Wazuh is an open source security solution that helps organizations detect and respond to security threats. Wazuh can be configured to detect a wide range of system activities having various security levels. From informational to critical incidents, the Wazuh ruleset is constantly updated to ensure an organization stays ahead of the threat landscape. An aspect of this landscape administrators often undermine are USB related activities.
USB drives are portable storage devices that connect to a computer’s USB port. It is important to monitor these ports because they often serve as an introductory point for malware into a computer endpoint and network. Organizations need to monitor all USB activities to prevent data breaches, curb the spread of malware, and protect sensitive information.
This blog post guides you on how to monitor USB drives that are plugged into Windows endpoints. Additionally, it describes how to configure filters for authorized and unauthorized USB drives.
Prerequisites
- A pre-built ready-to-use Wazuh OVA 4.3.10. Follow the steps in the Virtual Machine (OVA) documentation to download and set this up.
- A Windows 10 endpoint with the Wazuh agent installed and enrolled to the Wazuh server.
Configuration
Windows endpoint
The Audit PNP Activity is a Windows feature that helps detect USB drives and generate Plug and Play (PnP) events. This feature is available on Windows 10, Windows Server 2016, and later versions.
Perform the following steps to enable this feature:
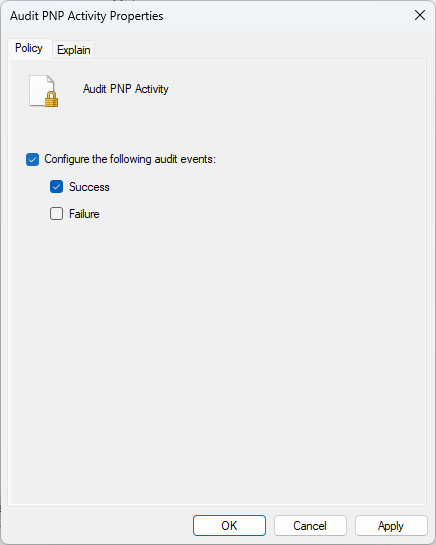
1. Launch the Windows Run utility using the Windows + R key combination. Type secpol.msc in the input box and click OK. This opens the Local Security Policy window, as shown below.
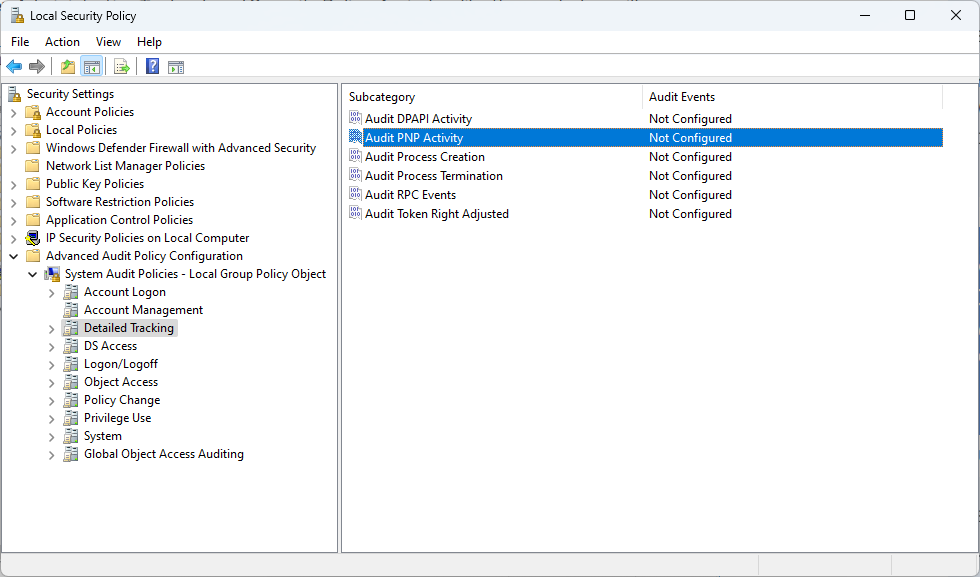
2. Navigate to Advanced Audit Policy Configuration > System Audit Policies – Local Group Policy Object > Detailed Tracking and double click Audit PNP Activity. In the new pop-up window, enable the policy by selecting Configure the following audit events: and Success. Click OK.
In this blog post, we consider the Windows event ID 6416, which is responsible for auditing external devices.
Note
An Audit PNP Activity generates four events when an external USB drive is plugged in. You can verify this using the Windows Event Viewer tool.
Wazuh server
In this section, we create a custom rule to detect USB drive activities on a monitored Windows endpoint.
1. Add the following rule to the Wazuh server /var/ossec/etc/rules/local_rules.xml file:
<group name="windows-usb-detect,">
<rule id="111000" level="7">
<if_sid>60103</if_sid>
<field name="win.system.eventID">^6416$</field>
<match>USBSTOR\\Disk</match>
<options>no_full_log</options>
<description>Windows: A PNP device $(win.eventdata.deviceDescription) was connected to $(win.system.computer)</description>
</rule>
</group>
Where:
- Rule ID
111000detects an event with WindowseventID6416. This type of event occurs when a Windows system recognizes an external device. In our case, it refers to a USB drive connected to the monitored Windows endpoint. <match>detects the event that has theUSBSTOR\\Diskkeyword in it. This keyword includes the vendor name, product name, revision number, and serial number. Events with other USB-related keywords are ignored.
2. Restart the Wazuh manager for the changes to take effect:
# systemctl restart wazuh-manager
Test the configuration
Perform the action below to generate USB events.
1. Plug a USB device into the monitored Windows endpoint.
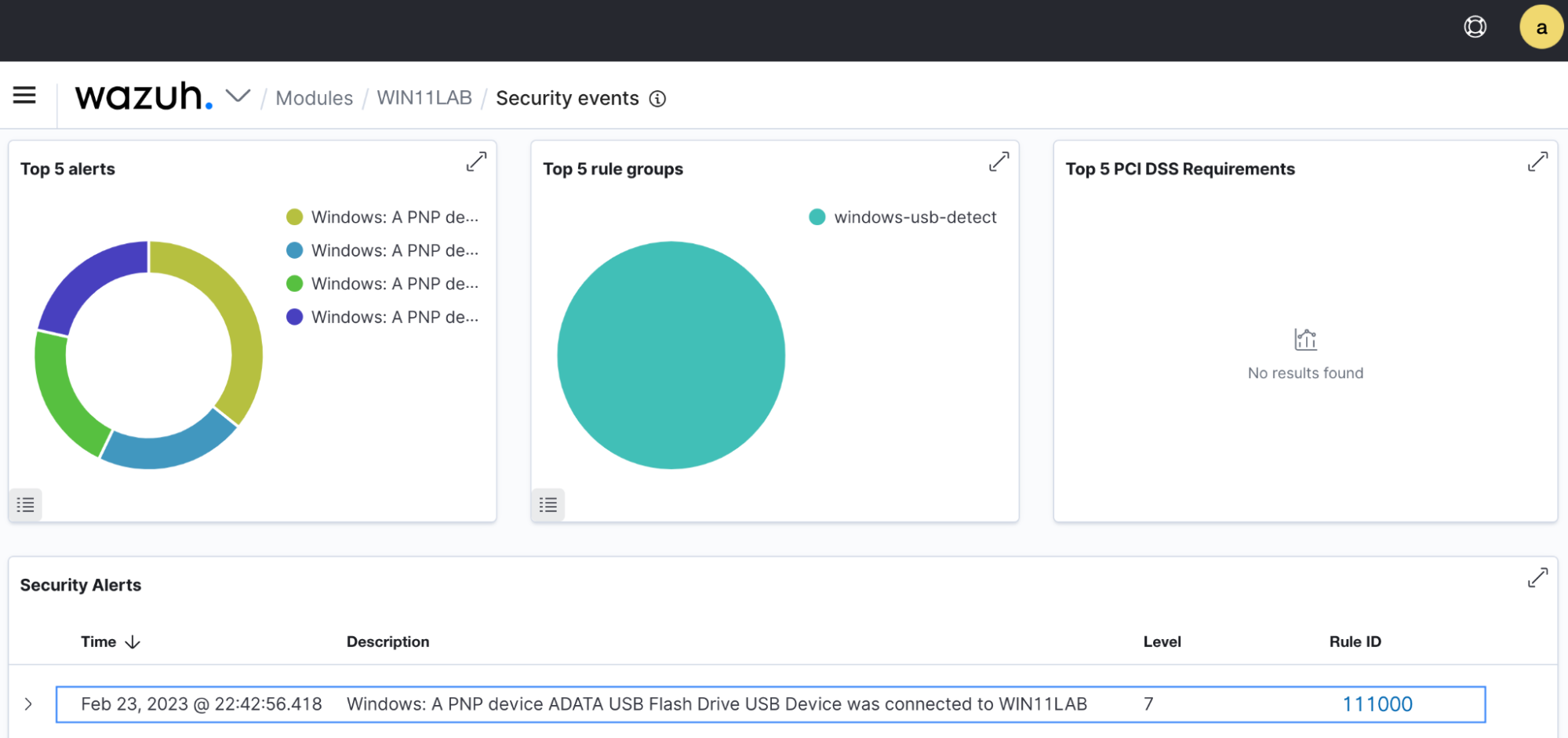
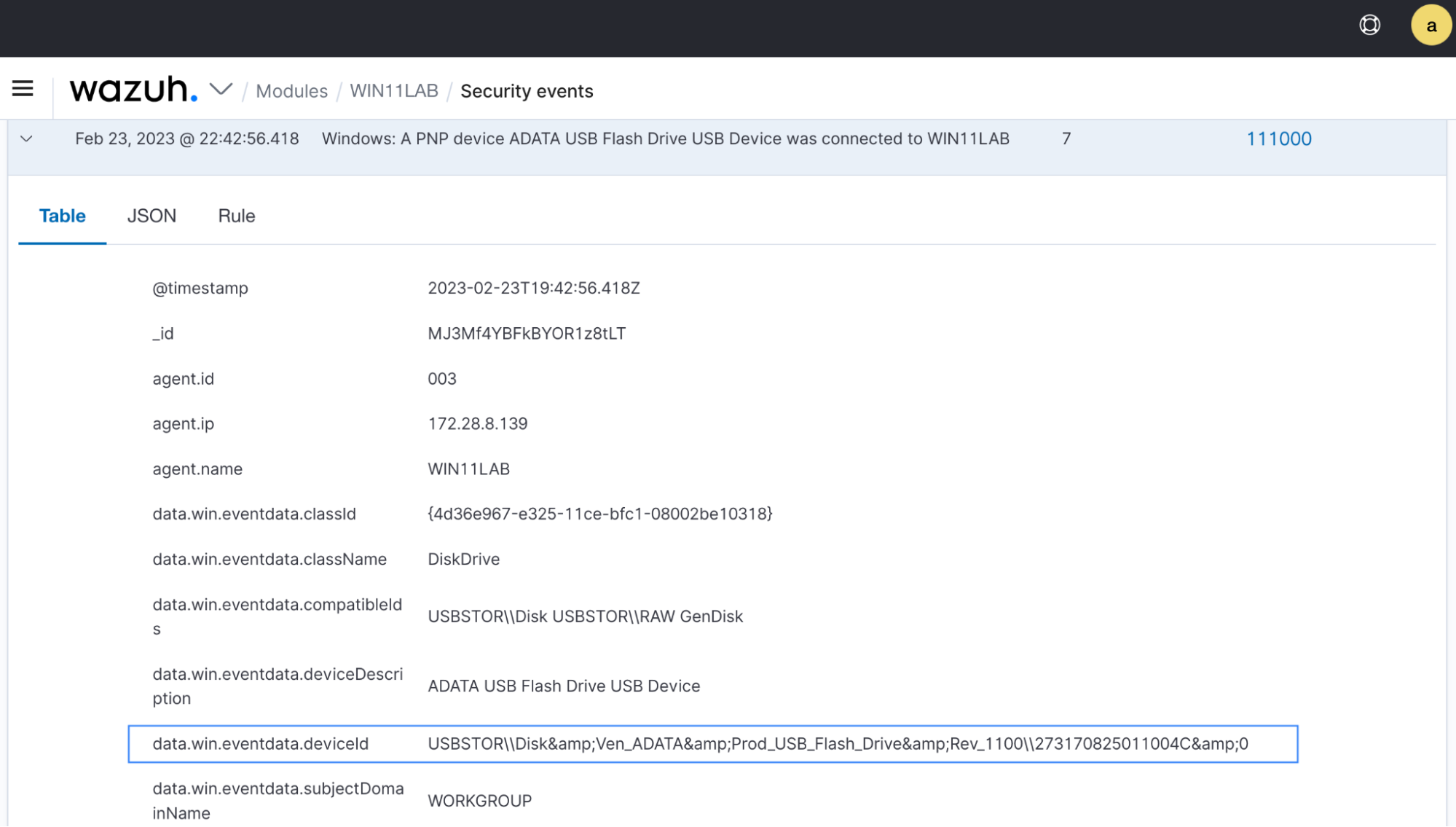
Navigate to the Security events tab in the Wazuh dashboard to see the alerts generated. The image below shows the alerts generated when a USB drive is inserted into the monitored Windows endpoint.
Filtering authorized and unauthorized USB drives
Perform the steps below to trigger alerts when authorized and unauthorized USB drives are inserted into the monitored Windows endpoint.
Creating a CDB list for authorized USB drives
You must create a CDB (constant database) list of authorized USB drives using their deviceId fields. We need a list of authorized devices for matching with detected drive activities. A drive not included on this list will be flagged as unauthorized.
1. On the Wazuh dashboard, expand the rule ID 111000 alert and extract the value from the data.win.eventdata.deviceId field. This field contains the vendor name, product name, revision number, and serial number. The image below shows the deviceId extracted from the alert generated earlier.
2. On the Wazuh server, create a usb-drives CDB list in the /var/ossec/etc/lists directory:
$ sudo touch /var/ossec/etc/lists/usb-drives
3. Add the extracted deviceId value followed by a colon(:) to the CDB list:
USBSTOR\\Disk&Ven_ADATA&Prod_USB_Flash_Drive&Rev_1100\\273170825011004C&0:
CBD lists typically use <key>:<value> pairs but can also accept a <key>: value. For more information on CDB lists, see the CDB lists guide.
4. Add <list>etc/lists/usb-drives</list> to the <ruleset> block of the /var/ossec/etc/ossec.conf file. These changes take effect once you restart the Wazuh manager in the next steps.
<ruleset> <!-- Default ruleset --> <decoder_dir>ruleset/decoders</decoder_dir> <rule_dir>ruleset/rules</rule_dir> <rule_exclude>0215-policy_rules.xml</rule_exclude> <list>etc/lists/audit-keys</list> <list>etc/lists/amazon/aws-eventnames</list> <list>etc/lists/security-eventchannel</list> <!-- User-defined ruleset --> <decoder_dir>etc/decoders</decoder_dir> <rule_dir>etc/rules</rule_dir> <list>etc/lists/usb-drives</list> </ruleset>
Our next step would be to create custom rules that match with the CDB list.
Adding rules for USB filtering
In this section, we create two new rules that detect authorized and unauthorized USB drives. Perform the steps below to add the rules to the Wazuh server.
1. Add the following rules to the previously created windows-usb-detect group in the /var/ossec/etc/rules/local_rules.xml file:
<rule id="111001" level="5"> <if_sid>111000</if_sid> <options>no_full_log</options> <description>Windows: Authorized PNP device $(win.eventdata.deviceDescription) was connected to $(win.system.computer).</description> </rule> <rule id="111002" level="8"> <if_sid>111000</if_sid> <list field="win.eventdata.deviceId" lookup="not_match_key">etc/lists/usb-drives</list> <options>no_full_log</options> <description>Windows: Unauthorized PNP device $(win.eventdata.deviceDescription) was connected to $(win.system.computer).</description> </rule>
Where:
- Rule ID
111001generates alerts when authorized USB drives are plugged into the endpoint. - Rule ID
111002generates alerts when unauthorized USB drives are plugged into the endpoint. This occurs when thedeviceIdis not found in the CDB list.
2. Restart the Wazuh manager for the changes to take effect.
# systemctl restart wazuh-manager
Test the configuration
Perform the following actions to detect authorized and unauthorized USB drives.
1. Plug an authorized USB device into the Windows endpoint. This should be the device whose deviceId field you added to the CDB list created earlier.
2. Plug an unauthorized USB device into the Windows endpoint. Its deviceId field should not be in the CDB list created earlier.
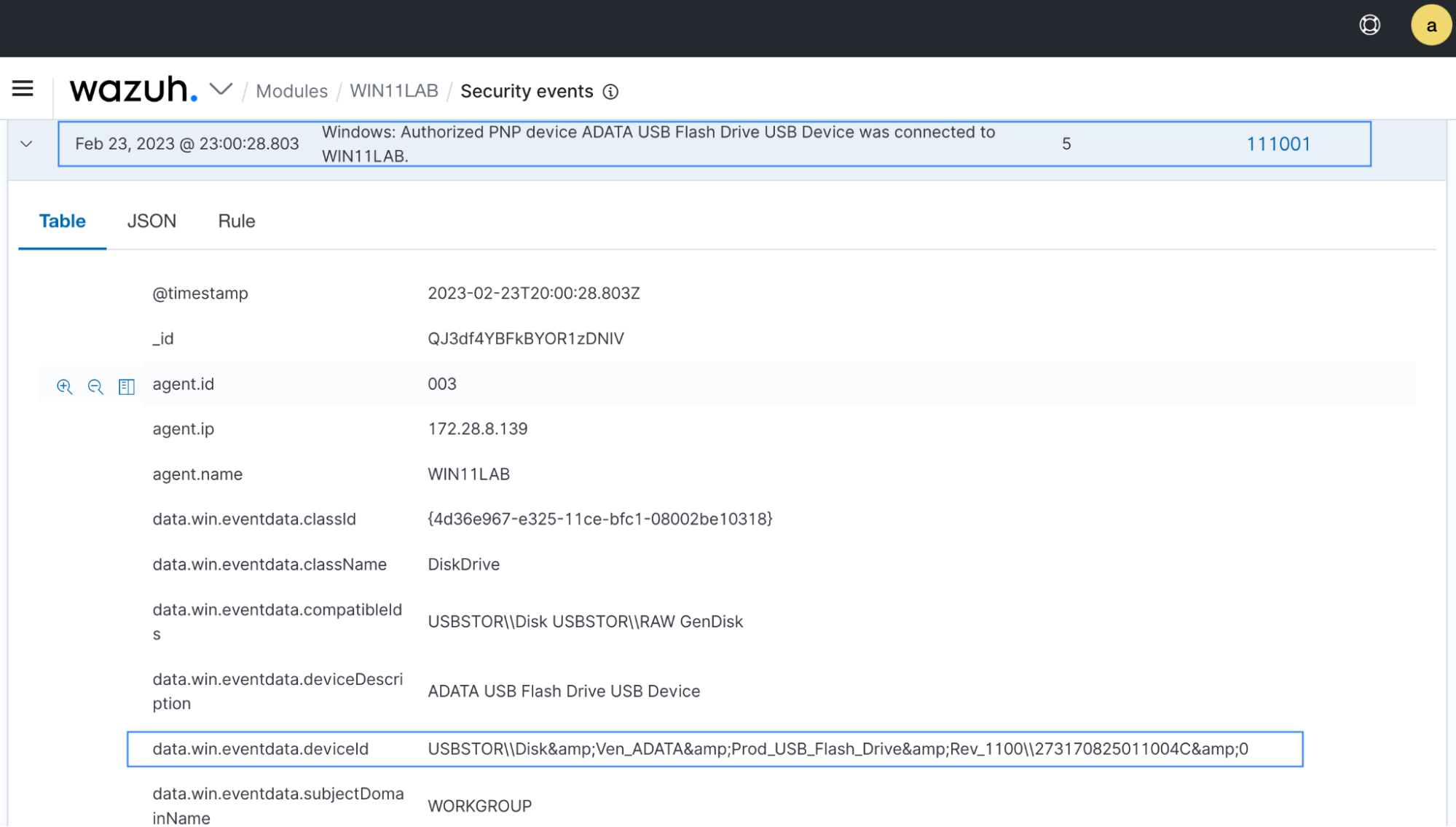
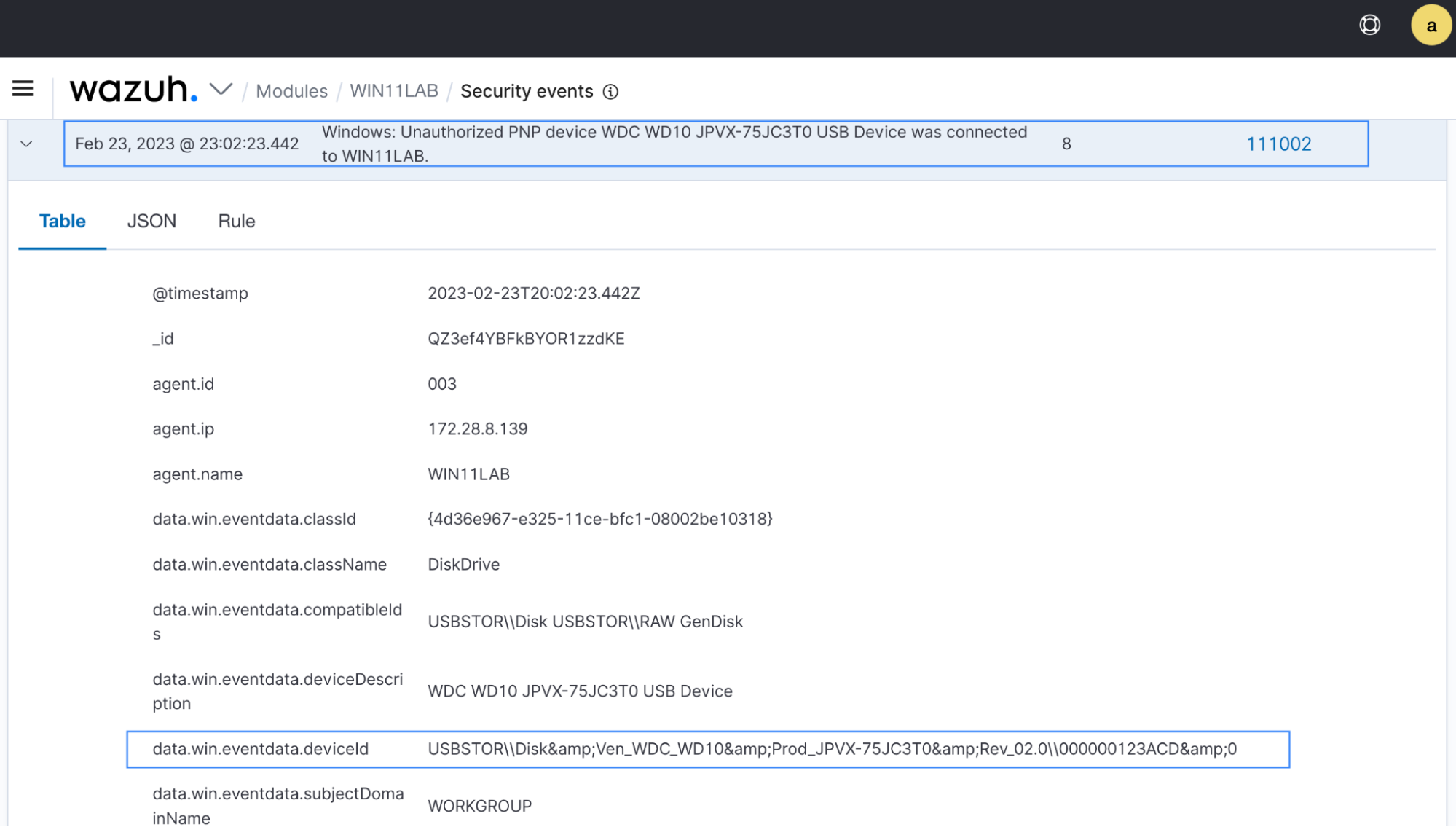
Navigate to the Security events in the Wazuh dashboard to see the alerts generated. Figure 5 shows an authorized USB drive event, and Figure 6 shows an unauthorized USB drive event.
Import custom visualization for authorized and unauthorized drive alerts
We have created a custom visualization that displays authorized and unauthorized USB drives. In this section, we describe how to import the custom visualization in the Wazuh dashboard.
Perform the steps below to import the custom visualization file.
1. Download the custom visualization file windows-usb-drive-monitoring-visualization.ndjson.
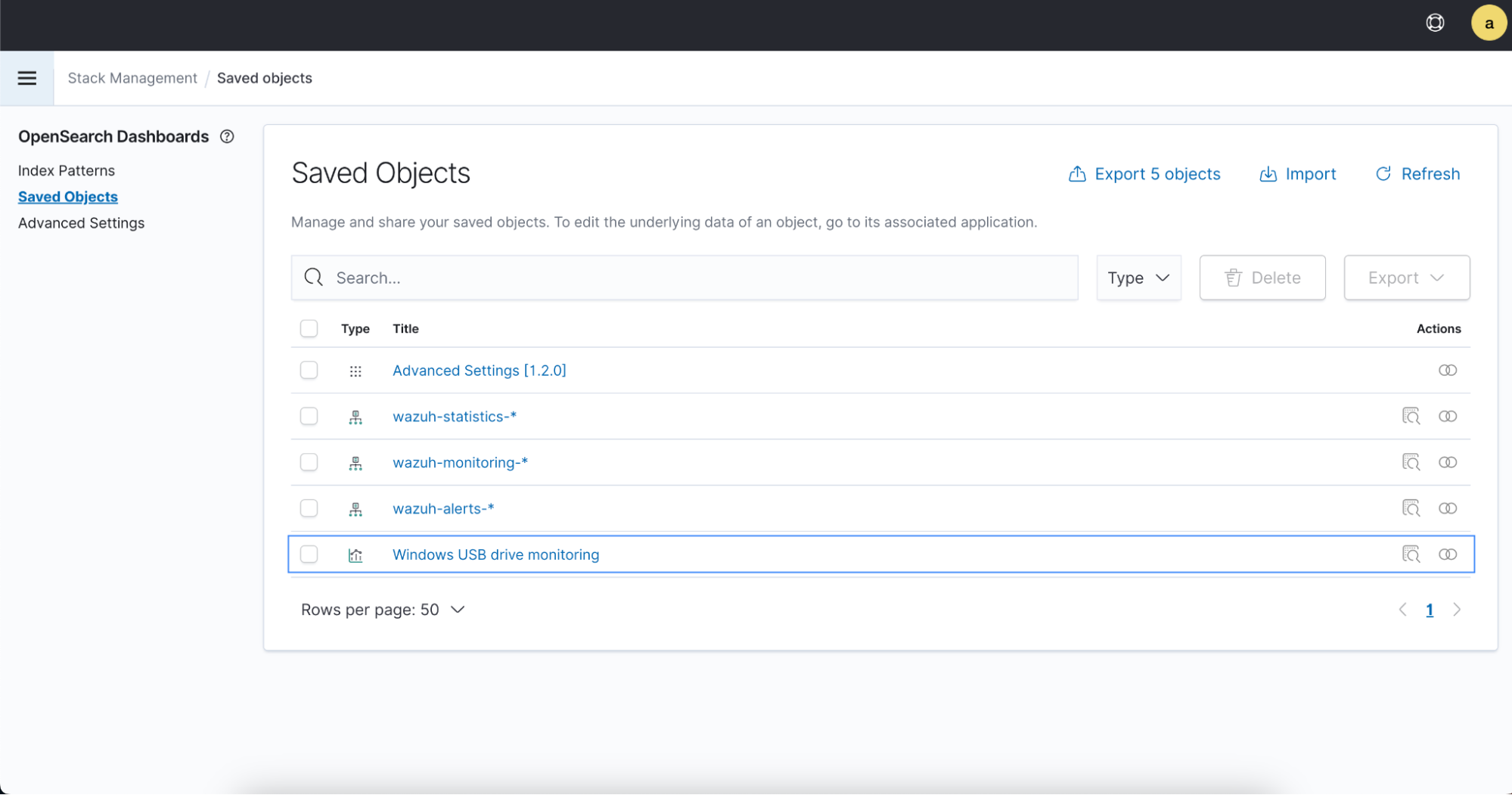
2. Select the Import option from Management > Stack Management > Saved Object to import the downloaded visualization file.
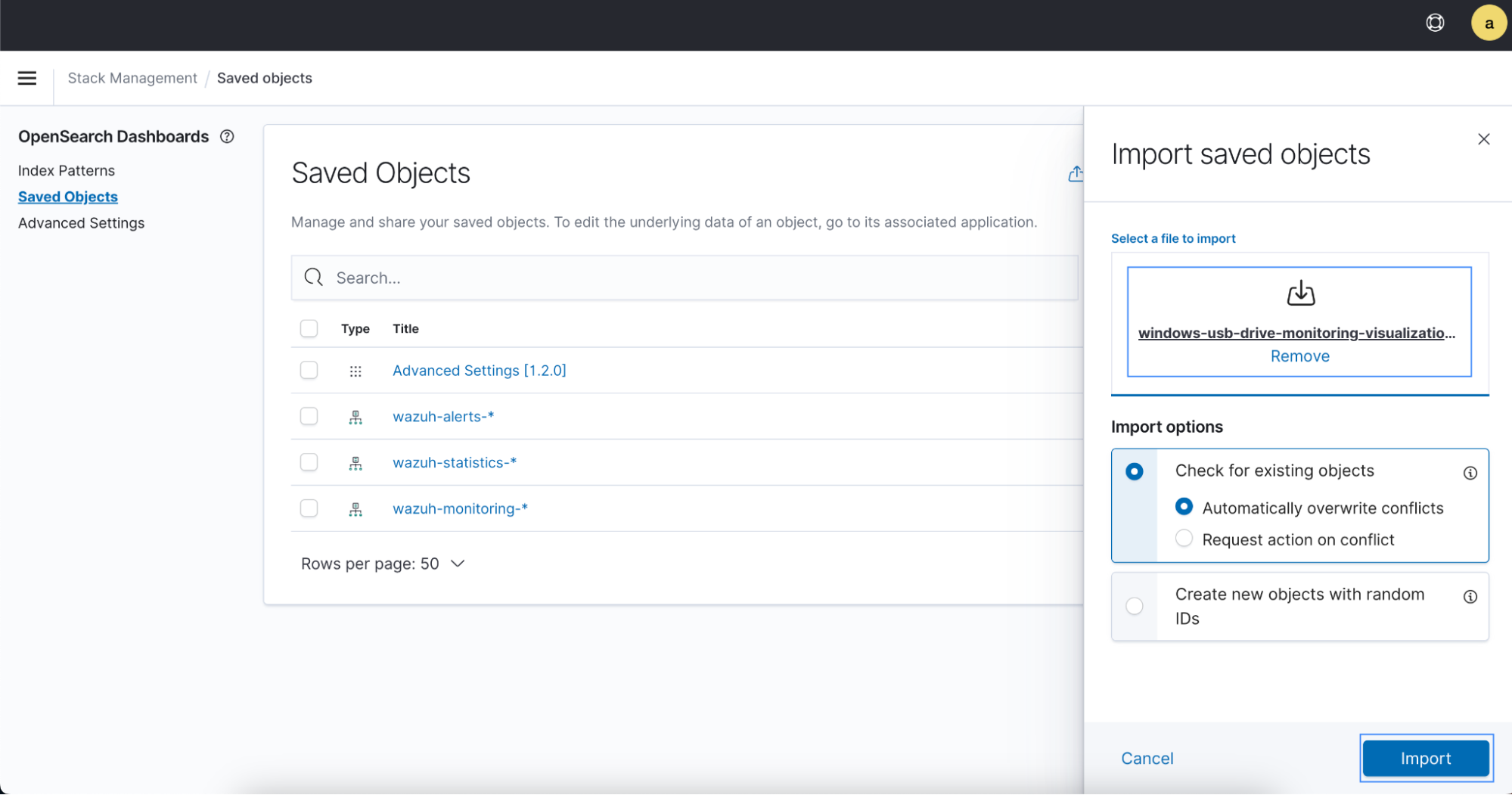
After a successful import, the new object named Windows USB drive monitoring should be visible in the Saved Objects list.
3. Select the Windows USB drive monitoring file to view its contents. The image below shows authorized and unauthorized USB drive alerts generated by rule ID 111001 and 111002.
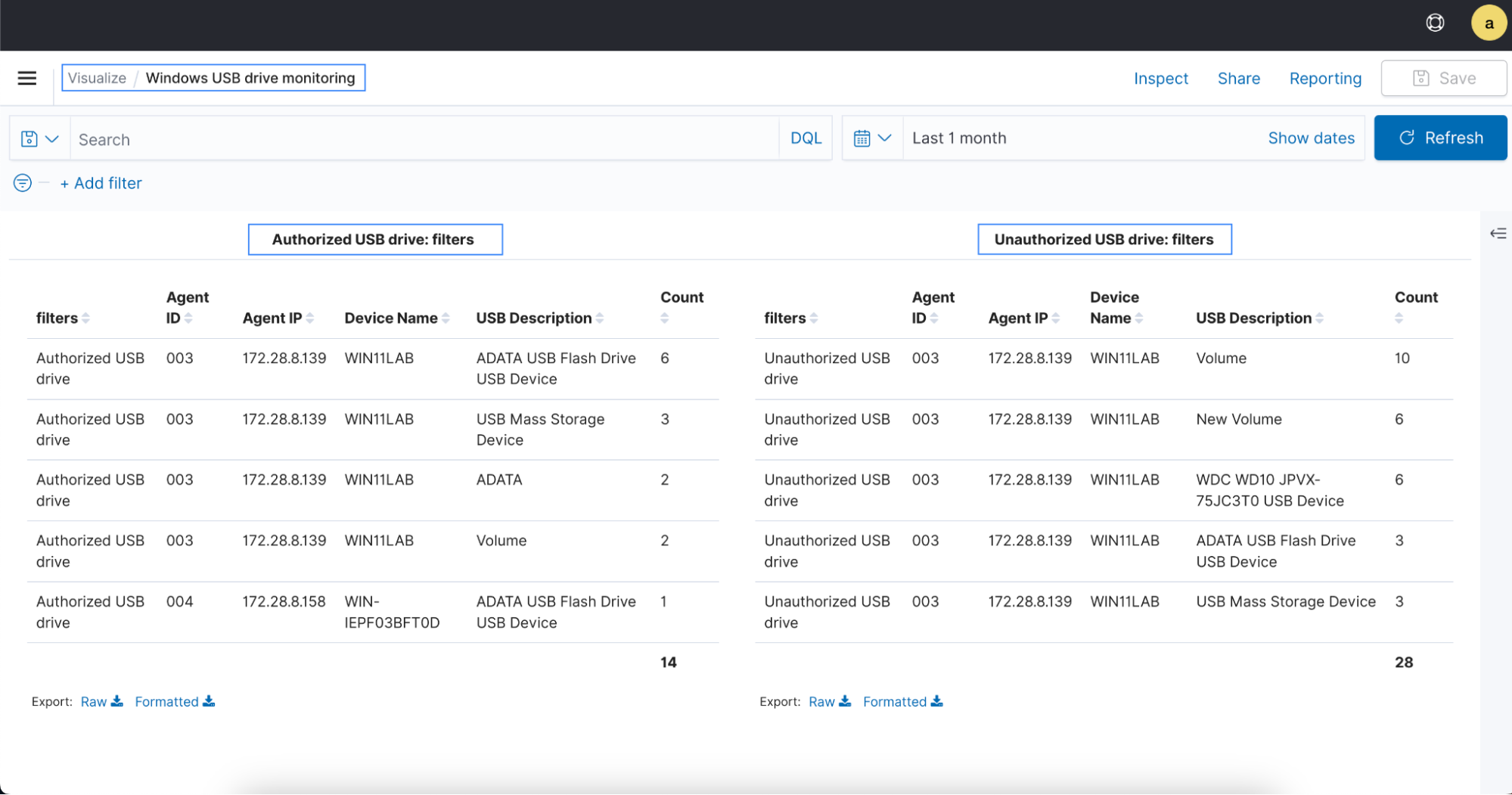
The imported custom visualization object is also visible in the Visualize section under OpenSearch Dashboards.
Conclusion
This blog post describes how Wazuh can help organizations to monitor USB drives plugged into monitored Windows endpoints in real-time. It also shows how to configure the Wazuh CDB list to filter authorized and unauthorized USB drives. By monitoring USB drives, you can protect organizational data from theft, and stop USB transferrable malware attacks, thereby improving your organization’s security.
Wazuh provides a comprehensive solution to secure your critical assets in various ways. To learn more about Wazuh capabilities, visit our documentation and other blog posts.