LimeRAT is an open source malicious remote access trojan (RAT) that is designed to provide attackers with control over an infected system. It is a powerful and versatile RAT that targets Windows operating systems. LimeRAT can operate as ransomware, a cryptocurrency miner, an information stealer, a keystroke logger, and a computer worm. The malware is primarily distributed through social engineering tactics such as email attachments, malicious online advertisements, and the distribution of cracked software.
In this blog post, we use Wazuh to detect the malicious activities of LimeRAT.
LimeRAT behavior and capabilities
The malware has a robust set of dangerous capabilities. These include USB drive propagation, infection of all USB files and folders, evasive techniques to avoid antivirus detection and awareness of virtual machines. Additionally, LimeRAT is capable of stealing cryptocurrency wallets and saved passwords, capturing keystrokes, establishing backdoor and RDP access, and deploying ransomware.
Cybercriminals can personalize each LimeRAT payload with different attributes. Once a victim installs the payload on the target machine, it retrieves sensitive information about the user, operating system, geolocation, CPU, and additional relevant data.
LimeRAT targets all versions of the Windows operating system and is coded in Visual Basic.NET. Security analysts have recognized LimeRAT for its adeptness in evading antivirus detection, anti-virtual machine features, minimal footprint, and encrypted communication channels.
It maintains redundancy with the command and control (C2) infrastructure by using multiple communication ports for the communication channels. To ensure resilience, the LimeRAT C2 abuses the pastie pastebin service by retrieving the actual C2 address from an encrypted HTTPS channel. The pastebin application allows users to upload and share text online. This resilience technique allows LimeRAT to maintain its C2 functionality with an extra layer of protection and adaptability.
The LimeRAT configuration which is written in the .NET language is encrypted and obfuscated. It makes use of a decryption algorithm for decoding the string that holds the C2 address.LimeRAT drops a copy of itself in the C:\Users\<USER_NAME>\AppData\Roaming folder with the filename checker netflix.exe to masquerade as a legitimate file. The <USER_NAME> placeholder is the name of the user account that installed the LimeRAT.
C:\Users\User\AppData\Roaming>dir /a
You can see the expected output below:
Volume in drive C is Windows
Volume Serial Number is CE1E-DB23
Directory of C:\Users\User\AppData\Roaming
06/04/2023 10:10 AM <DIR> .
11/13/2022 01:54 AM <DIR> ..
11/13/2022 01:55 AM <DIR> Adobe
06/04/2023 10:10 AM 210,432 checker netflix.exe
06/02/2023 04:49 AM <DIR> Microsoft
06/04/2023 09:04 AM <DIR> WinRAR
1 File(s) 210,432 bytes
5 Dir(s) 79,273,406,464 bytes free
LimeRAT creates a registry key in HKEY_CURRENT_USER\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN for the created checker netflix.exe file to ensure it runs anytime the victim endpoint is restarted.
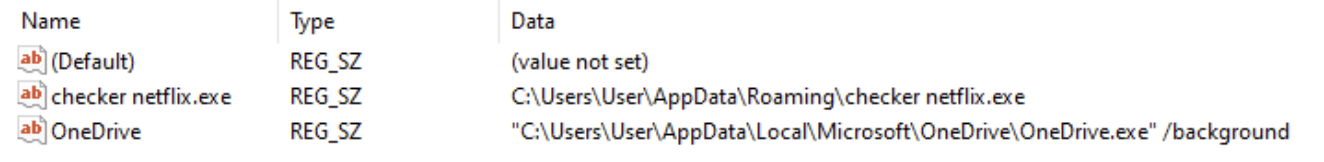
It also creates a registry key path HKEY_CURRENT_USER\SOFTWARE\<MUTEX CREATED> containing the value names Flood, Rans-Status, and USB of a registry string data type.

Where:
Floodrefers to the status of a flooding attack.Rans-Statusrefers to the status of the ransomware.USBrefers to the status of infected USB devices.
Analyzed IOC file:
| SHA1 | 14836dd608efb4a0c552a4f370e5aafb340e2a5d |
| SHA256 | 6d08ed6acac230f41d9d6fe2a26245eeaf08c84bc7a66fddc764d82d6786d334 |
| MD5 | d36f15bef276fd447e91af6ee9e38b28 |
| SSDEEP | 3072:DDiv2GSyn88sH888wQ2wmVgMk/211h36vEcIyNTY4WZd/w1UwIwEoTqPMinXHx+i:XOayy |
Infrastructure
To demonstrate the detection of LimeRAT with Wazuh, we use the following infrastructure.
1. A pre-built ready-to-use Wazuh OVA 4.4.4. Follow this guide to download the virtual machine.
2. A Windows 11 victim endpoint with Wazuh agent 4.4.4 installed. To install the Wazuh agent, refer to the following installation guide.
Detection with Wazuh
In this blog post, we use Sysmon integration and YARA with Wazuh to detect LimeRAT behavior on the victim endpoint.
Detection rules
We use Sysmon to monitor several system events and create rules on the Wazuh server to detect the malicious activities of LimeRAT malware.
Follow the steps below to detect the malicious activity performed by LimeRAT malware on the Windows endpoint.
Windows
Perform the following steps to configure the Wazuh agent to capture Sysmon logs and send them to the Wazuh server for analysis.
1. Download Sysmon from the Microsoft Sysinternals page.
2. Extract the compressed Sysmon file to your preferred location.
3. Download the Sysmon configuration file – sysmonconfig.xml using Powershell. Replace <SYSMON_EXECUTABLE_PATH> with the directory path to your Sysmon executable.
> wget -Uri https://wazuh.com/resources/blog/emulation-of-attack-techniques-and-detection-with-wazuh/sysmonconfig.xml -OutFile sysmonconfig.xml
4. Switch to the directory with the Sysmon executable. Run the command below to install and start Sysmon using PowerShell with Administrator privileges:
> .\Sysmon64.exe -accepteula -i sysmonconfig.xml
5. Add the following configuration to the C:\Program Files (x86)\ossec-agent\ossec.conf file within the <ossec_config> block to collect and forward Sysmon event logs to the Wazuh server:
<localfile> <location>Microsoft-Windows-Sysmon/Operational </location> <log_format>eventchannel</log_format></localfile>
6. Restart the Wazuh agent to apply the configuration changes:
> Restart-Service -Name wazuh
Wazuh server
In this section, we create rules to detect LimeRAT behavior on the endpoint.
1. Add the rules below to the /var/ossec/etc/rules/local_rules.xml file on the Wazuh server:
<group name="lime_rat,sysmon,">
<!-- Rogue create netflix.exe creation -->
<rule id="100024" level="12">
<if_sid>61613</if_sid>
<field name="win.eventdata.image" type="pcre2">\.exe</field>
<field name="win.eventdata.targetFilename" type="pcre2">(?i)[c-z]:\\\\Users\\\\.+\\\\AppData\\\\Roaming\\\\checker netflix\.exe</field>
<description>Potential LimeRAT activity detected: checker netflix.exe created at $(win.eventdata.targetFilename) by $(win.eventdata.image).</description>
<mitre>
<id>T1036</id>
</mitre>
</rule>
<!-- Registry key creation for persistence -->
<rule id="100025" level="12">
<if_group>sysmon</if_group>
<field name="win.eventdata.details" type="pcre2">(?i)[c-z]:\\\\Users\\\\.+\\\\AppData\\\\Roaming\\\\checker netflix\.exe</field>
<field name="win.eventdata.targetObject" type="pcre2" >HKU\\\\.+\\\\Software\\\\Microsoft\\\\Windows\\\\CurrentVersion\\\\Run\\\\checker netflix\.exe</field>
<field name="win.eventdata.eventType" type="pcre2" >^SetValue$</field>
<description>Potential LimeRAT activity detected: $(win.eventdata.details) added itself to the Registry as a startup program $(win.eventdata.targetObject) to establish persistence.</description>
<mitre>
<id>T1547.001</id>
</mitre>
</rule>
<!-- Network activity detection -->
<rule id="100026" level="12">
<if_sid>61605</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)[c-z]:\\\\Users\\\\.+\\\\AppData\\\\Roaming\\\\checker netflix\.exe</field>
<description>Potential LimeRAT activity detected: Suspicious DNS query made by $(win.eventdata.image).</description>
<mitre>
<id>T1572</id>
</mitre>
</rule>
<!-- DLL process injection -->
<rule id="100027" level="12" >
<if_sid>61609</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)[c-z]:\\\\Users\\\\.+\\\\AppData\\\\Roaming\\\\checker netflix\.exe</field>
<field name="win.eventdata.ImageLoaded" type="pcre2">(?i)[c-z]:\\\\Windows\\\\Microsoft\.NET\\\\Framework\\\\.+\\\\mscoreei\.dll</field>
<description>Potential LimeRAT activity detected: DLL $(win.eventdata.ImageLoaded) is injected on $(win.system.computer).</description>
<mitre>
<id>T1055.001</id>
</mitre>
</rule>
<!-- LimeRAT service creation -->
<rule id="100028" level="12">
<if_sid>61614</if_sid>
<field name="win.eventdata.targetObject" type="pcre2" >HKLM\\\\System\\\\CurrentControlSet\\\\Services\\\\disk</field>
<field name="win.eventdata.eventType" type="pcre2" >^CreateKey$</field>
<description>Potential LimeRAT activity detected: LimeRAT service $(win.eventdata.targetObject) has been created on $(win.system.computer).</description>
<mitre>
<id>T1543.003</id>
</mitre>
</rule>
</group>
Where:
- Rule ID
100024is triggered when LimeRAT creates a maliciouscreate netflix.exefile in theC:\Users\<USERNAME>\AppData\Roaming\folder. - Rule ID
100025is triggered when LimeRAT sets a copy ofcreate netflix.exeas a registry run key. - Rule ID
100026is triggered when LimeRAT makes a DNS query. - Rule ID
100027detects when LimeRAT injects a DLL processmscoreeiin theC:\Windows\Microsoft\.NET\Framework\folder. - Rule ID
100028detects when LimeRAT creates a registry keydisk.
2. Restart the Wazuh manager to apply the configuration changes:
# systemctl restart wazuh-manager
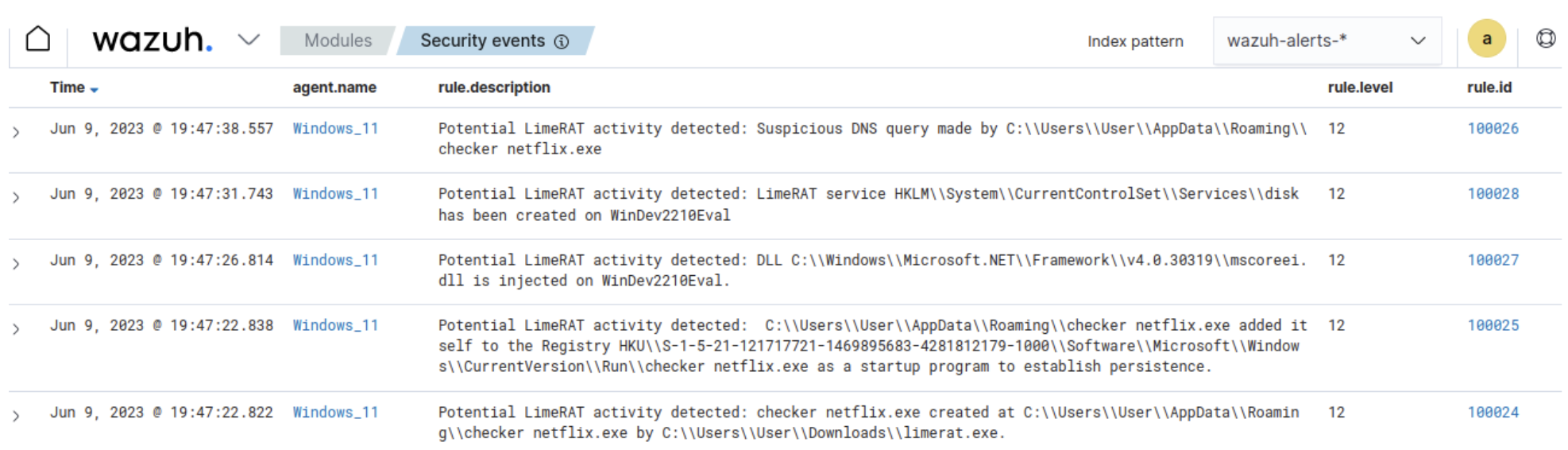
Detection results
Below is the image of the alerts generated on the Wazuh dashboard when a Windows endpoint is infected by LimeRAT.Navigate to the Security events tab to view the generated alerts.
YARA integration
There are various ways Wazuh can integrate with YARA. We will focus on utilizing the Wazuh FIM module, Wazuh active response module, and YARA:
- The Wazuh File Integrity Monitoring (FIM) module detects and alerts when files are created, modified, or deleted. In this blog post, the Wazuh FIM module is enabled for a directory within the Windows filesystem and FIM alerts are generated for any activity in the FIM-monitored directory.
- The Wazuh active response module executes predefined scripts when certain alerts occur. In this scenario, the FIM alerts automatically trigger the Wazuh active response script to execute YARA scans on the file that is added or modified. This is done in a FIM-monitored directory.
- YARA is an open source pattern-matching tool used to identify malware samples. When there is a positive YARA match, a YARA alert gets generated, the file is marked as malicious and the active response script immediately deletes the file.
In this blog post, we use the Wazuh active response module to automatically execute a YARA scan on files added or modified in the Downloads folder.
Windows
Install the following packages on the victim endpoint. These are required to download and install YARA.
1. Python v 3.8.7 or later (with pip pre-installed). Check the following boxes when prompted:
- Install launcher for all users.
- Add
Python.exeto PATH. This places the interpreter in the execution path.
2. Microsoft Visual C++ 2015 Redistributable.
After installing the above packages, follow the steps below to download the YARA executable:
1. Launch PowerShell with administrator privileges and download YARA:
> Invoke-WebRequest -Uri https://github.com/VirusTotal/yara/releases/download/v4.3.1/yara-4.3.1-2141-win64.zip -OutFile v4.3.1-2141-win64.zip
2. Extract the YARA executable:
> Expand-Archive v4.3.1-2141-win64.zip
3. Create a folder called C:\Program Files (x86)\ossec-agent\active-response\bin\yara\ and copy the YARA binary into it:
> mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\'> cp .\v4.3.1-2141-win64\yara64.exe 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\'
Follow the steps below to download YARA rules:
1. Using the same PowerShell terminal launched earlier, install valhallaAPI using the pip utility. The valhallaAPI is used to retrieve the public signature-base YARA ruleset:
> pip install valhallaAPI
2. Create the file download_yara_rules.py, and copy the following script into it:
from valhallaAPI.valhalla import ValhallaAPI
v = ValhallaAPI(api_key="1111111111111111111111111111111111111111111111111111111111111111")
response = v.get_rules_text()
with open('yara_rules.yar', 'w') as fh:
fh.write(response)
3. Download YARA rules and copy them to the C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\ folder:
> python download_yara_rules.py > mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\' > cp yara_rules.yar 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\'
4. Edit the C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yar file and add the following LimeRAT YARA rules:
rule win_limerat {
meta:
author = "Iseoluwa Titiloye Oyeniyi"
date = "2023-04-05"
description = "detects LimeRAT executable"
malpedia_family = "win.limerat"
tlp = "TLP:WHITE"
version = "v1.0"
strings:
$s1 = "Y21kLmV4ZSAvYyBwaW5nIDAgLW4gMiAmIGRlbCA=" wide
$s2 = "schtasks /create /f /sc ONLOGON /RL HIGHEST /tn LimeRAT-Admin /tr" wide
$s3 = "Minning..." fullword wide
$s4 = "--donate-level=" wide
$s5 = "\\vboxhook.dll" fullword wide
$s6 = { E5 A4 AA E5 AD AB E5 B0 87 }
$s7 = { 61 02 D2 0A 7C 04 69 02 }
$s8 = "LimeRAT" wide
$s9 = "MD5CryptoServiceProvider"
$s10 = "Win32_Processor.deviceid=\"CPU0\"" fullword wide
$s11 = "select CommandLine from Win32_Process where Name='{0}'" wide
$s12 = "Regasm.exe" fullword wide
$s13 = "Flood!" fullword wide
$s14 = "Rans-Status" fullword wide
$s15 = "cmd.exe /c ping 0" wide
$s16 = "mscoree.dll" wide
$s17 = "RijndaelManaged" wide
$s18 = "_CorExeMain" wide
condition:
uint16(0) == 0x5A4D and
5 of them
}
5. Edit the C:\Program Files (x86)\ossec-agent\ossec.conf file and add the below configuration within the <syscheck> block to monitor the Downloads folders of all users in real-time:
<directories realtime="yes">C:\Users\*\Downloads</directories>
Note: In this blog post, the Downloads folders of all users are monitored. However, you can configure other folders you wish to monitor.
6. Create a batch file yara.bat in the C:\Program Files (x86)\ossec-agent\active-response\bin\ folder. The active response module uses this file to perform YARA scans for malware detection and removal:
:: This script deletes LimeRAT as well as other malicious files matched by the YARA Rules
@echo off
setlocal enableDelayedExpansion
reg Query "HKLM\Hardware\Description\System\CentralProcessor\0" | find /i "x86" > NUL && SET OS=32BIT || SET OS=64BIT
if %OS%==32BIT (
SET log_file_path="%programfiles%\ossec-agent\active-response\active-responses.log"
)
if %OS%==64BIT (
SET log_file_path="%programfiles(x86)%\ossec-agent\active-response\active-responses.log"
)
set input=
for /f "delims=" %%a in ('PowerShell -command "$logInput = Read-Host; Write-Output $logInput"') do (
set input=%%a
)
set json_file_path="C:\Program Files (x86)\ossec-agent\active-response\stdin.txt"
set syscheck_file_path=
echo %input% > %json_file_path%
FOR /F "tokens=* USEBACKQ" %%F IN (`Powershell -Nop -C "(Get-Content 'C:\Program Files (x86)\ossec-agent\active-response\stdin.txt'|ConvertFrom-Json).parameters.alert.syscheck.path"`) DO (
SET syscheck_file_path=%%F
)
set yara_exe_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\yara64.exe"
set yara_rules_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yar"
echo %syscheck_file_path% >> %log_file_path%
for /f "delims=" %%a in ('powershell -command "& \"%yara_exe_path%\" \"%yara_rules_path%\" \"%syscheck_file_path%\""') do (
echo wazuh-yara: INFO - Scan result: %%a >> %log_file_path%
:: Deleting the scanned file.
del /f "%syscheck_file_path%" >nul 2>&1
if exist "%syscheck_file_path%" (
echo wazuh-yara: INFO - Error removing threat: %%a >> %log_file_path%
) else (
echo wazuh-yara: INFO - Successfully deleted: %%a >> %log_file_path%
)
)
exit /b
7. Restart the Wazuh agent using PowerShell for the changes to take effect:
> Restart-Service -Name wazuh
Wazuh server
Take the following steps to configure custom decoders, rules, and active response on the Wazuh server.1. Create custom rules in the /var/ossec/etc/rules/local_rules.xml file. These rules will provide alerts about files that are added or modified in the /Downloads directory on the monitored endpoint:
<group name= "syscheck,">
<rule id="100029" level="7">
<if_sid>550</if_sid>
<field name="file" type="pcre2">(?i)C:\\Users.+Downloads</field>
<description>File modified in the Downloads folder.</description>
</rule>
<rule id="100030" level="7">
<if_sid>554</if_sid>
<field name="file" type="pcre2">(?i)C:\\Users.+Downloads</field>
<description>File added to the Downloads folder.</description>
</rule>
</group>
Where:
- Rule ID
100029is triggered when a file is modified in the/Downloadsdirectory. - Rule ID
100030is triggered when a file is added to the/Downloadsdirectory.
2. Add the following configuration to the /var/ossec/etc/ossec.conf file within the <ossec_config> block:
<command> <name>yara</name> <executable>yara.bat</executable> <timeout_allowed>no</timeout_allowed> </command> <active-response> <command>yara</command> <location>local</location> <rules_id>100029,100030</rules_id> </active-response>
The Wazuh FIM module executes the yara.bat script when a file is added or modified in the Downloads folder.
Where:
<name>specifies the name of the command being called in the active response section.<executable>specifies the executable file to run.<command>specifies the command that will be used by the active response.- The
<active response>block calls the<command>block when the rule ID100029or100030triggers an alert. <location>specifies where the active response script is executed.
3. Add the following decoders to the /var/ossec/etc/decoders/local_decoder.xml file to decode the logs generated by the active response script:
<decoder name="yara_decoder">
<prematch>wazuh-yara:</prematch>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Scan result: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Successfully deleted: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Error removing threat: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
4. Create custom rules in the /var/ossec/etc/rules/local_rules.xml to alert when there is a YARA active response action:
<!-- Rule for the decoder (yara_decoder) -->
<group name="yara,">
<rule id="100031" level="0">
<decoded_as>yara_decoder</decoded_as>
<description>Yara grouping rule</description>
</rule>
<!-- YARA scan detects a positive match -->
<rule id="100032" level="12">
<if_sid>100031</if_sid>
<match type="pcre2">wazuh-yara: INFO - Scan result: </match>
<description>File "$(yara_scanned_file)" is a positive match. Yara rule: $(yara_rule)</description>
</rule>
<!-- Wazuh successfully deletes a malware with a positive match -->
<rule id="100033" level="12">
<if_sid>100031</if_sid>
<match type="pcre2">wazuh-yara: INFO - Successfully deleted: </match>
<description>Successfully removed "$(yara_scanned_file)" by active response due to YARA rule $(yara_rule) positive match</description>
</rule>
<!-- Wazuh encounters an error when deleting a malware with a positive match -->
<rule id="100034" level="12">
<if_sid>100031</if_sid>
<match type="pcre2">wazuh-yara: INFO - Error removing threat: </match>
<description>Error removing "$(yara_scanned_file)". YARA rule: $(yara_rule)</description>
</rule>
</group>
Where:
- Rule ID
100031is the base rule for detecting YARA events. - Rule ID
100032is triggered when YARA scans and detects a malicious file. - Rule ID
100033is triggered when the detected file has been successfully removed by Wazuh active response. - Rule ID
100034is triggered when the detected file is not removed successfully by Wazuh active response.
4. Restart the Wazuh manager for the changes to take effect:
$ sudo systemctl restart wazuh-manager
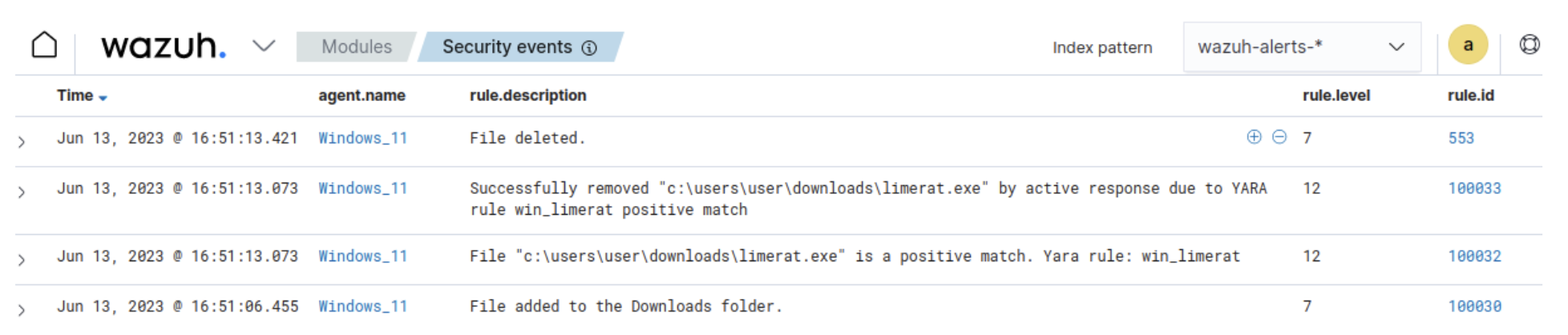
Detection results
The Wazuh dashboard generates alerts when LimeRAT is downloaded to the Downloads folder of the victim endpoint.Navigate to the Security events tab to view the generated alerts.
Conclusion
LimeRAT is a versatile piece of malware that gives attackers control over an infected endpoint. In this blog post, we used Sysmon integration with Wazuh to detect the behavior of LimeRAT. We also used YARA integration with Wazuh to detect and remove LimeRAT once it was downloaded to the endpoint.
Wazuh is a free and open source enterprise-ready security solution for threat detection, incident response, and compliance. Wazuh integrates seamlessly with third-party solutions and technologies. Wazuh also has an ever-growing community where users are supported. To learn more about Wazuh, please check out our documentation and blog posts.
References
