File Integrity Monitoring (FIM) is an IT security process that validates the integrity of system files to ensure they have not been tampered with or modified. This security process provides IT teams with file-level intelligence on when files are accessed, who tempers with files, and what is changed in files. Implementing File Integrity Monitoring helps organizations detect unauthorized file changes and some early signs of malicious actions and meet regulatory compliance standards.
Wazuh provides an open source File Integrity Monitoring module that helps security analysts gain visibility and track changes to sensitive system files, directories, and Windows Registry files in real-time. The Wazuh open source FIM module monitors and verifies the integrity of files and Windows Registry keys by continuously checking the hashes of these files in real-time to detect modifications. It performs real-time and scheduled system scans, tracking file changes as they happen or at particular intervals respectively. It can also monitor file attributes, extension changes, user actions on files, and user permission changes.
You can combine the Wazuh open source FIM module with other Wazuh capabilities to detect and respond to cyber threats.
Benefits of the Wazuh open source FIM
The Wazuh open source FIM module offers a wide range of benefits that you can utilize to gain file-level visibility into your organization for better security. These benefits include:
- Open source: The Wazuh open source FIM module is free to use and customize. It provides a cost-effective, flexible, and transparent way for organizations to secure their sensitive and critical files.
- Change management: The Wazuh open source FIM module detects changes to system files, directories, and Windows Registries protecting them from unauthorized access. It has real-time and scheduled file scanning options that provide you insights into events as they occur or at specified intervals respectively. These events are reported on the Wazuh dashboard aiding security analysts to visualize how files, directories, and Windows Registry keys are changed, who or what process accessed them, and when it occurred.
- Cyber threat protection: The Wazuh open source FIM module combined with other Wazuh capabilities provides you with a robust approach to protecting your organization against cyber threats. For example, you can configure it to detect malware intrusion and automatically trigger an incident response action to remediate the event. This approach helps organizations to promptly respond to cyber incidents.
- Compliance and audit support: The Wazuh open source FIM module helps organizations comply with security standards such as PCI DSS, GDPR, and NIST 800-53. The Wazuh open source FIM module provides an audit trail of file changes and logs within an organization that can be generated into reports to meet regulations and compliance requirements.
Use case
We simulate a scenario involving a malicious actor within an organization. In this scenario, we attempt to compromise a Windows and Linux endpoint’s security by executing a script that mimics the behaviors of malware. The script performs the following malicious actions:
- The script creates a
malicious_file.txtfile in the folderC:\WazuhFIMtestof the Windows endpoint and/root/WazuhFIMtestdirectory of the Linux endpoint. - The
rootuser permission of the filemalicious_file.txtis changed from read and write toread,write, andexecutablein the Linux endpoint andAdministratorin the Windows endpoint. - It creates a new Windows Registry key,
WazuhApp, with the value nameWazuhkeyin the Windows Registry path,HKEY_CURRENT_USER\Software. - It writes the text “Wazuh FIM test: malicious hex” to every file in the folder
C:\WazuhFIMteston the Windows endpoint and the directory/root/WazuhFIMteston the Linux endpoint. - It deletes the sensitive file,
financialrecord.txtfrom the endpoints.
Infrastructure
- A pre-built, ready-to-use Wazuh OVA 4.7.2. Follow this guide to download and configure the virtual machine (VM). This VM hosts the Wazuh central components (Wazuh server, Wazuh indexer, and Wazuh dashboard).
- A Windows 11 endpoint with Wazuh agent 4.7.2 installed and enrolled to the Wazuh server.
- An Ubuntu 22.04.3 endpoint with Wazuh agent 4.7.2 installed and enrolled to the Wazuh server.
Configuration
In our configuration, we enable the attributes whodata, realtime, check_all, and report_changes on the Wazuh agent to report real-time changes.
Where:
whodatarecords the user who performs an action on a monitored file. We configure this setting on the Ubuntu endpoint.realtimeenables real-time change detection. We configure this setting on the Windows endpoint.check_allrecords all the file attribute values.report_changesenables reporting of content change in a file.
By default, Wazuh provides rule IDs 554, 550, and 553 to detect file addition, modification, and deletion events.
Windows
We perform the following configuration in the Windows endpoint.
1. Create a new directory WazuhFIMtest in the C:\ folder:
> mkdir C:\WazuhFIMtest
2. Create some dummy files in the newly created C:\WazuhFIMtest folder:
> type NUL > financialrecord.txt > type NUL > sensitivefile.txt > type NUL > testfile.txt
3. Configure the directory and Windows Registry path to be monitored in the C:\Program Files (x86)\ossec-agent\ossec.conf file. In this scenario, we configure the C:\WazuhFIMtest directory and the Windows Registry path HKEY_LOCAL_MACHINE\SYSTEM\Setup to monitor the file and Windows Registry key changes.
- Directory path:
<ossec_config> <syscheck> <directories realtime="yes" check_all="yes">C:\WazuhFIMtest</directories> </syscheck> </ossec_config>
- Registry path:
<ossec_config> <syscheck> <windows_registry>HKEY_LOCAL_MACHINE\SYSTEM\Setup</windows_registry> </syscheck> </ossec_config>
4. Restart the Wazuh agent to apply the configuration using the command below:
> Restart-Service -Name wazuh
Ubuntu
We perform the following configuration in the Ubuntu endpoint.
1. Run the command below to install auditd. The who-data monitoring functionality uses the Linux Audit subsystem, auditd, to get information about who makes the changes in a monitored directory.
# apt-get install auditd
2. Create a directory WazuhFIMtest in the /root directory using the command below:
# mkdir /root/WazuhFIMtest && cd /root/WazuhFIMtest
3. Create some dummy files in the newly created /root/WazuhFIMtest directory::
# touch financialrecord.txt # touch sensitivefile.txt # touch testfile.txt
4. Append the configuration below to the /var/ossec/etc/ossec.conf file to monitor the /root/WazuhFIMtest directory:
<ossec_config>
<syscheck>
<directories whodata="yes" check_all="yes" report_changes="yes">/root/WazuhFIMtest</directories>
</syscheck>
</ossec_config>
5. Restart the Wazuh agent to apply the configuration using the command below:
# systemctl restart wazuh-agent
Attack emulation
We emulate an attack by creating and running a Python script fim_script.py with the content below on both Windows and Linux endpoints.
import platform
import subprocess
import os
import time
# Function to detect the OS
def get_os():
return platform.system()
# Function to create a file
def create_file(filename, content=""):
with open(filename, 'w') as file:
file.write(content)
print(f"File created: {filename}")
# Function to modify a file
def modify_file(file_path, text_to_append):
try:
if os.path.isfile(file_path):
with open(file_path, 'a') as file:
file.write(text_to_append + '\n')
print(f"Text appended to {file_path}")
else:
print(f"File not found: {file_path}")
except IOError as e:
print(f"Error modifying file: {e}")
# Function to find and modify files in the specified directory
def find_and_modify_files(directory, text_to_append, file_extension=None):
for file in os.listdir(directory):
if file_extension and not file.endswith(file_extension):
continue
file_path = os.path.join(directory, file)
if os.path.isfile(file_path):
modify_file(file_path, text_to_append)
# Function to delete a file
def delete_file(filename):
try:
os.remove(filename)
print(f"File deleted: {filename}")
except Exception as e:
print(f"Error deleting file: {e}")
def create_registry_key(key_path, key_name, value="Your Value"):
os_type = get_os()
if os_type != "Windows":
print("Registry operations are only supported on Windows.")
return
try:
import winreg
with winreg.ConnectRegistry(None, winreg.HKEY_LOCAL_MACHINE) as hkey:
with winreg.CreateKey(hkey, key_path) as reg_key:
winreg.SetValueEx(reg_key, key_name, 0, winreg.REG_SZ, value)
print(f"Registry key {key_name} created at {key_path}")
except Exception as e:
print(f"Error creating registry key: {e}")
# Main function to use the above functions
def main():
if get_os() == "Windows":
directory = r"C:\WazuhFIMtest"
elif get_os() == "Linux":
directory = "/root/WazuhFIMtest"
else:
print("Unsupported operating system.")
return
print(f"The current working directory is {directory}")
filename = os.path.join(directory, "malicious_file.txt")
create_file(filename)
time.sleep(2)
if get_os() == "Linux":
# Change file permission to rwx for the root user.
subprocess.run(['chmod', '0744', filename], check=True)
print(f"File permissions changed to rwx for the root user: {filename}")
time.sleep(2)
elif get_os() == "Windows":
create_registry_key(r"SYSTEM\Setup\WazuhApp", "WazuhKey")
# Modify files in the specified directory
text_to_append = "Wazuh FIM test: malicious hex"
find_and_modify_files(directory, text_to_append)
# Wait for 5 seconds before deleting the file
time.sleep(5)
if get_os() == "Windows":
delete_file(r"C:\WazuhFIMtest\financialrecord.txt")
elif get_os() == "Linux":
delete_file(r"/root/WazuhFIMtest/financialrecord.txt")
else:
print("Unsupported operating system.")
if __name__ == "__main__":
main()
Windows
We simulate the attack in the Windows endpoint by following the configuration steps below:
1. Create the Python script fim_script.py in the folder C:\WazuhFIMtest.
2. Download the Python installer from the official website and install it. We require Python to execute the script.
3. Install the pywin32 package, (this dependency is required for the script to run) with the command below:
> pip install pywin32
4. Run the malicious fim_script.py script on the victim endpoint with administrator privilege using the command below:
> python fim_script.py
Output:
The current working directory is C:\WazuhFIMtest File created: C:\WazuhFIMtest\malicious_file.txt Registry key WazuhKey created at SYSTEM\Setup\WazuhApp Text appended to C:\WazuhFIMtest\financialrecord.txt Text appended to C:\WazuhFIMtest\malicious_file.txt Text appended to C:\WazuhFIMtest\sensitivefile.txt Text appended to C:\WazuhFIMtest\testfile.txt File deleted: C:\WazuhFIMtest\financialrecord.txt
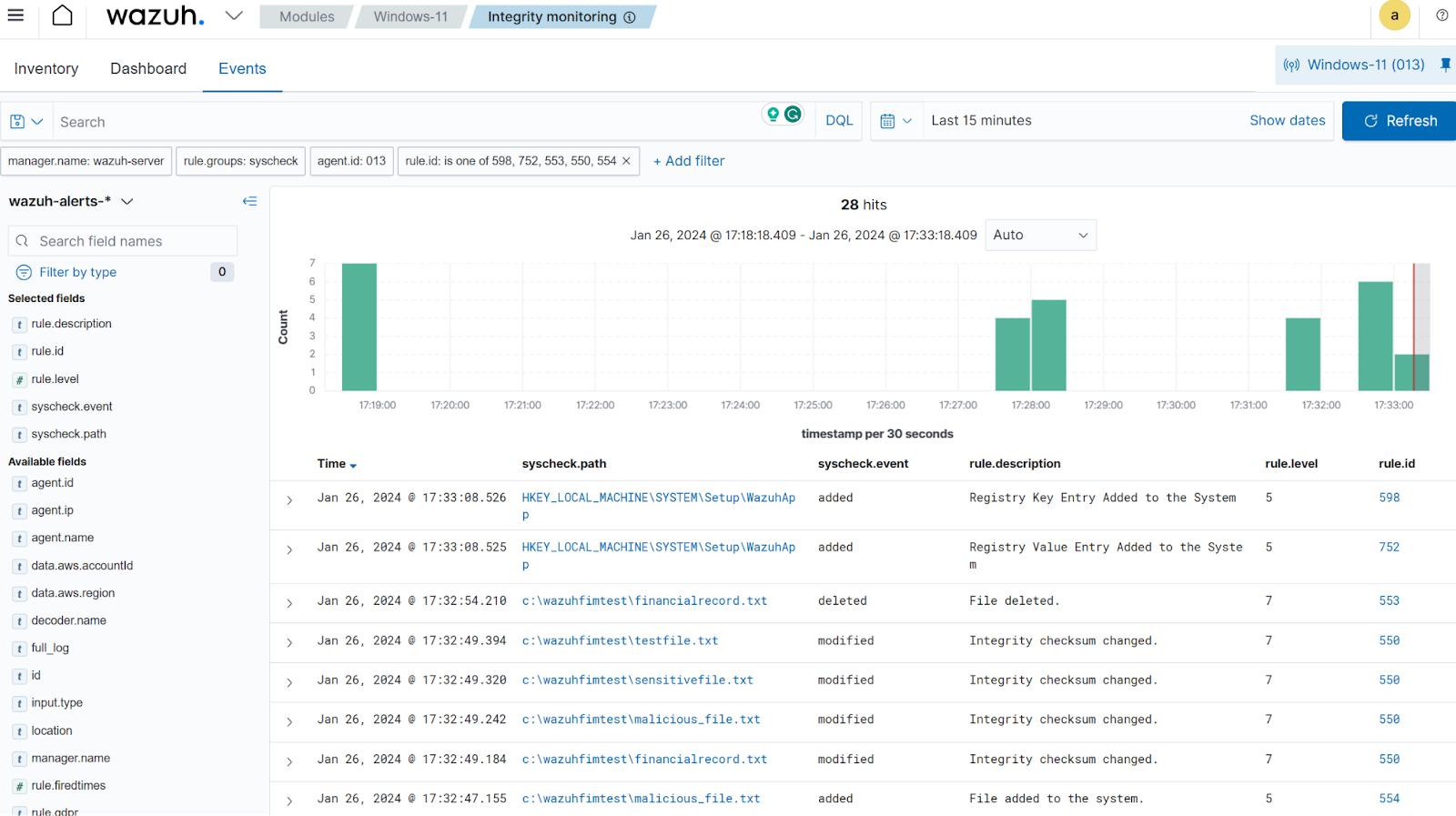
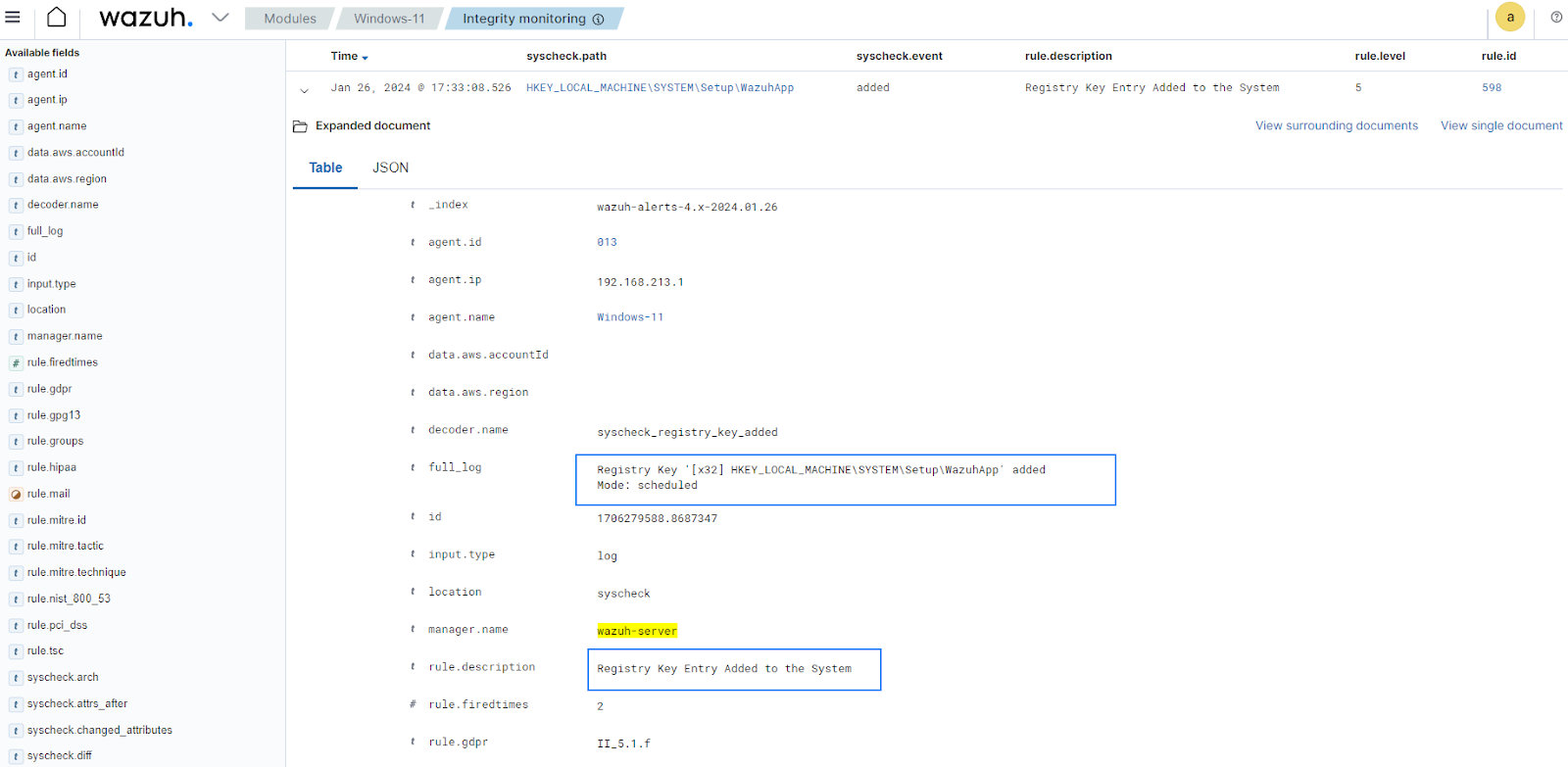
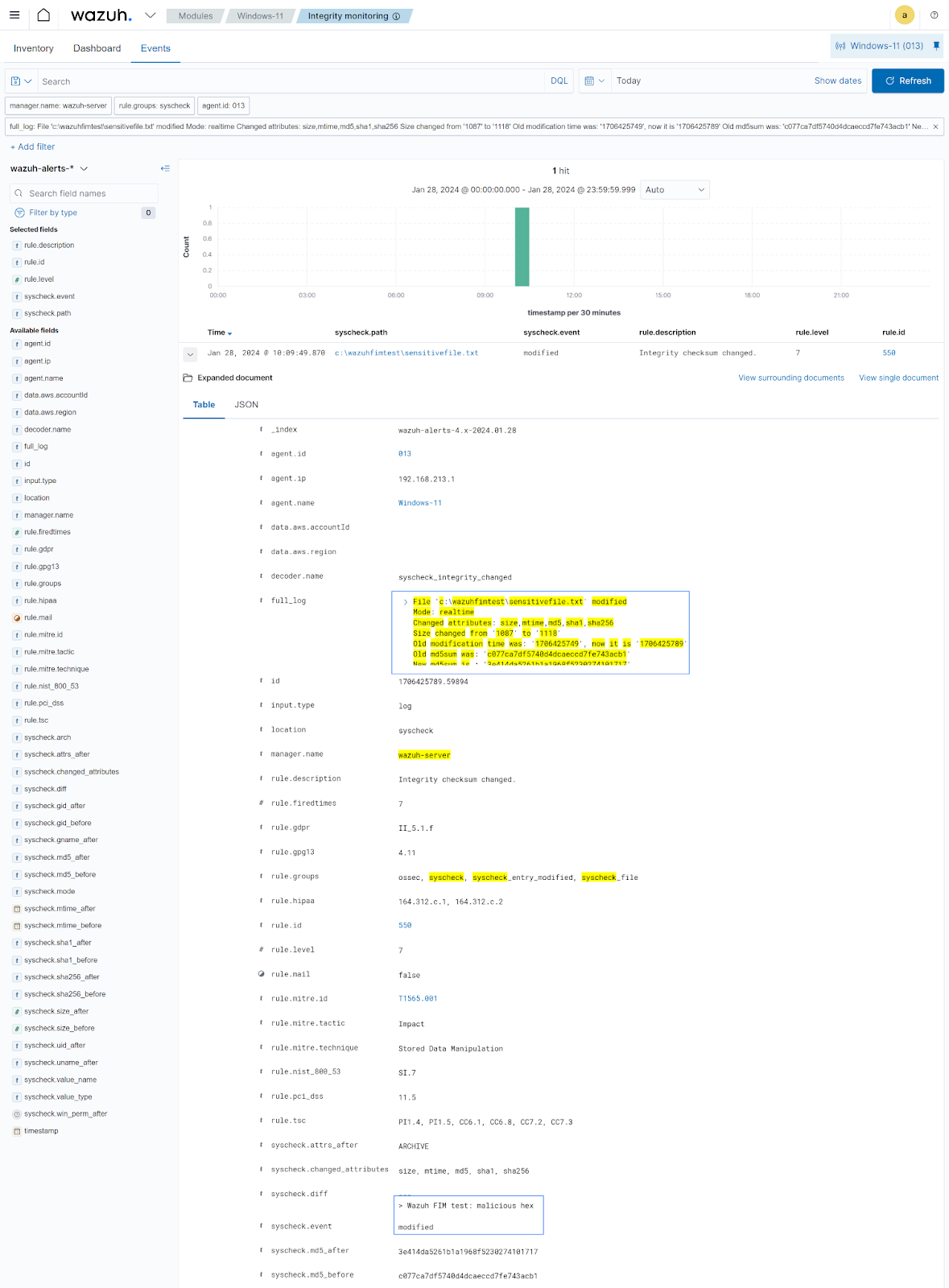
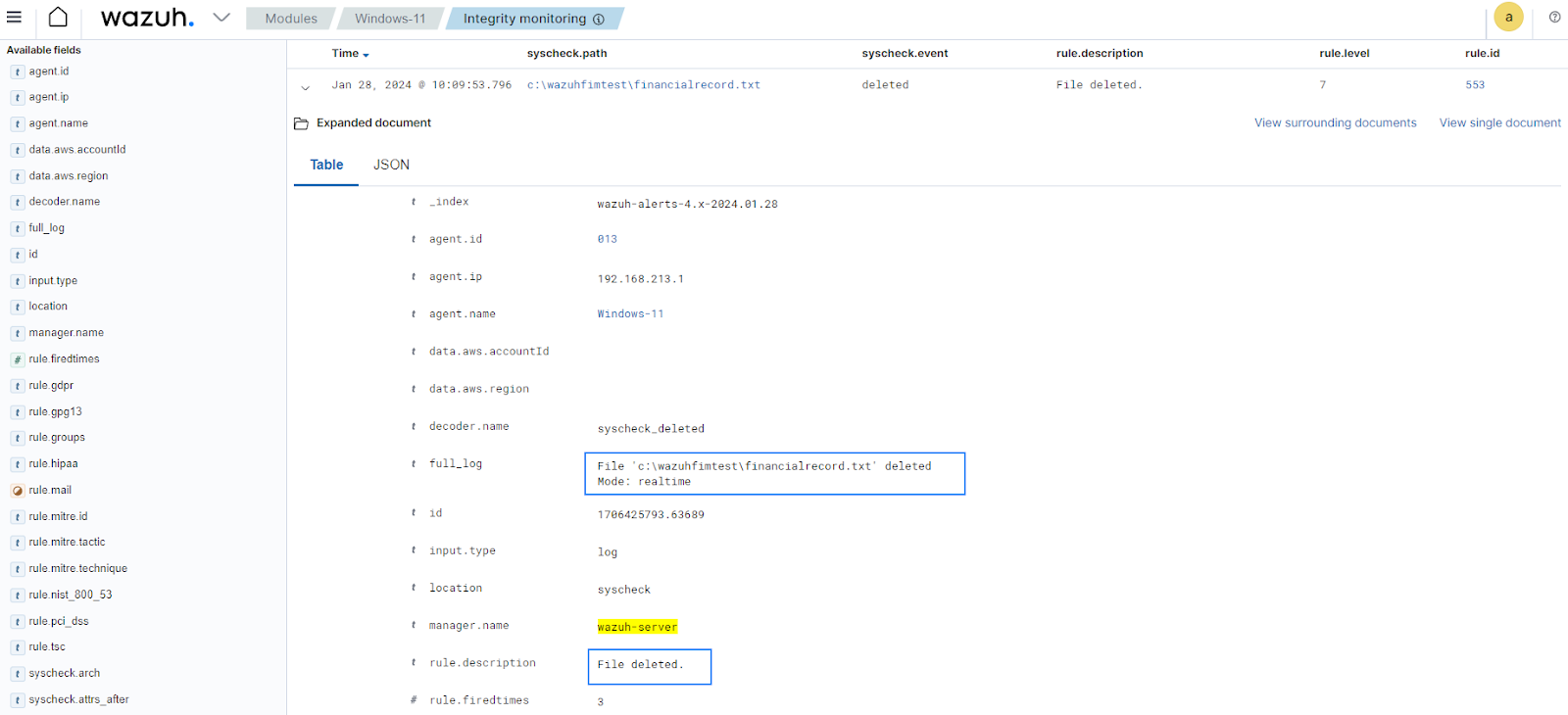
Detection result
Visit the Wazuh dashboard and navigate to the Modules > Security events tab to view the generated alerts.

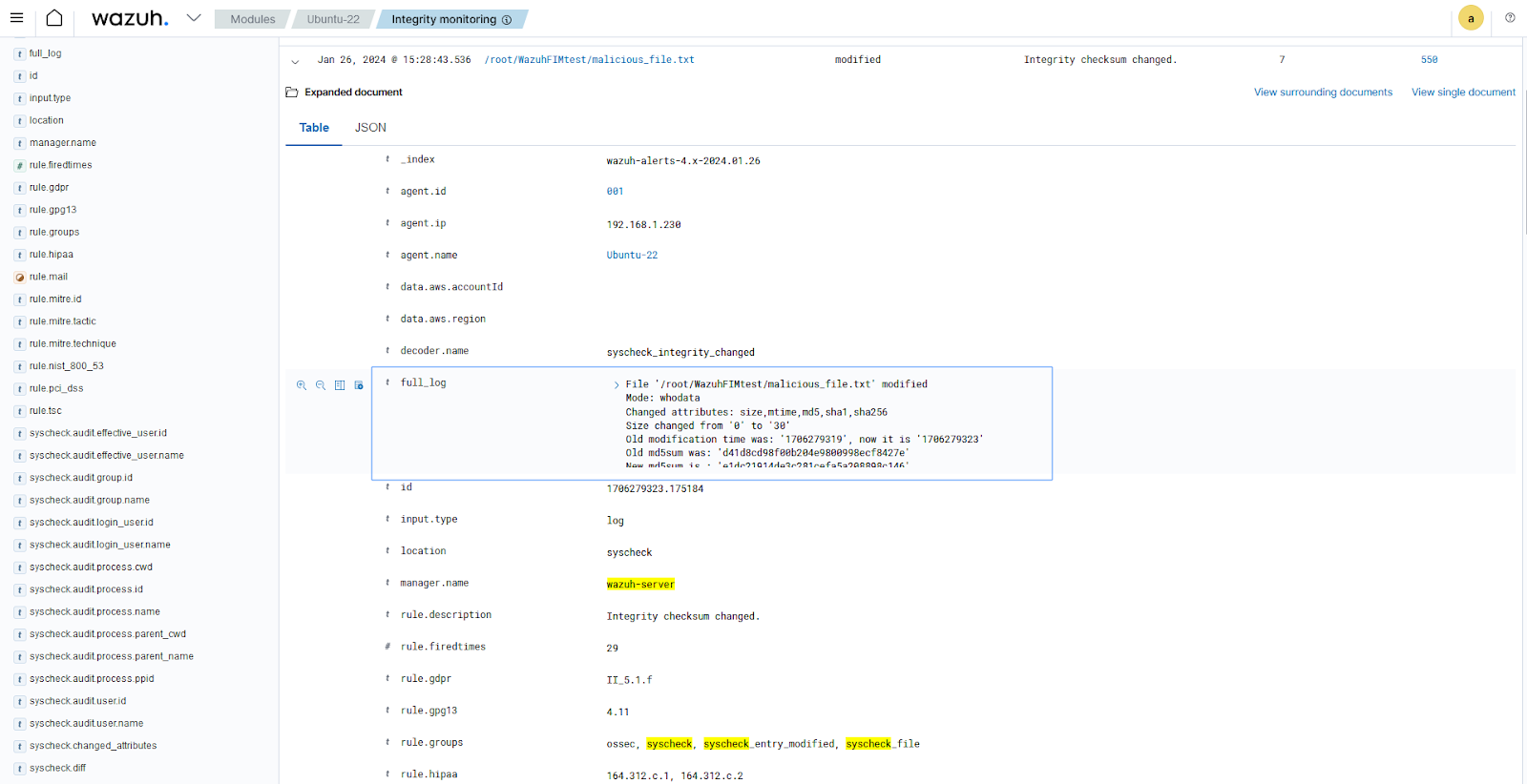
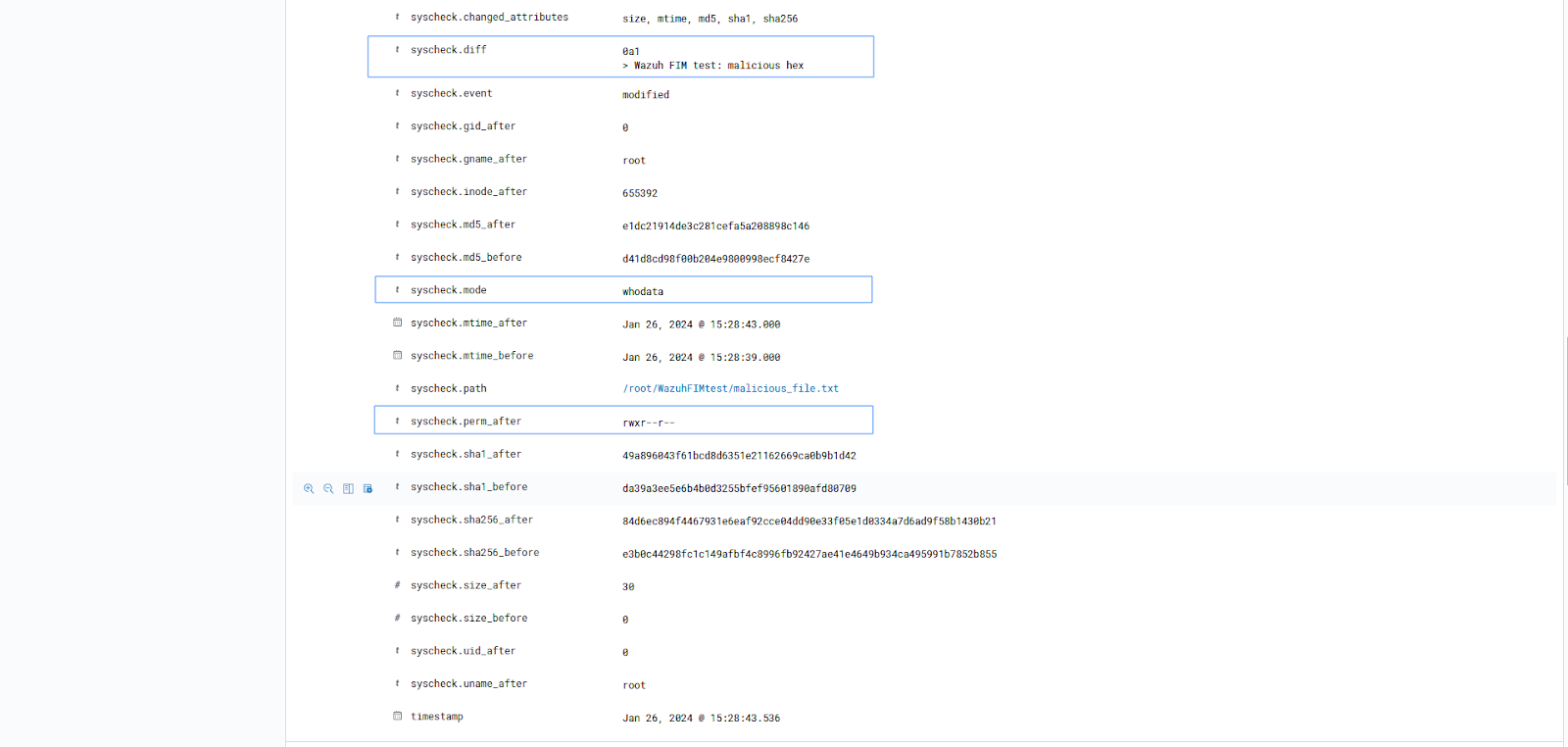
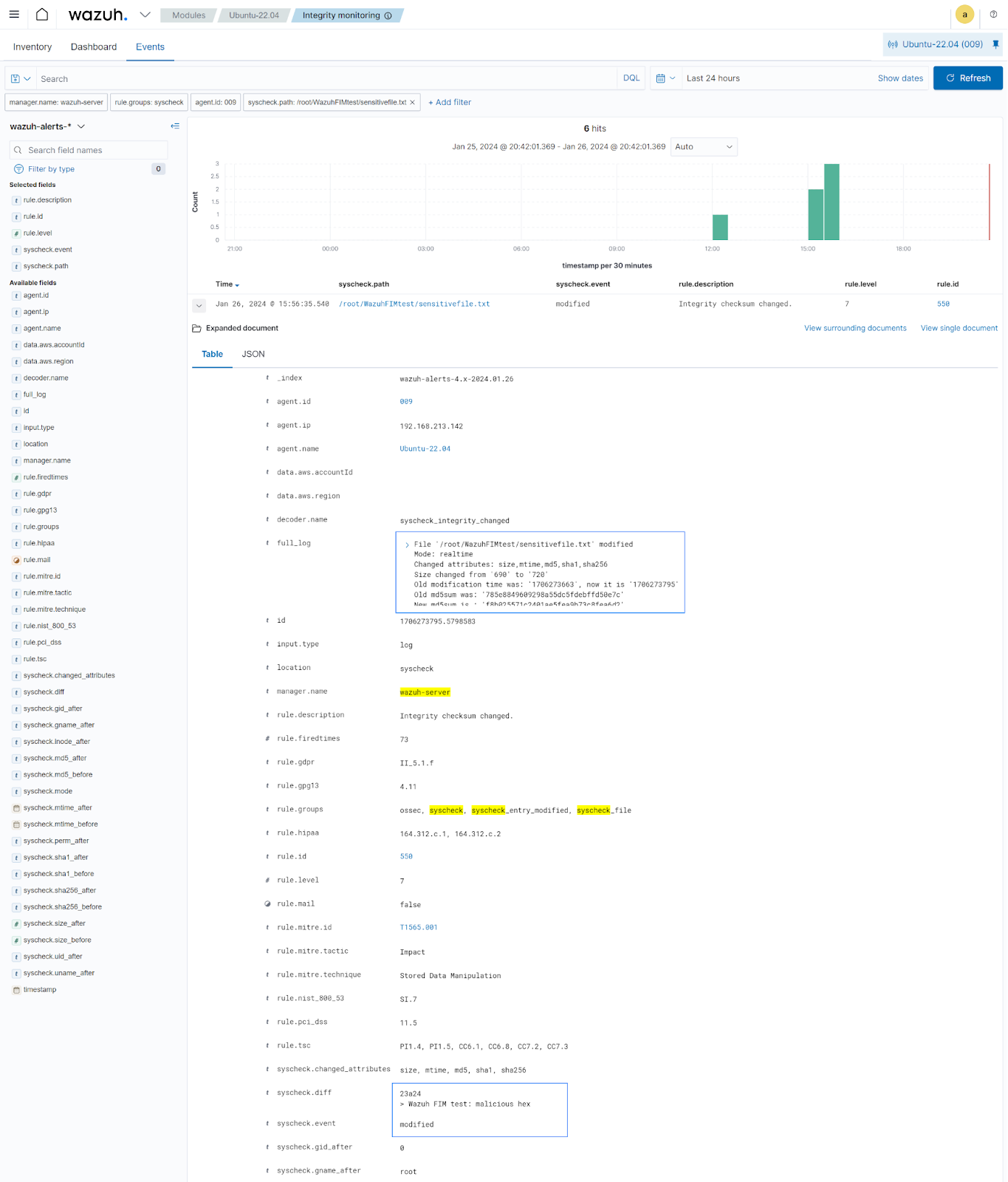
Ubuntu
We simulate the attack in the Ubuntu endpoint by following the configuration steps below:
1. Create the Python script fim_script.py in the /tmp directory.
2. The script fim_script.py requires python3 for its execution. Install Python3 if it is not pre-installed using the command below:
# sudo apt update # sudo apt install python3
3. Execute the malicious script to capture the malware behaviors:
# python3 /tmp/fim_script.py
Output:
The current working directory is /root/WazuhFIMtest File created: /root/WazuhFIMtest/malicious_file.txt File permissions changed to rwx for the root user: /root/WazuhFIMtest/malicious_file.txt Text appended to /root/WazuhFIMtest/malicious_file.txt Text appended to /root/WazuhFIMtest/financialrecord.txt Text appended to /root/WazuhFIMtest/testfile.txt Text appended to /root/WazuhFIMtest/sensitivefile.txt File deleted: /root/WazuhFIMtest/financialrecord.txt
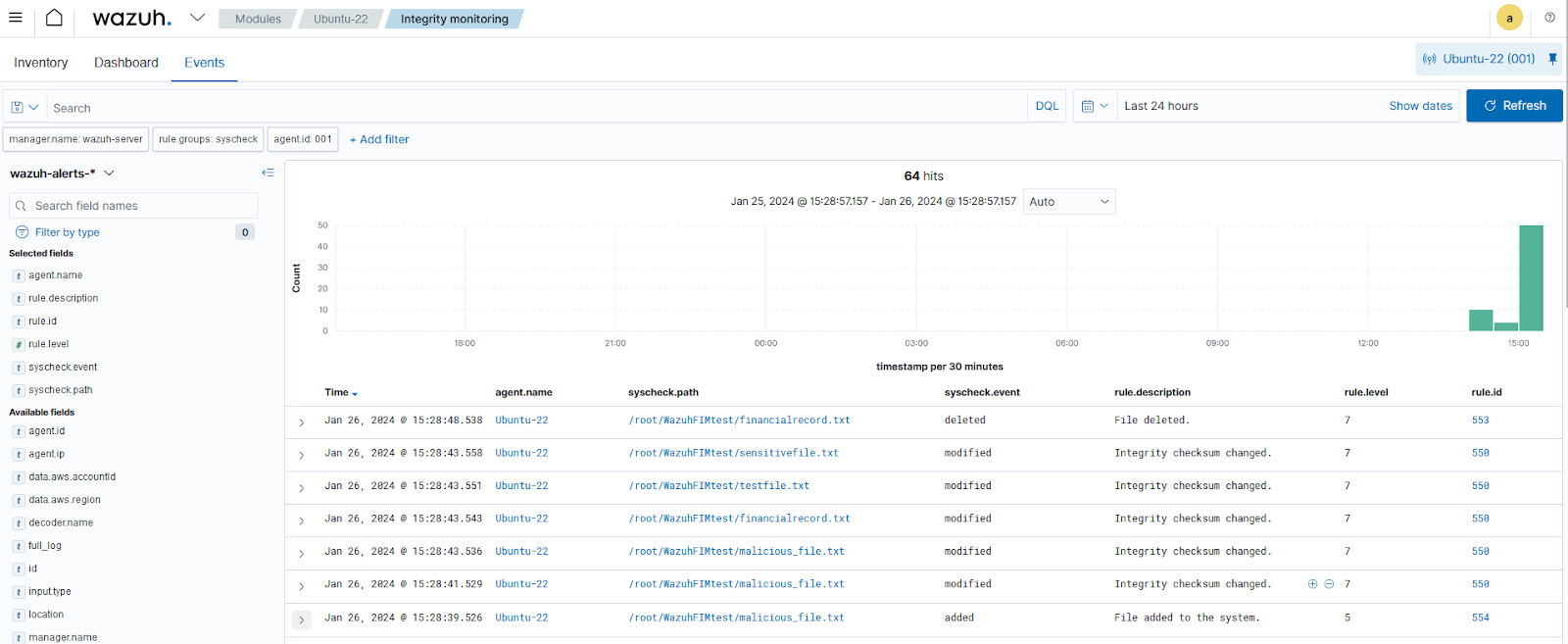
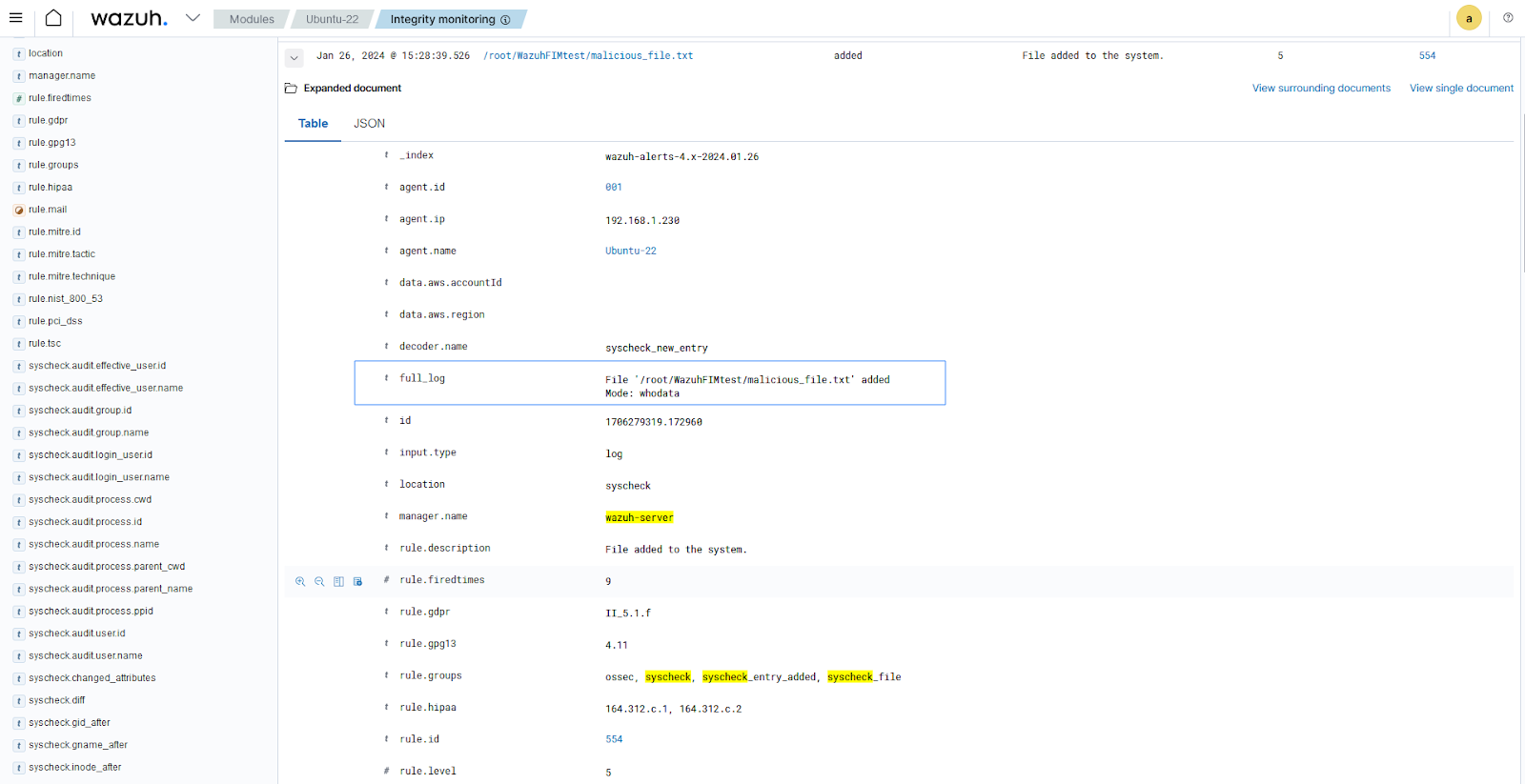
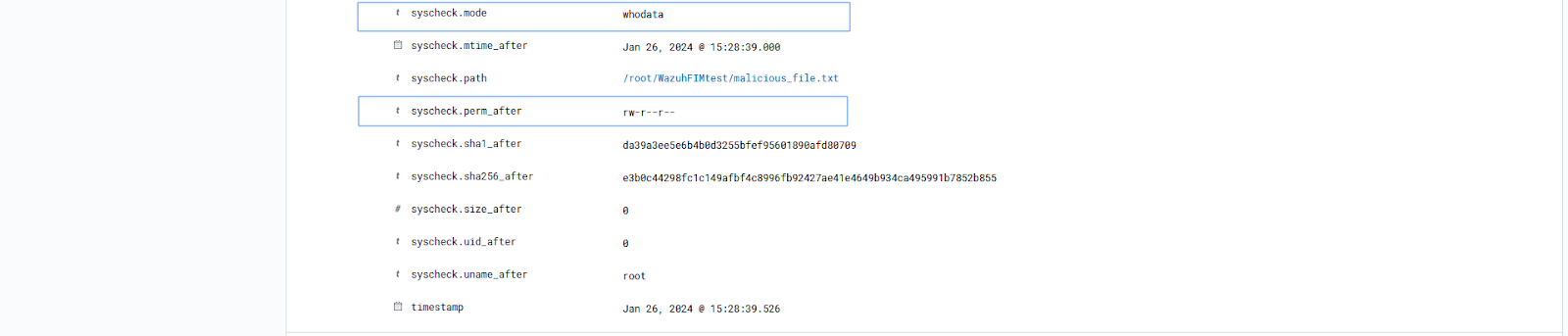
Detection result
Visit the Wazuh dashboard and navigate to the Modules > Security events tab to view the generated alerts.
Conclusion
In this blog post, we demonstrated how to utilize the Wazuh open source FIM module to detect file creation, deletion, modification, and Windows Registry manipulation. The Wazuh FIM module enables security analysts to monitor and detect changes made to monitored files, directories, and Windows Registry. File integrity monitoring helps organizations detect malware persistence, protect sensitive files, and prevent data theft.
Wazuh is an open source security platform for threat detection, compliance, and incident handling. It provides several capabilities including Security Configuration Assessment (SCA), vulnerability detection, malware detection, and more. You can integrate it with third-party solutions and technologies. Wazuh also has an ever-growing community to support users. To learn more about Wazuh, please check out our documentation and blog posts.
References
1. File integrity monitoring – Capabilities · Wazuh documentation
2. How it works – File integrity monitoring · Wazuh documentation