STRRAT is a Java-based remote access trojan (RAT) that provides threat actors with full remote control of infected Windows endpoints. STRRAT focuses on stealing credentials from browsers and email clients like Microsoft Edge, Google Chrome, Mozilla Firefox, Microsoft Outlook, Mozilla Thunderbird, and Foxmail. It also steals credentials by recording keystrokes of infected endpoints.
Previous versions of STRRAT relied on Java Runtime Environment (JRE) installed on infected endpoints. Recently, this trojan has acquired the ability to deploy its own JRE on infected endpoints.
STRRAT is usually delivered by phishing emails, and it allows attackers to run a plethora of commands on infected endpoints.
In this blog post, we use Wazuh to detect the malicious activities of STRRAT.
STRRAT behavior
- STRRAT poses as ransomware by adding a
.crimsonextension to the files on the victim endpoint, although it does not encrypt the files. - STRRAT collects basic information like system architecture, the presence of antivirus software, and the operating system of the victim endpoint.
- STRRAT creates a
<digits>lock.filefile in theC:\Users\<USER_NAME>\folder. The<digits>represents the port used by the trojan to connect to its command and control (C2) server. - STRRAT downloads a
system-hookJar file and uses this file to record the keystrokes of the victim endpoint. This Jar file is located in theC:\Users\<USER_NAME>\lib\folder. - STRRAT downloads
sqlite-jdbcandjna-platformJar files into theC:\Users\<USER_NAME>\lib\folder. The trojan uses these files to perform malicious activities on the victim endpoint. - STRRAT maintains persistence by using the task scheduler to create a Windows scheduled task called
Skype. This scheduled task runs the malware every 30 minutes. - STRRAT attempts to connect to a C2 server to exfiltrate data. It creates a
C:\Users\<USER_NAME>\AppData\Roaming\strlogsfolder before attempting to connect to its C2 server.
Infrastructure
To demonstrate the detection of STRRAT with Wazuh, we use the following infrastructure:
1. A pre-built ready-to-use Wazuh OVA 4.3.10. Follow this guide to download the virtual machine.
2. A Windows 10 victim endpoint with Java and Wazuh agent 4.3.10 installed. To install the Wazuh agent, refer to the following guide.
Detection with Wazuh
STRRAT is delivered in stages and uses obfuscation to evade detection on a victim endpoint. In this blog post, we use the following techniques to detect the presence of STRRAT:
- File integrity monitoring: To detect files created, modified, and downloaded by STRRAT.
- Command monitoring: To detect a scheduled task created by STRRAT.
File integrity monitoring
Wazuh uses its File Integrity Monitoring (FIM) module to detect and trigger alerts when files are created, modified, or deleted on monitored folders.
Follow the steps below to detect the presence of STRRAT on the victim endpoint.
Victim endpoint
Perform the following steps to configure FIM on the monitored endpoint.
1. Edit the Wazuh agent C:\Program Files (x86)\ossec-agent\ossec.conf file and include the following configuration within the <syscheck> block:
<!-- This configuration monitors the malicious activities of STRRAT on the victim endpoint--> <directories realtime="yes" recursion_level="2">C:\Users</directories>
2. Launch Powershell with administrative privilege and restart the Wazuh agent for the changes to take effect:
> Restart-Service -Name wazuh
Wazuh server
Perform the following steps to configure detection rules on the Wazuh server.
1. Edit the /var/ossec/etc/rules/local_rules.xml file on the Wazuh server and include the following rules:
<group name="syscheck,strrat_detection_rule,">
<!-- STRRAT downloads a system-hook Java file for recording keystrokes -->
<rule id="100050" level="12">
<if_sid>554</if_sid>
<field name="file" type="pcre2">(?i)^c:\\users.+lib\\system-hook.+jar$</field>
<description>Possible STRRAT malware detected. $(file) was downloaded on the endpoint</description>
<mitre>
<id>T1056.001</id>
</mitre>
</rule>
<!-- STRRAT poses as ransomware -->
<rule id="100051" level="8">
<if_sid>550,554</if_sid>
<field name="file" type="pcre2">(?i)c:\\users.+(documents|desktop|downloads).+crimson</field>
<description>Possible STRRAT malware detected. The .crimson extension has been appended to $(file)</description>
<mitre>
<id>T1486</id>
</mitre>
</rule>
<!-- STRRAT creates a lock file -->
<rule id="100052" level="12">
<if_sid>554</if_sid>
<field name="file" type="pcre2">(?i)^c:\\users.+\\\d{1,}lock\.file$</field>
<description>Possible STRRAT malware detected. $(file) was created on the endpoint</description>
</rule>
<!-- STRRAT downloads Java files -->
<rule id="100053" level="12">
<if_sid>554</if_sid>
<field name="file" type="pcre2">(?i)^c:\\users.+lib\\(jna\-platform|sqlite).+jar$</field>
<description>Possible STRRAT malware detected. $(file) was downloaded on the endpoint</description>
<mitre>
<id>T1407</id>
</mitre>
</rule>
</group>
Where:
- Rule id
100050is triggered when the STRRAT malware downloads asystem-hookjar file. - Rule id
100051is triggered when.crimsonextension is appended to files inDocuments,DesktoporDownloadsfolder. - Rule id
100052is triggered when STRRAT creates a<digits>lock.filefile inC:\Users\<USER_NAME>\folder. - Rule id
100053is triggered when STRRAT downloads ajna-platformorsqlite-jdbcjar file.
2. Restart the Wazuh manager for the changes to take effect:
# systemctl restart wazuh-manager
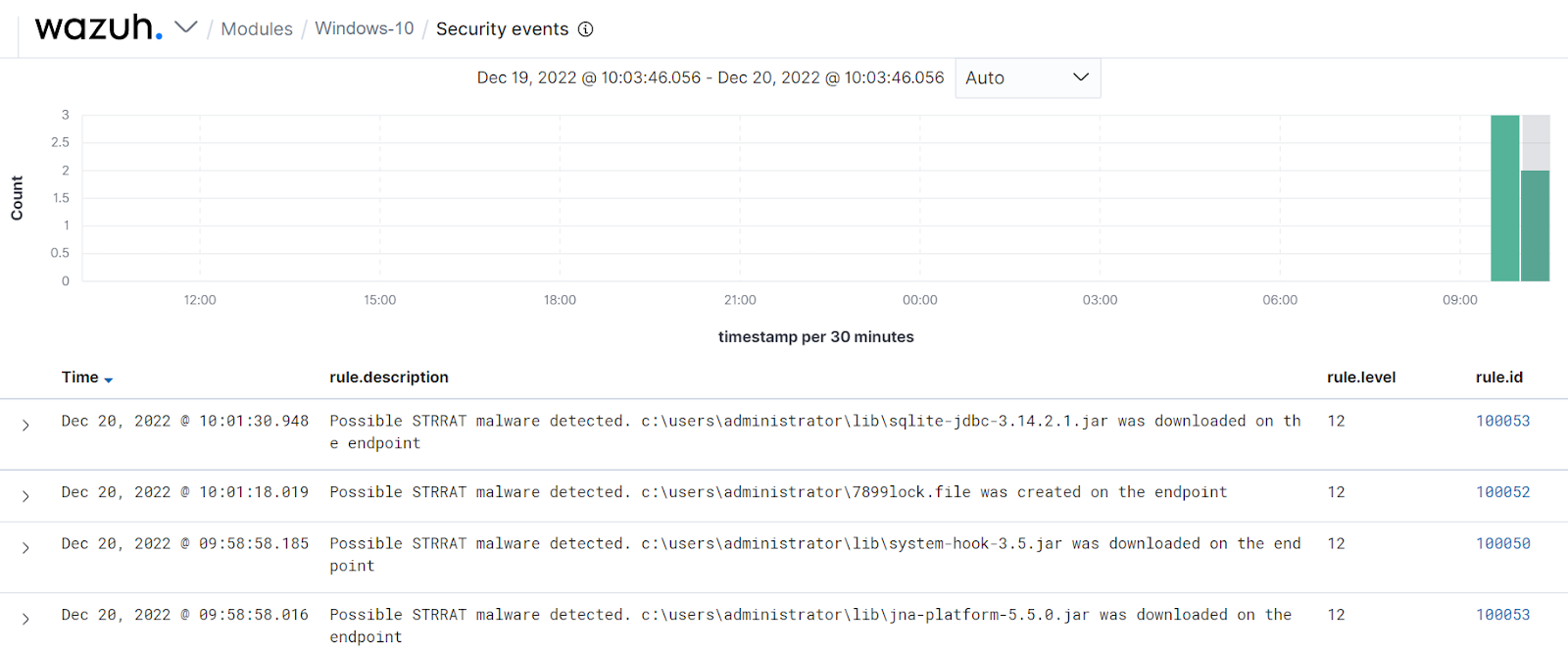
The alerts below are generated on the Wazuh dashboard when STRRAT is run on the victim endpoint.
Command monitoring
Wazuh has a command monitoring module to run commands and monitor the output of these commands on monitored endpoints. We use the command monitoring module to detect a Windows-scheduled task called Skype, created by STRRAT.
Victim endpoint
Perform the steps below to configure the Wazuh agent to monitor the scheduled task created by STRRAT on the victim endpoint.
1. Edit the C:\Program Files (x86)\ossec-agent\ossec.conf file and include the following configuration within the <ossec_config> block:
<localfile> <log_format>full_command</log_format> <command>schtasks /query /nh | findstr /c:"Skype"</command> <alias>finding_skype</alias> <frequency>300</frequency> </localfile>
Note
The above command runs every 300 seconds, and this is defined by the <frequency> tag.
2. Launch Powershell with administrative privilege and restart the Wazuh agent for the changes to take effect:
> Restart-Service -Name wazuh
Wazuh server
Perform the steps below to configure the Wazuh server to detect the scheduled task created by STRRAT on the victim endpoint.
1. Edit the /var/ossec/etc/rules/local_rules.xml file on the Wazuh server and include the following rules:
<group name="syscheck,strrat_detection_rule,">
<!-- STRRAT creates a scheduled task called Skype -->
<rule id="100054" level="0">
<if_sid>530</if_sid>
<match>^ossec: output: 'finding_skype'</match>
<description>A scheduled task called Skype is created</description>
</rule>
<!-- STRRAT maintains persistence -->
<rule id="100055" level="12" ignore="720">
<if_sid>100054</if_sid>
<match type="pcre2">(?i)Skype.+running</match>
<description>Possible STRRAT malware detected. Malware has achieved persistence</description>
<mitre>
<id>T1547.001</id>
</mitre>
</rule>
</group>
Where:
- Rule id
100054is triggered when a scheduled task namedSkypeis created. - Rule id
100055is triggered when a scheduled task namedSkypeis in a running state.
2. Restart the Wazuh manager for the changes to take effect:
# systemctl restart wazuh-manager
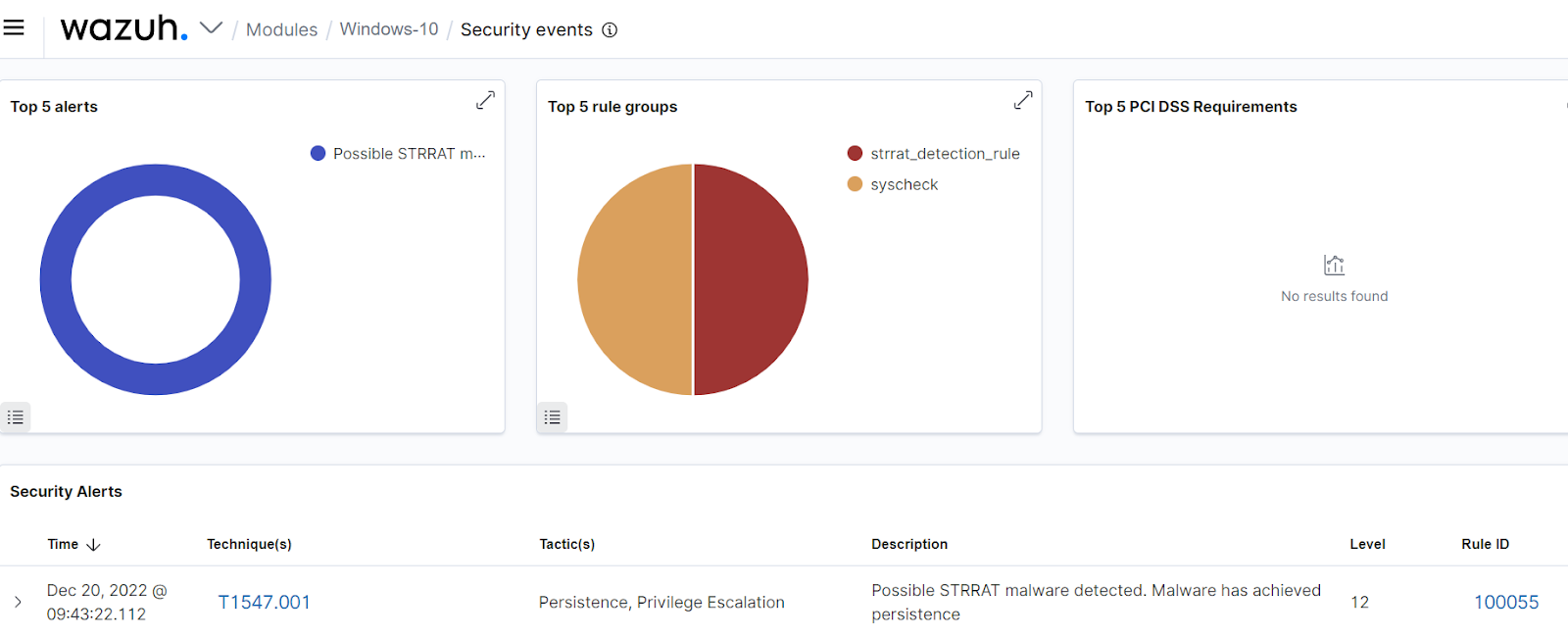
The alert below is generated on the Wazuh dashboard when STRRAT malware is run on the victim endpoint.
Note
The below alert takes approximately 30 minutes before it is generated on the Wazuh dashboard.
Conclusion
In this blog post, we have successfully used Wazuh to detect the behavior of STRRAT malware. Specifically, we used file integrity monitoring and command monitoring techniques to detect STRRAT malware on a Windows 10 endpoint.
Wazuh is a free and open source enterprise-ready security solution for threat detection and response. Wazuh integrates seamlessly with third-party solutions and technologies. Wazuh also has an ever growing community where users are supported. To learn more about Wazuh, please check out our documentation and blog posts.
