Amazon Security Lake is a centralized security data lake designed to help organizations store, query, and analyze security-related data across multiple AWS and third-party sources. It allows users to aggregate data from various sources and use analytics to identify security threats, anomalies, and trends. Amazon Security Lake offers a scalable, secure, and cost-effective solution for security operations teams to improve their security posture and reduce the risk of security incidents. Security logs and events stored in this unified data lake can be ingested by third-party security monitoring solutions for further analysis.
Wazuh is a free, open source, enterprise-ready security monitoring platform for threat detection, integrity monitoring, incident response, and compliance. It provides protection for cloud, on-premises, containerized, and virtual environments. Wazuh gives users visibility across their infrastructure and provides comprehensive capabilities that detect and respond to security threats.
Wazuh can be integrated with Amazon Security Lake to provide a more comprehensive view of an organization’s security posture. Amazon Security Lake supports integration as a subscriber or as a source. Integrating Wazuh with Amazon Security Lake as a subscriber enables direct querying and analysis of security logs from multiple sources within Wazuh. Thus, it eliminates the need for manual data transfers or additional infrastructure. In the future, Wazuh will be integrated as a source of security data for Amazon Security Lake to provide rich security logs and event data for a deeper insight into an organization’s security posture.
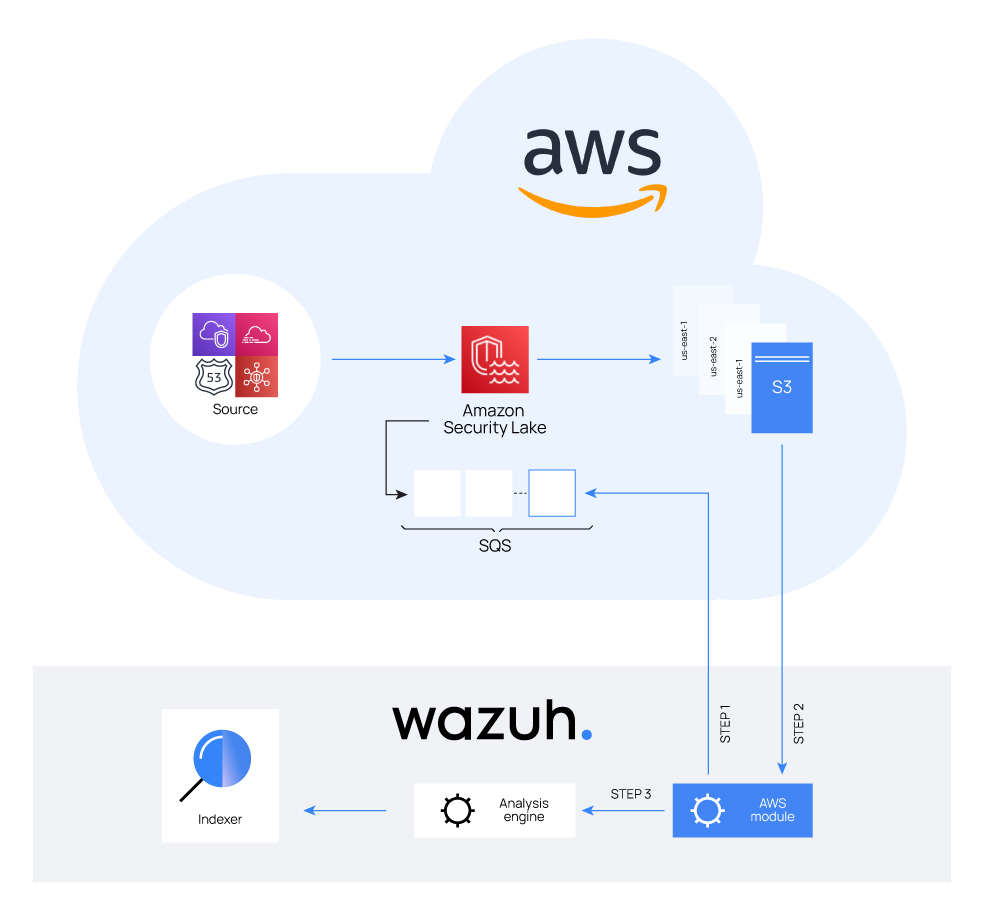
Wazuh is a unified XDR and SIEM platform that aggregates and analyzes security event logs from multiple sources. The Wazuh All-In-One Deployment based on an Amazon Machine Image is available in the AWS Marketplace. As a subscriber, Wazuh collects security event data that has been stored on Amazon Security Lake and analyzes them for real-time threat detection and response. Wazuh monitors activity logs and events from various sources such as CloudTrail, VPC Flow, Route53, and more, and provides pre-defined rules and alerts that help detect potential security threats in real-time. For instance, monitoring CloudTrail events provides an easy way to track, audit, and receive alerts on AWS API activity. This integration provides coverage for adversary activities like the ones described in the Adversary emulation on AWS with Stratus Red Team and Wazuh blog post. Such capabilities are important in today’s threat landscape, where threats can evolve rapidly.
Wazuh can be configured to autonomously respond to security-related events in an environment. For example, if a certain type of event is detected, Wazuh can automatically execute scripts to mitigate the threat. This can save time and improve incident response.
Furthermore, Wazuh offers high availability and scalability to manage large amounts of security-related data. This ensures that users can query and analyze logs without experiencing performance issues.
Conclusion
Wazuh is a free, open source, and enterprise-ready security monitoring platform. It offers SIEM and XDR capabilities to protect an organization’s digital assets. Wazuh has an ever-growing community and it is widely used by thousands of users. Also, it is worth adding that since May 2022 Wazuh uses the open source Amazon OpenSearch for its Wazuh Indexer and Wazuh Dashboard.
Integrating Wazuh with Amazon Security Lake provides many benefits, including data normalization with the Open Cyber Schema Framework (OCSF), real-time security monitoring, simplified querying and analysis, and automated response. With this integration, users can use the out-of-the-box capabilities of Wazuh to monitor and protect their workloads across different infrastructures. By leveraging Amazon Security Lake integration with Wazuh, users can extend the security visibility and protection of their infrastructure.
