Pandora Ransomware gained notoriety in March 2022 when DENSO, a well-known giant in the automotive industry was compromised. After this, several malware researchers analyzed Pandora samples and agree that it is a variant of Rook ransomware, a well-known malware that first appeared on VirusTotal in November 2021. The Pandora ransomware group has published several victims on its leak site in the Dark Web (TOR network), where they publicly announce their victims and threaten them with the data leak. In this post, we’ll be looking at detecting the presence of Pandora ransomware using Wazuh. We’ll also look at detecting common techniques being used by Rook and its variants.
Pandora is packed using the UPX packer and, when executed, it changes its privilege level and sets itself as a critical process. It also disables the Event Tracing for Windows (ETW) and further bypasses Antimalware Scan Interface (AMSI) to evade detection by antivirus products. Eventually, the malware encrypts files on the target machine and displays a ransom note. Pandora malware has been analyzed extensively and known indicators of compromise (IOCs) can be seen below.
File Hashes Type Description 0c4a84b66832a08dccc42b478d9d5e1b MD5 Binary 160320b920a5ef22ac17b48146152ffbef6046f SHA-1 Binary 5b56c5d86347e164c6e571c86dbf5b1535eae6b979fede6ed66b01e79ea33b7b SHA-256 Executable
Detection techniques
- Using FIM to detect known IOCs
- Scanning files with VirusTotal
- Collecting Windows events via Sysmon
Using FIM to detect known IOCs
We can configure Wazuh to monitor file changes for any folder in a system. For example, this method helps detect whenever a user downloads a new file. The FIM module is located in the Wazuh agent, where it runs periodic scans of the system and stores the checksums and attributes of the monitored files in a local FIM database. The module looks for the modifications by comparing the new files checksums to the old checksums. All detected changes are reported to the Wazuh manager. Using the hash values above, we can write rules that alert us whenever the Pandora sample is added to any of our monitored folders. In our case, we configure the FIM module to monitor the Downloads folder:
<syscheck> <directories check_all="yes" realtime="yes">C:\Users\*\Downloads</directories> </syscheck>
Note
Configuring FIM directories using wildcard * is only supported for Wazuh manager and agents running version 4.3.0 or higher. For earlier versions, please specify the absolute path.
Next, we write rules that alert us whenever files, whose hash matches the Pandora IOCs, are downloaded. For example, to detect the Pandora ransomware executable we add the following to our local_rules.xml file:
<group name="syscheck,malware,">
<rule id="100008" level="10">
<if_sid>554</if_sid>
<field name="sha256">5b56c5d86347e164c6e571c86dbf5b1535eae6b979fede6ed66b01e79ea33b7b</field>
<description>Malware Hash Match: Pandora Ransomware Executable Detected</description>
</rule>
</group>
The following alert is seen when we download the Pandora ransomware artifact to the monitored folder:

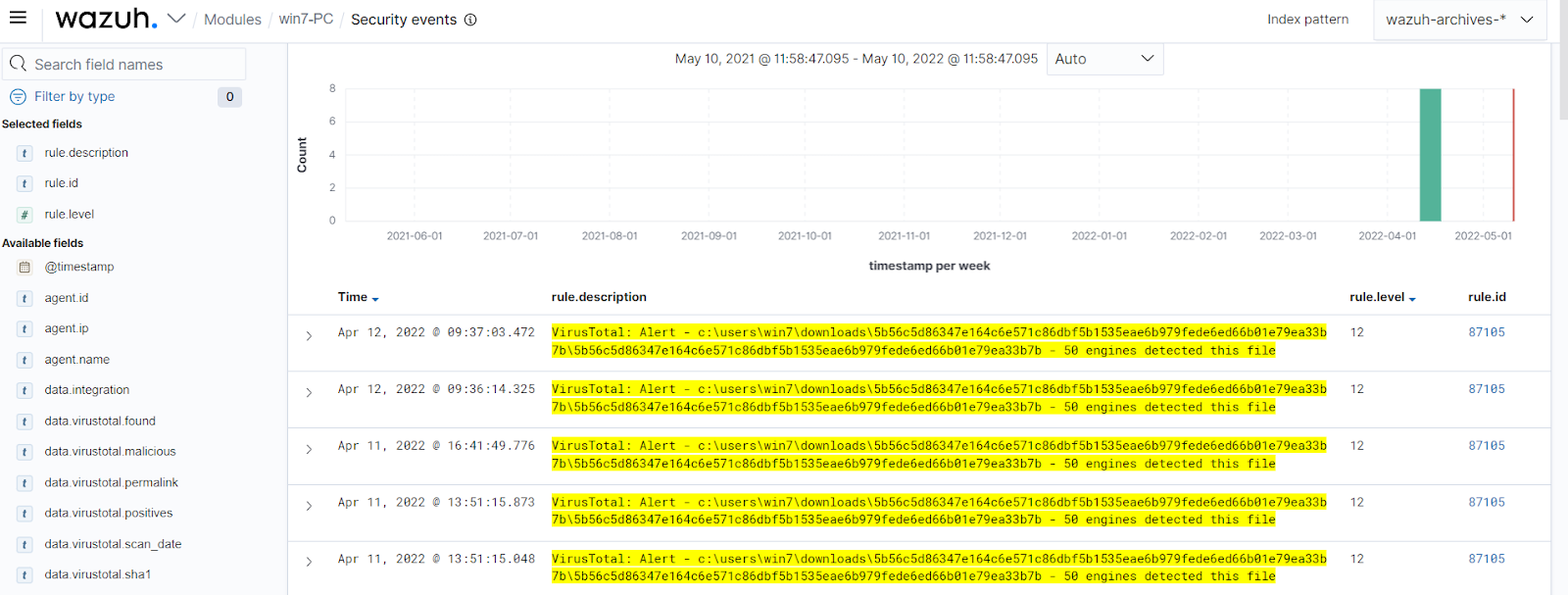
Scanning files with VirusTotal
Although using the FIM module to detect known IOCs hashes works, it is cumbersome to create an alert for every file hash. One way to automate the above technique is to use the VirusTotal integration to detect known malicious file hashes. VirusTotal aggregates many antivirus products and online scan engines, offering an API that can be queried by using either URLs, IPs, domains, or file hashes. The Wazuh integration can automatically perform a request to VirusTotal API with the hashes of files that are created or changed in any folder monitored with FIM. The process follows the steps below:
- File monitoring: The FIM module detects a file change and triggers an alert.
- VirusTotal request: After FIM triggers an alert, the Wazuh manager queries VirusTotal with the hash of the file.
- Alerting: If positive matches are found, the Wazuh manager generates a VirusTotal alert.
After enabling the integration, we get alerts whenever the malicious Pandora ransomware files are added to our monitored folders.
Collecting Windows events via Sysmon
As we stated in the introduction, Pandora is a variant of Rook ransomware, which means that the detection techniques above may not be able to detect other variants of this ransomware with different IOCs. Another way to detect the presence of Pandora ransomware is using Wazuh to collect process creation events through Sysmon. During a deep dive analysis of the processes created by Pandora, it is seen that it deletes shadow copies using vssadmin. The image below shows the processes that are created by Pandora, including using vssadmin to delete shadow copies.
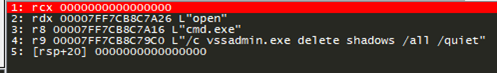
This process is initiated before files are encrypted and using the steps below we can configure Wazuh to detect Pandora by collecting Windows events via Sysmon:
Step 1: Install Sysmon on monitored endpoint.
- Sysmon is downloaded from the Microsoft Sysinternals page and is installed with the configuration file sysmonconfig.xml.
- The following command is used to install Sysmon, with the downloaded configuration file, via PowerShell.
sysmon.exe -accepteula -i sysmonconfig.xml
Step 2: Configure the Wazuh agent to collect Sysmon events.
- Configure the agent to capture Sysmon events by adding the following settings to the agent configuration file in “C:\Program Files (x86)\ossec-agent\ossec.conf”.
<localfile> <location>Microsoft-Windows-Sysmon/Operational</location> <log_format>eventchannel</log_format> </localfile>
- Apply the changes by restarting the agent using this PowerShell command.
Restart-Service -Name wazuh
Step 3: Create a ransomware detection rule.
To generate the alert, the following rule is added to the/var/ossec/etc/rules/local_rules.xml file on the Wazuh manager.
<group name="windows,sysmon">
<rule id="100009" level="12">
<if_group>windows</if_group>
<field name="win.system.eventID">1</field>
<match>vssadmin.exe delete shadows</match>
<description>[Possible Ransomware] Suspicious vssadmin Process Launched!</description>
</rule>
</group>
When we run the ransomware sample again, we get alerts seen below.

Conclusion
This article demonstrates how to detect known adversary behavior like Pandora ransomware. We used Wazuh FIM, VirusTotal, and Sysmon detection rules to show examples of detection for this particular ransomware.