Credential access attacks have become over time one of the critical security concerns for organizations. This phase of an attack, where adversaries obtain access to sensitive credentials, poses the most significant threat. It enables adversaries to gain unauthorized entry into systems, facilitating lateral movement and privilege escalation within the targeted environment. This stealthy approach makes it easier for attackers to achieve their objectives while evading detection.
To effectively detect and respond to credential access attacks on Windows, organizations should implement a robust security monitoring system to check for abnormal behaviors. In this blog post, we demonstrate how to simulate and detect the following credential attack techniques:
- Local Security Authority Subsystem Service (LSASS) memory dumping.
- Security Account Manager (SAM) database extraction.
- Windows Credential Manager Abuse.
Infrastructure
To demonstrate the detection of credential access attacks with Wazuh, we use the following infrastructure.
- A pre-built, ready-to-use Wazuh OVA 4.5.1 Follow this guide to download the virtual machine (VM). This VM hosts the Wazuh central components (Wazuh server, Wazuh indexer, and Wazuh dashboard).
- A Windows 11 victim endpoint with Wazuh agent 4.5.1 installed and enrolled to the Wazuh server. To install the Wazuh agent, refer to the Wazuh Windows installation guide.
Credential access attacks techniques
On a Windows system, possible targets for adversaries include but are not limited to:
- Local accounts
- Domain accounts
- Browsers
- Password managers
- Windows Credential Manager
1. LSASS memory dumping:
Dumping LSASS memory is a technique that attackers can employ to steal sensitive information from a compromised system, particularly credentials. The Local Security Authority Subsystem Service (LSASS) is a critical Windows process responsible for security related functions including handling user authentication and storing credentials. By extracting the LSASS memory, attackers can potentially access plaintext passwords and other sensitive data.
Below are some LSASS memory dumping approaches:
- Rundll32.exe MiniDump with comsvcs:
rundll32.exeis a legitimate Windows process used to run dynamic link library (DLL) functions. Adversaries may abuse itsMiniDumpfunction to extract LSASS memory contents into a DMP (dump) file.
For example Adversaries can leverage the capabilities of the Component Services (comsvcs) DLL to achieve similar memory dumping objectives. By invoking relevant functions, attackers can extract LSASS memory and save it in a DMP file for later analysis.
- Use of Procdump, Process Explorer, or Dumpert: Some adversaries opt for specialized tools like
Procdump,Process Explorer, orDumpertto carry out LSASS memory dumping. These tools provide more control and flexibility, allowing attackers to target specific memory regions and extract sensitive information.
2. SAM database hive extraction
The Security Account Manager (SAM) is a crucial component within the Windows operating system’s security infrastructure. It serves as a database file responsible for storing local user accounts’ security information and credentials. This includes sensitive data like password hashes, which are used for authentication purposes. The SAM database is a fundamental part of the Windows Security subsystem and plays a vital role in maintaining the security of user accounts and system resources.
Exploitation is essentially done by using the legitimate Windows utility reg.exe to interact with the system’s registry. By exporting registry hives, attackers can access credentials offline, enabling them to crack passwords or perform other malicious activities.
3. Windows Credential Manager exploitation
Windows Credential Manager is a built-in feature in Microsoft Windows operating systems that allows users to store and manage various credentials such as usernames, passwords, and other authentication data. This tool helps users to simplify the process of logging into various applications, websites, and network resources. However, its utilization also makes it a target for malicious actors seeking to steal these sensitive credentials.
Exploitation techniques include:
- Utilizing rundll32.exe and Key Management Service: Adversaries often abuse the
rundll32.exeprocess to interact with the Windows Credential Manager. Specifically, they may employ thekeymgr.dllfile to manipulate credentials and thecredwizutility, to make a backup of the credentials (to a.crdfile). For detection, we should pay special attention to detecting whenrundll32.exeis used with commands that involvekeymdr.dll, especially when the “KRShowKeyMgr” argument is used. - VaultCmd process enumeration: Adversaries may leverage the
vaultcmdprocess to list credentials, granting them a comprehensive view of stored credentials. Detection efforts should be aimed at spottingvaultcmdcommands that include the “listcmd” argument.
Detection with Wazuh
In this section, we use detection rules to spot malicious activities on the Windows 11 endpoint.
Sysmon integration
Perform the following steps to configure the Wazuh agent to capture Sysmon logs and send them to the Wazuh server for analysis.
1. Download Sysmon from the Microsoft Sysinternals page with the configuration file sysmonconfig.xml on the Windows 11 endpoint.
2. Run the following command as administrator to install Sysmon with the downloaded configuration file via PowerShell:
> .\sysmon.exe -accepteula -i sysmonconfig.xml
3. Configure the Wazuh agent to collect Sysmon events by appending the following settings to the agent configuration file in “C:\Program Files (x86)\ossec-agent\ossec.conf“:
<ossec_config>
<localfile>
<location>Microsoft-Windows-Sysmon/Operational</location>
<log_format>eventchannel</log_format>
</localfile>
</ossec_config>
4. Apply the changes by restarting the agent using this PowerShell command as administrator:
> Restart-Service -Name wazuh
Wazuh server configuration
1. Add the following rules to the /var/ossec/etc/rules/local_rules.xml file to generate alerts on the Wazuh dashboard whenever an attacker performs any of the attacks mentioned above:
<group name="Windows,attack,">
<!-- Detecting an LSASS memory dumping attack using Rundll32.exe Minidump Function or Comsvcs.dll Exploitation -->
<rule id="100010" level="10">
<if_sid>61609</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)\\\\rundll32.exe</field>
<field name="win.eventdata.imageLoaded" type="pcre2">(?i)[c-z]:\\\\Windows\\\\System32\\\\comsvcs\.dll</field>
<description>Possible adversary activity - LSASS memory dump: $(win.eventdata.imageLoaded) loaded by using $(win.eventData.image) on $(win.system.computer).</description>
<mitre>
<id>T1003.001</id>
</mitre>
</rule>
<!-- Detecting an LSASS memory dumping attack using specialized tools -->
<rule id="100011" level="10">
<if_sid>61613</if_sid>
<field name="win.eventData.targetFilename" type="pcre2">(?i)\\\\[^\\]*\.dmp$</field>
<field name="win.eventData.image" negate="yes" type="pcre2">(?i)\\\\lsass.*</field>
<description>Possible adversary activity - LSASS memory dump: $(win.eventdata.image) created a new file on $(win.system.computer) endpoint.</description>
<mitre>
<id>T1003.001</id>
</mitre>
</rule>
<!-- Detecting a Windows Credential Manager exploitation attack -->
<rule id="100012" level="10">
<if_sid>61603</if_sid>
<field name="win.eventData.Image" type="pcre2">(?i)\\\\rundll32.exe</field>
<field name="win.eventData.commandLine" type="pcre2">keymgr.dll,KRShowKeyMgr</field>
<description>Possible adversary activity - Credential Manager Access via $(win.eventData.Image) on $(win.system.computer) endpoint.</description>
<mitre>
<id>T1003</id>
</mitre>
</rule>
<!-- Detecting a Windows Credential Manager exploitation attack by VaultCmd process enumeration -->
<rule id="100013" level="10">
<if_sid>92052</if_sid>
<field name="win.eventData.image" type="pcre2">(?i)\\\\vaultcmd.exe</field>
<field name="win.eventData.commandLine" type="pcre2">list</field>
<description>Possible adversary activity - Attempt to list credentials via $(win.eventData.Image) on $(win.system.computer) endpoint.</description>
<mitre>
<id>T1003</id>
</mitre>
</rule>
</group>
Where:
- Rule ID
100010is triggered when LSASS memory is dumped using the Windows utilitiesrundll32.exeandcomsvcs.dll. - Rule ID
100011is triggered when LSASS memory is dumped using tools likeprocdumpordumpert. - Rule ID
100012is triggered when the Windows Credential Manager is being accessed and backed up. - Rule ID
100013is triggered when Windows credentials are being listed by using thevaultcmd.exeutility.
2. Restart the Wazuh manager to apply the configuration changes:
# systemctl restart wazuh-manager
Attacks simulation
In this section, we explore the simulation of various credential access attack techniques on the Windows 11 endpoint.
Note: Run the commands below in Powershell with administrator privileges.
LSASS memory dumping
Rundll32.exe MiniDump with comsvcs
Run the following command to simulate an LSASS memory dump using the rundll32.exe and exploiting the comsvcs.dll:
> rundll32.exe C:\Windows\System32\comsvcs.dll, MiniDump 624 C:\temp\lsass.dmp full
Using specialized tools
The steps below show how simulating an LSASS dump can be done using tools like Procdump, Process Explorer, or Dumpert.
Note: Windows Security might block these tools execution. Turn off the Real-time protection on your Windows 11 endpoint to continue with the attack simulations.
Procdump:
Procdump is a command-line utility developed by Sysinternals that can be used to create memory dumps of processes, including LSASS. To simulate an LSASS dump with Procdump:
1. Download Procdump from the Microsoft website:
> Invoke-WebRequest https://download.sysinternals.com/files/Procdump.zip -OutFile procdump.zip
2. Navigate to the download location and unzip the compressed file by running the following command:
> Expand-Archive procdump.zip
3. Navigate to the Procdump directory and run the executable to create a memory dump of the LSASS process as follows:
> cd procdump > .\procdump.exe -accepteula -ma lsass.exe lsass.dmp
The output should be similar to the following:
| Output |
ProcDump v11.0 - Sysinternals process dump utility Copyright (C) 2009-2022 Mark Russinovich and Andrew RichardsSysinternals - www.sysinternals.com[20:04:09] Dump 1 initiated: C:\Users\Lab\Downloads\Procdump\lsass.dmp[20:04:09] Waiting for dump to complete...[20:04:09] Dump 1 writing: Estimated dump file size is 45 MB. |
Dumpert:
Dumpert is a memory dump utility developed by Outflank. It makes use of system calls and API unhooking techniques to create a dump of the LSASS memory. To simulate an LSASS dump attack with dumpert:
1. Download Dumpert using the below command:
> Invoke-WebRequest https://github.com/clr2of8/Dumpert/raw/5838c357224cc9bc69618c80c2b5b2d17a394b10/Dumpert/x64/Release/Outflank-Dumpert.exe -OutFile Outflank-Dumpert.exe
2. Run the executable to simulate the attack as follows:
> .\Outflank-Dumpert.exe
The output should be similar to the following:
| Output |
________ __ _____.__ __[1] Checking OS version details: |
SAM database hive extraction
The SAM database can be located in the %SystemRoot%\System32\config\SAM directory. Various tools and techniques can be used to extract data from the SAM database hive. Commonly used tools include SAMInside, PwDump, and the built-in Windows Registry Editor (Regedit).
In this section, we show how to exploit the SAM database using the regedit utility. Run either of the following commands to simulate the hive extraction from SAM:
> reg.exe save hklm\sam sam.save > reg.exe save hklm\system system.save
The above commands will create a backup or save a copy of the Windows Security Account Manager (SAM) and the Windows Registry’s “HKEY_LOCAL_MACHINE\SYSTEM” hive. Adversaries can then use them to successfully obtain the hashes of all local accounts on the system.
Windows Credential Manager exploitation
Utilizing rundll32.exe and Key Manager Process
Run the following command to simulate a Windows Credential Manager exploitation using this tactic:
> rundll32 keymgr.dll,KRShowKeyMgr
This command opens the “Stored User Names and Passwords” on the Windows endpoint making it easier for adversaries to create a backup of the list of credentials.
VaultCmd process enumeration
Run the following command to start a vaultcmd process to list credentials stored in the Windows credentials vault:
> vaultcmd /listcreds:"Windows Credentials" /all
Detection result
After completing each attack simulation, the different events will be displayed on the Wazuh dashboard as shown on the figure below:
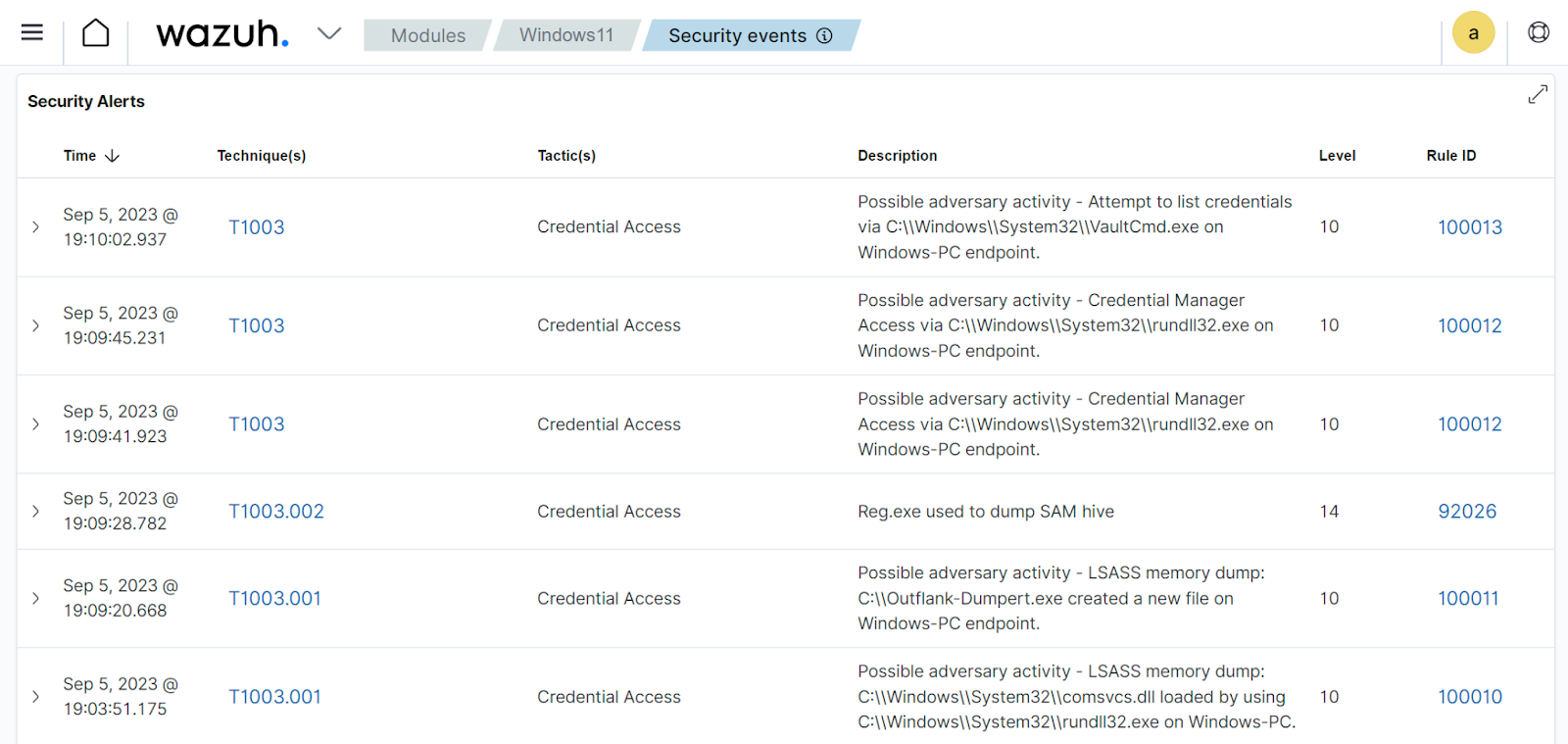
92026 which is fired in case of SAM hive dumping.Conclusion
In this blog post, we have explored the role that Wazuh plays in the proactive hunt for credential access threats. As organizations increasingly find themselves under the crosshairs of sophisticated cybercriminals, the need to fortify their defenses against credential compromise has never been more critical.
With Wazuh as your vigilant sentinel, you can stay one step ahead of attackers, safeguard your organization’s credentials, and preserve the integrity of your digital fortress.
References
