Actions to prevent and detect ransomware attacks are mandatory to keep your system safe. In this article you will learn how Wazuh can help detect ransomware attacks in progress using the file integrity monitoring module.
In recent years increasing waves of attacks with ransomware have been reported targeting different business sectors. This particular type of malware is designed to deny access to a computer system or data, via encryption, until a ransom is paid.
Ransomware spreads typically through email phishing and spam (messages with links to compromised websites or malicious attachments). Besides, some ransomware families, like WannaCry, do take advantage of exploits to infect other systems in the network, meaning that they do not require human help to propagate. In order to avoid ransomware, it is recommended to keep your systems updated and properly secured, backup your data on a regular basis and educate your end-users in security. The modules that help prevent and detect ransomware are:
- Scanless vulnerability detection: Identifies vulnerable systems and applications correlating inventory data with well known CVEs.
- Security Configuration Assessment: Used to expose poorly configured systems. It runs configuration checks periodically, enforcing good practices by following standards such as CIS (Center of Internet Security).
- File integrity monitoring: Monitors changes to the file system, and can be used to detect the presence of malicious files (see, for example, our integration with VirusTotal).
File system events during a ransomware attack
The following actions are performed by the ransomware during an attack:
- Read the file content.
- Encrypt the content and write it into a new file.
- Remove the original file.
Since Wazuh file integrity monitoring is able to monitor addition, changes, and deletion of files in directories, we can easily detect that new files are being created when encrypted and the original ones are removed. If an unlikely high number of file creation and deletion alerts are reported, we could be facing a ransomware attack.
Detecting ransomware with Wazuh by monitoring the file system
Let’s now run a simple proof of concept using Wazuh file integrity monitoring module. For it, we created a Python script (wazuh-ransomware-poc.py) to simulate a ransomware attack. The script requires Python 3 and the cryptography package.
Step 1: Prepare the test environment
First, we create the /home/vagrant/test directory:
# mkdir -p /home/vagrant/test
We need to configure the Wazuh agent to monitor the previous directory:
<syscheck>
<directories check_all="yes" whodata="yes">/home/vagrant/test</directories>
</syscheck>
Note that we enabled whodata. This will make the Wazuh agent use an integration with the operating system kernel in order to report file changes in real-time and include details on who and how those changes were made.
Restart the agent to apply changes:
# systemctl restart wazuh-agent
We create several files and subdirectories in our agent. By default, the script will add 10 directories with 20 files each of 1KB in /home/vagrant/test:
# python3 wazuh-ransomware-poc.py prepare
Now the directories and files created can be listed:
# ls -lRh /home/vagrant/test/ /home/vagrant/test/: total 40K drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_00 drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_01 drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_02 drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_03 drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_04 drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_05 drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_06 drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_07 drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_08 drwxr-xr-x. 2 root root 4.0K Nov 28 14:27 Directory_09 /home/vagrant/test/Directory_00: total 80K -rw-r--r--. 1 root root 1.0K Nov 28 14:27 File_00.txt -rw-r--r--. 1 root root 1.0K Nov 28 14:27 File_19.txt /home/vagrant/test/Directory_01: total 80K -rw-r--r--. 1 root root 1.0K Nov 28 14:27 File_00.txt
From the Wazuh UI, we can see the new files:
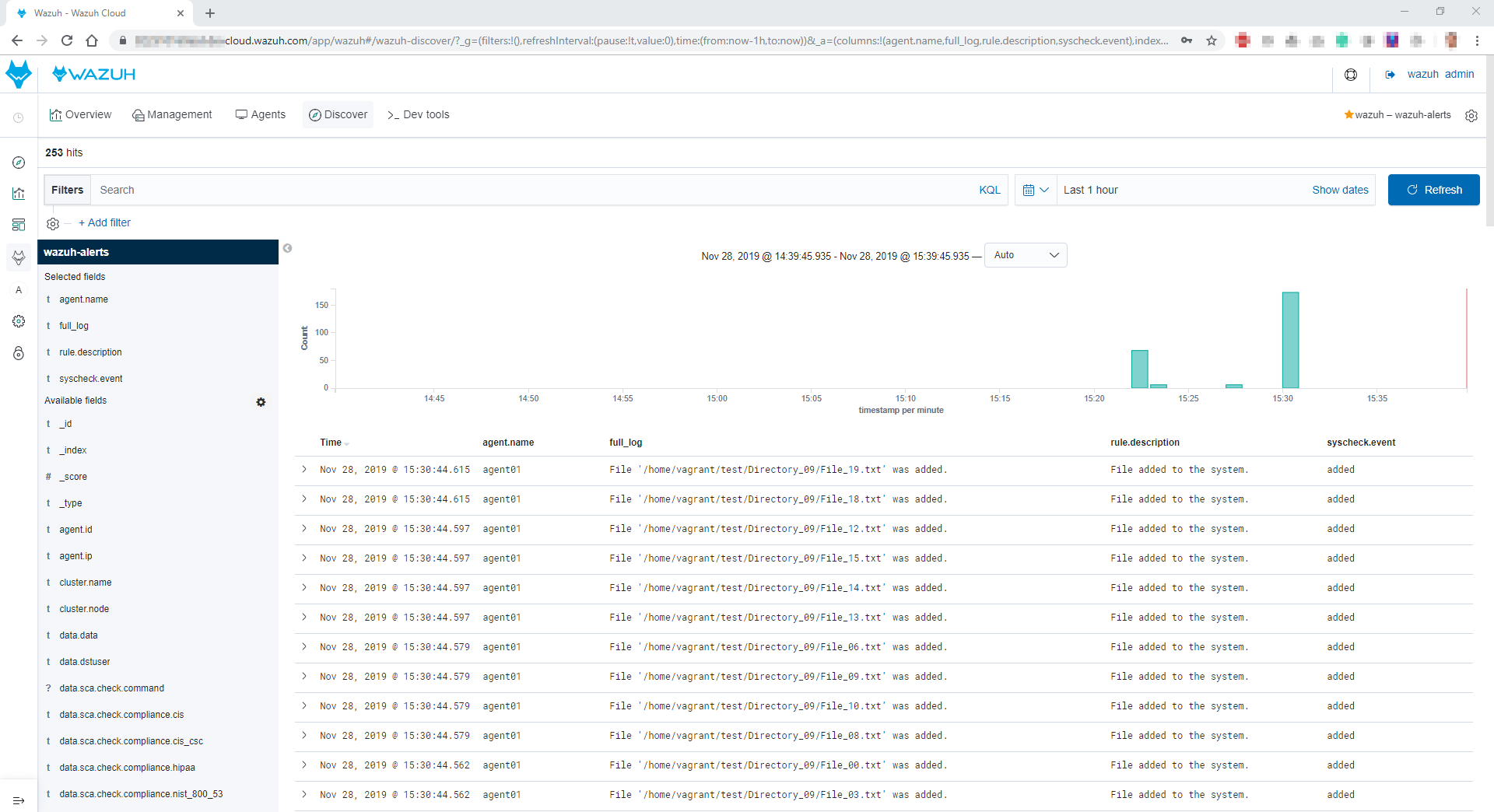
Step 2: Simulating the attack
Now it is time to simulate the ransomware attack. The following command will encrypt every file in /home/vagrant/test and will remove the original one:
# python3 wazuh-ransomware-poc.py attack
From the Wazuh UI, we see the two types of file integrity monitoring alerts: added and deleted.
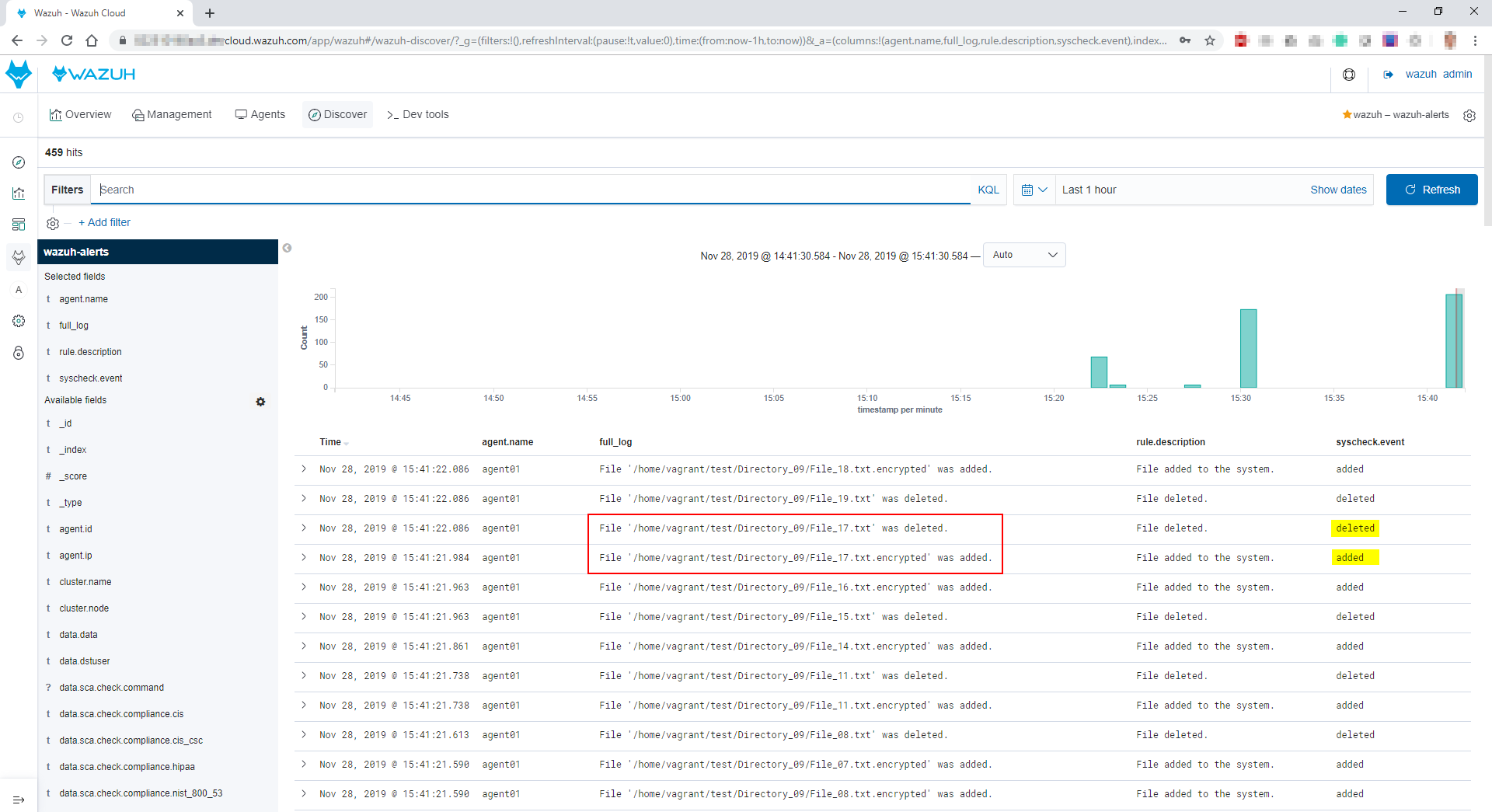
Wazuh successfully detected the events that are generated during the attack in this simulation.
Monitoring Wazuh alerts and setting up triggers
We have seen that Wazuh is able to detect the events generated by a ransomware attack, but it still can be difficult for a person to know when the attack is going on. That is why it helps to automatically trigger alerts when this situation is detected. For this purpose, we use the Alerting feature of Open Distro (the free and open source alternative to Elastic Watchers).
First, we create a monitor for the file added alerts (filter: syscheck.event is added):
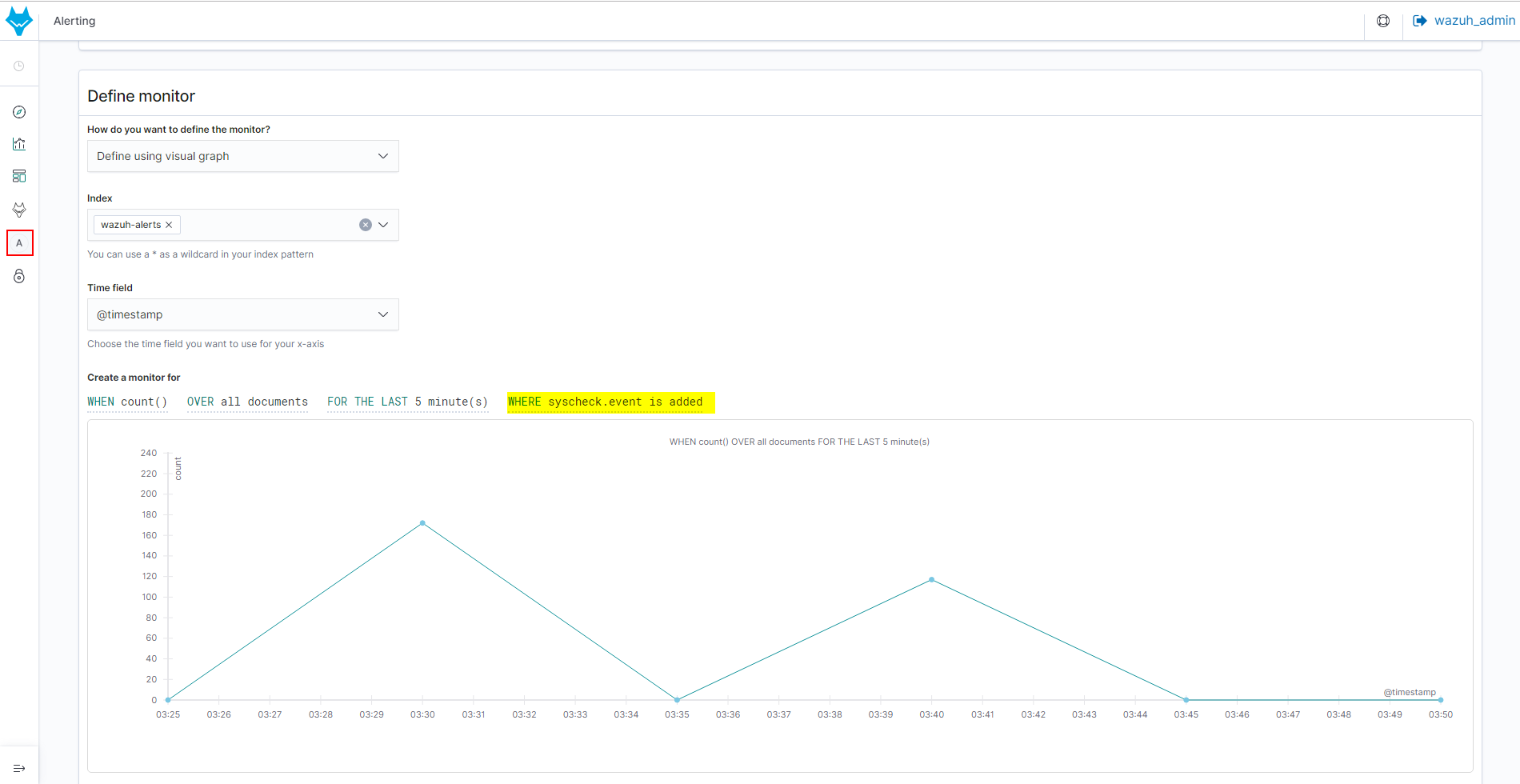
Then, for the previous defined monitor, we create a trigger setting the condition to 100 hits. You can adjust this parameter to your own needs:

Finally, we create another monitor for file deleted alerts (filter: syscheck.event is deleted) and the corresponding trigger.
Next time Wazuh detects the attack behavior, we can see both monitors with active status at the same time:
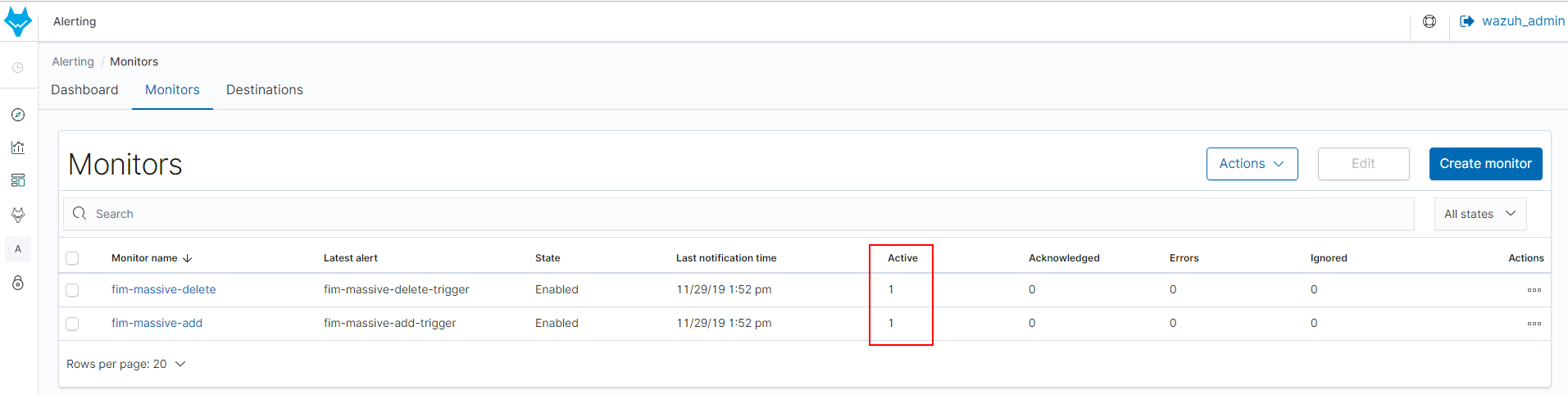
Additionally, you can send these alerts to third-party services such as Amazon Chime, Slack, ServiceNow or a custom webhook using the Action setting of a trigger.
Conclusion
Thanks to the file integrity monitoring module, it is possible to react quickly to a ransomware attack in progress, which is crucial for the security of our systems.
In our documentation you can learn how to block the attack using custom rules and the Active response module. We also recommend the Vulnerability detector module to identify unpatched software and the Security Configuration Assessment to enforce secure system configurations.
If you have any questions about this, join our Slack #community channel! Our team and other contributors will help you.