Hi everyone,
we are happy to announce that Wazuh v2.0 has just been released!
As many of you already know, it includes the integration of our forked version of OSSEC with OpenSCAP and Elastic Stack 5. In addition, we improved some core capabilities for infrastructure security monitoring and developed a new WUI in the form of a Kibana app.
Here are the highlights of the new release of Wazuh v2.0:
Log analysis and management new features of Wazuh v2.0
- Modified OSSEC analysis engine to support dynamic data analysis, being able to extract as many fields from a raw log as needed. This can also be used to create rules with dynamic fields and titles (Examples: New Auditd or OpenSCAP decoders and rules).
- Modified analysis engine output to dynamically (as picked by decoders) print fields in JSON output, both for raw logs and alerts.
- Created new decoders and rules (more than 500 new ones!).
- Created Auditd rules to keep track of user actions and system calls (e.g. keep track of users running commands as root).
- Integrated with Amazon AWS API, being now able to alert on Cloudtrail data (e.g. “new amazon user created” or “security group changed”). There are decoders for VPC, IAM and EC2 services.
- Created Logstash template for integration with Elasticsearch, adding Geo-location metadata to the alerts.
File integrity monitoring new features
- Keep track of user or process modifying a file (via Auditd).
- Keep track of file changes (recording diffs) both on Windows and Linux systems.
- Improved realtime monitoring features, decreasing time to detection of file changes.
- FIM alerts JSON output enriched.
- Keep track of file inodes.
- FIM SQLite databases implemented per agent. They are used by the RESTful API component to run complex searches.
Policy monitoring – Integration with OpenSCAP
We realized that OSSEC’s ability to monitor system configurations is limited. This is why we decided to incorporate OpenSCAP as an agent component. It allows users to check that the systems are configured according to the company policy or well known standards like CIS (Center of Internet Security) hardening guides.
This means that, via OpenSCAP, we now support OVAL (Open Vulnerability Assessment Language) checks. We have put together default templates for well-known platforms (RedHat, Fedora, CentOS, Ubuntu, and Debian) using OVAL checks provided by CIS repository.
Now the agent is able to run checks periodically and report back to the manager, where alerts are generated, using new decoders and rules (developed using the new dynamic fields feature). Alerts include a description, a check rationale, references, and CCE or CVE identifiers.
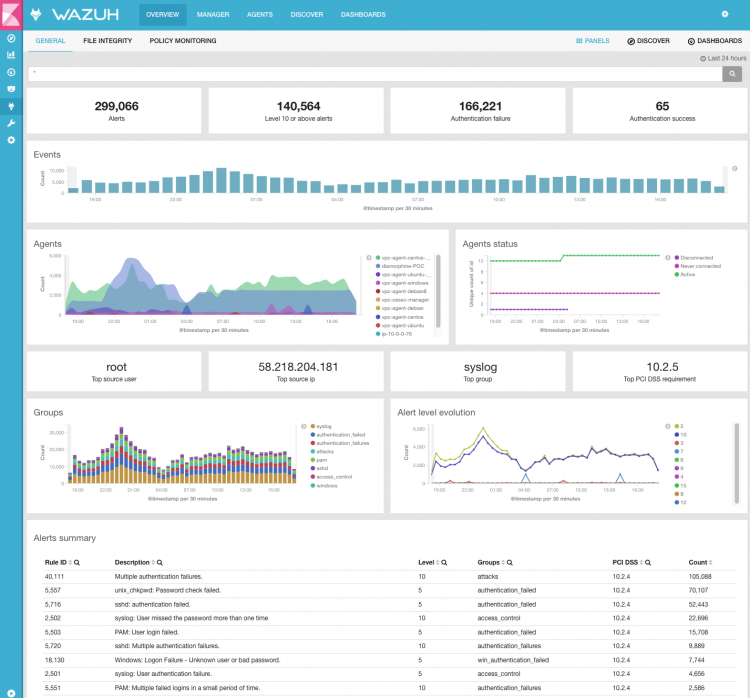
PCI DSS compliance support
We natively support PCI DSS by mapping alerts with compliance controls. This includes not only the alerts triggered by the log analysis engine but also the ones that come from OpenSCAP scans (OVAL checks). We also provide compliance dashboards in the web user interface.
RESTful API new features
- Monitor manager and agents configuration and status.
- Query FIM and Policy monitoring databases.
- Get information about monitored systems (OS, hostname, IP address, Kernel, agent id, agent key).
- Browse through rules and decoders.
- Register new agents.
- Navigate through OSSEC logs.
New Kibana App – Web user interface on Wazuh v2.0
We support integration with Elastic 5, and have built a WUI in the form of a Kibana APP for configuration and status monitoring.
We would also like to thank our developers, contributors, and users. We are looking forward to your feedback, so please don’t hesitate to post on our mailing list if you have any questions about Wazuh v2.0. You can also join our #community Slack channel.
