We are thrilled to announce that Wazuh 4.3.0 has been released, along with a new website and improved documentation. This is an important milestone for our project, and excellent news for our open source community.
The path to a unified SIEM and XDR platform
Back in 2015, our project started as a fork of OSSEC. This was a good starting point but, in order to provide a comprehensive security solution, important capabilities were missing.
Over the years, the integration of Elastic Stack and the development of new features have helped us build a platform that provides robust protection for endpoints and cloud workloads.
Today, the Wazuh solution includes many SIEM (Security Information and Event Management) and XDR (eXtended Detection and Response) capabilities. This list summarizes some of them:
- Collection, correlation, and analysis of security events.
- File integrity monitoring (FIM).
- Malware and rootkits detection.
- Security configuration assessment (SCA).
- Agent-based vulnerability detection.
- Security monitoring for cloud-native applications, containers and Kubernetes.
- Threat detection for SaaS solutions and cloud providers.
- MITRE ATT&CK and regulatory compliance mapping.
- Automated responses to detected threats.
In the future, our team will continue to work on providing best-in-class threat prevention, detection, and response capabilities. And, of course, completely free and open source.
The new Wazuh indexer and Wazuh dashboard
With Wazuh 4.3.0, two new components have been added: the Wazuh indexer and the Wazuh dashboard. These components are based on OpenSearch, an open source search and analytics project derived from Elasticsearch and Kibana.
The Wazuh indexer is an Opensearch distribution with additional tools that our team has developed to assist with the installation and configuration of the search engine.
The Wazuh dashboard, which is the web user interface for the Wazuh platform, is a customized OpenSearch Dashboards distribution that includes the Wazuh plugin.
Support for Elastic Stack, Splunk and Open Distro users
For new installations we recommend to use the Quickstart or the Wazuh installation guide, which deploy the solution with Wazuh indexer and Wazuh dashboard. With the installation of these two components the majority of our users won’t need to deploy Elastic Stack, Splunk or Open Distro.
Having said that, we realize that users have different types of needs, and many are already using Wazuh with Elastic Stack, Open Distro and Splunk. This is why Wazuh 4.3.0 will continue to provide support for these platforms.
Here is the list of supported versions:
- Elastic Stack: The Wazuh Kibana plugin supports Kibana versions 7.16 and 7.17, including all of their patch versions.
- Open Distro: The Wazuh Kibana plugin provides support for the latest version of Open Distro, which at this moment is version 1.13.2.
- Splunk: The Splunk app supports Splunk version 8.1 and 8.2, including all their patch versions.
Guides to deploy Wazuh with Elastic Stack and Splunk can also be found in our documentation.
Wazuh 4.3.0 highlights
Wazuh 4.3.0 includes many new features that will improve the user experience and help provide better threat protection.
Vulnerability detection improvements
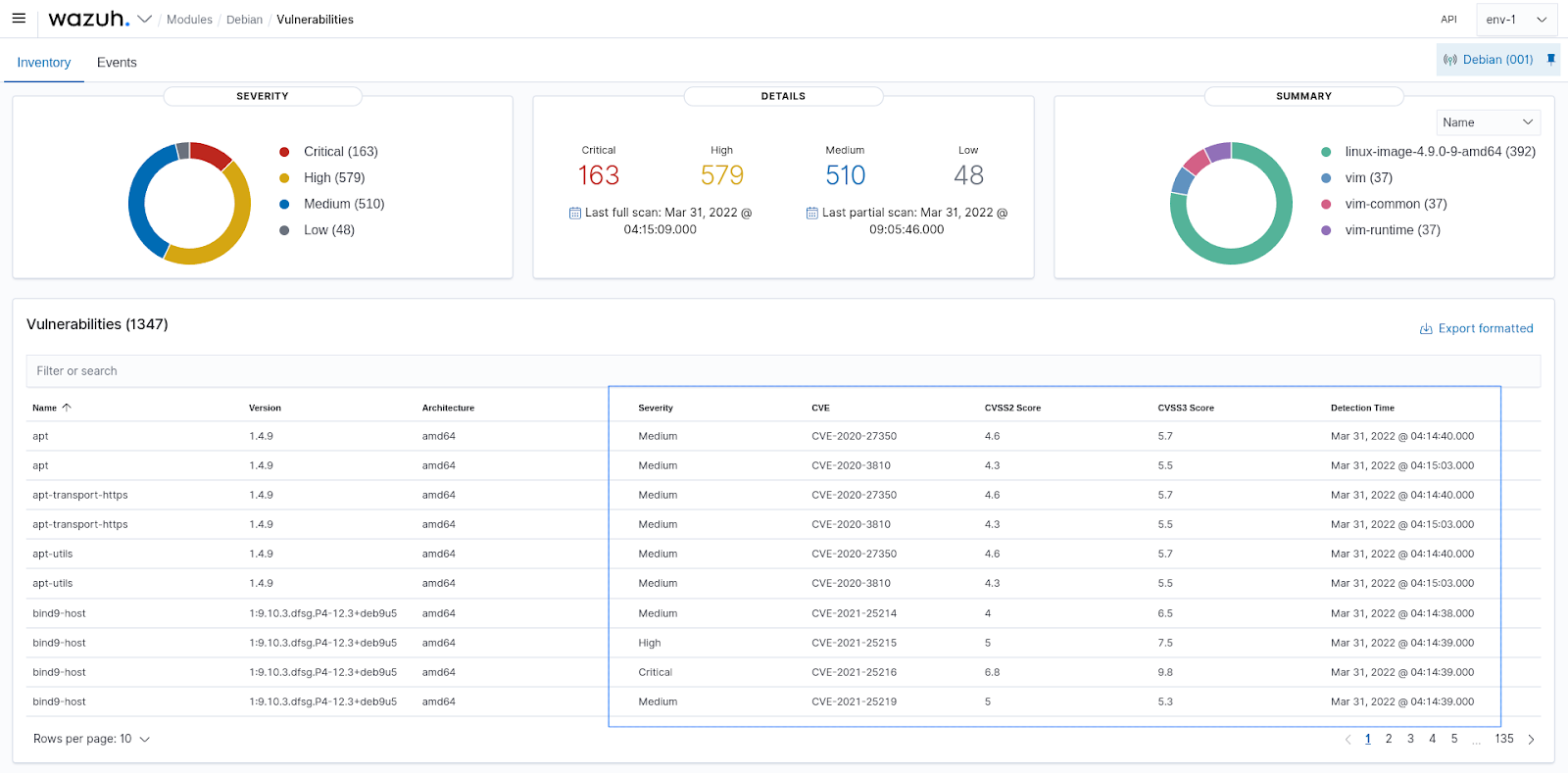
The vulnerability detector web user interface has been redesigned. In addition, the module now includes support for Amazon Linux (ALAS and ALAS2) and Arch Linux.
New integrations with Office 365 and GitHub
New security monitoring modules have been added for Office 365 and GitHub. Now the Wazuh agent can be used to collect auditing logs from these services. Besides, the Wazuh server provides decoders and rules for analyzing these logs and detecting threats.
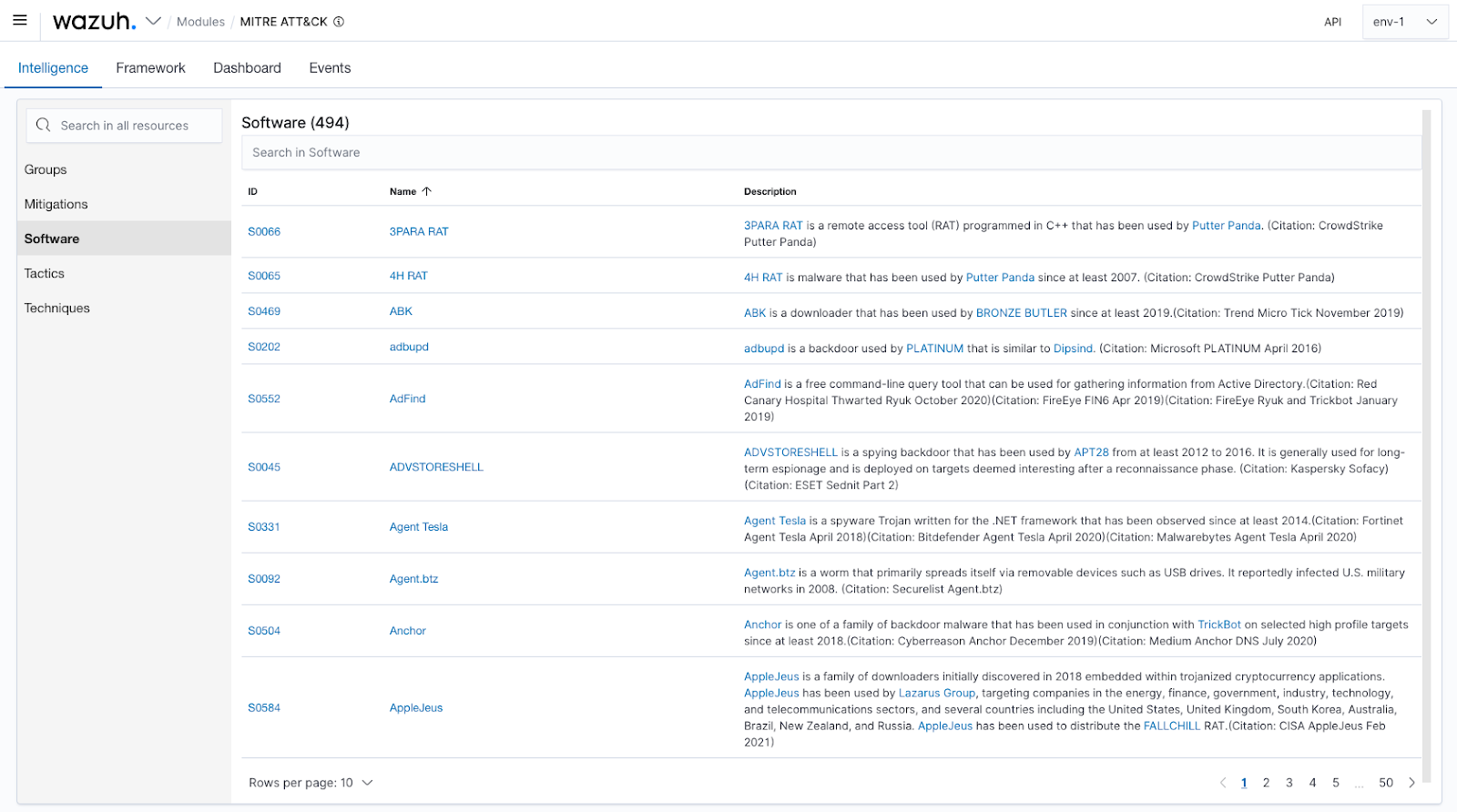
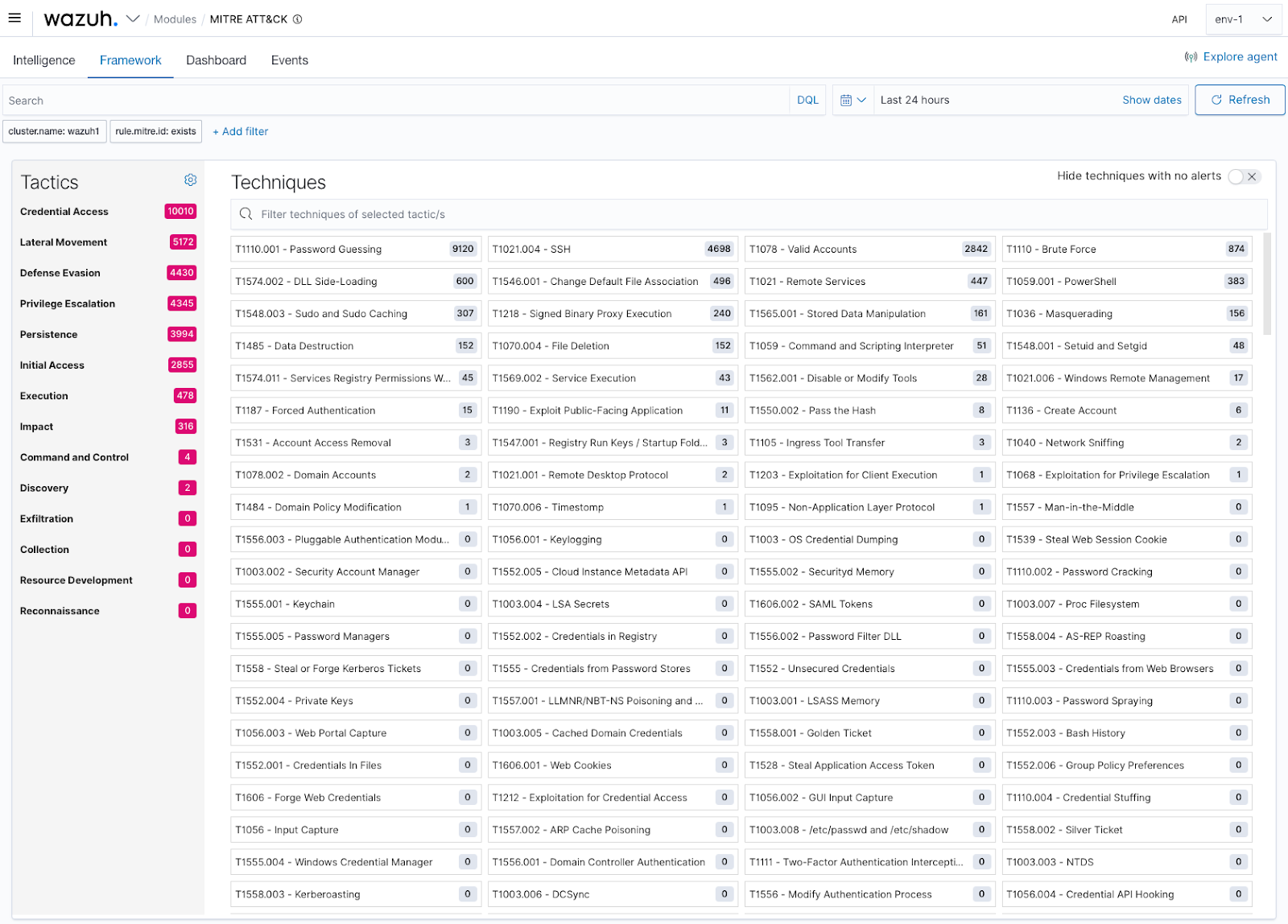
MITRE ATT&CK intelligence
Now it is possible to navigate through the different threat groups, mitigations, software, tactics and techniques. The mapping with detection rules has also been updated.
Improvements for macOS agents
Several improvements have been done for Wazuh macOs agents:
- Support for data collection of native macOS logs (Unified Logging System).
- The Wazuh agent can now be upgraded remotely from the Wazuh server via WPK.
- New security configuration assessment (SCA) policies have been added.
Release notes
Many other features, fixes, and performance improvements have been added to version 4.3.0. Please check our release notes for more information. For much more details you can also see our changelog.
