MeshAgent is a software that allows users to remotely manage endpoints by connecting to an open source remote management server called MeshCentral. Users can install MeshAgent on Windows, Linux, macOS, and FreeBSD endpoints.
MeshAgent is not inherently malicious but can be abused by threat actors to create backdoor(s) on endpoints. It allows users to utilize native remote access programs like VNC, RDP, or SSH to connect to a remote device.
We have discovered that in recent times, threat actors use MeshAgent to maintain persistence and send remote commands to compromised endpoints. This has also been reported by a number of security researchers.
Threat actors commonly use MeshAgent for the following reasons:
- MeshCentral requires no additional user actions to establish connections between endpoints once MeshAgent is installed.
- MeshCentral can connect to MeshAgent directly or via RDP without the consent of the agent endpoint.
- MeshCentral is able to wake, power off, and restart MeshAgent endpoints.
- MeshCentral can act as a command and control server because it provides the option to execute shell commands on MeshAgent endpoints without the user’s knowledge.
- MeshCentral can exfiltrate or upload files to agent endpoints.
- Operations initiated from the MeshCentral on the MeshAgent are performed by the
NT AUTHORITY\SYSTEMaccount. This account handles background tasks and maintenance; this would not ordinarily be detected as an anomaly. - It is difficult to detect the MeshAgent executable based on file hashes because users generate unique MeshAgent files on MeshCentral.
In this blog post, we look at the behavior of MeshAgent on a Windows endpoint and demonstrate how to detect MeshAgent activities with Wazuh.
MeshAgent behavior
Threat actors may deliver MeshAgent to the target endpoint as an attachment in a phishing mail. MeshAgent has a high probability of bypassing port-based firewalls because it uses conventional ports like 80 and 443 for communication with MeshCentral.
MeshAgent performs the following actions when it is executed on a Windows endpoint:
1. It creates a process for the execution of MeshCentral background service.
2. It establishes a network connection using the MeshCentral IP address.
3. It creates a pipe communication channel whenever communication is initiated from or to MeshCentral.
4. MeshAgent is usually installed with the command line flag -fullinstall.
5. It usually installs the MeshAgent executable in the file path C:\Program Files\Mesh Agent\MeshAgent.exe.
6. It creates a registry key HKLM\System\CurrentControlSet\Services\Mesh Agent. This key is used by MeshAgent to save configuration settings and options it needs to function properly.
7. It creates a registry key at HKLM\System\CurrentControlSet\Control \SafeBoot\Network\MeshAgent. SafeBoot subkey indicates that the system booted in Safe Mode when connecting to the MeshCentral and can access network resources without credentials.
8. The MeshAgent modifies Windows service to achieve persistence on an endpoint. It creates a registry key HKLM\System\CurrentControlSet\Services\SharedAccess\Parameters \FirewallPolicy\FirewallRules\ to configure the Windows firewall to allow incoming and outgoing WebRTC traffic to MeshCentral.
9. It performs most of its actions with the NT AUTHORITY\SYSTEM and LocalService accounts that have unlimited privileges on Windows endpoints.
MeshAgent exhibits the following behavior when it reconnects to MeshCentral:
1. It creates a pipe communication channel whenever a communication is reinitiated from or to MeshCentral.
2. It creates a registry key at HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree\MeshUserTask to schedule certain tasks MeshCentral can execute. Tasks such as wake, sleep, and power on. Other activities that MeshAgent schedules tasks for include command execution, file upload, and download.
When MeshCentral reconnects to the MeshAgent without its permission, it modifies the connection manager service from “demand start” to “auto start”.
Infrastructure
We use the following infrastructure to demonstrate how Wazuh detects MeshAgent on an endpoint:
- A pre-built ready-to-use Wazuh OVA 4.4.1. Follow this guide to download the virtual machine.
- Wazuh agent running on a Windows 10 endpoint, we refer to this as the victim. Install Wazuh agent 4.4.1 on this endpoint by following this installation guide.
- MeshCentral running on a Windows 10 endpoint, we refer to this as the C2 server.
Victim endpoint
1. Download Sysmon from the Microsoft Sysinternals page.
2. Download the Sysmon configuration file sysmonconfig.xml.
3. Install Sysmon with the downloaded configuration file using PowerShell with administrator privileges:
> .\sysmon.exe -accepteula -i .\sysmonconfig.xml
4. Configure the Wazuh agent to capture Sysmon events by adding the following configuration to the agent configuration file in C:\Program Files (x86)\ossec-agent\ossec.conf within <ossec_config></ossec_config> block
<localfile> <location>Microsoft-Windows-Sysmon/Operational</location> <log_format>eventchannel</log_format> </localfile>
5. Restart the Wazuh agent to apply the changes. Run the following PowerShell command as an administrator:
> Restart-Service -Name wazuh
Wazuh server
Wazuh has the capability to detect newly created services, which we can extend by creating custom rules to detect specific behaviors of MeshAgent. Take the following steps to configure your Wazuh server to detect the activities of MeshAgent:
1. Create a new rules file for MeshAgent:
# touch /var/ossec/etc/rules/meshagent.xml
2. Copy the rules below into the rule file /var/ossec/etc/rules/meshagent.xml:
<group name="meshagent,windows,sysmon">
<!-- MeshAgent installation -->
<rule id="100011" level="12">
<if_sid>61603</if_sid>
<field name="win.eventdata.image" type="pcre2">\.exe</field>
<field name="win.eventdata.CommandLine" type="pcre2">(meshagent|mesh).*\.exe.*-fullinstall</field>
<description>MeshAgent installation</description>
<mitre>
<id>T1204.002</id>
<id>T1036</id>
<id>T1219</id>
</mitre>
</rule>
<!-- MeshAgent creates file -->
<rule id="100012" level="12">
<if_sid>61613</if_sid>
<field name="win.eventdata.image" type="pcre2">\.exe</field>
<field name="win.eventdata.targetFilename" type="pcre2">(?i)[c-z]:\\\\Program\sFiles\\\\Mesh\sAgent\\\\MeshAgent\.exe</field>
<description>Possible MeshAgent folder has been created</description>
<mitre>
<id>T1219</id>
</mitre>
</rule>
<!-- MeshAgent service registry key detection-->
<rule id="100013" level="10">
<if_sid>61614</if_sid>
<field name="win.eventdata.targetObject" type="pcre2" >HKLM\\\\System\\\\CurrentControlSet\\\\Services\\\\Mesh\sAgent</field>
<field name="win.eventdata.eventType" type="pcre2" >^CreateKey$</field>
<field name="win.eventdata.user" type="pcre2" >NT AUTHORITY\\\\SYSTEM</field>
<description>Registry key created for MeshAgent service</description>
<mitre>
<id>T1112</id>
<id>T1219</id>
</mitre>
</rule>
<!-- MeshAgent registry Value detection-->
<rule id="100014" level="10">
<if_sid>61615</if_sid>
<field name="win.eventdata.targetObject" type="pcre2" >HKLM\\\\System\\\\CurrentControlSet\\\\Services\\\\Mesh\sAgent\\\\Type</field>
<field name="win.eventdata.eventType" type="pcre2" >^SetValue$</field>
<field name="win.eventdata.user" type="pcre2" >NT AUTHORITY\\\\SYSTEM</field>
<description>MeshAgent registry modified</description>
<mitre>
<id>T1112</id>
<id>T1219</id>
</mitre>
</rule>
<!-- MeshAgent registry key for safe booting detection-->
<rule id="100015" level="10">
<if_sid>61614</if_sid>
<field name="win.eventdata.targetObject" type="pcre2" >HKLM\\\\System\\\\CurrentControlSet\\\\Control\\\\SafeBoot\\\\Network\\\\Mesh\sAgent</field>
<field name="win.eventdata.eventType" type="pcre2" >^CreateKey$</field>
<field name="win.eventdata.user" type="pcre2" >.</field>
<description>Registry key created for MeshAgent booting</description>
<mitre>
<id>T1534</id>
<id>T1219</id>
</mitre>
</rule>
<!-- MeshAgent firewall rule detection-->
<rule id="100016" level="12">
<if_sid>61615</if_sid>
<field name="win.eventdata.targetObject" type="pcre2" >HKLM\\\\System\\\\CurrentControlSet\\\\Services\\\\SharedAccess\\\\Parameters\\\\FirewallPolicy\\\\FirewallRules</field>
<field name="win.eventdata.eventType" type="pcre2" >^SetValue$</field>
<field name="win.eventdata.details" type="pcre2" >\|Action=Allow\|Active=TRUE.*MeshAgent\.exe</field>
<description>Firewall rule created for MeshAgent service</description>
<mitre>
<id>T1543</id>
<id>T1219</id>
</mitre>
</rule>
</group>
Where:
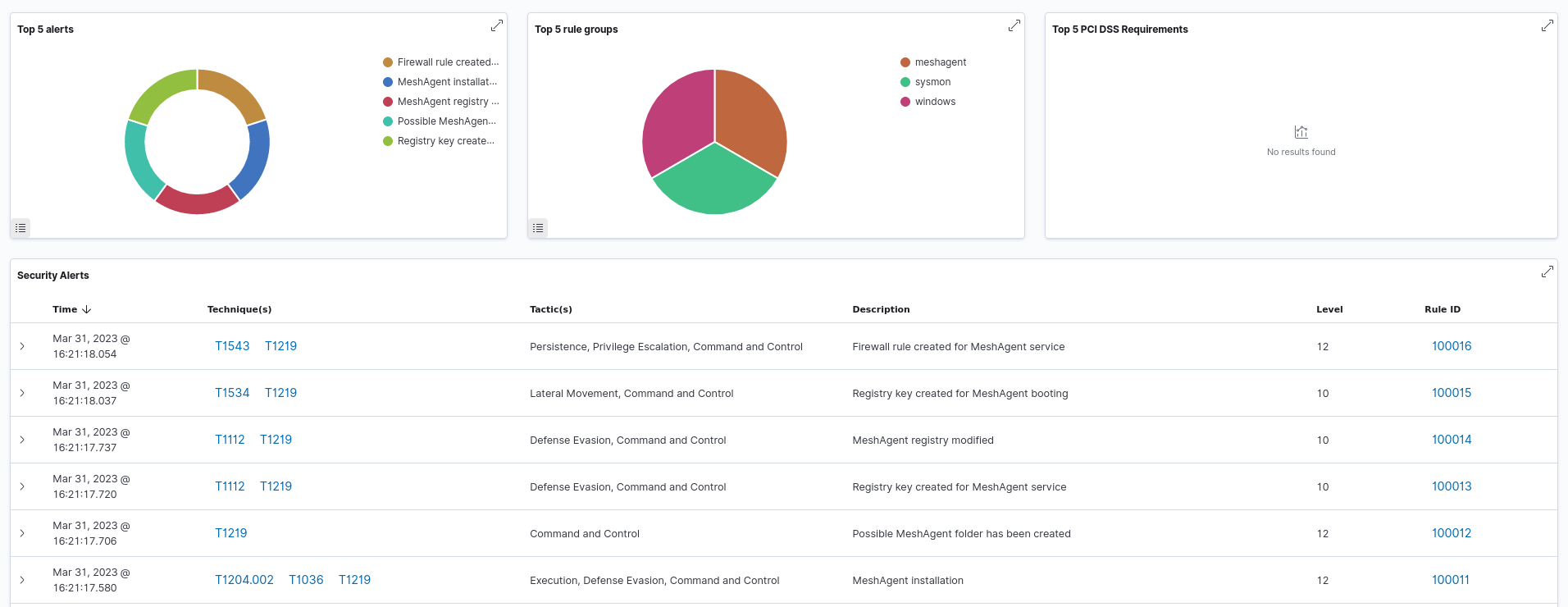
- Rule ID
100011is triggered when MeshAgent is installed using the-fullinstallcommand flag. - Rule ID
100012is triggered when a folder is created for MeshAgent in theC:\Program Files\ filepath. - Rule ID
100013is triggered when a registry key is created for the MeshAgent service. - Rule ID
100014is triggered when the registry is modified. - Rule ID
100015is triggered when a registry key is created for booting MeshAgent in safe mode. - Rule ID
100016is triggered when a firewall rule is created to allow web traffic from the monitored endpoint to MeshCentral.
Note
If you use MeshAgent in your environment, you may want to lower the level of alert if you are only looking for abuse of the remote tool.
3. Restart the Wazuh manager to apply the changes:
# systemctl restart wazuh-manager
Testing the rules
Set up MeshCentral on C2 server
Take the following steps to install MeshCentral on the other Windows 10 endpoint:
1. Download and install Node.js for Windows from the official website.
2. Open PowerShell and run the following command to create a directory in your desired file path for MeshCentral installation:
> mkdir MeshAgent > cd MeshAgent
3. Run the following command to install MeshCentral:
> npm install meshcentral
4. Run the following command to start MeshCentral from the same directory it was installed:
> node node_modules\meshcentral
MeshCentral HTTP redirection server running on port 80. Generating Certificates, may take a few minutes… …. Server has no user, next new account will be site administrator. MeshCentral HTTPS server running on port 443.
We can see the port numbers required to access the web UI of MeshCentral.
Note
Rerun the command If you get this error message “Module node-windows can’t be loaded. Restart MeshCentral.”
5. Go to your browser and type http://localhost:443. Then, accept the self-signed certificate on your browser.
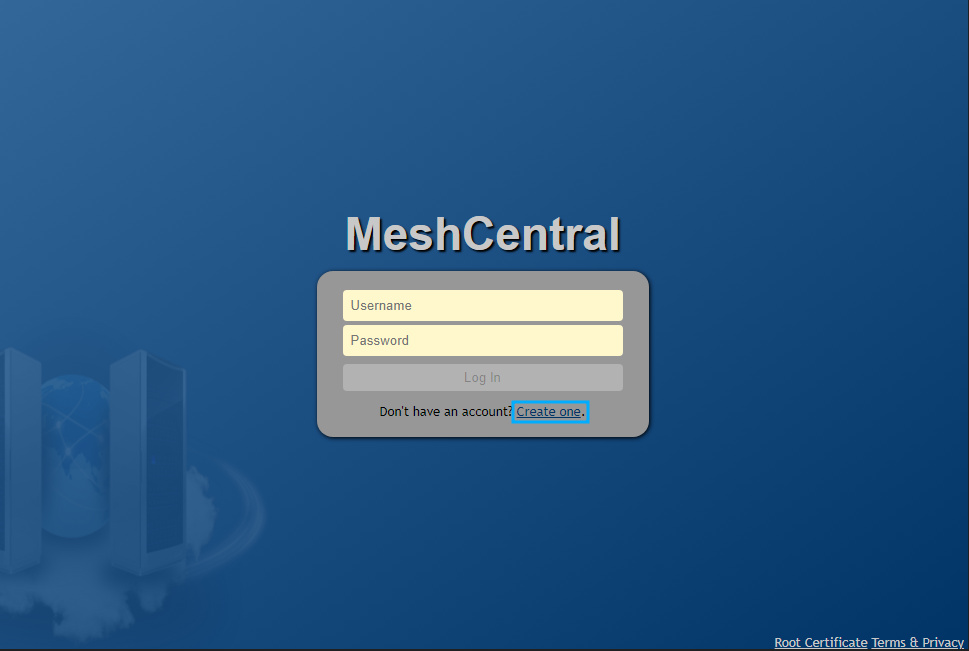
6. Click on Create one on the login page to create an administrator account.
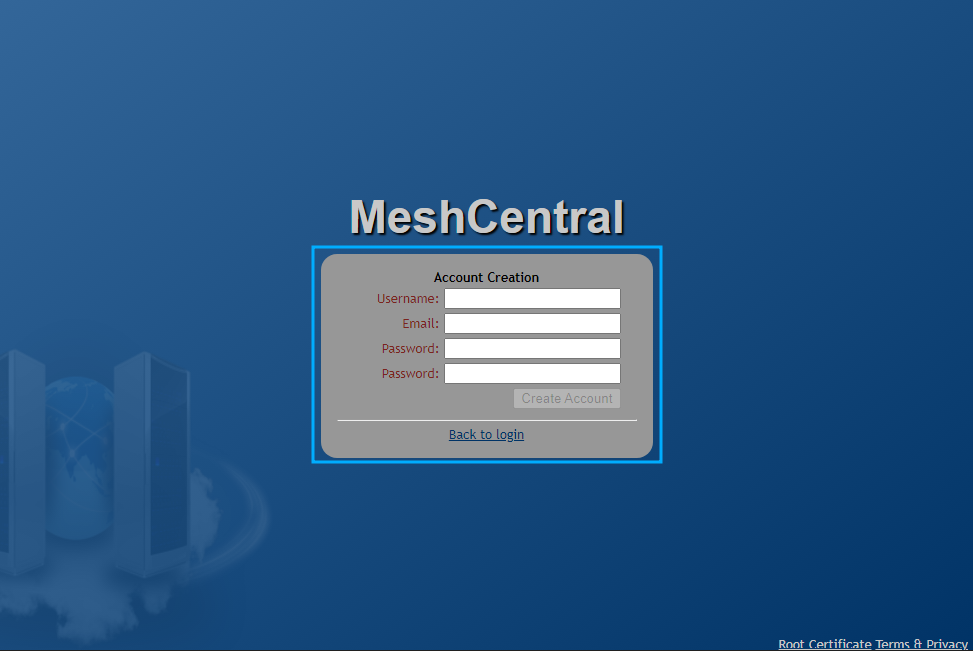
7. Add a username, email, and password. Click Create Account.
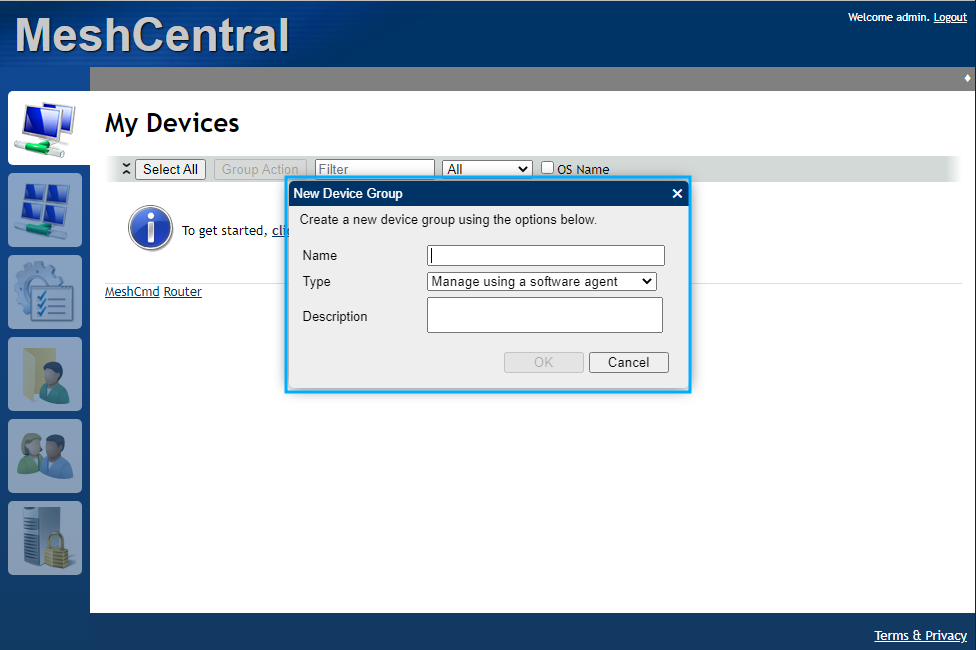
8. Click create a device group. Then add a Device group name, for example, “my_group” and select manage using a software agent for Type.
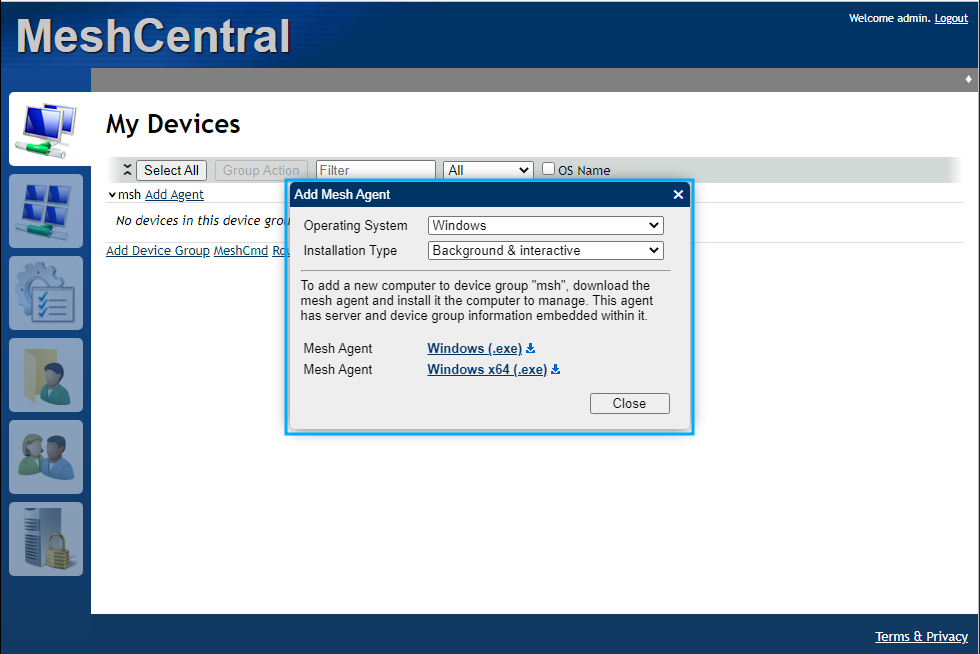
9. Click Add Agent.
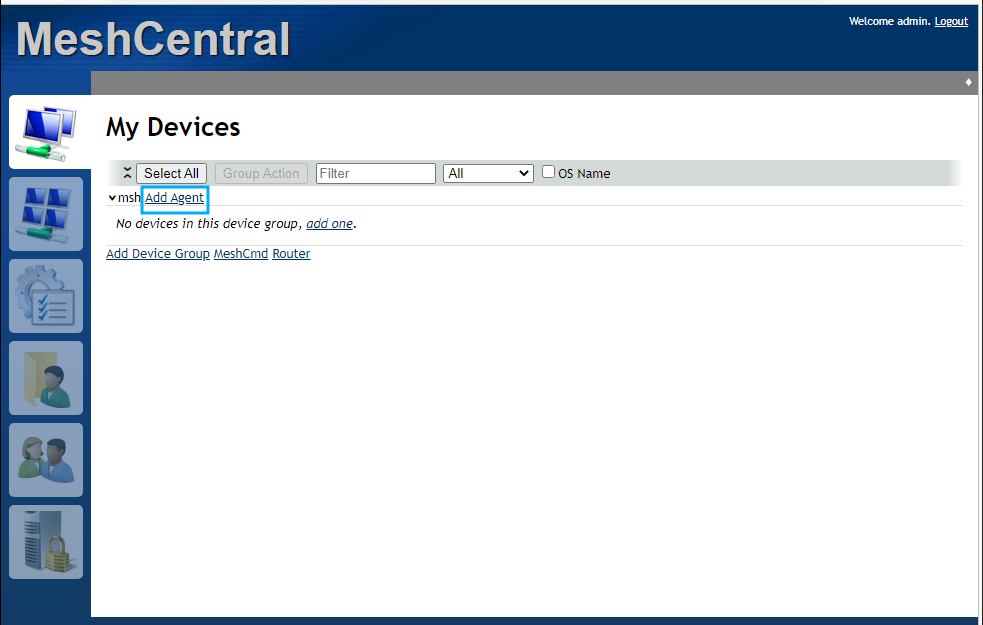
10. Choose the following options from the prompt:
- Click Windows to select the type of operating system.
- Click Background & interactive option to select the type of operating system,
- Then click on the download option (x32 or x64) for the version of Windows you have.
- Copy the downloaded MeshAgent executable to the victim endpoint.
Install MeshAgent on the victim endpoint
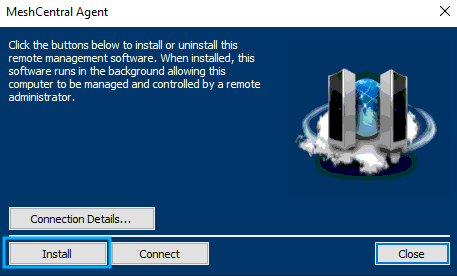
1. Double-click the .exe file that you have copied to the victim endpoint. Then click install.
The screenshot below shows that Wazuh detected the installation of MeshAgent, the connection to MeshCentral, and other behaviors exhibited by MeshAgent.
Conclusion
This blog post describes how to detect MeshAgent activities using Wazuh. MeshAgent allows remote administration and support, but attackers can exploit it to exfiltrate data and deploy malware. Detecting MeshAgent activities is therefore essential for preventing potential incidents that could lead to unauthorized access, data exfiltration, and lateral movement within your environment.
Wazuh is a free and open source security monitoring platform that has the capabilities to detect command and control (C2) activities on monitored endpoints. To learn more about Wazuh capabilities, check out our documentation and blog posts.
