Hi everyone,
The team is pleased to announce the release of Wazuh v3.11. This new version comes with lots of additions and improvements, so here are some of the release highlights:
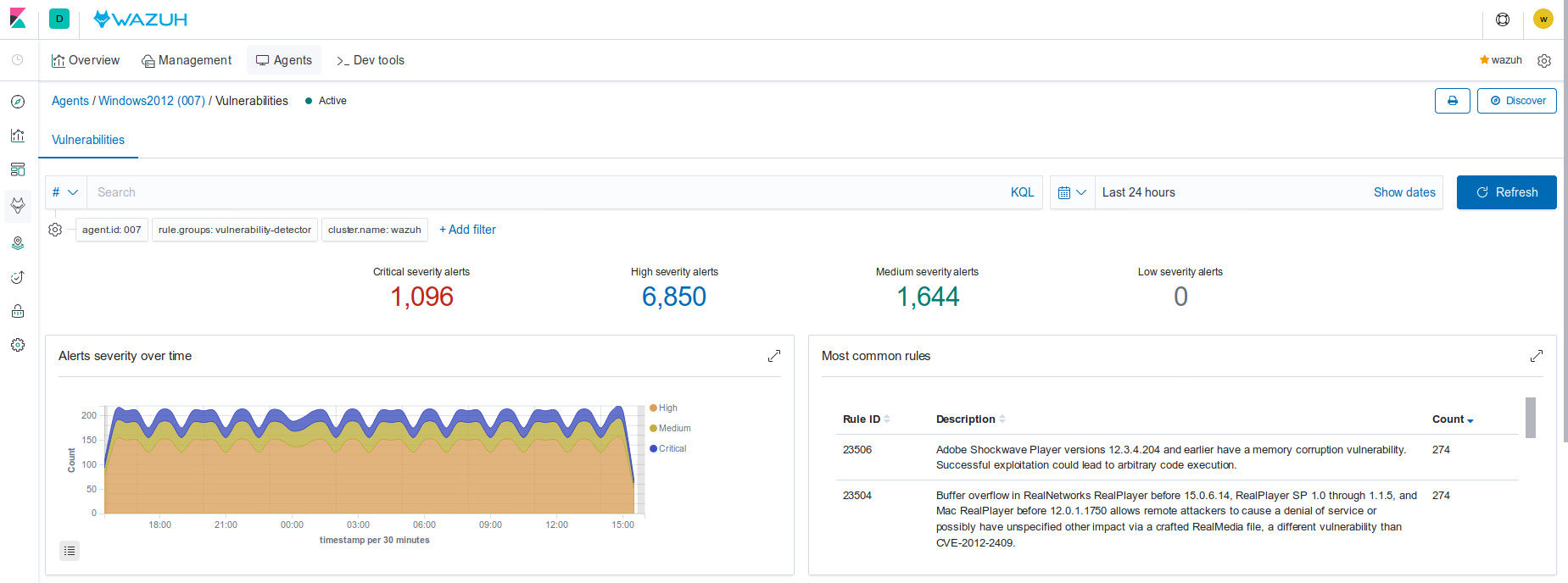
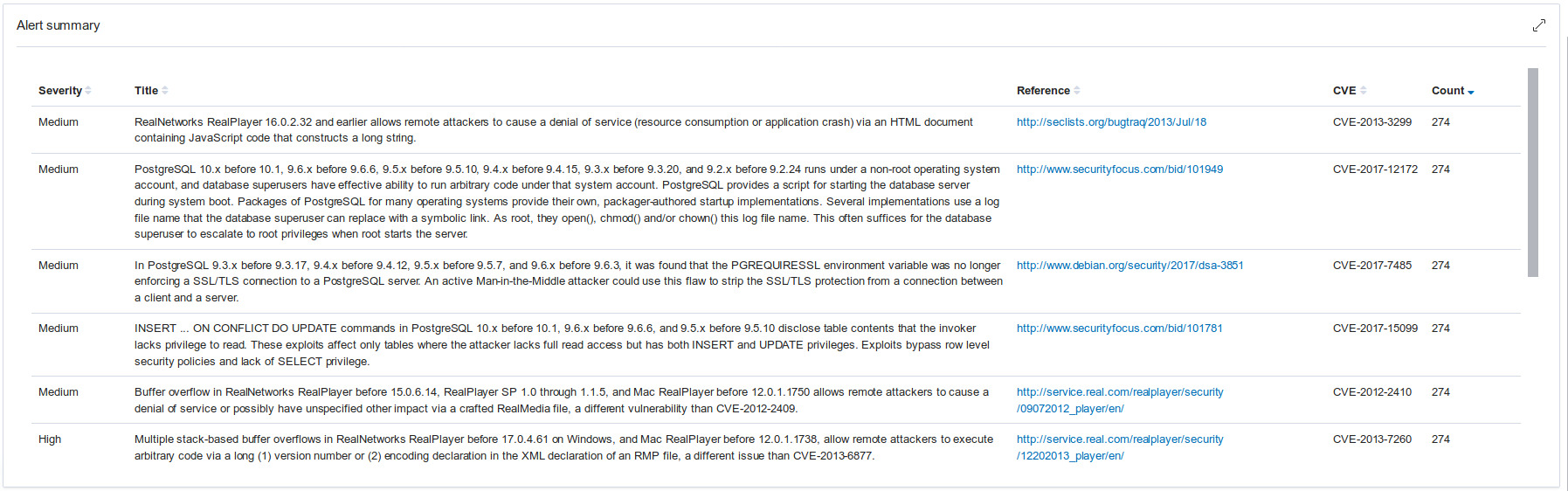
Vulnerability Detection module is now able to detect Windows system and application vulnerabilities
- The package scan collects the installed applications and evaluates them against a package vulnerability database.
- OS vulnerabilities are evaluated by collecting the Windows hotfixes installed on agents and using another database to retrieve potential system vulnerabilities.
- Both previous databases are periodically updated through NVD (National Vulnerability Database) to ensure the last reported vulnerabilities are taken care of.
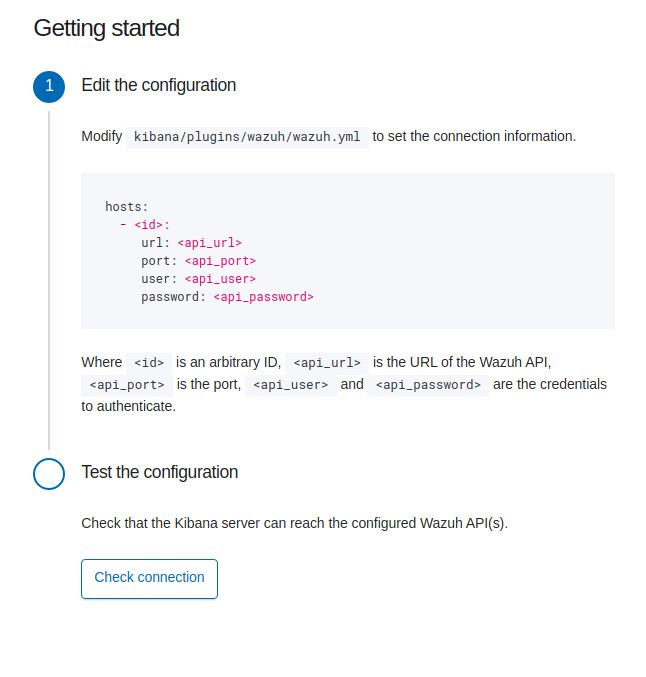
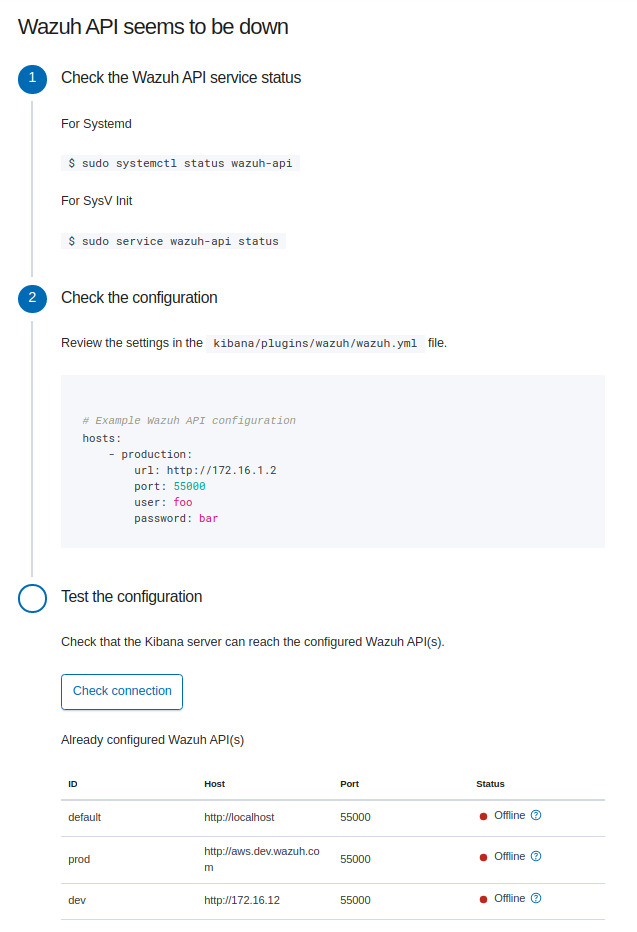
Improved API credentials management
In the previous Wazuh versions, the API credentials were stored in an Elasticsearch index. The credentials are now managed through a YAML configuration file. For a quick and easy adaptation, in empty or non-reachable API’s scenario, the further user guides are shown:
Upload Ruleset and CDB lists faster and easier through drag & drop interface
Rules/decoders files and CDB lists can now be uploaded through a drag and drop interface.

Enhanced inventory macOS support
The System details collection module now supports processes and ports inventory on macOS X systems.
Agents reset API request
The new API call provides users with an easy tool to quickly reset all agents belonging to a group.
# curl -u foo:bar -k -X PUT "https://localhost:55000/agents/restart?pretty";
{
"error": 0,
"data": "Restarting all agents"
}
Further information and documentation can be found in the following URLs:
- Release notes
- Wazuh core changelog
- Wazuh API changelog
- Wazuh Ruleset changelog
- Kibana app changelog
- Splunk app changelog
- Project documentation
- Packages list
We would also like to thank our developers, contributors, and users. We are looking forward to your feedback, so please don’t hesitate to post on our mailing list if you have any questions about Wazuh v3.11. You can also join our #community Slack channel.
