Daolpu is a malware that steals sensitive information from infected Windows endpoints. This malware was first seen in July 2024, after CrowdStrike distributed a legitimate update to its Falcon product that caused widespread disruptions to Windows systems running this product. Due to this update, roughly 8.5 million Windows systems crashed and were unable to reboot normally. Threat actors exploited this opportunity to install Daolpu on affected Windows systems by providing a fake CrowdStrike recovery manual.
Daolpu infostealer is delivered through phishing emails that contain a Microsoft Word document attachment with malicious macros. This malware collects login credentials, browser history, and cookies stored in Google Chrome, Microsoft Edge, FireFox and other web browsers. The malware sends stolen data to a remote command and control (C2) server through HTTP POST requests.
This blog post demonstrates how to use Wazuh to detect and respond to Daolpu malware on an infected Windows endpoint.
Behavioural analysis of Daolpu infostealer
- Daolpu malware kills the Chrome process by executing the following command:
taskkill /F /IM chrome.exe
The malware then collects login data and cookies stored in Google Chrome, Microsoft Edge, Firefox and other Chromium browsers.
- Daolpu saves the stolen data in a file
%TMP%\result.txtand sends this file to a remote C2 server controlled by threat actors. - The malware finally deletes the file
result.txtto evade detection.
Infrastructure
We use the following infrastructure to demonstrate the detection of Daolpu malware with Wazuh:
- A pre-built, ready-to-use Wazuh OVA 4.8.2: Follow this guide to download the virtual machine (VM). This VM hosts the Wazuh central components (Wazuh server, Wazuh indexer, and Wazuh dashboard)
- A Windows 10 endpoint: The victim endpoint has Wazuh agent 4.8.2 installed and enrolled to the Wazuh server. Refer to the following guide to install the Wazuh agent.
Detection with Wazuh
In this blog post, we use the following techniques to detect the malicious activities of Daolpu on a Windows 10 endpoint.
- Wazuh detection rules: To detect malicious activities performed by Daolpu malware.
- YARA integration with Wazuh: To detect and remove Daolpu malware.
Wazuh detection rules
We use Sysmon to monitor several system events and create rules on the Wazuh server to detect the malicious activities performed by Daolpu malware.
Victim endpoint
In this section, we install Sysmon on the Windows endpoint and configure the Wazuh agent to collect Sysmon logs.
Perform the steps below to detect the malicious activities performed by Daolpu malware on the Windows endpoint.
1. Download Sysmon and the configuration file sysmonconfig.xml.
2. Edit the file sysmonconfig.xml and include the below configuration within the <EventFiltering> block. This configuration records the activity when Daolpu deletes a file it uses to store stolen data:
<!-- This configuration records the activity when Daolpu deletes a file it uses to store stolen data --> <RuleGroup groupRelation="or"> <FileDeleteDetected onmatch="include"> <TargetFilename condition="contains">\Temp\result.txt</TargetFilename> </FileDeleteDetected> </RuleGroup>
3. Launch PowerShell with administrative privilege, and install Sysmon as follows:
> .\Sysmon64.exe -accepteula -i .\sysmonconfig.xml
4. Edit the Wazuh agent file C:\Program Files (x86)\ossec-agent\ossec.conf and include the following settings within the <ossec_config> block:
<!-- Configure Wazuh agent to receive events from Sysmon --> <localfile> <location>Microsoft-Windows-Sysmon/Operational</location> <log_format>eventchannel</log_format> </localfile>
5. Restart the Wazuh agent for the changes to take effect:
> Restart-Service -Name wazuh
Wazuh server
Perform the following steps to configure detection rules on the Wazuh server.
1. Create a new file /var/ossec/etc/rules/daolpu_malware.xml on the Wazuh server:
# touch /var/ossec/etc/rules/daolpu_malware.xml
2. Edit the file /var/ossec/etc/rules/daolpu_malware.xml and include the following detection rules for Daolpu malware:
<group name="windows,sysmon,daolpu_detection_rule,">
<!-- Daolpu malware attempts to kill the Chrome process -->
<rule id="100060" level="10">
<if_sid>92032</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)\\taskkill.exe</field>
<match type="pcre2">(?i)cmd.exe /c taskkill /F /IM chrome.exe</match>
<description>Possible Daolpu malware detected. Malware has attempted to kill the Chrome process.</description>
<mitre>
<id>T1489</id>
</mitre>
</rule>
<!-- Daolpu creates a file it uses to store sensitive data -->
<rule id="100061" level="12">
<if_sid>61613</if_sid>
<field name="win.system.eventID">11</field>
<field name="win.eventdata.image" type="pcre2">(?i)\\.+(exe|dll|bat|msi)</field>
<field name="win.eventdata.targetFilename" type="pcre2">(?i)\\Windows\\Temp\\result.txt</field>
<description>Possible Daolpu malware detected. Malware creates a file it uses to store sensitive data.</description>
<mitre>
<id>T1555</id>
</mitre>
</rule>
<!-- Daolpu deletes a file it uses to store sensitive data -->
<rule id="100062" level="10">
<if_sid>61654</if_sid>
<field name="win.system.eventID">26</field>
<field name="win.eventdata.image" type="pcre2">(?i)\\.+(exe|dll|bat|msi)</field>
<field name="win.eventdata.targetFilename" type="pcre2">(?i)\\Windows\\Temp\\result.txt</field>
<description>Possible Daolpu malware detected. Malware deletes the file it uses to store sensitive data.</description>
<mitre>
<id>T1070.004</id>
</mitre>
</rule>
</group>
Where:
- Rule ID
100060is triggered when the malware kills the Chrome process. - Rule ID
100061is triggered when the malware creates a file to store sensitive data. - Rule ID
100062is triggered when the malware deletes the file it uses to store sensitive data.
3. Restart the Wazuh manager for the changes to take effect:
sudo systemctl restart wazuh-manager
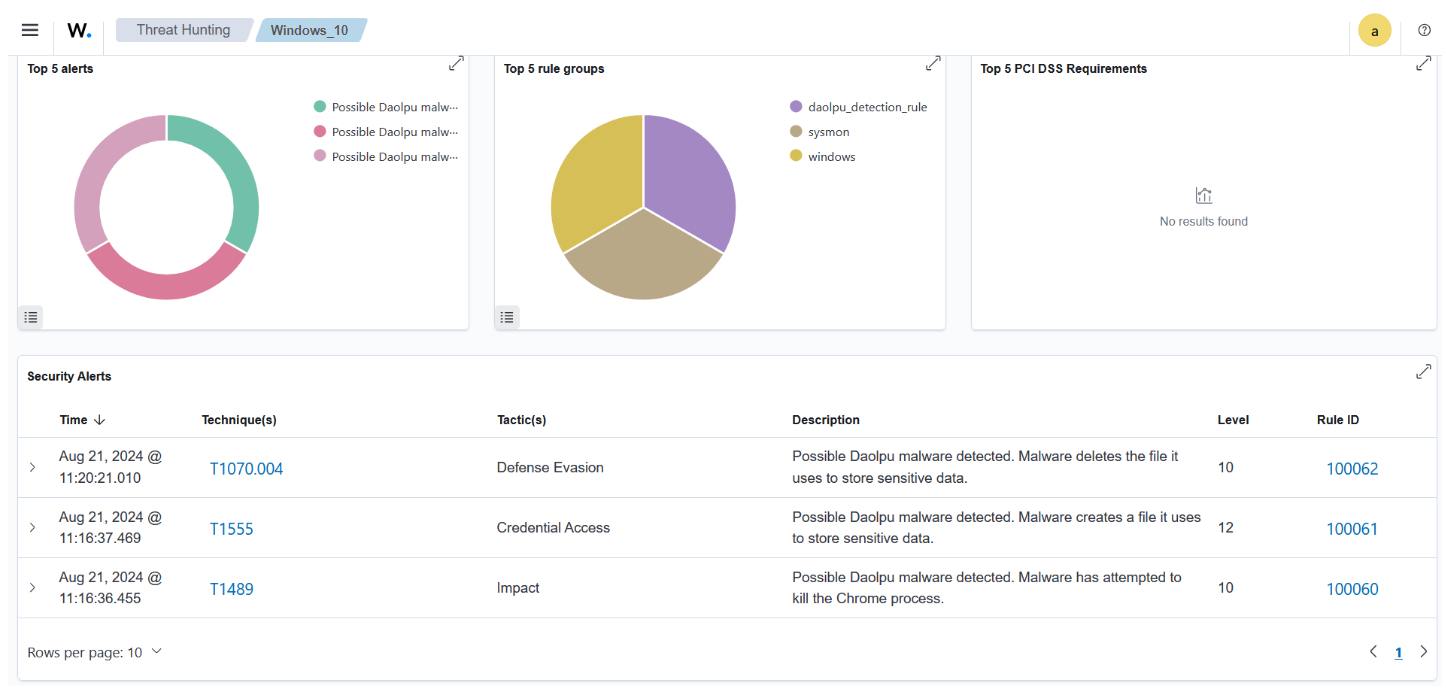
Visualizing alerts on the Wazuh dashboard
The alerts below are generated on the Wazuh dashboard when the Daolpu malware is run on the victim endpoint. Perform the following steps to view the alerts on the Wazuh dashboard.
1. Navigate to Threat intelligence > Threat Hunting.
2. Click + Add filter. Then, filter for rule.id in the Field field.
3. Filter for is one of in the Operator field.
4. Filter for 100060, 100061, and 100062 in the Values field.
5. Click Save.
YARA integration with Wazuh
YARA is a versatile open source and multi-platform tool that identifies and classifies malware samples based on their textual or binary patterns. In this blog post, we use the Wazuh active response module to automatically execute a YARA scan on files added or modified in the Downloads folder.
Victim endpoint
To download and install YARA, we require the following packages installed on the victim endpoint:
- Python v 3.8.7 or later (with pip pre-installed).
- Microsoft Visual C++ 2015 Redistributable.
After installing the above packages, perform the steps below to download the YARA executable:
1. Launch PowerShell with administrative privilege and download YARA:
Invoke-WebRequest -Uri https://github.com/VirusTotal/yara/releases/download/v4.5.1/yara-master-2298-win64.zip -OutFile v4.5.1-2298-win64.zip
2. Extract the YARA executable:
Expand-Archive v4.5.1-2298-win64.zip
3. Create a folder called C:\Program Files (x86)\ossec-agent\active-response\bin\yara\ and copy the YARA binary into it:
mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\' cp .\v4.5.1-2298-win64\yara64.exe 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\'
Perform the steps below to download YARA rules:
1. Using the same PowerShell terminal launched earlier, install valhallaAPI using the pip utility:
pip install valhallaAPI
2. Create the file download_yara_rules.py and copy the following script into it:
from valhallaAPI.valhalla import ValhallaAPI
v = ValhallaAPI(api_key="1111111111111111111111111111111111111111111111111111111111111111")
response = v.get_rules_text()
with open('yara_rules.yar', 'w') as fh:
fh.write(response)
3. Download YARA rules and copy them to the C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\ folder:
python download_yara_rules.py mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\' cp yara_rules.yar 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\'
4. Edit the file C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yar and add the following YARA rule to detect Daolpu malware:
rule Daolpu_infostealer
{
meta:
Author = "Benjamin Nworah"
Description = "Detect Daolpu malware"
Date = "16-08-2024"
Hash1 = "3a9323a939fbecbc6d0ceb5c1e1f3ebde91e9f186b46fdf3ba1aee03d1d41cd8"
Hash2 = "4ad9845e691dd415420e0c253ba452772495c0b971f48294b54631e79a22644a"
strings:
$a1 = "D:\c++\Mal_Cookie_x64\x64\Release\mscorsvc.pdb"
$a2 = "C:\Windows\Temp\result.txt"
condition:
all of ($a*)
}
5. Edit the Wazuh agent file C:\Program Files (x86)\ossec-agent\ossec.conf and add the below configuration within the <syscheck> block to monitor the Downloads folders of all users in real-time:
<directories realtime="yes">C:\Users\*\Downloads</directories>
Note: In this blog post, the Downloads folders of all users are monitored. However, you can configure other folders you intend to monitor.
6. Create a batch file yara.bat in the C:\Program Files (x86)\ossec-agent\active-response\bin\ folder. The Wazuh active response module uses this file to perform YARA scans for malware detection and removal:
:: This script deletes Daolpu malware and other malicious files matched by the YARA Rules @echo off setlocal enableDelayedExpansion reg Query "HKLM\Hardware\Description\System\CentralProcessorRestart-Service -Name wazuh" | find /i "x86" > NUL && SET OS=32BIT || SET OS=64BIT if %OS%==32BIT ( SET log_file_path="%programfiles%\ossec-agent\active-response\active-responses.log" ) if %OS%==64BIT ( SET log_file_path="%programfiles(x86)%\ossec-agent\active-response\active-responses.log" ) set input= for /f "delims=" %%a in ('PowerShell -command "$logInput = Read-Host; Write-Output $logInput"') do ( set input=%%a ) set json_file_path="C:\Program Files (x86)\ossec-agent\active-response\stdin.txt" set syscheck_file_path= echo %input% > %json_file_path% FOR /F "tokens=* USEBACKQ" %%F IN (`Powershell -Nop -C "(Get-Content 'C:\Program Files (x86)\ossec-agent\active-response\stdin.txt'|ConvertFrom-Json).parameters.alert.syscheck.path"`) DO ( SET syscheck_file_path=%%F ) set yara_exe_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\yara64.exe" set yara_rules_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yar" echo %syscheck_file_path% >> %log_file_path% for /f "delims=" %%a in ('powershell -command "& \"%yara_exe_path%\" \"%yara_rules_path%\" \"%syscheck_file_path%\""') do ( echo wazuh-yara: INFO - Scan result: %%a >> %log_file_path% :: Deleting the scanned file. del /f "%syscheck_file_path%" echo wazuh-yara: INFO - Successfully deleted: %%a >> %log_file_path% ) exit /b
7. Restart the Wazuh agent using PowerShell for the changes to take effect:
<!-- The decoders parse logs from the YARA scans -->
<decoder name="yara_decoder">
<prematch>wazuh-yara:</prematch>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Scan result: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Successfully deleted: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
Wazuh server
Perform the following steps to configure custom decoders, rules, and active response on the Wazuh server.
1. Edit the file /var/ossec/etc/decoders/local_decoder.xml on the Wazuh server and include the following decoders:
<!-- File added to the Downloads folder -->
<group name= "syscheck,">
<rule id="100028" level="7">
<if_sid>550</if_sid>
<field name="file" type="pcre2">(?i)C:\Users.+Downloads</field>
<description>File modified in the Downloads folder.</description>
</rule>
<!-- File modified in the Downloads folder -->
<rule id="100029" level="7">
<if_sid>554</if_sid>
<field name="file" type="pcre2">(?i)C:\Users.+Downloads</field>
<description>File added to the Downloads folder.</description>
</rule>
</group>
<!-- Rule for the decoder (yara_decoder) -->
<group name="yara,">
<rule id="100063" level="0">
<decoded_as>yara_decoder</decoded_as>
<description>Yara grouping rule</description>
</rule>
<!-- YARA scan detects a positive match -->
<rule id="100064" level="12">
<if_sid>100063</if_sid>
<match type="pcre2">wazuh-yara: INFO - Scan result: </match>
<description>File "$(yara_scanned_file)" is a positive match. Yara rule: $(yara_rule)</description>
</rule>
<rule id="100065" level="12">
<if_sid>100063</if_sid>
<match type="pcre2">wazuh-yara: INFO - Successfully deleted: </match>
<description>Successfully removed "$(yara_scanned_file)". YARA rule: $(yara_rule)</description>
</rule>
</group>
2. Edit the file /var/ossec/etc/rules/local_rules.xml on the Wazuh server and include the following rules:
<!-- The YARA batch script is executed when a file is added or modified in the Downloads folder monitored by Wazuh --> <command> <name>yara</name> <executable>yara.bat</executable> <timeout_allowed>no</timeout_allowed> </command> <active-response> <command>yara</command> <location>local</location> <rules_id>100028,100029</rules_id> </active-response>
3. Add the following configuration to the Wazuh server file /var/ossec/etc/ossec.conf within the <ossec_config> block:
sudo systemctl restart wazuh-manager
4. Restart the Wazuh manager for the changes to take effect:
sudo systemctl restart wazuh-manager
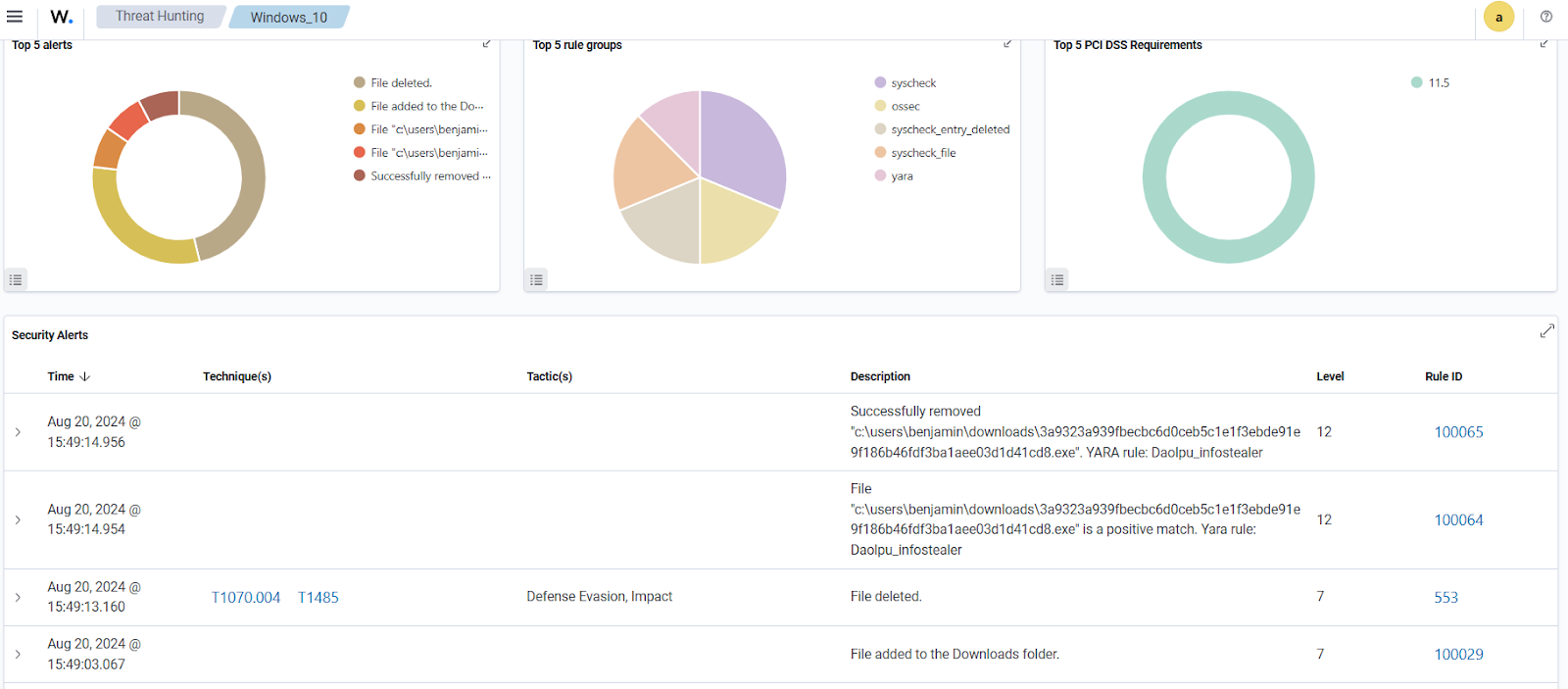
Visualizing alerts on the Wazuh dashboard
The Wazuh dashboard generates alerts when Daolpu malware is downloaded to the Downloads folder of the victim endpoint. Perform the following steps to view the alerts on the Wazuh dashboard.
1. Navigate to Threat intelligence > Threat Hunting.
2. Click + Add filter. Then filter for rule.id in the Field field.
3. Filter for is one of in the Operator field.
4. Filter for 553, 100029, 100064, and 100065 in the Values field.
5. Click Save.
Conclusion
This blog post used Sysmon integration with Wazuh to detect the behavior of Daolpu malware. We also used YARA integration with Wazuh to detect and remove this malware once it was downloaded to an endpoint.
Wazuh is a free and open source enterprise-ready security platform for uncovering security threats, incident response, and compliance. Wazuh integrates with third-party platforms. We also have a growing community where users are supported. To learn more about Wazuh, please check out our documentation and blog posts.
References