Wazuh 3.11 introduced a new capability: Vulnerability Detection for Windows. Using the National Vulnerability Database, Wazuh can detect vulnerabilities on Windows hosts by looking at their installed software and Windows updates.
In 2019, more than 700 vulnerabilities were discovered in Microsoft operating systems. As soon as they are in Microsoft’s hands, they start planning, developing and publishing the patches that fix them. Also, every Windows software manufacturer has to be aware of all the affected vulnerabilities in their Windows software.
In this post, we will show you how to configure it and what vulnerabilities affect a Vagrant Windows server default box. We will use the Wazuh OVA.
Getting started
For this tutorial you will need:
- Wazuh manager v3.11.0 or higher.
- Vagrant.
Once we have the Wazuh manager and Elastic stack configured (you can learn how to install Wazuh manager and Elastic stack, or you can download all the stack in OVA format, which will be used in this example), we can import it by using Vmware, VirtualBox, or another provider of your choice. After importing it, get access to it via SSH.
Then, we need to choose a Vagrant box, to be used in this demo. We used the Vagrant Discover tool, searching by “Windows”. We will use the most downloaded one. After having the Windows host running, you should install and configure a Wazuh agent for windows v3.11.0 or higher.
Vulnerability Detection configuration
The Vulnerability Detection works on the manager’s side because it stores the inventory of the connected agents. Let’s see how can we make it work. The file /var/ossec/etc/ossec.conf contains the following section:
<vulnerability-detector>
<enabled>no</enabled>
<interval>5m</interval>
<ignore_time>6h</ignore_time>
<run_on_start>yes</run_on_start>
<provider name="canonical">
<enabled>no</enabled>
<os>precise</os>
<os>trusty</os>
<os>xenial</os>
<os>bionic</os>
<update_interval>1h</update_interval>
</provider>
<provider name="debian">
<enabled>no</enabled>
<os>wheezy</os>
<os>stretch</os>
<os>jessie</os>
<os>buster</os>
<update_interval>1h</update_interval>
</provider>
<provider name="redhat">
<enabled>no</enabled>
<update_from_year>2010</update_from_year>
<update_interval>1h</update_interval>
</provider>
<provider name="nvd">
<enabled>no</enabled>
<update_from_year>2010</update_from_year>
<update_interval>1h</update_interval>
</provider>
</vulnerability-detector>
By default, the Vulnerability Detector capability is disabled. To turn it on, change the enabled tag value to yes. The interval setting is the elapsed time between vulnerability scans. The ignore_time is the time during which the vulnerabilities that have already generated an alert will not generate another alert. run_on_start defines if the Vulnerability scan and the database updates run immediately when service is started.
After those main settings, the Vulnerability providers are defined. In this case, we will just enable the NVD provider as it is needed to detect Windows vulnerabilities. We suggest that you only enable providers that match your agents’ operating system. That way you will save disk space and the download time for unnecessary resources.
In this provider section, change the enabled value from no to yes. The setting update_from_year indicates the year from which the indexed vulnerabilities are going to be downloaded. The update_interval shows the frequency in which the module will check if a new version of the feed is available, in which case it will be updated.
Further configuration settings can be found in the Wazuh documentation.
After setting up the two enabled labels to yes, restart the manager to apply the new configuration: systemctl restart wazuh-manager or service wazuh-manager restart.
Running the assessment
Once the new Vulnerability Detector configuration has been saved and the Wazuh manager service restarted, you will have access to the vulnerability report for the Windows agent in the WUI (Wazuh user interface) after the scanner completes the following steps:
- At start-up, it downloads the needed resources from the providers, the NVD in this case.
- After the feeds download, the module runs for every agent whose inventory is available.
- You can check the Vulnerability Detector is running properly in the
/var/ossec/logs/ossec.logfile.
When the Wazuh manager updates the NVD database, this message must appear in the /var/ossec/logs/ossec.log file:
2020/02/04 11:30:34 wazuh-modulesd:vulnerability-detector: INFO: (5461): Starting National Vulnerability Database database update.
The updated database will be ready when the following message appears:
2020/02/04 11:45:47 wazuh-modulesd:vulnerability-detector: INFO: (5494): The update of the National Vulnerability Database feed finished successfully.
Once the feeds are downloaded, the scan starts automatically. It is finished when the following log appears:
2020/04/16 00:21:52 wazuh-modulesd:vulnerability-detector: INFO: (5453): Vulnerability scanning finished.
When the scan is completed, we are ready to check the detected vulnerabilities in the WUI.
Looking into the endpoints inventory data
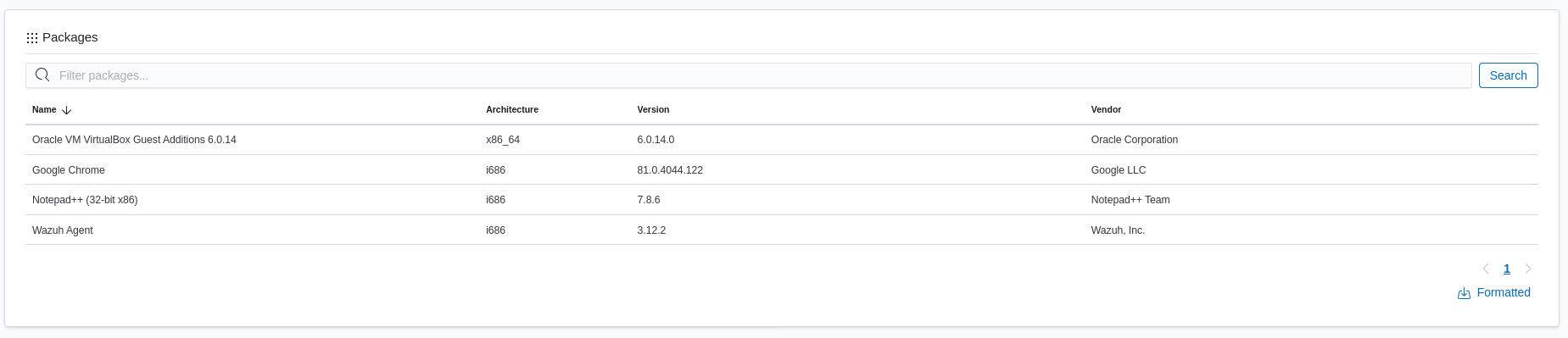
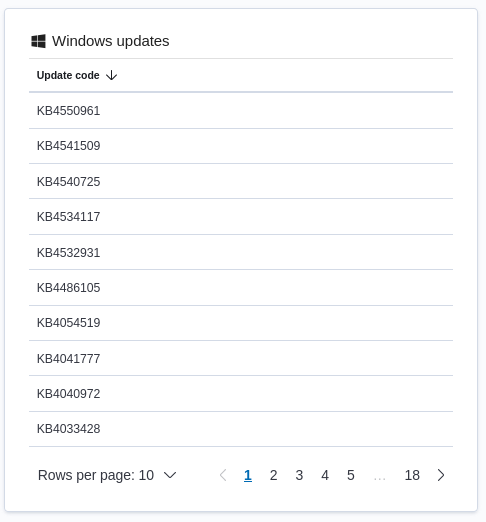
Using the Wazuh user interface, you can see all applications, network configuration, open ports, and processes running on your monitored systems. For that, click on Agents in the top bar, select the Windows agent from the list, and click on Inventory data.Processes, installed programs, installed Windows updates, network settings, ports, and interfaces can be checked in this section.
Exploring the outstanding vulnerabilities
Once in the WUI, we can use the following section: Vulnerabilities. For that, click on Agents in the top bar, select the Windows agent from the list, click on Vulnerabilities and you will see the Windows agent vulnerability dashboard.
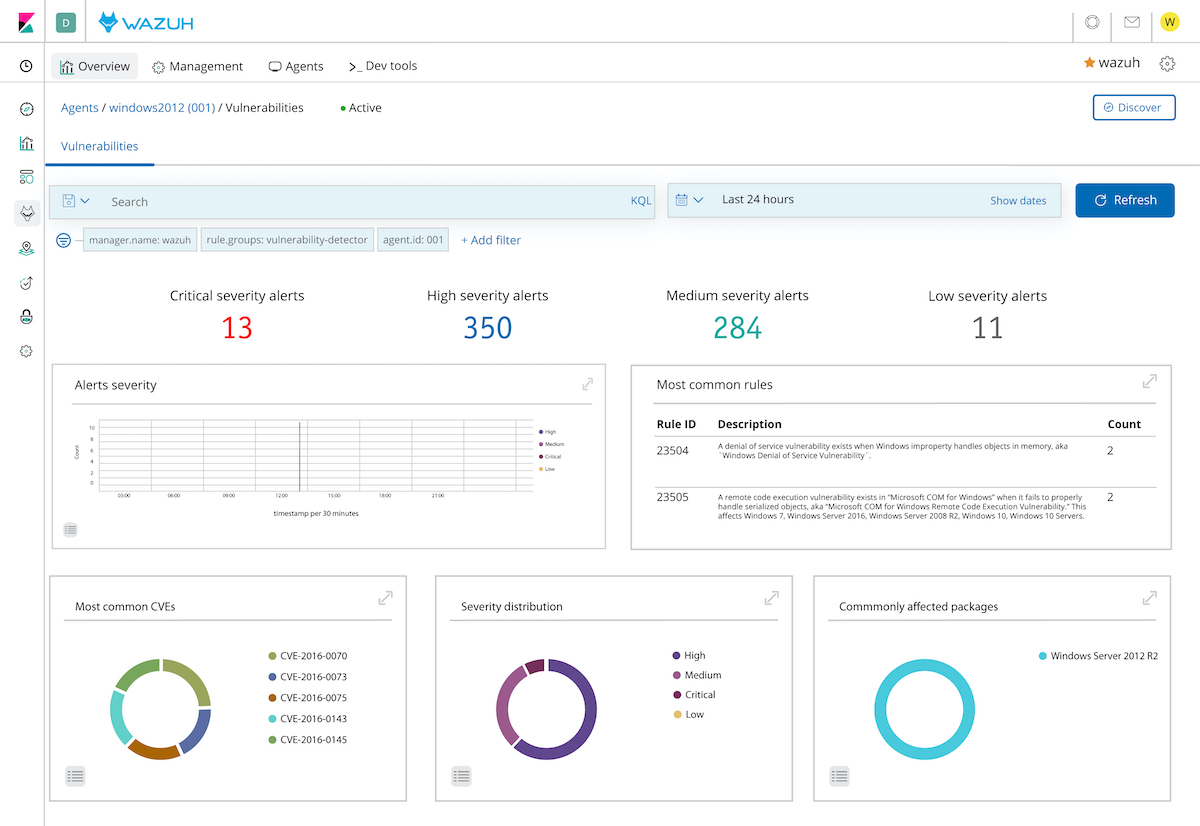
Vulnerability alerts can be filtered by severity, let’s filter by the critical ones. Click on Add filter, select Field data.vulnerability.severity. Operator is and Value Critical.
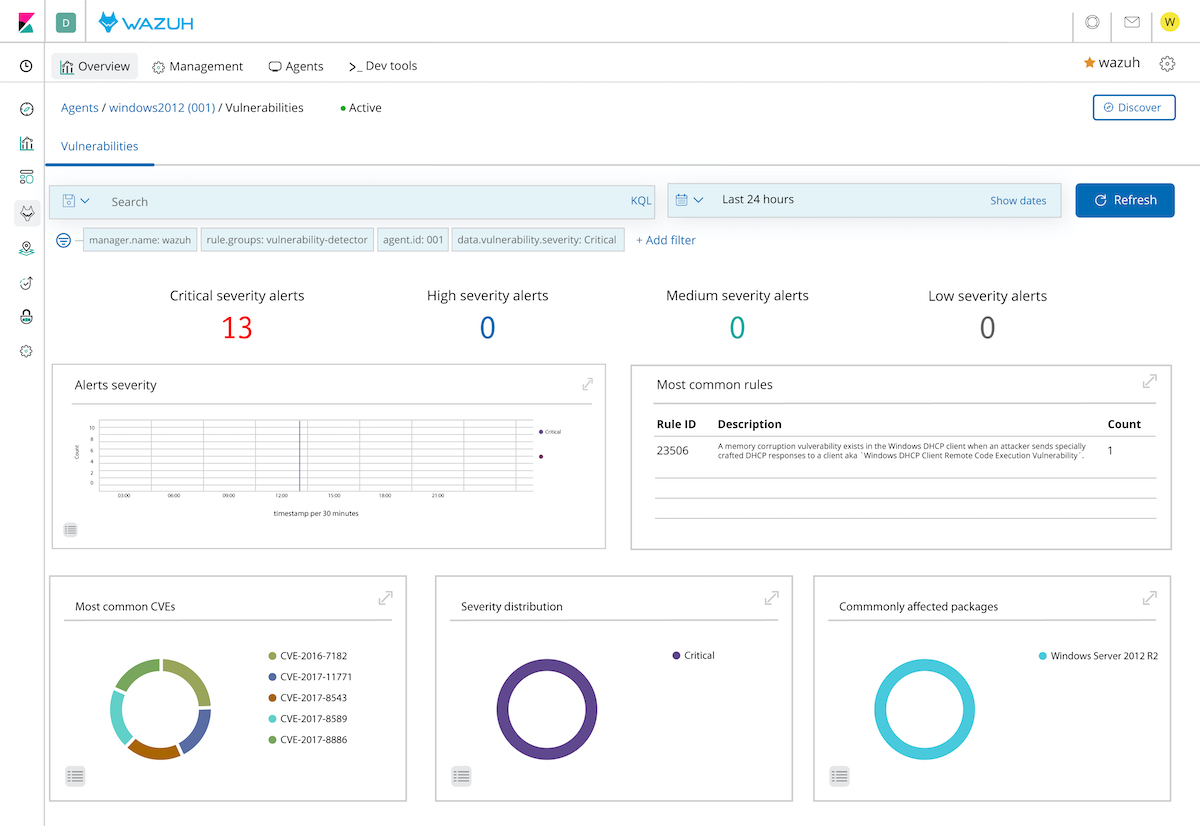
The Wazuh User Interface will show you all the vulnerabilities detected. In this example, we want to analyze one of the critical ones: CVE-2016-7182. You should be able to see it by clicking on Discover button. Then, click on Add filter, and select Field data.vulnerability.cve. Operator is and Value CVE-2016-7182. This is the vulnerability alert content:
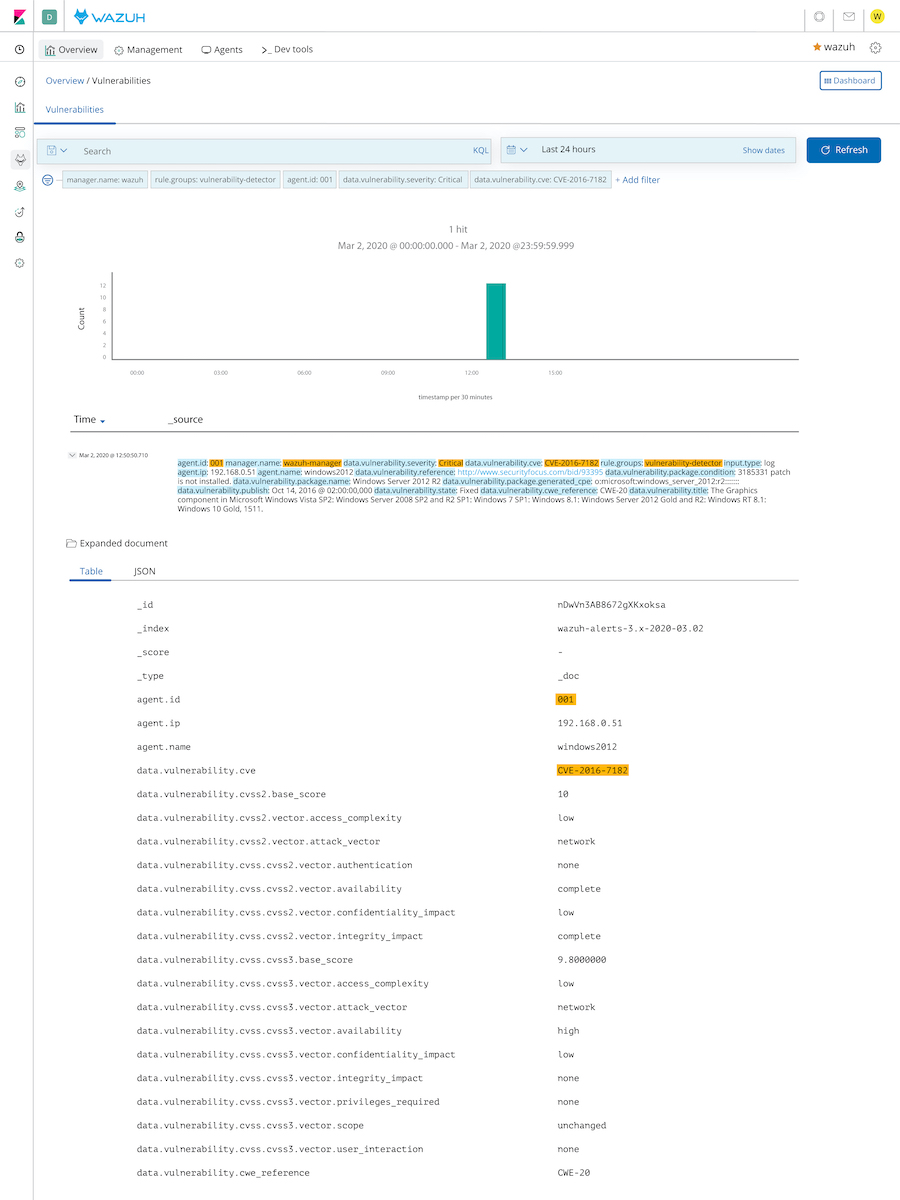
The vulnerability: CVE-2016-7182 describes how the Graphics component of a set of Microsoft products allows attackers to execute arbitrary code via a crafted True Type font. This vulnerability is cataloged as Critical and the field data.vulnerability.package.condition describes why this vulnerability is not fixed: 3185331 patch is not installed. Once the user downloads and installs the patch or a more recent one containing it, the operating system will be patched for the detected vulnerability.
Summarizing, the users can scan their Windows endpoints searching for vulnerabilities. If this vulnerability has immediate remediation, the Wazuh alert will indicate which patch fixes the vulnerability.
Start the vulnerability detection today with Wazuh. Do you have any questions? Let us know. Join our Slack #community channel. Our team and other contributors will help you.
