Meduza Stealer is a malware that is designed solely for comprehensive data theft. It is a powerful stealer that targets Windows operating systems. It steals system information and a wide range of browser-related information. These include sensitive login credentials, browsing history, saved bookmarks, crypto wallet extensions, password managers, and 2FA (two-factor authentication) extensions. Once stolen data is collected, Meduza Stealer attempts to send the data to the attacker’s command and control server.
Meduza Stealer infection could potentially lead to major data breaches and financial losses for affected organizations. The malware is primarily distributed through phishing emails or malicious attachments, and it can be difficult to detect once it has infected a system.
In this blog post, we use Wazuh to detect the malicious activities of Meduza Stealer.
Meduza behavior and capabilities
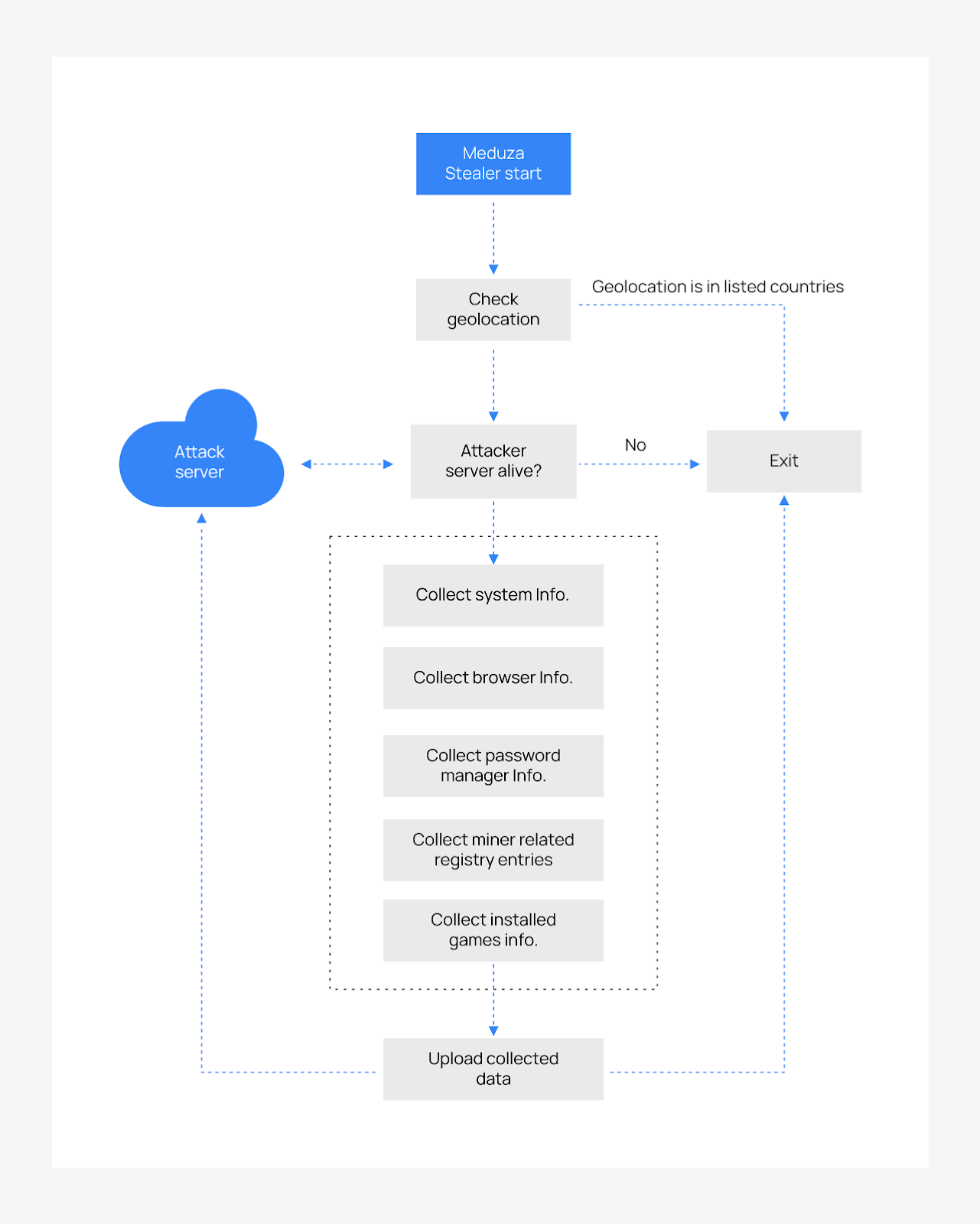
The malware starts by checking the geolocation of the affected endpoint. It leverages the GetUserGeoID and GetGeoInfoA APIs on the infected endpoint to obtain its country details. There is a predefined list of countries that are excluded from its infection. The malware terminates immediately If the infected endpoint’s location is within the predefined list of excluded countries as shown below:
| Country name | Country code |
| Russia | RU |
| Kazakhstan | KZ |
| Belarus | BY |
| Georgia | GE |
| Turkmenistan | TM |
| Uzbekistan | UZ |
| Armenia | AM |
| Kyrgyzstan | KG |
| Moldova | MD |
| Tajikistan | TJ |
If the infected endpoint’s location is not on the exclusion list, Meduza Stealer checks if its server is active. It attempts to establish a connection with the attacker’s server before initiating the data theft from affected endpoints. The stealer immediately terminates its activities if this server is not accessible and the connection fails. This adds complexity to any detection attempts to trace the stealers activities.
However, when the location check and server accessibility conditions are favorable, Meduza Stealer then begins to infiltrate the infected endpoint and gathers extensive information. This information includes browser data, system information, password manager data, mining-related registry data, and installed games. It gathers this information using some Windows APIs such as GetUserName, GetComputerName, GetCurrentHWProfile, and EnumDisplayDevices. The public IP address of the infected endpoint is retrieved using the HTTPS-based API found at https[:]//api.ipify[.]org.
Once this extensive collection of data is gathered, it is packaged and uploaded to the attacker’s remote server. This is the complete Meduza Stealer’s mode of operation within an infected endpoint. The malware is also able to evade detection from a number of top-tier antivirus solutions that have proven ineffective in detecting the stealer either statically or dynamically.
The malware’s administrator provides a web panel that allows subscribers to craft their customized binary. The web panel displays information such as affected OS names, IP addresses, geographical data, stolen passwords, cookies, and wallets. Malware subscribers can access these stolen data on the web panel.
Analyzed IOC file:
| MD5 | 82eecea4083e39c33733428c2d845b15 |
| SHA256 | ebd41d486952eddaa670358497f33abc615cd311fca173b8833575893aea83ef |
Infrastructure
To demonstrate the detection of Meduza Stealer with Wazuh, we use the following infrastructure.
- A pre-built ready-to-use Wazuh OVA 4.7.2. Follow this guide to download the virtual machine.
- A Windows 11 victim endpoint with Wazuh agent 4.7.2 installed. To install the Wazuh agent, refer to the following installation guide.
Detection with Wazuh
In this blog post, we integrate Sysmon and YARA with Wazuh to detect Meduza Stealer behavior on the victim endpoint.
Detection rules
We use Sysmon to monitor several system events and create rules on the Wazuh server to detect the malicious activities of Meduza Stealer malware.
Follow the steps below to detect the malicious activity performed by Meduza Stealer malware on the Windows endpoint.
Windows
Perform the following steps to configure the Wazuh agent to capture Sysmon logs and send them to the Wazuh server for analysis.
1. Download Sysmon from the Microsoft Sysinternals page.
2. Extract the compressed Sysmon file to your preferred location.
3. Download the Sysmon configuration file – sysmonconfig.xml using Powershell. Replace <SYSMON_EXECUTABLE_PATH> with the directory path to your Sysmon executable:
> wget -Uri https://wazuh.com/resources/blog/emulation-of-attack-techniques-and-detection-with-wazuh/sysmonconfig.xml -OutFile <SYSMON_EXECUTABLE_PATH>\sysmonconfig.xml
4. Switch to the directory with the Sysmon executable. Run the command below to install and start Sysmon using PowerShell with Administrator privileges:
> .\Sysmon64.exe -accepteula -i sysmonconfig.xml
5. Add the following configuration to the C:\Program Files (x86)\ossec-agent\ossec.conf file within the <ossec_config> block to collect and forward Sysmon event logs to the Wazuh server:
<localfile> <location>Microsoft-Windows-Sysmon/Operational</location> <log_format>eventchannel</log_format> </localfile>
6. Restart the Wazuh agent to apply the configuration changes:
> Restart-Service -Name wazuh
Wazuh server
In this section, we create rules to detect the behavior of Meduza Stealer on the Windows endpoint.
1. Add the rules below to the /var/ossec/etc/rules/local_rules.xml file on the Wazuh server:
<group name="meduza_stealer,sysmon,"> <!-- Rogue a.exe file creation --> <rule id="100020" level="12"> <if_sid>61617</if_sid> <field name="win.eventdata.image" type="pcre2">\.exe</field> <field name="win.eventdata.targetFilename" type="pcre2">(?i)([\\]+?)(a\.exe$)</field> <description>Potential Meduza Stealer activity detected: a.exe created at $(win.eventdata.targetFilename) by $(win.eventdata.image).</description> <mitre> <id>T1036</id> </mitre> </rule> <!-- Rogue a.exe:extractor.dll file creation --> <rule id="100021" level="12"> <if_sid>61613</if_sid> <field name="win.eventdata.image" type="pcre2">\.exe</field> <field name="win.eventdata.targetFilename" type="pcre2">(?i)([\\]+?)(a\.exe\:extractor\.dll$)</field> <description>Potential Meduza Stealer activity detected: DLL $(win.eventdata.targetFilename) created by a.exe and injected on $(win.system.computer).</description> </rule> <!-- Registry object created --> <rule id="100023" level="12"> <if_sid>61614</if_sid> <field name="win.eventdata.image" type="pcre2">(?i)[c-z]:\\\\Windows\\\\system32\\\\(consent\.exe$|svchost\.exe$)</field> <field name="win.eventdata.targetObject" type="pcre2" >HKU\\\\.+\\\\Software\\\\Microsoft\\\\SystemCertificates\\\\CA\\\\Certificates</field> <field name="win.eventdata.eventType" type="pcre2" >^CreateKey$</field> <description>Potential Meduza Stealer activity detected: $(win.eventdata.image) dumps credentials to $(win.eventdata.targetObject).</description> <mitre> <id>T1130</id> </mitre> </rule> <!-- File system permission weakness --> <rule id="100024" level="12"> <if_sid>61613</if_sid> <field name="win.eventdata.image" type="pcre2">(?i)[c-z]:\\\\Windows\\\\system32\\\\svchost\.exe</field> <field name="win.eventdata.targetFilename" type="pcre2">(?i)[c-z]:\\\\Windows\\\\Prefetch\\\\(EBD41D486952EDDAA670358497F33)(-.+\.pf$)</field> <description>Potential Meduza Stealer activity detected:$(win.eventdata.targetFilename) created by $(win.eventdata.image).</description> <mitre> <id>T1047</id> </mitre> </rule> <!-- Suspicious command execution --> <rule id="100025" level="12" > <if_sid>61603</if_sid> <field name="win.eventdata.parentCommandLine" type="pcre2">(?i)[c-z]:\\\\Windows\\\\System32\\\\svchost\.exe\s-k\sWerSvcGroup</field> <field name="win.eventdata.commandLine" type="pcre2">(?i)[c-z]:\\\\Windows\\\\system32\\\\WerFault\.exe\s-pss\s-s\s\d+\s-p\s\d+\s-ip\s\d+</field> <description>Potential Meduza Stealer activity detected: suspicious command execution $(win.eventdata.commandLine).</description> <mitre> <id>T1546.008</id> </mitre> </rule> </group>
Where:
- Rule ID
100020is triggered when Meduza Stealer creates ana.exefile. - Rule ID
100021is triggered when Meduza Stealer creates anencryptor.dllfile. - Rule ID
100023is triggered when Meduza Stealer creates a registry key file. - Rule ID
100024is triggered when Meduza Stealer exploits the file system permissions. - Rule ID
100025is triggered when Meduza Stealer executes suspicious commands.
2. Restart the Wazuh manager to apply the configuration changes:
# systemctl restart wazuh-manager
Detection results
Below is the image of the alerts generated on the Wazuh dashboard when a Windows endpoint is infected by Meduza Stealer.
Navigate to the Security events tab to view the generated alerts.

YARA integration
There are various ways Wazuh can integrate with YARA. We focus on utilizing the Wazuh File Integrity Monitoring (FIM) module, Wazuh active response module, and YARA:
- The Wazuh FIM module detects and generates alerts when files are created, modified, or deleted. In this blog post, the Wazuh FIM module is enabled for the
Downloadsfolder within the Windows filesystem, and FIM alerts are generated for any activity in the FIM-monitored directory. - The Wazuh active response module executes predefined scripts when certain alerts occur. In this scenario, the FIM alerts automatically trigger the Wazuh active response script to execute YARA scans on the file that is added or modified.
- YARA is an open source pattern-matching tool used to identify malware samples. When there is a positive YARA match, a YARA alert gets generated, the file is marked as malicious and the active response script immediately deletes the file.
Windows
Install the following packages on the victim endpoint. These are required to download and install YARA.
1. Python v 3.12.0 or later (with pip pre-installed). Check the following boxes when prompted:
- Use admin privileges when installing py.exe
- Add
Python.exeto PATH. This places the interpreter in the execution path.
2. Microsoft Visual C++ 2015 Redistributable.
After installing the above packages, follow the steps below to download the YARA executable:
1. Launch PowerShell with administrator privileges and download YARA:
> Invoke-WebRequest -Uri https://github.com/VirusTotal/yara/releases/download/v4.3.1/yara-4.3.1-2141-win64.zip -OutFile v4.3.1-2141-win64.zip
2. Extract the YARA executable:
> Expand-Archive v4.3.1-2141-win64.zip
3. Create a folder called C:\Program Files (x86)\ossec-agent\active-response\bin\yara\ and copy the YARA binary into it:
> mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\' > cp .\v4.3.1-2141-win64\yara64.exe 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\'
Follow the steps below to download YARA rules:
1. Using the same PowerShell terminal launched earlier, install valhallaAPI using the pip utility. The valhallaAPI is used to retrieve the public signature-base YARA ruleset:
> pip install valhallaAPI
2. Create the file download_yara_rules.py, and copy the following script into it:
from valhallaAPI.valhalla import ValhallaAPI
v = ValhallaAPI(api_key="1111111111111111111111111111111111111111111111111111111111111111")
response = v.get_rules_text()
with open('yara_rules.yar', 'w') as fh:
fh.write(response)
3. Download YARA rules and copy them to the C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\ folder:
> python download_yara_rules.py > mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\' > cp yara_rules.yar 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\'
4. Edit the C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yar file and add the following Meduza Stealer YARA rules:
rule Wazuh_Meduza
{
meta:
malware_name = "Meduza"
description = "Meduza is a trojan stealer that gathers sensitive data such as browser cookies, histories, crypto wallet information, and more from infected machines."
author = "Iseoluwa Titiloye Oyeniyi"
version = "1"
strings:
$x1 = "autofill-profiles.json" ascii wide
$x2 = "formhistory.sqlite" ascii wide
$x3 = "logins.json" ascii wide
$x4 = "cookies.sqlite" ascii wide
$x5 = "key4.db" ascii wide
$x6 = "Electrum\\config" ascii wide
$x7 = "Sparrow\\wallets" ascii wide
$x8 = "Coinomi\\wallets" ascii wide
$x9 = "Electrum-LTC\\wallets" ascii wide
$x10 = "Mozilla\\SeaMonkey" ascii wide
$x11 = "Yandex\\YandexBrowser" ascii wide
$x12 = "BrowserPass" ascii wide
$x13 = "`anonymous namespace'" ascii wide
$x14 = "api-ms-" ascii wide
$x15 = "FlsAlloc" ascii wide
$x16 = "mscoree.dll" ascii wide
$x17 = "AppPolicyGetProcessTerminationMethod" ascii wide
condition:
3 of ( $x* )
}
5. Edit the C:\Program Files (x86)\ossec-agent\ossec.conf file and add the below configuration within the <syscheck> block to monitor the Downloads folders of all users in real-time:
<directories realtime="yes">C:\Users\*\Downloads</directories>
Note: In this blog post, the Downloads folders of all users are monitored. However, you can configure other folders you wish to monitor.
6. Create a batch file yara.bat in the C:\Program Files (x86)\ossec-agent\active-response\bin\ folder. The active response module uses this file to perform YARA scans for malware detection and removal:
:: This script deletes Meduza Stealer as well as other malicious files matched by the YARA Rules
@echo off
setlocal enableDelayedExpansion
reg Query "HKLM\Hardware\Description\System\CentralProcessor\0" | find /i "x86" > NUL && SET OS=32BIT || SET OS=64BIT
if %OS%==32BIT (
SET log_file_path="%programfiles%\ossec-agent\active-response\active-responses.log"
)
if %OS%==64BIT (
SET log_file_path="%programfiles(x86)%\ossec-agent\active-response\active-responses.log"
)
set input=
for /f "delims=" %%a in ('PowerShell -command "$logInput = Read-Host; Write-Output $logInput"') do (
set input=%%a
)
set json_file_path="C:\Program Files (x86)\ossec-agent\active-response\stdin.txt"
set syscheck_file_path=
echo %input% > %json_file_path%
FOR /F "tokens=* USEBACKQ" %%F IN (`Powershell -Nop -C "(Get-Content 'C:\Program Files (x86)\ossec-agent\active-response\stdin.txt'|ConvertFrom-Json).parameters.alert.syscheck.path"`) DO (
SET syscheck_file_path=%%F
)
set yara_exe_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\yara64.exe"
set yara_rules_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yar"
echo %syscheck_file_path% >> %log_file_path%
for /f "delims=" %%a in ('powershell -command "& \"%yara_exe_path%\" \"%yara_rules_path%\" \"%syscheck_file_path%\""') do (
echo wazuh-yara: INFO - Scan result: %%a >> %log_file_path%
:: Deleting the scanned file.
del /f "%syscheck_file_path%" >nul 2>&1
if exist "%syscheck_file_path%" (
echo wazuh-yara: INFO - Error removing threat: %%a >> %log_file_path%
) else (
echo wazuh-yara: INFO - Successfully deleted: %%a >> %log_file_path%
)
)
exit /b
7. Restart the Wazuh agent using PowerShell for the changes to take effect:
> Restart-Service -Name wazuh
Wazuh server
Take the following steps to configure custom decoders, rules, and active response on the Wazuh server.
1. Create custom rules in the /var/ossec/etc/rules/local_rules.xml file. These rules will provide alerts about files that are added or modified in the /Downloads directory on the monitored endpoint:
<group name= "syscheck,">
<rule id="100029" level="7">
<if_sid>550</if_sid>
<field name="file" type="pcre2">(?i)C:\\Users.+Downloads</field>
<description>File modified in the Downloads folder.</description>
</rule>
<rule id="100030" level="7">
<if_sid>554</if_sid>
<field name="file" type="pcre2">(?i)C:\\Users.+Downloads</field>
<description>File added to the Downloads folder.</description>
</rule>
</group>
Where:
- Rule ID
100029is triggered when a file is modified in the/Downloadsdirectory. - Rule ID
100030is triggered when a file is added to the/Downloadsdirectory.
2. Add the following configuration to the /var/ossec/etc/ossec.conf file within the <ossec_config> block:
<command> <name>yara</name> <executable>yara.bat</executable> <timeout_allowed>no</timeout_allowed> </command> <active-response> <command>yara</command> <location>local</location> <rules_id>100029,100030</rules_id> </active-response>
The Wazuh FIM module executes the yara.bat script when a file is added or modified in the Downloads folder.
Where:
<name>specifies the name of the command being called in the active response section.<executable>specifies the executable file to run.<command>specifies the command that will be used by the active response.- The
<active response>block calls the<command>block when the rule ID100029or100030triggers an alert. <location>specifies where the active response script is executed.
3. Add the following decoders to the /var/ossec/etc/decoders/local_decoder.xml file to decode the logs generated by the active response script:
<decoder name="yara_decoder">
<prematch>wazuh-yara:</prematch>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Scan result: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Successfully deleted: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Error removing threat: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
4. Create custom rules in the /var/ossec/etc/rules/local_rules.xml to alert when there is a YARA active response action:
<!-- Rule for the decoder (yara_decoder) -->
<group name="yara,">
<rule id="100031" level="0">
<decoded_as>yara_decoder</decoded_as>
<description>Yara grouping rule</description>
</rule>
<!-- YARA scan detects a positive match -->
<rule id="100032" level="12">
<if_sid>100031</if_sid>
<match type="pcre2">wazuh-yara: INFO - Scan result: </match>
<description>File "$(yara_scanned_file)" is a positive match. Yara rule: $(yara_rule)</description>
</rule>
<!-- Wazuh successfully deletes a malware with a positive match -->
<rule id="100033" level="12">
<if_sid>100031</if_sid>
<match type="pcre2">wazuh-yara: INFO - Successfully deleted: </match>
<description>Successfully removed "$(yara_scanned_file)" by active response due to YARA rule $(yara_rule) positive match</description>
</rule>
<!-- Wazuh encounters an error when deleting a malware with a positive match -->
<rule id="100034" level="12">
<if_sid>100031</if_sid>
<match type="pcre2">wazuh-yara: INFO - Error removing threat: </match>
<description>Error removing "$(yara_scanned_file)". YARA rule: $(yara_rule)</description>
</rule>
</group>
Where:
- Rule ID
100031is the base rule for detecting YARA events. - Rule ID
100032is triggered when YARA scans and detects a malicious file. - Rule ID
100033is triggered when the detected file has been successfully removed by Wazuh active response. - Rule ID
100034is triggered when the detected file is not removed successfully by Wazuh active response.
4. Restart the Wazuh manager for the changes to take effect:
$ sudo systemctl restart wazuh-manager
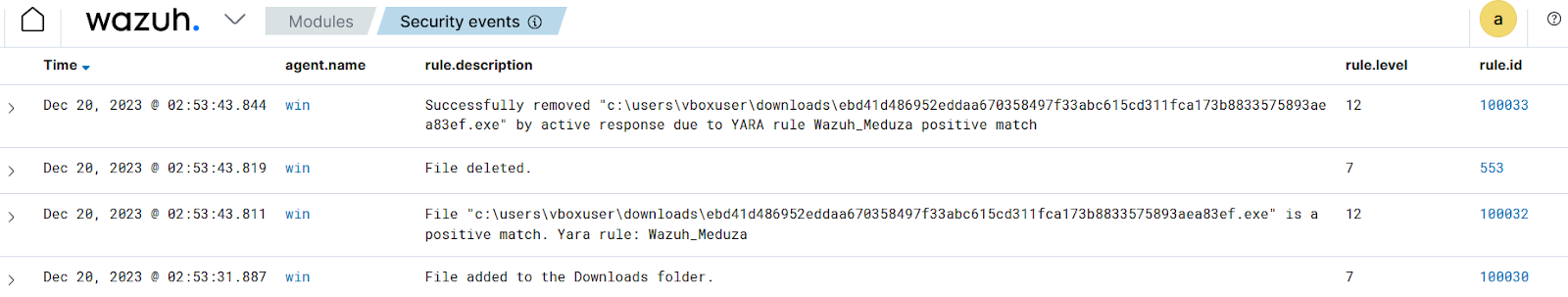
Detection results
The Wazuh dashboard generates alerts when Meduza Stealer is downloaded to the Downloads folder of the victim endpoint.Navigate to the Security events tab to view the generated alerts.
Conclusion
Meduza Stealer is a comprehensive stealer malware. In this blog post, we used Sysmon integration with Wazuh to detect the behavior of Meduza Stealer. We also used YARA integration with Wazuh to detect and remove Meduza Stealer once it was downloaded to the endpoint.
Wazuh is a free and open source enterprise-ready security solution for threat detection, incident response, and compliance. Wazuh integrates seamlessly with third-party solutions and technologies. Wazuh also has an ever-growing community where users are supported. To learn more about Wazuh, please check out our documentation and blog posts.
References
