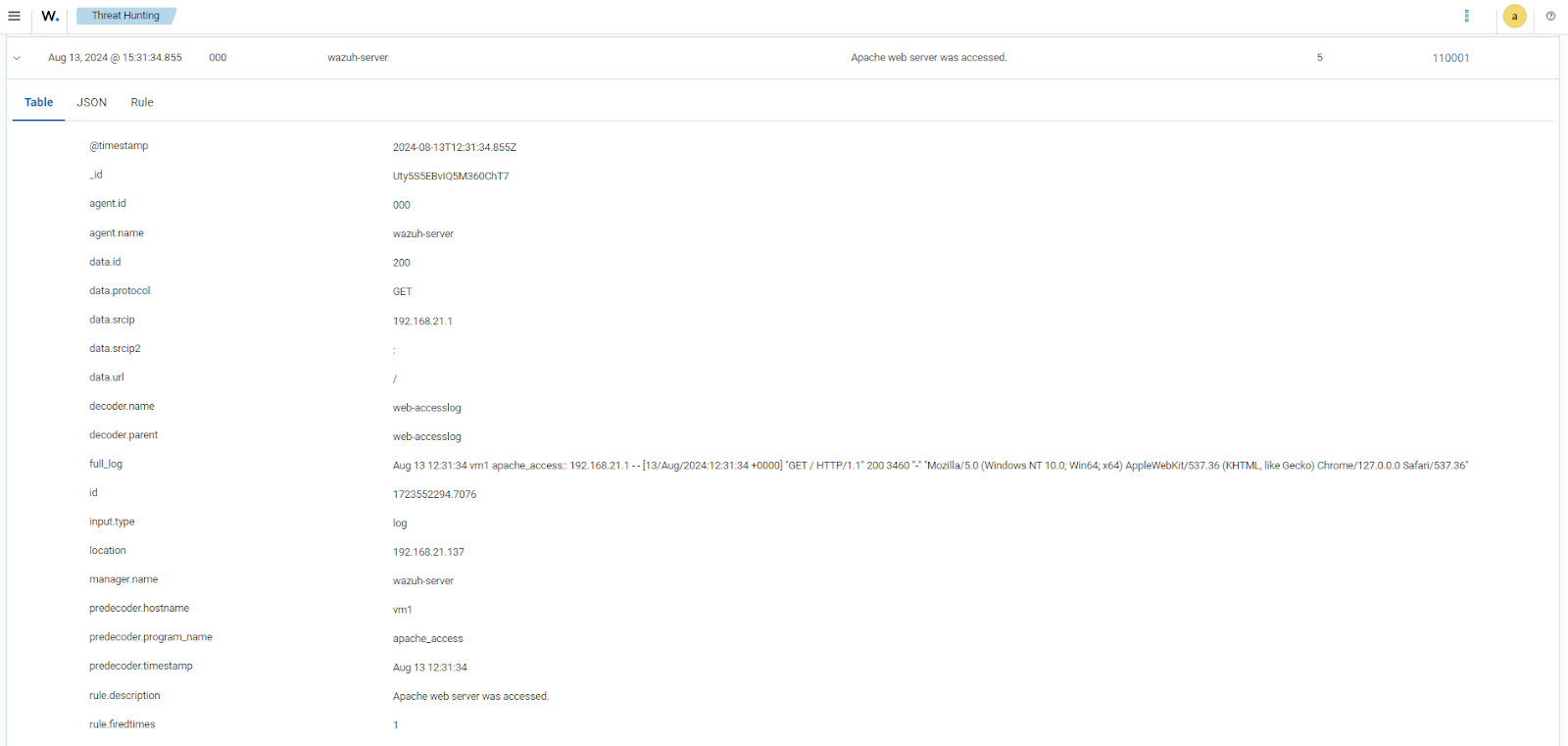
2. Append the following rule to the /var/ossec/etc/rules/local_rules.xml rule file. This rule is configured to trigger an alert each time the apache web server is accessed either from a browser or from a terminal:
<group name="web,accesslog,">
<rule id="110001" level="5">
<if_sid>31108</if_sid>
<description>Apache web server was accessed</description>
</rule>
</group>
3. Restart the Wazuh manager to apply the changes:
# systemctl restart wazuh-manager
Configure the endpoint
1. Run the following command to install apache2 on your monitored endpoint if not yet installed:
# apt install -y apache2
2. Add the following lines in the <VirtualHost> block of the /etc/apache2/sites-available/000-default.conf file. This enables Apache to log to both local files and a remote server:
ErrorLog "|/bin/sh -c '/usr/bin/tee -a /var/log/apache2/error.log | /usr/bin/logger -t apache_error: -p local6.err'"
CustomLog "|/bin/sh -c '/usr/bin/tee -a /var/log/apache2/access.log | /usr/bin/logger -t apache_access: -p local6.notice'" combined
Note: Make sure to comment the existing ErrorLog and CustomLog lines to avoid conflicting instructions.
3. Append the following lines to the /etc/rsyslog.conf file to enable remote logging by specifying the server to which Rsyslog should send messages as follows:
local6.notice action(type="omfwd" target="<WAZUH_SERVER_IP>" port="514" protocol="tcp") local6.err action(type="omfwd" target="<WAZUH_SERVER_IP>" port="514" protocol="tcp")
4. Run the following command to check correctness of Rsyslog and Apache configurations:
# apachectl -t
Syntax OK
# rsyslogd -N1
rsyslogd: version 8.2112.0, config validation run (level 1), master config /etc/rsyslog.confrsyslogd: End of config validation run. Bye.
5. Restart the Rsyslog and Apache2 services to apply the changes:
# systemctl restart rsyslog apache2
Testing the configuration
From your web browser, connect to the apache url http://<ENDPOINT_IP> replacing <ENDPOINT_IP> with the IP address of the Ubuntu endpoint.
To visualize the events on the Wazuh dashboard, navigate to Threat hunting > Events.
Note: Depending on the specific program you are monitoring, you might need to write custom decoders and rules to view the events on the Wazuh dashboard.
Conclusion
By forwarding logs to a security information and event management (SIEM) system or a security monitoring platform like Wazuh, Rsyslog helps enhance security monitoring and threat detection capabilities.
Integrating Rsyslog with Wazuh, the unified XDR and SIEM security platform, ensures that all your system logs are centralized and analyzed for potential threats, providing a robust solution for maintaining a secure and compliant IT environment.
To learn more about Wazuh capabilities, check out our documentation, blog posts, and community for support and updates.
References
