We are happy to announce that Wazuh 4.2.0 is released. After working tirelessly to create the best open source security platform during the last years, Wazuh is now better than ever. Below you can explore some of the new additions and improvements of this brand new release!
New features in Wazuh 4.2.0
Wazuh 4.2.0 includes many new additions such as a significant improvement in the Active Response (AR) capacities, enhanced insight into the Common Vulnerabilities and Exposures (CVE) that affect systems, and a new ruleset test tool in the Wazuh user interface. Below you will find more information about each of these new features.
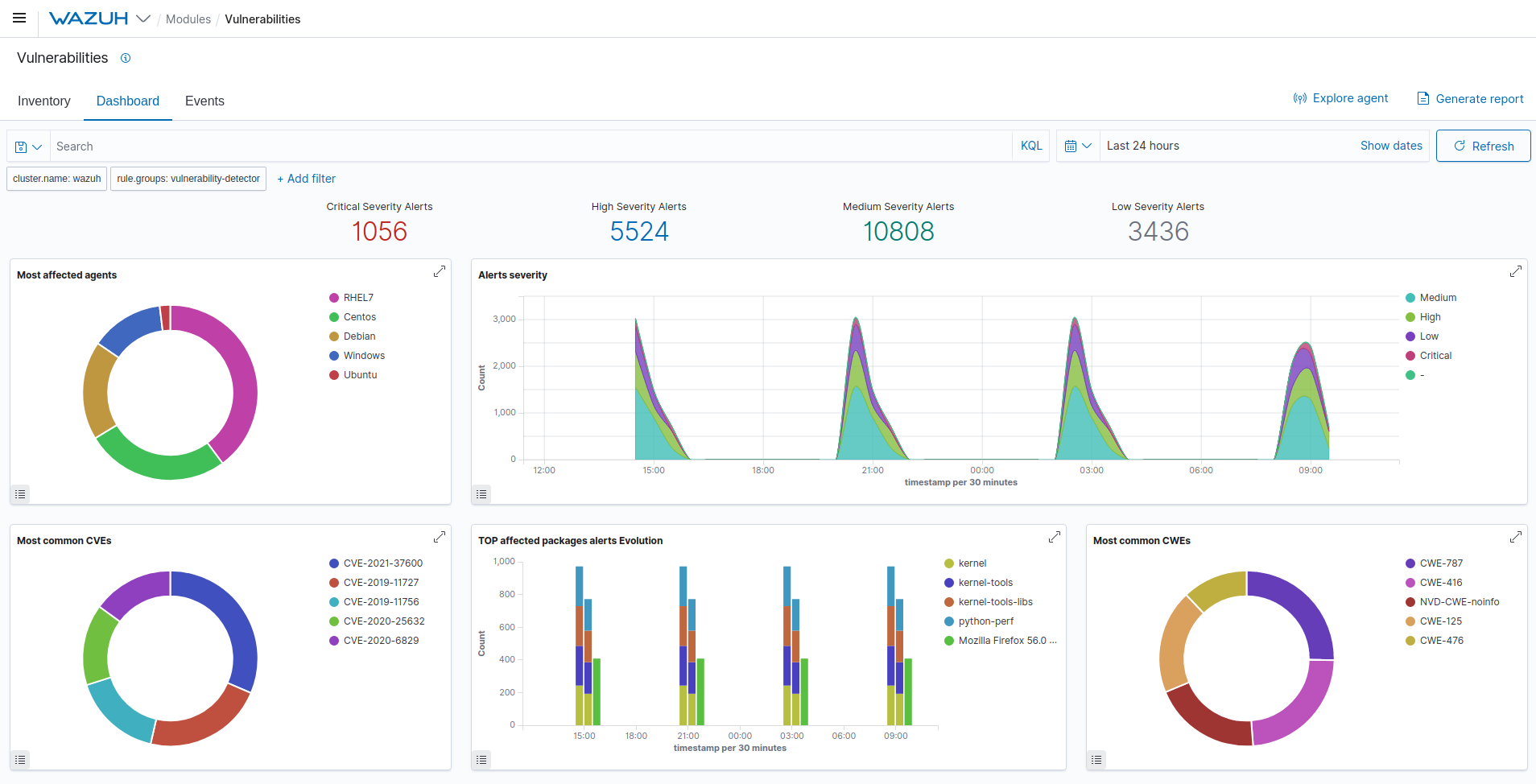
Wazuh 4.2.0 provides you with enhanced insight into the CVEs that affect systems and applications.
Improved Active Response capacities
The changes in the AR capacities include removing the limitation of fields that can be received to execute a command related to the AR. This new feature is backward-compatible with previous versions of the agents.
As part of a new Core feature, AR protocol changed to receive notifications in JSON format that include the full alert. So, the whole alert is sent to execute commands related to an AR.
Wazuh 4.2.0 now transmits information to the AR executables via standard input (stdin) instead of in-line arguments. As part of the agent upgrade process, previous versions of the AR scripts present in the active-response/bin directories were replaced. In addition, the new 4.2 Wazuh server continues sending in-line arguments to Wazuh agents version 4.1.5 and earlier.
Wazuh 4.2.0 Common Vulnerabilities and Exposures (CVE) enhanced insight
Another Wazuh 4.2.0 significant new feature is the enhanced insight into the CVEs detected by agents. Different development teams within Wazuh were working together to reach this achievement.
Wazuh now generates CVEs inventory reports that provide users insight into the vulnerabilities that are monitored by agents. This visibility improvement allows users to visualize information on their interface. In addition, users can analyze vulnerabilities recognized by agents and evaluate this information to perform corrective actions.
Now Wazuh has a new endpoint to get CVEs data detected by agents. Through this endpoint, users can query the vulnerability data of any agent and get enhanced insight into the CVEs. In addition, this new feature gives users easy access to information such as package name, version, architecture, and the CVE ID that affects each application.
With this new feature, Wazuh now supplies users with enhanced insight into the CVEs monitored by agents. Thanks to the newly added Inventory tab in the Vulnerabilities module, users can now visualize all the information related to each specific vulnerability entry detailed in the Inventory section.
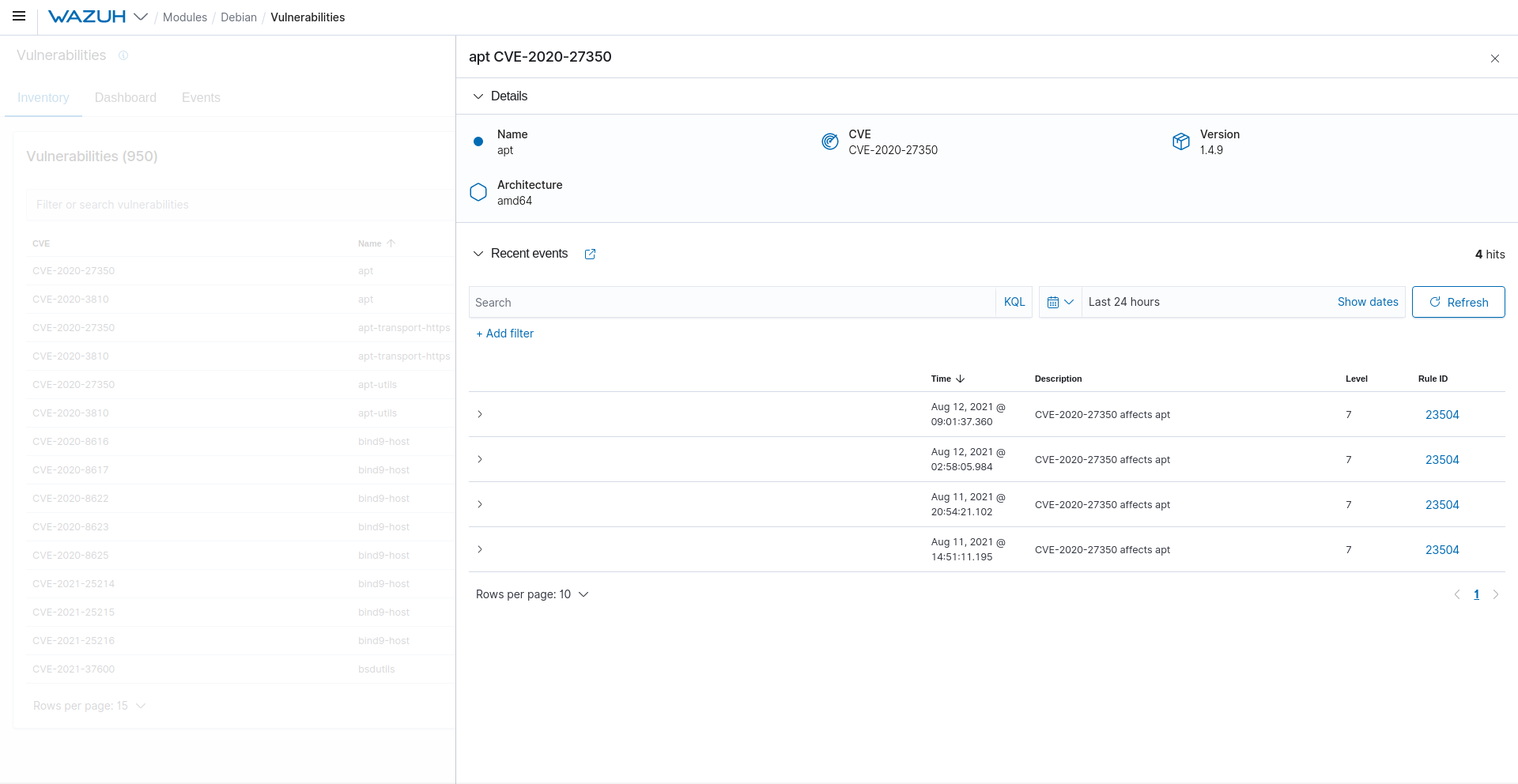
Wazuh 4.2.0 generates CVEs inventory reports that provide insight into the vulnerabilities monitored by agents.
New ruleset test tool for the Wazuh user interface
Wazuh 4.2.0 presents a new ruleset test tool that can be accessed through the Wazuh user interface. Users can now visualize how the ruleset responds to specific log messages by testing sample logs directly on the Wazuh user interface.
This new feature will improve the users’ experience by integrating an input box for reading sample logs and an output box to visualize the test results. Users can also keep the ruleset test window open to edit or create threat detection rules while on the web interface.
Wazuh 4.2.0 provides users with the ability to test log messages as they write rules and decoders in the interface. Users now have more visualization control related to the ruleset test through the web interface.
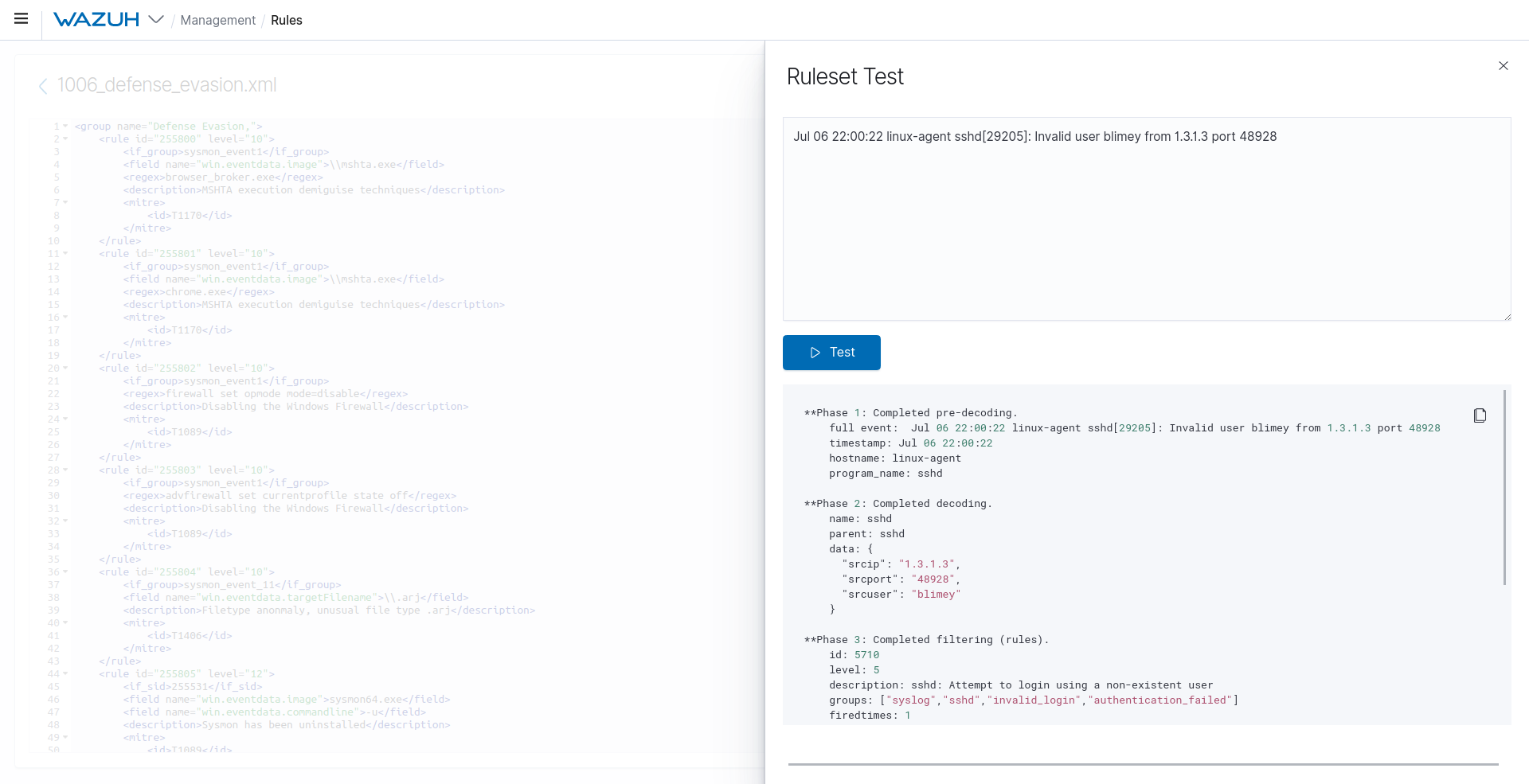
Wazuh 4.2.0 presents a new ruleset test tool that users can access through the Wazuh user interface.
More fixes and enhancements in version 4.2.0
Wazuh 4.2.0 includes many enhancements and fixes from previous releases, such as the following:
- Wazuh adds Logcollector support for bookmarks, allowing users to continue reading a log file from the last read line where the agent stopped, improving efficiency and productivity.
- Improvements in cluster node integrity calculation make the process more efficient. Now, it calculates the MD5 of only the files that were modified since the last integrity check.
- The synchronization workflow of agent information between cluster nodes is optimized, and now the synchronization is performed in a single task for each agent.
- Quoting in commands to group arguments in the command module and SCA checks are allowed. Before this enhancement, the system parsed quoted substrings into the same argument, but double quotes were kept. Now, scapes and double-quotes are allowed so that users can handle arguments in command calls.
- An issue with RBAC with agent group permissions is fixed. Now, when authorized agents are specified by their group instead of their IDs, users can successfully access the Security configuration assessment module, the Integrity monitoring module, and the Configuration window on the Agents page.
- Wazuh new Stability enhancements provide stability to several features of the solution, including Analysisd, File Integrity Monitoring, Remoted, and Vulnerability Detector. These changes improve user experience throughout the product.
- Remoted now supports listening to TCP and UDP ports simultaneously. This new support of both protocols provides several enhanced features related to manager active check, agent connection and logging, active response, API requests, and JSON formatting.
More information and links about Wazuh 4.2.0
This release includes many more fixes and performance improvements, and you can find more information about it at the following links:
If you have any questions about Wazuh 4.2.0, don’t hesitate to check out our documentation to learn more about it. You can also join our Slack and mailing list, where our team and other users will help you.
