A network device is a hardware or software component that facilitates the transfer of data and information between nodes within a network. Common types of network devices include routers, switches, hubs, modems, access points, and firewalls.
Without adequate safeguards, network devices become vulnerable entry points for malicious actors to gain unauthorized access to systems, orchestrate data breaches, or cause network disruptions. As such, safeguarding network devices through robust security measures, regular updates, and vigilant monitoring is imperative to maintaining the integrity and reliability of both local and global networks.
List of network devices Wazuh supports
Wazuh supports the following devices by providing out-of-the-box rules and decoders:
- Cisco PIX, ASA, and FWSM (all versions)
- Cisco IOS routers (all versions)
- Juniper Netscreen (all versions)
- SonicWall firewall (all versions)
- Checkpoint firewall (all versions)
- Cisco IOS IDS/IPS module (all versions)
- Sourcefire (Snort) IDS/IPS (all versions)
- Dragon NIDS (all versions)
- Checkpoint Smart Defense (all versions)
- Bluecoat proxy (all versions)
- Cisco VPN concentrators (all versions)
- VMWare ESXi 4.x
- Huawei USG
- pfSense
- Junos devices
This blog post provides a walkthrough on using Wazuh to monitor a MikroTik router.
Prerequisites
- A pre-built, ready-to-use Wazuh OVA 4.7.2. Follow the Virtual Machine (OVA) – Installation guide to download and set up the Wazuh virtual machine.
- An Ubuntu 22.04 endpoint with the Wazuh agent 4.7.2 installed.
- A MikroTik router with software version 7.13 stable.
Configuration
Ubuntu endpoint
Rsyslog is a preinstalled utility in Ubuntu 22.04 for receiving syslog events. The following section shows the steps for enabling Rsyslog on the Ubuntu endpoint and configuring the Wazuh agent to send the syslog log data to the Wazuh server.
1. Paste the following code snippet at the bottom of the /etc/rsyslog.conf file on the Ubuntu endpoint. This code enables the UDP port 514 to listen for syslogs and adds a location to store the security events:
$ModLoad imudp $UDPServerRun 514 #Storing Messages from a Remote System into a specific File if $fromhost-ip startswith '<YOUR_MIKROTIK_IP_ADDRESS>' then /var/log/mikrotik.log & ~
Replace <YOUR_MIKROTIK_IP_ADDRESS> with the IP address of the MikroTik device.
2. Create the mikrotik.log file in the /var/log directory to store the syslog events:
# touch /var/log/mikrotik.log
3. Change the file ownership for the /var/log/mikrotik.log file to syslog and group to adm:
# chown syslog:adm /var/log/mikrotik.log
4. Restart the rsyslog utility for the changes to take effect:
# systemctl restart rsyslog
5. Paste the following within the <ossec_config> block of the Wazuh agent /var/ossec/etc/ossec.conf configuration file.
<localfile> <log_format>syslog</log_format> <location>/var/log/mikrotik.log</location> <out_format>RouterOS7.1-logs: $(log)</out_format> </localfile>
6. Restart the Wazuh agent to apply the changes:
# systemctl restart wazuh-agent
MikroTik configuration
In this scenario, we configure the MikroTik router to send syslog messages remotely to the Wazuh agent using port 514. Perform the following configuration using the MikroTik Winbox tool on a Windows operating system or the WebUI using the MikroTik device IP address.
1. Log in to your router using the Winbox utility or WebUI.
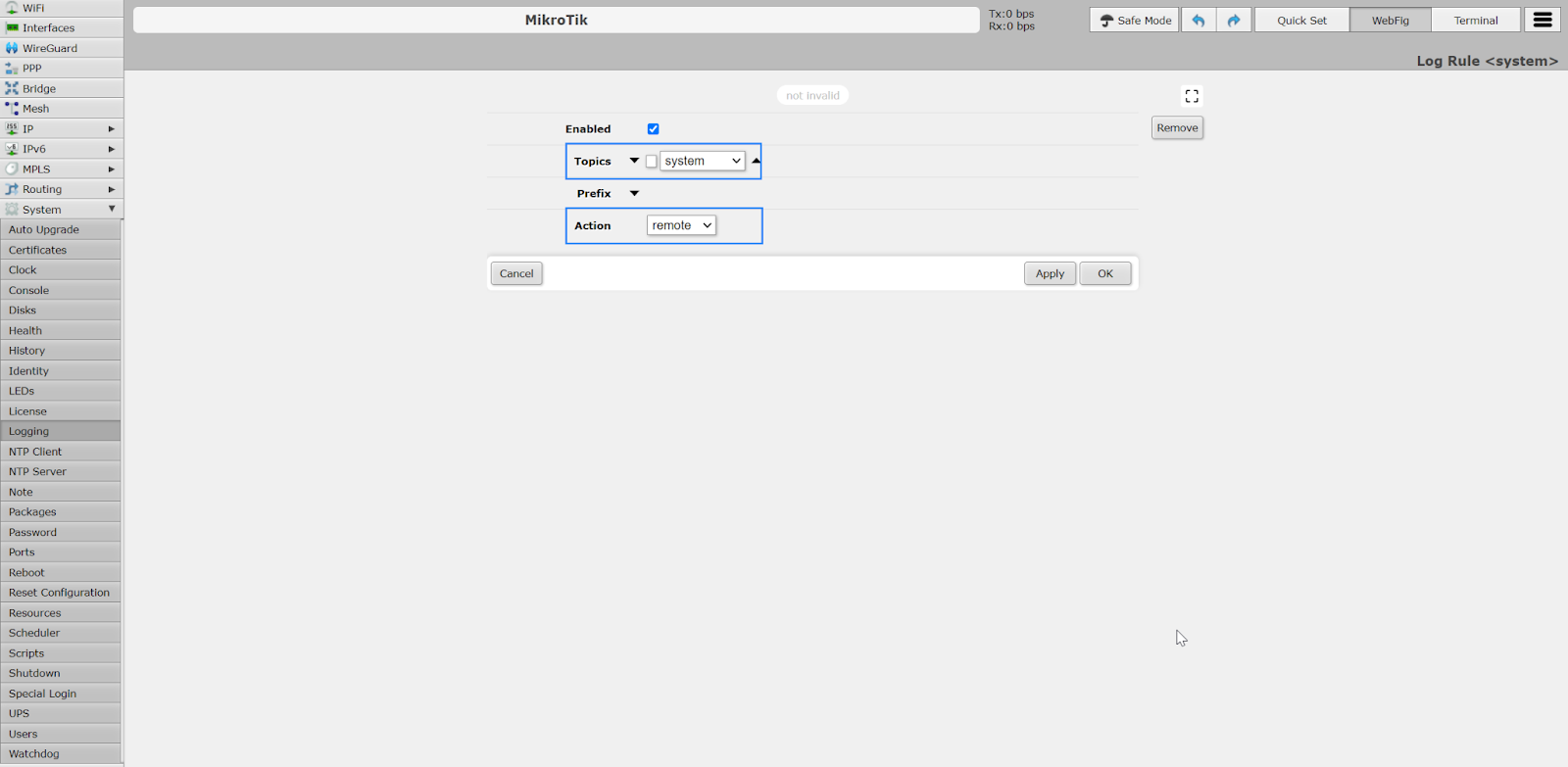
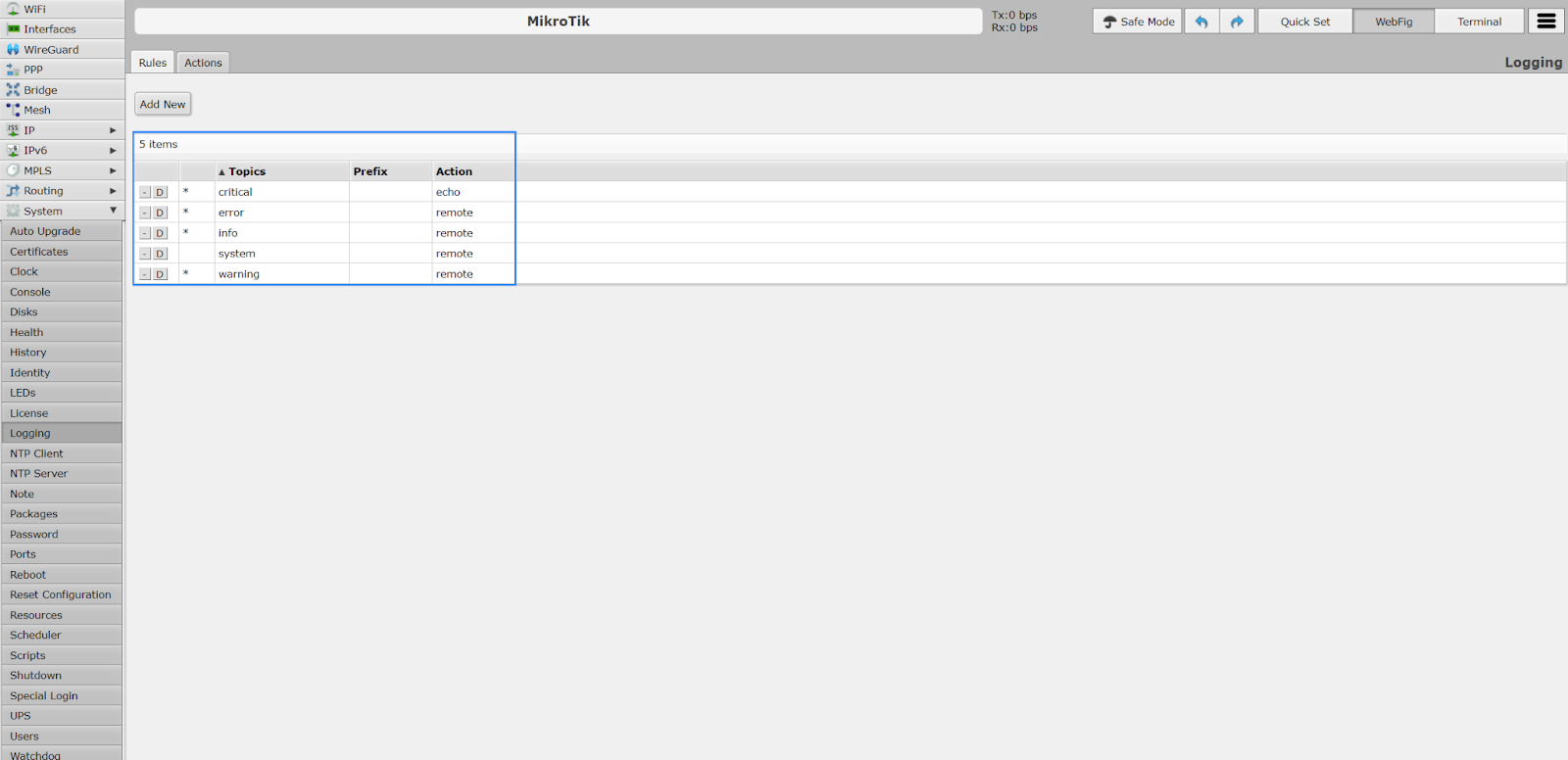
2. Click on the System > Logging > Actions tab and add a new rule where Topics is set to system and Action is set to remote. Click on Apply to save the above rule.
3. Click on the System > Logging > Actions tab and create new or modify the existing rules where the topic’s error, info, and warning are set to remote.
4. Click the System > Logging > Actions tab to edit the remote action. Set the Remote address field to the IP address of the Wazuh agent and the Remote port field to the Rsyslog listening port.
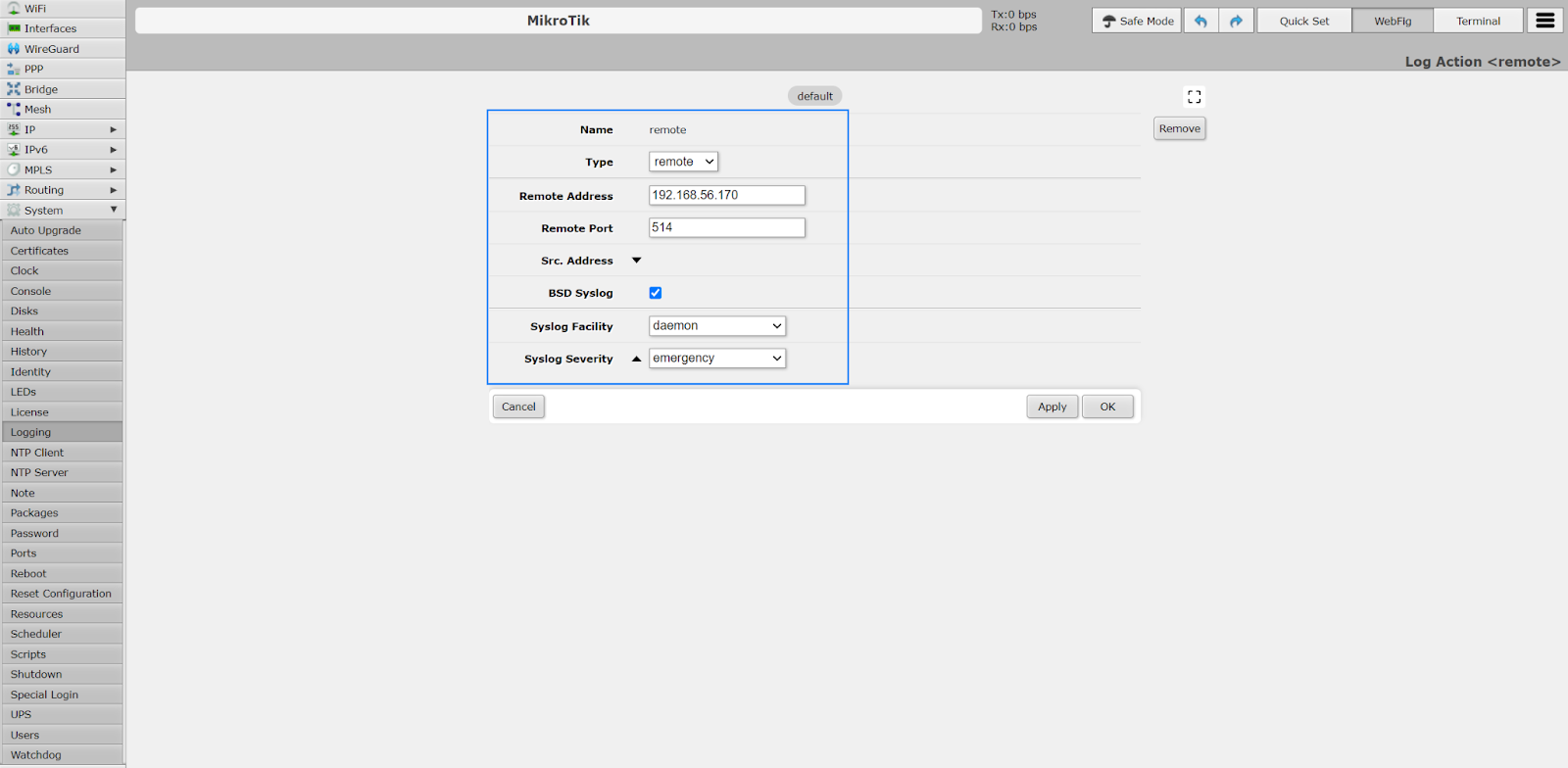
Ensure BSD Syslog is enabled, Syslog Facility is set to daemon, and Syslog Severity is set to emergency.
5. Click on Apply to save the above action.
6. Click on the System > Identity and ensure the Identity is set to MikroTik.
7. Click on Apply to ensure that the configuration is set.
Wazuh server
We create custom decoders and rules to extract the necessary fields from the MikroTik syslog and generate alerts based on their relevance. Follow the steps below to create custom rules and decoders in the Wazuh server.
MikroTik decoders
1. Create a custom decoder file mikrotik_decoders.xml in the /var/ossec/etc/decoders/ directory.
2. Add the custom MikroTik decoders below to the /var/ossec/etc/decoders/mikrotik_decoders.xml file:
<decoder name="mikrotik"> <prematch>^RouterOS7.1-logs: </prematch> </decoder> <decoder name="mikrotik1"> <parent>mikrotik</parent> <regex type="pcre2">\S+ (\w+ \d+ \d+:\d+:\d+) MikroTik user (\S+) (.*?) from (\d+.\d+.\d+.\d+) via (\w+)</regex> <order>logtimestamp, logged_user, action, ip_address, protocol</order> </decoder> <decoder name="mikrotik1"> <parent>mikrotik</parent> <regex type="pcre2">\S+ (\w+ \d+ \d+:\d+:\d+) MikroTik dhcp-client on (\S+) (.*?) address (\d+.\d+.\d+.\d+)</regex> <order>logtimestamp, interface, action, ip_address</order> </decoder> <decoder name="mikrotik1"> <parent>mikrotik</parent> <regex type="pcre2">\S+ (\w+ \d+ \d+:\d+:\d+) MikroTik router (\S+)</regex> <order>logtimestamp, action</order> </decoder>
3. Save the decoder and restart the Wazuh manager.
# systemctl restart wazuh-manager
MikroTik rules
1. Create a custom rule file mikrotik_rules.xml in the /var/ossec/etc/rules/ directory.
2. Add the custom MikroTik rules below to the /var/ossec/etc/rules/mikrotik_rules.xml file.
<group name="Mikrotik,">
<rule id="110000" level="0">
<decoded_as>mikrotik</decoded_as>
<description>Mikrotik-Event</description>
</rule>
<rule id="110001" level="5">
<if_sid>110000</if_sid>
<match>dhcp-client on ether</match>
<description>MikroTik dhcp-client received an IP address $(ip_address)</description>
</rule>
<rule id="110002" level="5">
<if_sid>110000</if_sid>
<match>rebooted</match>
<description>MikroTik router rebooted</description>
</rule>
<rule id="110003" level="5">
<if_sid>110000</if_sid>
<match>logged out from</match>
<description>MikroTik user logged out via $(protocol)</description>
</rule>
<rule id="110004" level="5">
<if_sid>110000</if_sid>
<match>logged in from</match>
<description>MikroTik user logged in from $(ip_address) via $(protocol)</description>
</rule>
</group>
Where:
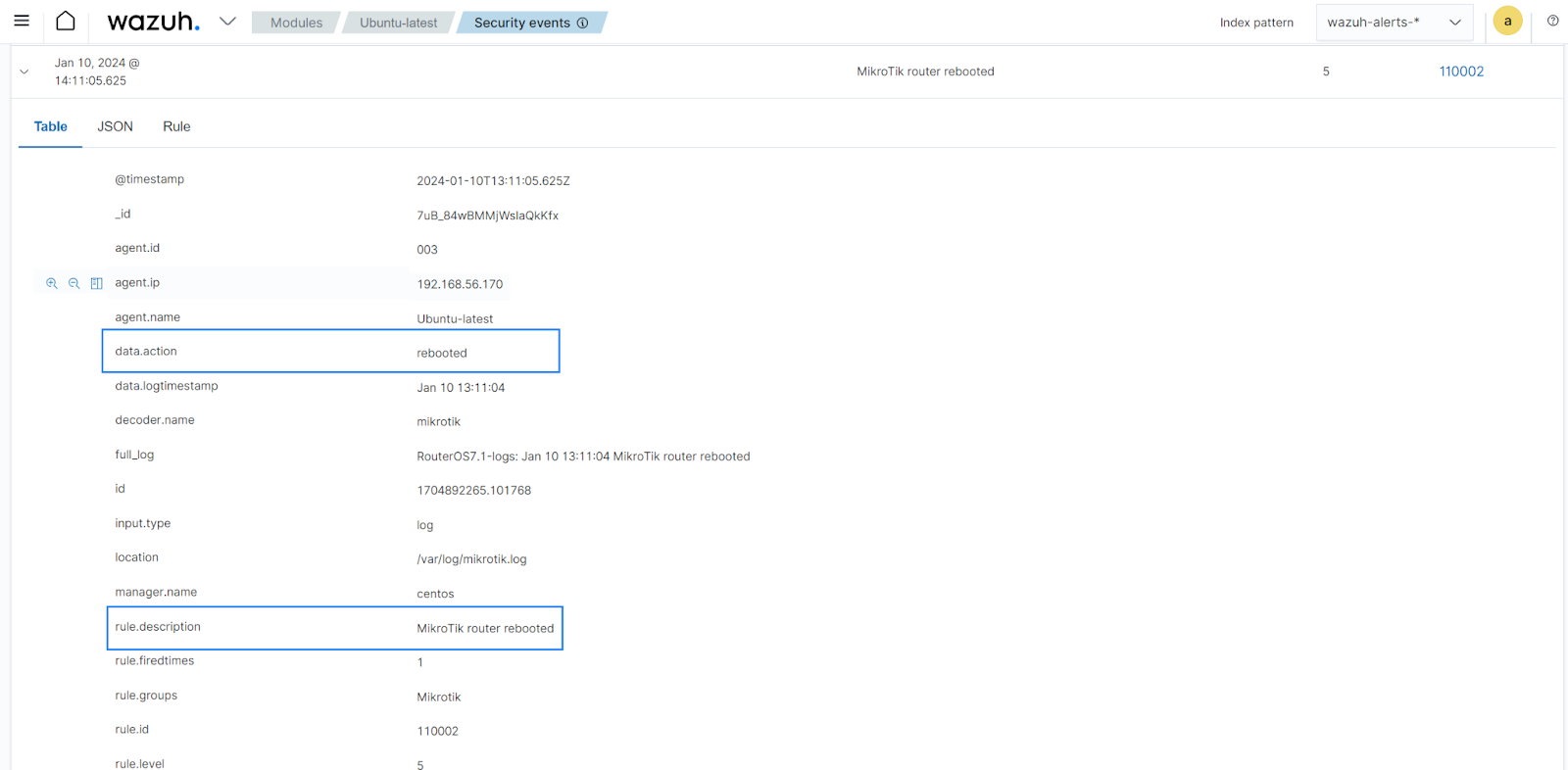
- Rule ID
110000is triggered when Wazuh detects a new MikroTik event - Rule ID
110001is triggered when Wazuh detects an IP address has been received by the MikroTik device using thedhcp-clientprotocol - Rule ID
110002is triggered when Wazuh detects the MikroTik device has been rebooted - Rule ID
110003is triggered when Wazuh detects a MikroTik user has logged out - Rule ID
110004is triggered when Wazuh detects a MikroTik user has logged in
3. Save the rule and restart the Wazuh manager.
# systemctl restart wazuh-manager
Use case
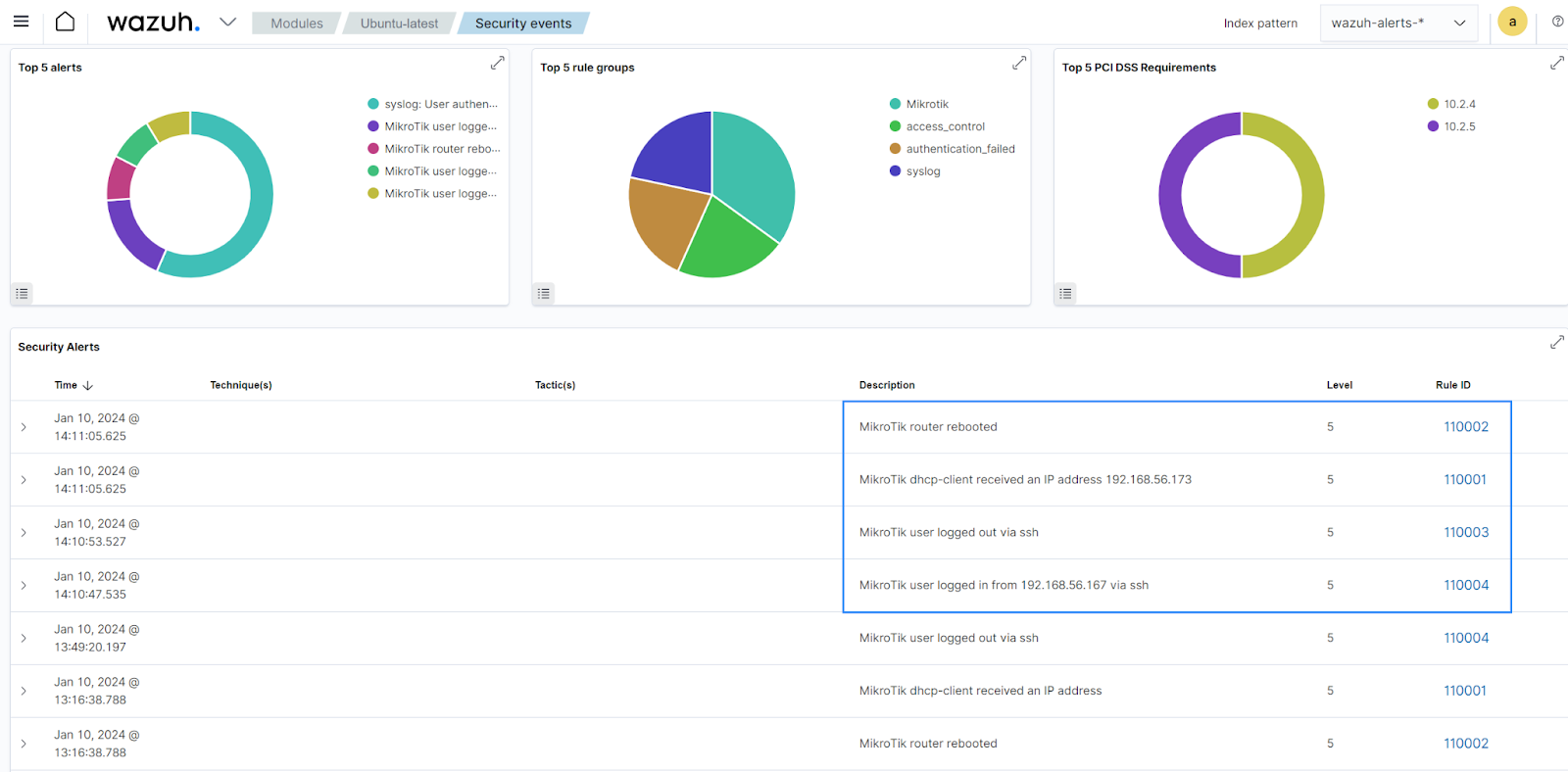
The following use case generates alerts on the Wazuh dashboard when certain events match the above rules. We performed a successful SSH login and rebooted the MikroTik router to generate the events.
1. Run the following commands from any endpoint within the same network as the MikroTik router:
$ ssh <MIKROTIK_USER>@<MIKROTIK_IP_ADDRESS> > /system/reboot
Replace:
<MIKROTIK_USER>with the username of the account used for administration on the Mikrotik device.<MIKROTIK_IP_ADDRESS>with the IP address of the MikroTik device.
2. Navigate to the Security events page of your Ubuntu endpoint on your Wazuh dashboard. The image below shows the alerts generated for the above actions.
Conclusion
Protecting your network devices is paramount to ensuring the integrity of your communication channels. This blog post shows how to achieve this using a MikroTik device as an example. It covers the necessary configurations that allow a MikroTik router to forward logs to your Wazuh server and the Wazuh configuration for triggering MikroTik-related alerts.
Please visit our website to find out more about securing other aspects of your infrastructure with Wazuh.
References