Remcos was originally produced in 2016 as a legitimate software by BreakingSecurity for managing Windows systems remotely. Remcos has been classified as a remote access trojan (RAT) because threat actors widely use it to perform malicious campaigns.
Remcos is usually delivered by phishing emails, and it allows attackers to secretly take full control of infected endpoints. This malware keeps receiving updates and is being actively maintained, with new releases coming out almost every month.
In this blog post, we use Wazuh to detect the malicious activities of Remcos.
Remcos RAT provides the following capabilities:
- Records keystrokes on the victim endpoint.
- Collects basic information like computer name, OS version, and system uptime on the victim endpoint.
- Captures screenshots of the victim endpoint.
- Data exfiltration from the victim endpoint to a C2 server.
Remcos RAT behavior
Remcos targets all versions of the Windows operating system, and it has the following behaviors:
- Remcos RAT adds a registry sub-key
Remcos-{alphanumeric}orhpsupport-{alphanumeric}to theHKEY_CURRENT_USER\SOFTWAREfolder. - Remcos RAT drops files in the
C:\Users\<USER_NAME>\AppData\Local\Tempfolder. - Remcos RAT creates a
logs.datfile for recording the keystrokes of the victim endpoint. The log file is located in theC:\Users\<USER_NAME>\AppData\Roaming\remcosorC:\Users\<USER_NAME>\AppData\Roaming\hpsupportfolder. As shown below, the keystrokePassword12345$has been recorded in thelogs.datfile:
[ logs.dat - Notepad ] [ *password.txt - Notepad ] Password12345$ [ remcos ]
- Remcos RAT tries to connect to a command and control (C2) server in order to exfiltrate data:
Active Connections Proto Local Address Foreign Address State TCP 192.168.0.80:52170 xx.xx.xx.xx:2404 SYN_SENT
Infrastructure
To demonstrate the detection of Remcos RAT with Wazuh, we use the following infrastructure:
1. A pre-built ready-to-use Wazuh OVA 4.3.9. Follow this guide to download the virtual machine.
2. A Windows 10 victim endpoint that has the Wazuh agent installed. To install the Wazuh agent, refer to the following guide.
Detection with Wazuh
In this blog post, we use the Sysmon and YARA integration with Wazuh to detect Remcos behavior on the victim endpoint.
Using detection rules
Remcos is delivered in stages and it uses different obfuscation techniques to evade detection on the victim endpoint. We use Sysmon to monitor several system events and create rules on the Wazuh server to detect the presence of Remcos RAT.
Follow the steps below to detect the activities of Remcos RAT with Wazuh:
Victim endpoint
Take the following steps to install Sysmon on the victim endpoint and configure the Wazuh agent to collect Sysmon logs.
1. Download Sysmon and the configuration file sysmonconfig.xml.
2. Edit the sysmonconfig.xml file and include the below configuration within the <EventFiltering> block:
<!-- This configuration records the malicious activities of Remcos RAT in Microsoft event viewer -->
<RuleGroup groupRelation="or">
<RegistryEvent onmatch="include">
<Rule groupRelation="and">
<EventType condition="is">CreateKey</EventType>
<TargetObject condition="begin with">HKU</TargetObject>
<TargetObject condition="contains any">Remcos;hpsupport</TargetObject>
</Rule>
</RegistryEvent>
</RuleGroup>
<RuleGroup groupRelation="or">
<FileCreate onmatch="include">
<TargetFilename condition="contains">\AppData\Roaming\</TargetFilename>
<TargetFilename condition="contains">\AppData\Local\</TargetFilename>
</FileCreate>
</RuleGroup>
3. Launch PowerShell with administrator privileges and install Sysmon with the edited sysmonconfig.xml file as follows:
Sysmon64.exe -accepteula -i sysmonconfig.xml
4. Edit the file C:\Program Files (x86)\ossec-agent\ossec.conf and include the following settings within the <ossec_config> block:
<!-- Configure Wazuh agent to receive events from Sysmon --> <localfile> <location>Microsoft-Windows-Sysmon/Operational</location> <log_format>eventchannel</log_format> </localfile>
5. Restart the Wazuh agent using PowerShell with administrator privileges for the changes to take effect:
Restart-Service -Name wazuh
Wazuh server
Take the following steps to configure detection rules on the Wazuh server.
1. Edit the /var/ossec/etc/rules/local_rules.xml file on the Wazuh server and include the following rules:
<group name="windows,sysmon,">
<!-- Remcos RAT drops a file -->
<rule id="100030" level="12">
<if_sid>92204</if_sid>
<match type="pcre2">(eqvkptgalnkxk7m.dll|install.vbs)</match>
<description>Possible Remcos RAT detected. File dropped on $(win.system.computer).</description>
<mitre>
<id>T1059</id>
</mitre>
</rule>
<!-- Remcos RAT creates a registry key -->
<rule id="100032" level="10">
<if_sid>61614</if_sid>
<match type="pcre2">(?i)(Remcos|hpsupport)-[a-zA-Z0-9]*</match>
<field name="win.eventdata.eventType" type="pcre2">^CreateKey$</field>
<description>Possible Remcos RAT detected. Registry key created on $(win.system.computer).</description>
<mitre>
<id>T1112</id>
</mitre>
</rule>
<!-- Remcos RAT capturing keystrokes -->
<rule id="100034" level="12" >
<if_sid>61613</if_sid>
<field name="win.eventdata.targetFilename" type="pcre2">(?i)\\AppData\\Roaming.+logs.dat</field>
<description>Possible Remcos RAT detected. Keystrokes are being captured on $(win.system.computer).</description>
<mitre>
<id>T1056.001</id>
</mitre>
</rule>
</group>
Where:
- Rule id
100030is triggered when a fileeqvkptgalnkxk7m.dllorinstall.vbsis dropped in theC:\Users\<USER_NAME>\Appdata\Local\Tempfolder. - Rule id
100032is triggered when a sub registry keyRemcos-{alphanumeric}orhpsupport-{alphanumeric}is created inHKEY_CURRENT_USER\SOFTWAREfolder. - Rule id
100034is triggered when alogs.datfile is created inC:\Users\<USER_NAME>\AppData\Roaming\remcosorC:\Users\<USER_NAME>\AppData\Roaming\hpsupportfolder.
2. Restart the Wazuh manager for the changes to take effect:
sudo systemctl restart wazuh-manager
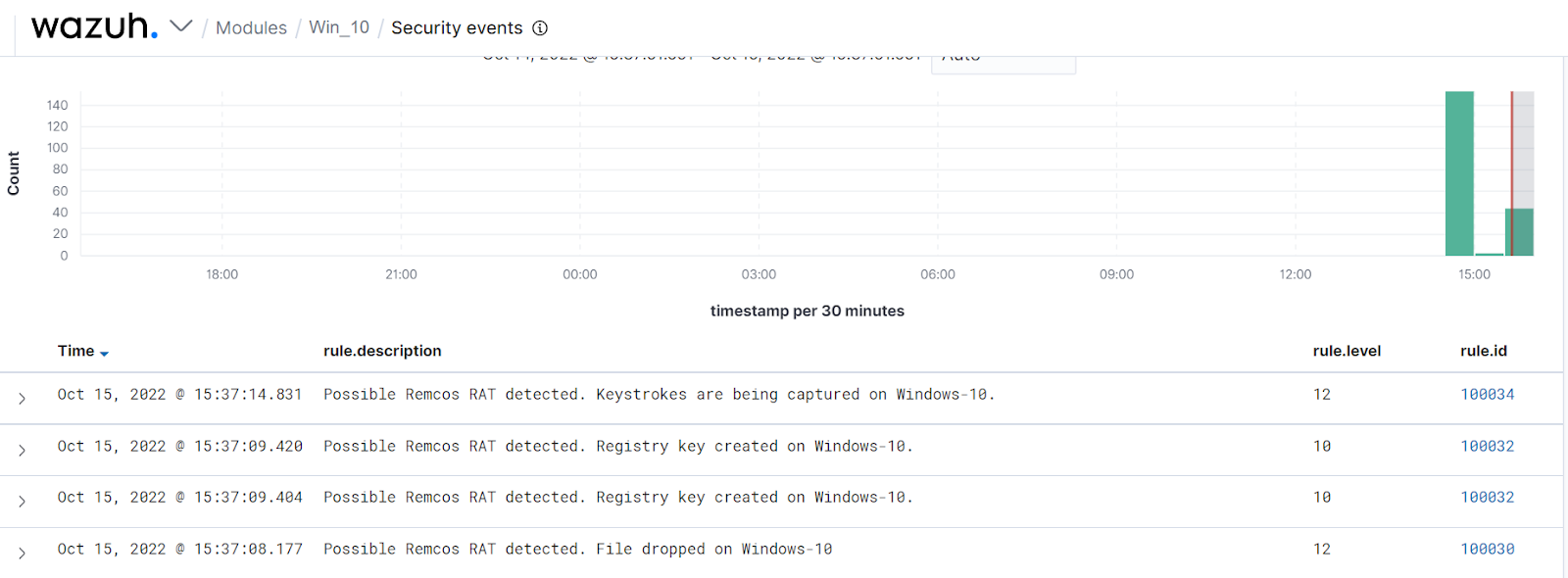
The alerts below are generated on the Wazuh dashboard when the Remcos RAT is run on the victim endpoint.
YARA integration
YARA is a versatile open source and multi-platform tool that identifies and classifies malware samples based on their textual or binary patterns. In this blog post, we use the Wazuh active response module to automatically execute a YARA scan on files added or modified in the Downloads folder.
Victim endpoint
Install the following packages on the victim endpoint. These are required to download and install YARA.
1. Python v 3.8.7 or later (with pip pre-installed).
2. Microsoft Visual C++ 2015 Redistributable.
After installing the above packages, follow the steps below to download the YARA executable:
1. Launch PowerShell with administrator privileges and download YARA:
Invoke-WebRequest -Uri https://github.com/VirusTotal/yara/releases/download/v4.2.3/yara-4.2.3-2029-win64.zip -OutFile v4.2.3-2029-win64.zip
2. Extract the YARA executable:
Expand-Archive v4.2.3-2029-win64.zip
3. Create a folder called C:\Program Files (x86)\ossec-agent\active-response\bin\yara\ and copy the YARA binary into it:
mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\' cp .\v4.2.3-2029-win64\yara64.exe 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\'
Follow the steps below to download YARA rules:
1. Using the same PowerShell terminal launched earlier, install valhallaAPI using the pip utility:
pip install valhallaAPI
2. Create the file download_yara_rules.py, and copy the following script into it:
from valhallaAPI.valhalla import ValhallaAPI
v = ValhallaAPI(api_key="1111111111111111111111111111111111111111111111111111111111111111")
response = v.get_rules_text()
with open('yara_rules.yar', 'w') as fh:
fh.write(response)
3. Download YARA rules and copy them to the C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\ folder:
python download_yara_rules.py mkdir 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\' cp yara_rules.yar 'C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\'
4. Edit the C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yar file and add the following Remcos RAT YARA rules:
rule Remcos_RAT
{
meta:
Author = "Benjamin Nworah"
Description = "Detect Remcos RAT"
Reference = "Personal Research"
Date = "27-09-2022"
Hash1 = "bcca157ab3520b1104411e86ea78f6a2efbb58ef"
Hash2 = "8d3c6c8e83275a60401a152797e7b158ea808413"
strings:
$a1 = "Olympianize3.exe" wide nocase
$a2 = "target_pid" ascii
$a3 = "VS_VERSION_INFO" wide
$a4 = {45 56 45 4E 54 5F 53 49 4E 4B 5F 41 64 64 52 65 66 00 15 00 45 56 45 4E 54 5F 53
49 4E 4B 5F 52 65 6C 65 61 73 65 00 00 14 00 45 56 45 4E 54 5F 53 49 4E 4B 5F 51
75 65 72 79 49 6E 74 65 72 66 61 63 65 00 8E 00 5F 5F 76 62 61 45 78 63 65 70 74
48 61 6E 64 6C 65 72}
$a5 = "C:\Program Files (x86)\Microsoft Visual Studio\VB98\VB6.OLB"
$b1 = "Software\Microsoft\Windows\CurrentVersion"
$b2 = "SearchPath"
$b3 = "RegCreateKeyEx"
$b4 = "WritePrivateProfileString"
$b5 = "MoveFile"
$b6 = "CreateFile"
$b7 = "GetTempFileName"
$b8 = "LookupPrivilegeValue"
$b9 = {52 65 67 44 65 6C 65 74 65 4B 65 79 45 78}
condition:
all of ($a*) or all of ($b*)
}
rule REMCOS_RAT_variants
{
meta:
Author = "Adam M. Swanda"
Website = "https://www.deadbits.org"
Repo = "https://github.com/deadbits/yara-rules"
Date = "2019-07-18"
Description = "Detects multiple variants of REMCOS seen in the wild."
strings:
$funcs1 = "autogetofflinelogs" ascii fullword
$funcs2 = "clearlogins" ascii fullword
$funcs3 = "getofflinelogs" ascii fullword
$funcs4 = "execcom" ascii fullword
$funcs5 = "deletekeylog" ascii fullword
$funcs6 = "remscriptexecd" ascii fullword
$funcs7 = "getwindows" ascii fullword
$funcs8 = "fundlldata" ascii fullword
$funcs9 = "getfunlib" ascii fullword
$funcs10 = "autofflinelogs" ascii fullword
$funcs11 = "getclipboard" ascii fullword
$funcs12 = "getscrslist" ascii fullword
$funcs13 = "offlinelogs" ascii fullword
$funcs14 = "getcamsingleframe" ascii fullword
$funcs15 = "listfiles" ascii fullword
$funcs16 = "getproclist" ascii fullword
$funcs17 = "onlinelogs" ascii fullword
$funcs18 = "getdrives" ascii fullword
$funcs19 = "remscriptsuccess" ascii fullword
$funcs20 = "getcamframe" ascii fullword
$str_a1 = "C:\Windows\System32\cmd.exe" ascii fullword
$str_a2 = "C:\WINDOWS\system32\userinit.exe" ascii fullword
$str_a3 = "/k %windir%\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWOR" ascii
$str_a4 = "/k %windir%\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWOR" ascii
$str_a5 = "\AppData\Local\Google\Chrome\User Data\Default\Login Data" ascii fullword
$str_b1 = "CreateObject(\"Scripting.FileSystemObject\").DeleteFile(Wscript.ScriptFullName)" wide fullword
$str_b2 = "Executing file: " ascii fullword
$str_b3 = "GetDirectListeningPort" ascii fullword
$str_b4 = "Set fso = CreateObject(\"Scripting.FileSystemObject\")" wide fullword
$str_b5 = "licence_code.txt" ascii fullword
$str_b6 = "\restart.vbs" wide fullword
$str_b7 = "\update.vbs" wide fullword
$str_b8 = "\uninstall.vbs" wide fullword
$str_b9 = "Downloaded file: " ascii fullword
$str_b10 = "Downloading file: " ascii fullword
$str_b11 = "KeepAlive Enabled! Timeout: %i seconds" ascii fullword
$str_b12 = "Failed to upload file: " ascii fullword
$str_b13 = "StartForward" ascii fullword
$str_b14 = "StopForward" ascii fullword
$str_b15 = "fso.DeleteFile \"" wide fullword
$str_b16 = "On Error Resume Next" wide fullword
$str_b17 = "fso.DeleteFolder \"" wide fullword
$str_b18 = "Uploaded file: " ascii fullword
$str_b19 = "Unable to delete: " ascii fullword
$str_b20 = "while fso.FileExists(\"" wide fullword
$str_c0 = "[Firefox StoredLogins not found]" ascii fullword
$str_c1 = "Software\Classes\mscfile\shell\open\command" ascii fullword
$str_c2 = "[Chrome StoredLogins found, cleared!]" ascii fullword
$str_c3 = "[Chrome StoredLogins not found]" ascii fullword
$str_c4 = "[Firefox StoredLogins cleared!]" ascii fullword
$str_c5 = "Remcos_Mutex_Inj" ascii fullword
$str_c6 = "\logins.json" ascii fullword
$str_c7 = "[Chrome Cookies found, cleared!]" ascii fullword
$str_c8 = "[Firefox Cookies not found]" ascii fullword
$str_c9 = "[Chrome Cookies not found]" ascii fullword
$str_c10 = "[Firefox cookies found, cleared!]" ascii fullword
$str_c11 = "mscfile\shell\open\command" ascii fullword
$str_c12 = "\AppData\Roaming\Mozilla\Firefox\Profiles\" ascii fullword
$str_c13 = "eventvwr.exe" ascii fullword
condition:
uint16(0) == 0x5a4d and filesize < 600KB
and
(
((8 of ($funcs*)) or all of ($funcs*))
or
((1 of ($str_a*) and 4 of them) or all of ($str_a*))
or
((8 of ($str_b*)) or all of ($str_b*))
or
all of ($str_c*)
)
}
5. Edit the C:\Program Files (x86)\ossec-agent\ossec.conf file and add the below configuration within the <syscheck> block to monitor the Downloads folders of all users in real-time:
<directories realtime="yes">C:\Users\*\Downloads</directories>
Note
In this blog post, the Downloads folders of all users are monitored. However, you can configure other folders you wish to monitor.
6. Create a batch file yara.bat in the C:\Program Files (x86)\ossec-agent\active-response\bin\ folder. The active response module uses this file to perform YARA scans for malware detection and removal:
:: This script deletes Remcos RAT as well as other malicious files matched by the YARA Rules @echo off setlocal enableDelayedExpansion reg Query "HKLM\Hardware\Description\System\CentralProcessorRestart-Service -Name wazuh" | find /i "x86" > NUL && SET OS=32BIT || SET OS=64BIT if %OS%==32BIT ( SET log_file_path="%programfiles%\ossec-agent\active-response\active-responses.log" ) if %OS%==64BIT ( SET log_file_path="%programfiles(x86)%\ossec-agent\active-response\active-responses.log" ) set input= for /f "delims=" %%a in ('PowerShell -command "$logInput = Read-Host; Write-Output $logInput"') do ( set input=%%a ) set json_file_path="C:\Program Files (x86)\ossec-agent\active-response\stdin.txt" set syscheck_file_path= echo %input% > %json_file_path% FOR /F "tokens=* USEBACKQ" %%F IN (`Powershell -Nop -C "(Get-Content 'C:\Program Files (x86)\ossec-agent\active-response\stdin.txt'|ConvertFrom-Json).parameters.alert.syscheck.path"`) DO ( SET syscheck_file_path=%%F ) set yara_exe_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\yara64.exe" set yara_rules_path="C:\Program Files (x86)\ossec-agent\active-response\bin\yara\rules\yara_rules.yar" echo %syscheck_file_path% >> %log_file_path% for /f "delims=" %%a in ('powershell -command "& \"%yara_exe_path%\" \"%yara_rules_path%\" \"%syscheck_file_path%\""') do ( echo wazuh-yara: INFO - Scan result: %%a >> %log_file_path% :: Deleting the scanned file. del /f "%syscheck_file_path%" echo wazuh-yara: INFO - Successfully deleted: %%a >> %log_file_path% ) exit /b
7. Restart the Wazuh agent using PowerShell for the changes to take effect:
<!-- The decoders are used to parse logs from the YARA scans -->
<decoder name="yara_decoder">
<prematch>wazuh-yara:</prematch>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Scan result: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
<decoder name="yara_decoder1">
<parent>yara_decoder</parent>
<regex>wazuh-yara: (\S+) - Successfully deleted: (\S+) (\S+)</regex>
<order>log_type, yara_rule, yara_scanned_file</order>
</decoder>
Wazuh server
Take the following steps to configure custom decoders, rules, and active response on the Wazuh server.
1. Edit the /var/ossec/etc/decoders/local_decoder.xml file on the Wazuh server and include the following decoders:
<!-- File added to the Downloads folder -->
<group name= "syscheck,">
<rule id="100028" level="7">
<if_sid>550</if_sid>
<field name="file" type="pcre2">(?i)C:\Users.+Downloads</field>
<description>File modified in the Downloads folder.</description>
</rule>
<!-- File modified in the Downloads folder -->
<rule id="100029" level="7">
<if_sid>554</if_sid>
<field name="file" type="pcre2">(?i)C:\Users.+Downloads</field>
<description>File added to the Downloads folder.</description>
</rule>
</group>
<!-- Rule for the decoder (yara_decoder) -->
<group name="yara,">
<rule id="100037" level="0">
<decoded_as>yara_decoder</decoded_as>
<description>Yara grouping rule</description>
</rule>
<!-- YARA scan detects a positive match -->
<rule id="100038" level="12">
<if_sid>100037</if_sid>
<match type="pcre2">wazuh-yara: INFO - Scan result: </match>
<description>File "$(yara_scanned_file)" is a positive match. Yara rule: $(yara_rule)</description>
</rule>
<rule id="100039" level="12">
<if_sid>100037</if_sid>
<match type="pcre2">wazuh-yara: INFO - Successfully deleted: </match>
<description>Successfully removed "$(yara_scanned_file)". YARA rule: $(yara_rule)</description>
</rule>
</group>
2. Edit the /var/ossec/etc/rules/local_rules.xml file on the Wazuh server and include the following rules:
<!-- The YARA batch script is executed when a file is added or modified in the Downloads folder monitored by the Wazuh FIM --> <command> <name>yara</name> <executable>yara.bat</executable> <timeout_allowed>no</timeout_allowed> </command> <active-response> <command>yara</command> <location>local</location> <rules_id>100028,100029</rules_id> </active-response>
3. Add the following configuration to the /var/ossec/etc/ossec.conf file within the <ossec_config> block:
sudo systemctl restart wazuh-manager
4. Restart the Wazuh manager for the changes to take effect:
sudo systemctl restart wazuh-manager
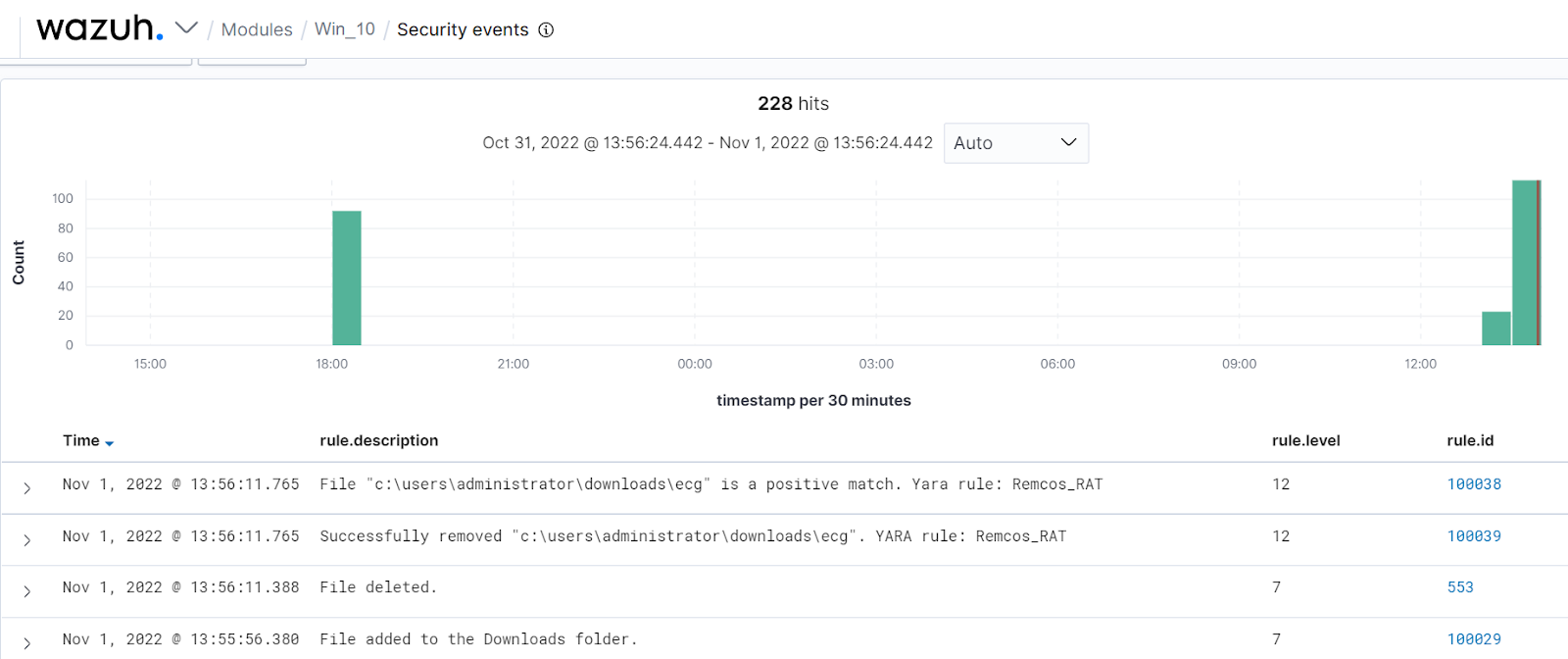
The Wazuh dashboard generates alerts when Remcos is downloaded to the Downloads folder of the victim endpoint.
Conclusion
In this blog post, we used Sysmon integration with Wazuh to detect the behavior of Remcos RAT. We also used YARA integration with Wazuh to detect and remove Remcos RAT once it was downloaded to the endpoint.
