Introduction
PsExec is a part of Sysinternals command line tools named PsTools. It facilitates system administration and can execute processes on local and remote systems. While PsExec is not malicious, several threat actors such as Turla, Fin6, and Cleaver use it for activities such as lateral movement and privilege escalation within a network; it is therefore important to detect its usage.
In this blog post, we examine PsExec usage on a Windows endpoint and we detect its activities using the Wazuh platform.
Setting up the lab
This section explains how the Windows endpoint and Wazuh manager are configured. Due to the nature of the activities being done, we recommend using disposable virtual machines for the Windows endpoint.
Wazuh server
The Wazuh server analyzes the data received from Wazuh agents and triggers alerts when threats or anomalies are detected. You can find the installation guide here.
Windows endpoint
We can install the Wazuh agent and configure Sysmon on a Windows endpoint by following the steps below:
- Install and enroll the Wazuh agent on the Windows endpoint. The agent will send the logs generated on the endpoint to the Wazuh server.
- Download Sysmon from the Microsoft Sysinternals page.
- Download the Sysmon configuration file sysmonconfig.xml.
- Install Sysmon with the downloaded configuration file using PowerShell (as administrator):
.\sysmon.exe -accepteula -i .\sysmonconfig.xml
- Configure the agent to capture Sysmon events by adding the following settings to the agent configuration file in “
C:\Program Files (x86)\ossec-agent\ossec.conf“:
<localfile> <location>Microsoft-Windows-Sysmon/Operational</location> <log_format>eventchannel</log_format> </localfile>
- To apply the changes, restart the agent by running the following PowerShell command as an administrator:
Restart-Service -Name wazuh
Detection with Wazuh
Out of the Box, Wazuh can detect when a new service is created on a Windows machine. To extend the detection capabilities to cover PsExec activities, we add the following rules to the /var/ossec/etc/rules/local_rules.xml file on the Wazuh manager.
<group name="windows,sysmon">
<rule id="160010" level="10">
<if_group>windows,sysmon</if_group>
<field name="win.eventdata.eventType" type="pcre2" >SetValue</field>
<field name="win.eventdata.targetObject" type="pcre2" >\\\\SOFTWARE\\\\Sysinternals\\\\PsExec\\\\EulaAccepted</field>
<options>no_full_log</options>
<description>PsExec EULA registry found on $(win.system.computer)</description>
<mitre>
<id>T1112</id>
</mitre>
</rule>
<rule id="160011" level="10">
<if_group>windows,sysmon</if_group>
<field name="win.eventdata.targetObject" type="pcre2" >HKLM\\\\System\\\\CurrentControlSet\\\\Services\\\\PSEXESVC</field>
<field name="win.eventdata.eventType" type="pcre2" >^SetValue$</field>
<field name="win.eventdata.user" type="pcre2" >NT AUTHORITY\\\\SYSTEM</field>
<options>no_full_log</options>
<description>PsExec service running as $(win.eventdata.user) has been created on $(win.system.computer)</description>
<mitre>
<id>T1543.003</id>
</mitre>
</rule>
<rule id="160012" level="10">
<if_group>windows,sysmon</if_group>
<field name="win.eventdata.targetObject" type="pcre2" >HKLM\\\\System\\\\CurrentControlSet\\\\Services\\\\PSEXESVC</field>
<field name="win.eventdata.eventType" type="pcre2" >^DeleteKey$</field>
<field name="win.eventdata.user" type="pcre2" >NT AUTHORITY\\\\SYSTEM</field>
<options>no_full_log</options>
<description>PsExec service running as $(win.eventdata.user) has been deleted on $(win.system.computer)</description>
<mitre>
<id>T1543.003</id>
</mitre>
</rule>
<rule id="160013" level="10">
<if_group>windows,sysmon</if_group>
<field name="win.eventdata.eventType" type="pcre2" >CreatePipe</field>
<field name="win.eventdata.image" type="pcre2" >\\\\PSEXESVC.exe</field>
<match type="pcre2">(?i)(PSEXESVC|stdin|stdout|stderr)</match>
<field name="win.eventdata.user" type="pcre2" >NT AUTHORITY\\\\SYSTEM</field>
<options>no_full_log</options>
<description>PsExec named pipe running as $(win.eventdata.user) has been found on $(win.system.computer)</description>
<mitre>
<id>T1570</id>
</mitre>
</rule>
</group>
We restart the Wazuh server so it starts using the new rules:
systemctl restart wazuh-manager
Privilege escalation with PsExec
Privilege escalation techniques allow an adversary to gain a higher privilege level on a system or network. Examples of elevated privileges include escalating a standard account to an administrator, or from a local administrator account to a local SYSTEM user. The SYSTEM account is the highest privilege level in the Windows user model, it is used by the operating system and services that run under Windows.
In this section, we use PsExec to escalate the Windows PowerShell privileges from administrator to SYSTEM, we also analyze the log generated by its execution.
PsExec execution
We download the PsTools archive from the Microsoft Sysinternals page and extract the PsExec binary from the archive. The following command escalates a Windows PowerShell process from an administrator user to a SYSTEM user:
./psexec -i -s powershell
We can confirm the new instance of PowerShell is now running as SYSTEM using the command below:
whoami
The result shows PowerShell is now running as a SYSTEM user:
PS C:\Windows\system32> whoami nt authority\system
Detected activity
This section describes the activity discovered on the Windows endpoint as a result of running PsExec.
License agreement key
The first time PsExec is executed on a system, it displays an End User License Agreement (EULA) prompt which the user needs to accept. This creates a registry key: HKCU\Software\Sysinternals\PsExec\EulaAccepted=0x01, which we can see in the logs of the Windows endpoint below.
Registry value set:
RuleName: technique_id=T1569.002,technique_name=Service Execution
EventType: SetValue
UtcTime: 2022-05-20 10:13:18.933
ProcessGuid: {5a1492c8-69bc-6287-9d01-000000000b00}
ProcessId: 5176
Image: C:\PSTools\PsExec.exe
TargetObject: HKU\S-1-5-21-239732096-1583447084-1784059003-1001\SOFTWARE\Sysinternals\PsExec\EulaAccepted
Details: DWORD (0x00000001)
User: WAZUH-LAB\Wazuh-Test
Service creation and deletion
A service named PSEXESVC is created each time PsExec is executed on a machine. It is also deleted once PsExec is exited. These events are logged on the Windows endpoint as seen below.
Registry value set:
RuleName: technique_id=T1543,technique_name=Service Creation
EventType: SetValue
UtcTime: 2022-05-20 10:13:19.028
ProcessGuid: {5a1492c8-602f-6287-0b00-000000000b00}
ProcessId: 656
Image: C:\Windows\system32\services.exe
TargetObject: HKLM\System\CurrentControlSet\Services\PSEXESVC\Type
Details: DWORD (0x00000010)
User: NT AUTHORITY\SYSTEM
Registry object added or deleted:
RuleName: technique_id=T1543,technique_name=Service Creation
EventType: DeleteKey
UtcTime: 2022-05-18 12:09:07.593
ProcessGuid: {5a1492c8-df91-6284-0b00-000000000a00}
ProcessId: 648
Image: C:\Windows\system32\services.exe
TargetObject: HKLM\System\CurrentControlSet\Services\PSEXESVC
User: NT AUTHORITY\SYSTEM
Use of named pipes
Named pipes provide communication between processes on the same computer or between processes on different computers within a network. Four named pipes are created when PsExec is running. One is created for the PSEXESVC service, while the other named pipes redirect the stdin, stdout, and stderr processes. Using the pipelist program, we can see the following pipes running on the Windows endpoint:
PSEXESVC PSEXESVC-WAZUH-LAB-6424-stdin PSEXESVC-WAZUH-LAB-6424-stdout PSEXESVC-WAZUH-LAB-6424-stderr
The logged activities for PSEXESVC named pipe are seen below:
Pipe Created:
RuleName: -
EventType: CreatePipe
UtcTime: 2022-05-20 10:13:19.215
ProcessGuid: {5a1492c8-69bf-6287-9e01-000000000b00}
ProcessId: 3992
PipeName: \PSEXESVC
Image: C:\Windows\PSEXESVC.exe
User: NT AUTHORITY\SYSTEM
Results
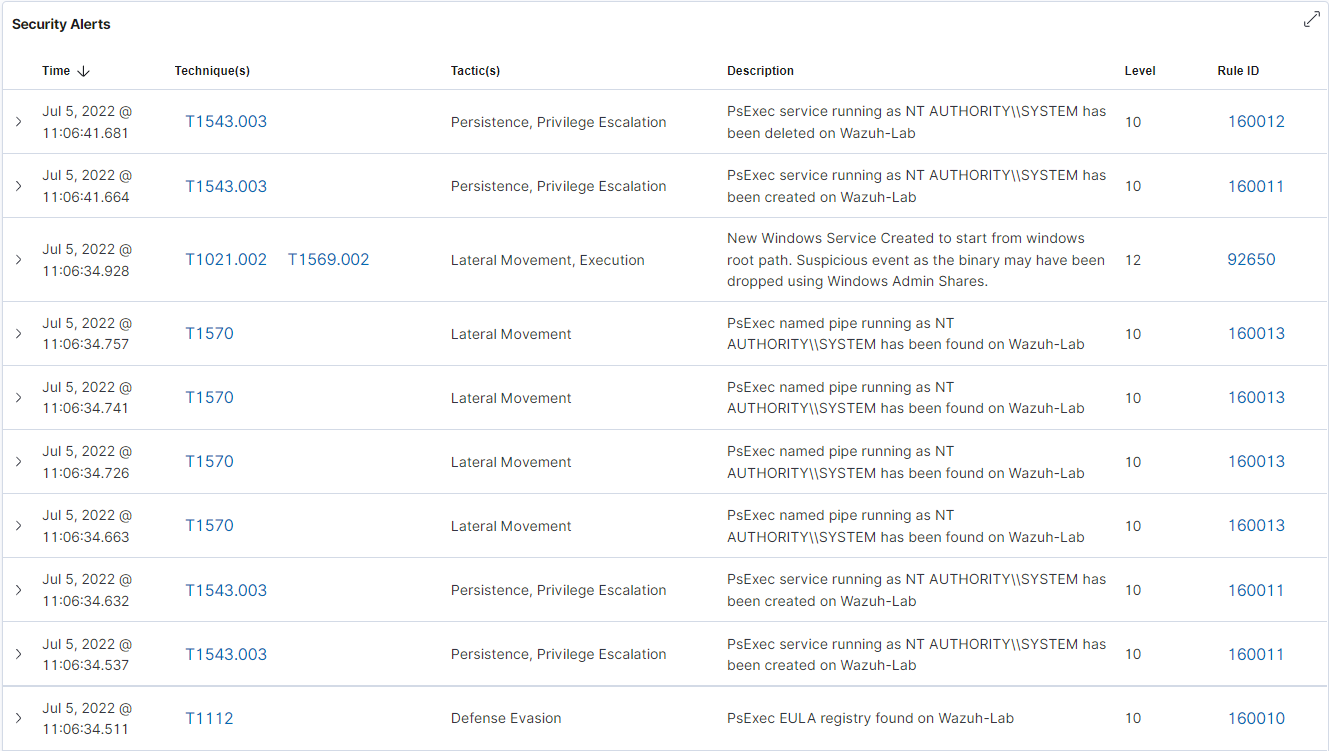
Several alerts were triggered on the Wazuh dashboard after PsExec had been executed on the Windows endpoint. The screenshot below shows that Wazuh has detected the usage of PsExec.
Conclusion
In this blog post, we have been able to detect the usage of PsExec on the Windows endpoint. PsExec service creation was detected out of the box by Wazuh, while other activities were detected on the Wazuh platform using custom Wazuh detection rules.
References
